Perfecthosting.co is a deceptive website that displays fake security alerts, which are designed to scare people into calling a remote tech support phone number.
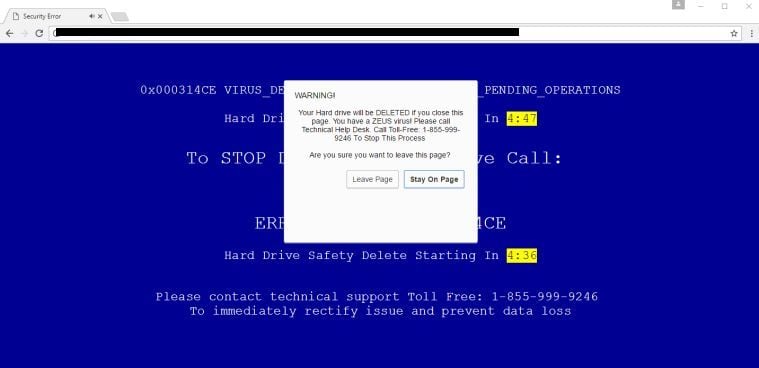
These alerts are shown in such a way as to trick the user into thinking their computer has crashed or that a virus has been detected on the computer. It does this to try and scare the infected user into calling one of the listed numbers in order to receive support. In reality, though, they will only be greeted with people who are trying to sell them unneeded support contracts and services.
Under no circumstances should you call these numbers, and if you have already have and purchased services, we advise you to dispute the charges with your credit card company.
The Perfecthosting.co pop-up ads are caused by an adware program which is distributed through various monetization platforms during installation. Unfortunately, some free downloads do not adequately disclose that other software will also be installed and you may find that you have installed adware without your knowledge.
When infected with this malicious program, other common symptoms include:
- Advertising banners are injected with the web pages that you are visiting.
- Random web page text is turned into hyperlinks.
- Browser popups appear which recommend fake updates or other software.
- Other unwanted adware programs might get installed without the user’s knowledge.
How to remove Perfecthosting.co pop-up ads (Virus Removal Guide)
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
- To remove Perfecthosting.co, follow these steps:
- STEP 1: Scan your computer with Malwarebytes AdwCleaner
- STEP 2: Scan your computer with Malwarebytes Anti-Malware
- STEP 3:Scan your computer HitmanPro
- (OPTIONAL) STEP 4: Reset your browser to default settings
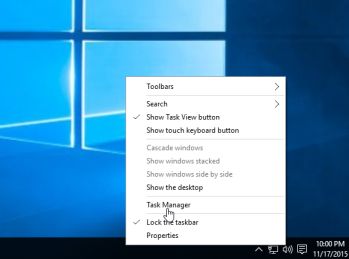
This step is needed if the malicious Perfecthosting.co pop-ups will not allow you to close your browser.
- Open Task Manager by right-clicking the taskbar and then clicking Start Task Manager. Alternatively to start the Windows Task Manager, you can press Ctrl+Alt+Del and click on Task Manager or simply press on Ctrl+Shift+Esc.
- Scroll through the list till you see your web browser’s process and left-click on it once so it becomes highlighted. Once you have selected the browser’s process, click on the End Task button as show in the picture below.
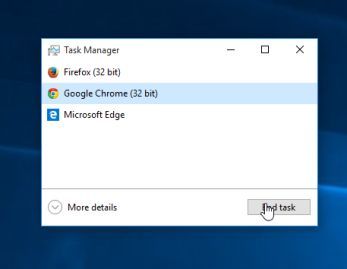
- Your browser window should now be closed. The next time you open your browser, do not allow the browser to open the last opened page.
STEP 1: Scan your computer with Malwarebytes AdwCleaner
Malwarebytes AdwCleaner is a free utility that will scan your computer for adware programs that may have been installed without your knowledge.
- You can download Malwarebytes AdwCleaner from the below link.
MALWAREBYTES ADWCLEANER DOWNLOAD LINK (This link will start the download of “Malwarebytes AdwCleaner” on your computer) - Before starting Malwarebytes AdwCleaner, close your web browser, then double-click on the Malwarebytes AdwCleaner icon.

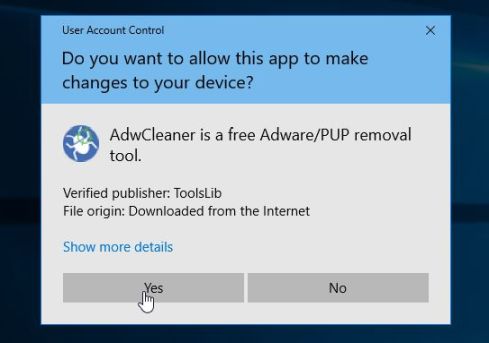
If Windows prompts you as to whether or not you wish to run Malwarebytes AdwCleaner, please allow it to run.
