The GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungen lockdown is a ransomware alert that is locking your computer, and posing as an official notice from the Gesellschaft zur Verfolgung von Urheberrethtsverletzungen, claims that the your PC has been determined to have visited illegal websites.In reality, none of what the GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungenscreen is reporting is real, and the alert is only used to scare you into paying for a non-existing fine and stealing your personal financial information.
If you’ve got a GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungen ransomware infection , you’ll be seeing this screens :
Here is what the fake screen from the bloqué French GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungen says:
GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungen
Auf Ihrem Computer wurden illegal heruntergeladene Medien (“Raubkopien”) gefunden.
Diese sind in Form von Musik, Filmen oder Entertainmentsoftware vorhanden. Durch den Download wurden diese Medien vervielfältigt, so dass ebenfalls eine Strafbarkeit gemäß § 106 Urhebergesetz gegeben ist.
Der Download von urheberrechtlich geschützten Medien durch das Internet oder einer Dateitauschbörse (Filesharing) ist illegal und wird gemäß § 106 Urhebergesetz mit Geldstrafe oder Freiheitsstrafe von bis zu 3 Jahren bestraft. Weiterhin ist der Besitz nach § 184 Absatz 3 StGB strafbar und kann auch zur Einziehung des Rechners führen, mit dem die Dateien heruntergeladen wurden.
Eine eindeutige identifizierung Ihrer Person ist mit hilfe Ihrer IP-Adresse und des Hostnames problemlos mögliach.
Die gefundenen Raubkopien wurden verschlüsselt und in ein geschütztes Verzeichnis kopiert.
Um die Sperre aufzuheben und weiteren Strafrechtlichen konsequenzen aus dem Weg zu gehen, sind Sie verpflichtet eine Mahngebühr in Höhe von € 50,- zu bezahlen. Zahlbar durch unseren Payment- Partner Paysafecard. Nach erfolgreicher Bezahlung wird Ihr Computer automatisch entsperrt.
Um die Bezahlung durchzuführen, geben Sie den erworbenen Paysafecard-Code in das dafür vorgesehene Zahlungsfeld ein, wählen Sie den Wert Ihres Codes und drücken Sie anschliessend auf “Absenden”.
Die GVU ist gesetzlich legitimiert – und steht in engem Kontakt zu den Gesetzgebern.
We strongly advise you to follow our GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungen ransomware removal guide and ignore any alerts that this malicious software might generate.Under no circumstance should you send any any money to this cyber criminals as this could lead to identity theft.
Removal Instructions for GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungen
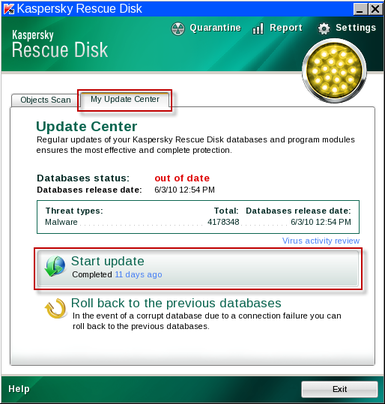
We will be using the Kaspersky Rescue Disk Bootable CD to clean the Windows registry and to perform a system scan to remove the malicious files.
What you’ll need to perform this removal guide :
- A computer with Internet access.
- 1 blank DVD or CD
- 1 DVD/CD Burner
- Software which can create a bootable CD – http://www.imgburn.com/index.php?act=download
- A copy of the latest Kaspersky Rescue Disc from here – http://rescuedisk.kaspersky-labs.com/rescuedisk/updatable/
- About 1 -2 hours depending on how much data you have on C:
STEP 1: Download and create a bootable Kaspersky Rescue Disk CD
- Download the Kaspersky Rescue Disk ISOimage from below.
KASPERSKY RESCUE DISK DOWNLOAD LINK (This link will open a new page from where you can download Kaspersky Rescue Disk ISO) - Download ImgBurn, a software that will help us create this bootable disk.