- When the Malwarebytes AdwCleaner program will open, click on the “Scan” button as shown below.
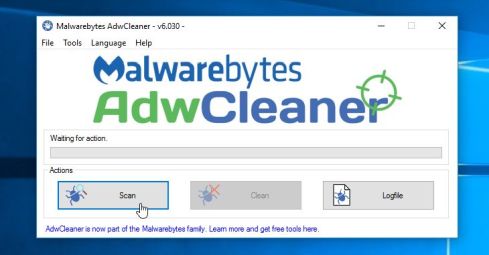
Malwarebytes AdwCleaner will now start to search for adware and other malicious programs. - To remove the malicious files that were detected in the previous step, please click on the “Clean” button.
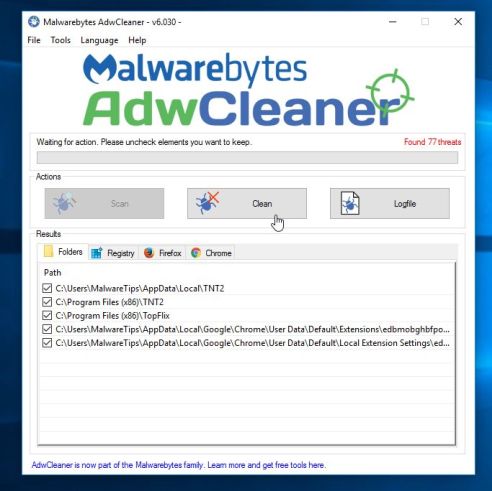
- Malwarebytes AdwCleaner will prompt you to save any open files or documents, as the program will need to reboot the computer to complete the cleaning process. Please do so, and then click on the “OK” button.
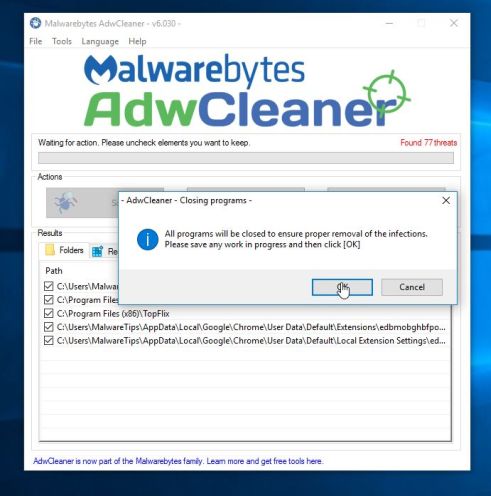
When your computer reboots and you are logged in, Malwarebytes AdwCleaner will automatically open a log file that contains the files, registry keys, and programs that were removed from your computer. Please review this log file and then close the notepad window.
STEP 2: Scan your computer with Malwarebytes Anti-Malware
Malwarebytes Anti-Malware is a powerful on-demand scanner which should remove the Perfecthosting.co redirect from your machine. It is important to note that Malwarebytes Anti-Malware will run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download “Malwarebytes Anti-Malware”) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup” to start the installation of Malwarebytes Anti-Malware.

You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.

- When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.

To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.

- Once installed, Malwarebytes Anti-Malware will automatically start and will update the antivirus database. To start a system scan you can click on the “Scan Now” button.

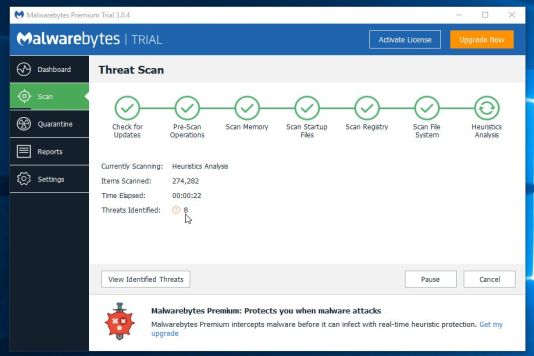
- Malwarebytes Anti-Malware will now start scanning your computer for malware. When Malwarebytes Anti-Malware is scanning it will look like the image below.
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Remove Selected” button.
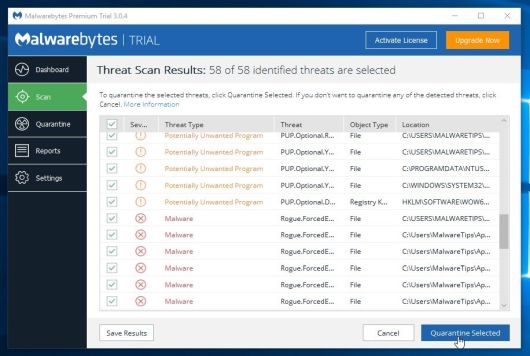
- Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
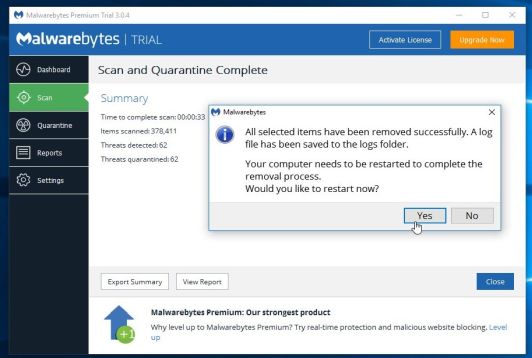
After your computer will restart, you should open Malwarebytes Anti-Malware and perform another scan to verify that there are no remaining threats
STEP 3: Scan your computer with HitmanPro
HitmanPro can find and remove malware, adware, bots and other threats that even the best antivirus suite can oftentimes miss. HitmanPro is designed to run alongside your antivirus suite, firewall and other security tools.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows).

Click on the “Next” button, to install HitmanPro on your computer.

- HitmanPro will now begin to scan your computer for malware.
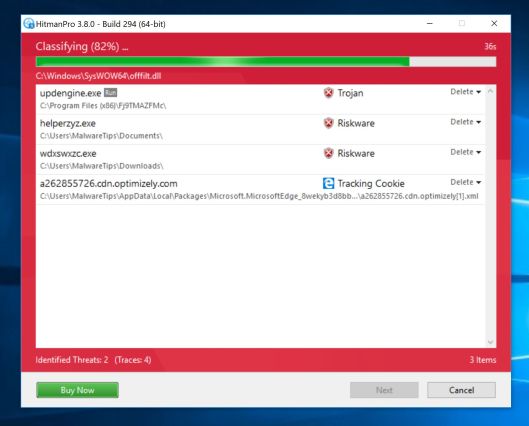
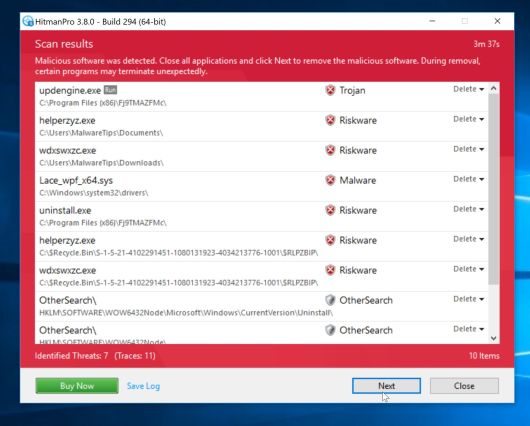
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
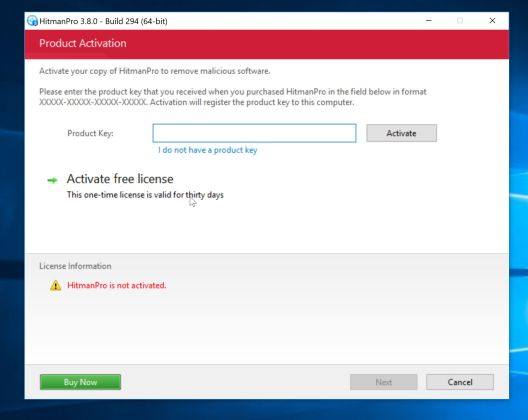
- Click on the “Activate free license” button to begin the free 30 days trial and remove all the malicious files from your computer.
(OPTIONAL) STEP 4: Reset your browser to default settings
This step should be performed only if your issues have not been solved by the previous steps.