IMGBURN DOWNLOAD LINK (This link will open a new page from where you can download ImgBurn) - You can now insert your blank DVD/CD in your burner.
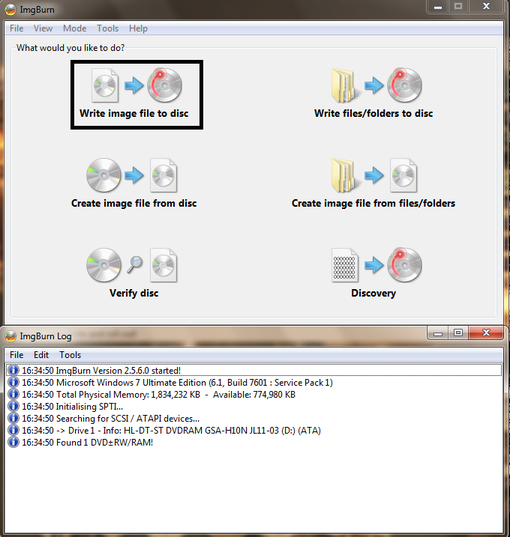
- Install ImgBurn by following the prompts and then start this program.
- Click on the Write image file to disc button.
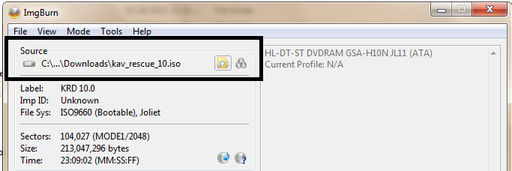
- Under ‘Source’ click on the Browse for file button, then browse to the location where you previously saved the Kaspersky Rescue Disk ISO file.(kav_rescue_10.iso)
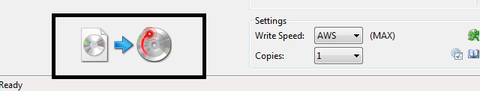
- Click on the big Write button.
- The disc creation process will now start and it will take around 5-10 minutes to complete.
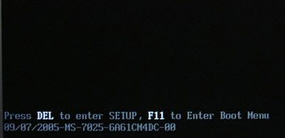
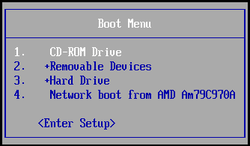
STEP 2:Configure the computer to boot from CD-ROM
- Use the Delete or F2 keys, to load the BIOS menu.Information how to enter the BIOS menu is displayed on the screen at the start of the OS boot:
- In your PC BIOS settings select the Boot menu and set CD/DVD-ROM as a primary boot device.
- Insert your Kaspersky Rescue Disk and restart your computer.
STEP 3:Boot your computer from Kaspersky Rescue Disk
- Your computer will now boot from the Kaspersky Rescue Disk,and you’ll be asked to press any key to proceed with this process
- In the start up wizard window that will open, select your language using the cursor moving keys. Press the ENTER key on the keyboard.
- On the next screen, select Kaspersky Rescue Disk. Graphic Mode then press ENTER.
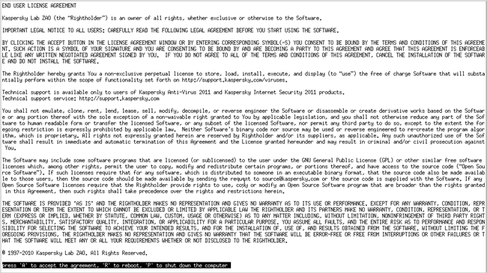
- The End User License Agreement of Kaspersky Rescue Disk will be displayed on the screen. Read carefully the agreement then press the C button on your keyboard.
- Once the actions described above have been performed, the Kasprsky operating system will start.