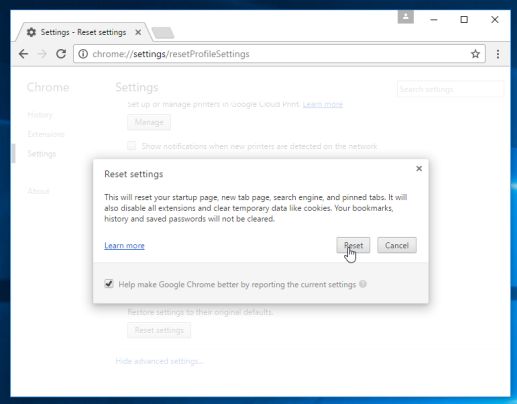
Google Chrome
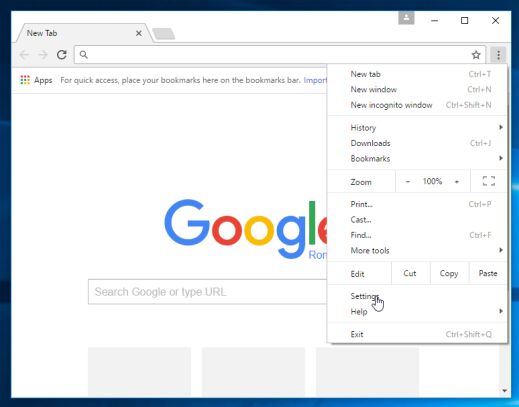
- Click on Chrome’s main menu button, represented by three horizontal lines. When the drop-down menu appears, select the option labeled Settings.
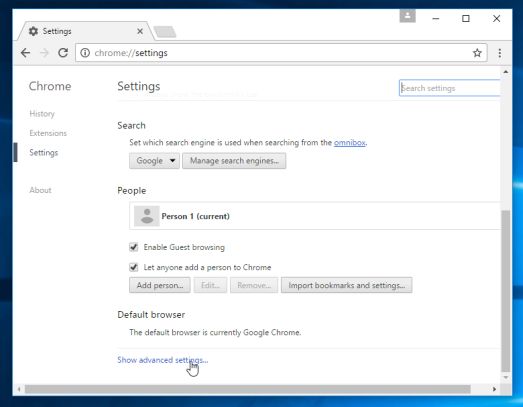
- Chrome’s Settings should now be displayed in a new tab or window, depending on your configuration. Next, scroll to the bottom of the page and click on the Show advanced settings link (as seen in the below example).
- Chrome’s advanced Settings should now be displayed. Scroll down until the Reset browser settings section is visible, as shown in the example below. Next, click on the Reset browser settings button.
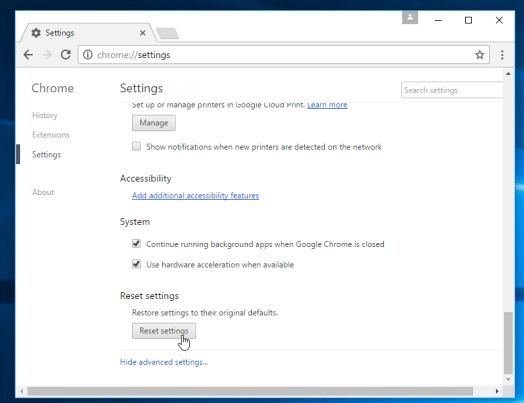
- A confirmation dialog should now be displayed, detailing the components that will be restored to their default state should you continue on with the reset process. To complete the restoration process, click on the Reset button.
Internet Explorer
- Open Internet Explorer, click on the “gear icon”
 in the upper right part of your browser, then click again on Internet Options.
in the upper right part of your browser, then click again on Internet Options.
![Click on the Gear Icon then on Internet Options [Image: Internet Options in Internet Explorer]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/Internet-Options-Internet-Explorer.jpg)
- In the “Internet Options” dialog box, click on the “Advanced” tab, then click on the “Reset” button.
![In the Advanced tab click on the Reset button [Image: Reset Internet Explorer]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/Reset-Internet-Explorer.jpg)
- In the “Reset Internet Explorer settings” section, select the “Delete personal settings” check box, then click on “Reset” button.
![Click on the Reset button to revert IE to its default settings [Image: Reset Internet Explorer to its default settings]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/reset-button-Internet-Explorer.jpg)
- When Internet Explorer has completed its task, click on the “Close” button in the confirmation dialogue box. You will now need to close your browser and then you can open Internet Explorer again.
![Click on the Close button [Image Reset Internet Explorer settings]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/Close-button-Reset.jpg)
Mozilla Firefox
- In the upper-right corner of the Firefox window, click the Firefox menu button (
![Firefox Menu button [Image: Firefox Menu button]](https://malwaretips.com/blogs/wp-content/uploads/2014/04/Firefox-menu-button.png) ), then click on the “Help” (
), then click on the “Help” (![Firefox Help button [Image: Firefox Help button]](https://malwaretips.com/blogs/wp-content/uploads/2014/04/Firefox-Help.png) ) button.