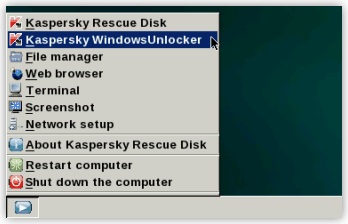
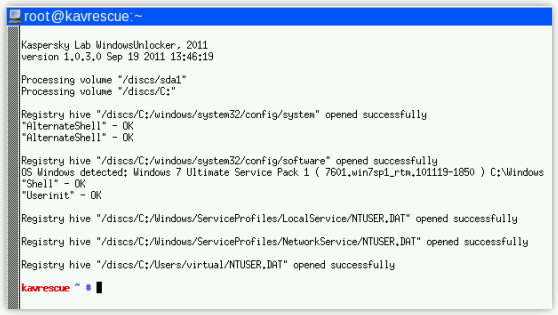
STEP 4: Launch Kaspersky WindowsUnlocker to remove the GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungen virus malicious registry changes
This virus has modified your Windows system registry so that when you’re trying to boot your computer it will instead launch his lock screen.To remove this malicious registry changes we need to use the Kasersky WindowsUnlocker from Kaspersky Rescue Disk.
- Click on the Start button located in the left bottom corner of the screen and select the Kaspersky WindowsUnlocker.
Alternatively you can select Terminal and in the command prompt type windowsunlocker and then press Enteron the keyboard. - A white colored console window will appear and will automatically start loading the registry files for scanning and disinfection. The whole process will take only a couple of seconds and after this process you should be able to boot your computer in normal mode.
STEP 5:Scan your system with Kaspersky Rescue Disk
- Click on the Start button located in the left bottom corner of the screen and select the Kaspersky Rescue Disk then click on My Update Center and press Start update.
- When the update process has completed, the light at the top of the window will turn green, and the databases release date will be updated.
- Click on the Objects Scan tab, then click Start Objects Scanto begin the scan.
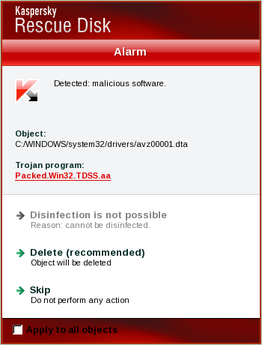
- If any malicious items are found, the default settings are to prompt you for action with a red popup window on the bottom right. Delete is the recommended action in most cases but we strongly recommend that you try first to disinfect , and if it doesn’t work chose to quarantine the infected files just to be on the safe side.
- When all detected items have been processed and removed, the light in the window will turn green and the scan will show as completed.
- When done you can close the Kaspersky Rescue Disk window and use the Start Menu to Restart the computer.
STEP 2: Download and scan with Malwarebytes Anti-Malware FREE to remove any left over malicious files from your computer.
- Download and run Malwarebytes Anti-Malware FREE
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK - Install Mawlarebytes Anti-Malware by following the prompts. Do not make any changes to the default installation settings and do not restart your computer if asked so.
- On the Scanner tab,please select Perform full scan and then click on the Scan button to start scanning your computer for any possible infections.
- When the scan is finished click the ‘OK‘ button and then you will be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected.
Make sure that everything is Checked (ticked) and click on Remove Selected button.
- Malwarebytes’ Anti-Malware will now start removing the malicious files.If during the removal process Malwarebytes will display a message stating that it needs to reboot, please allow this request.
If you are still experiencing problems while trying to remove Polisen Enheten for databrott alert from your machine, please start a new thread in our Malware Removal Assistance forum.
What’s next? Join our amazing community and build up your malware defenses !

![GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungen ransomware [Image: GVU Gesellschaft zur Verfolgung von Urheberrethtsverletzungen.png]](http://malwaretips.com/blogs/wp-content/uploads/2012/04/Gesellschaft-zur-Verfolgung-von-Urheberrethtsverletzungen.png)






![Install Malwarebytes Anti-Malware [Image: install-malwarebytes.png]](http://malwaretips.com/images/removalguide/mbam2.png)
![Perform a Full System Scan [Image: malwarebytes-full-system-scan.png]](http://malwaretips.com/images/removalguide/mbam4.png)
![Scan results [Image: malwarebytes-scan-results.png]](http://malwaretips.com/images/removalguide/mbam6.png)