) button.
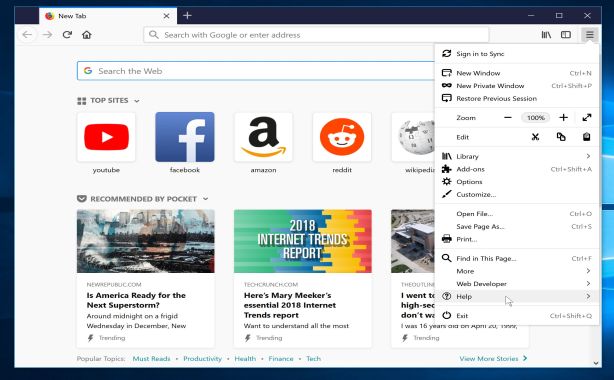
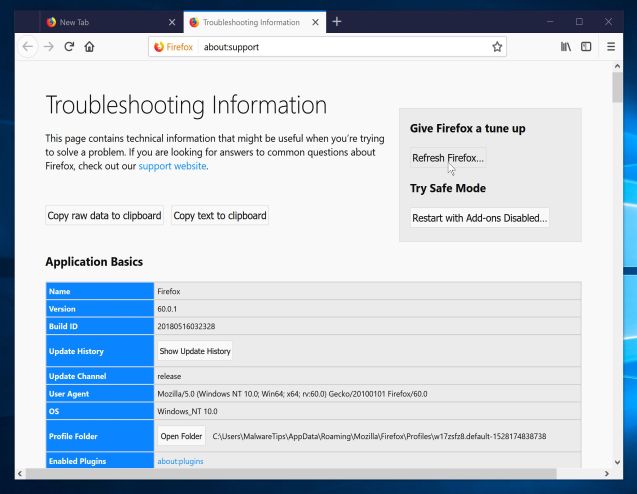
- From the Help menu, choose Troubleshooting Information.
If you’re unable to access the Help menu, type about:support in your address bar to bring up the Troubleshooting information page.
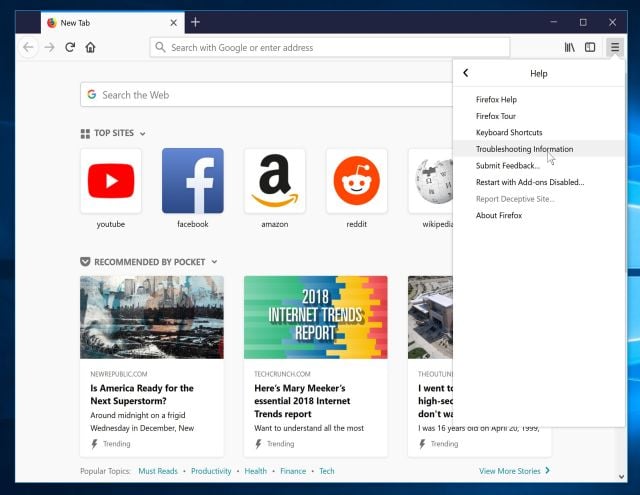
- Click the “Refresh Firefox” button in the upper-right corner of the “Troubleshooting Information” page.
- To continue, click on the “Refresh Firefox” button in the new confirmation window that opens.
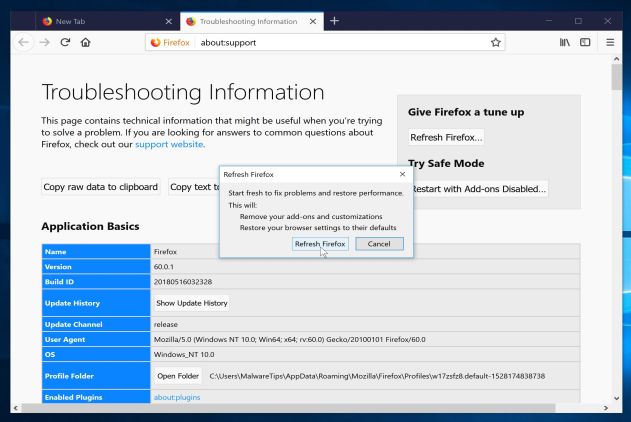
- Firefox will close itself and will revert to its default settings. When it’s done, a window will list the information that was imported. Click on the “Finish“.
Note: Your old Firefox profile will be placed on your desktop in a folder named “Old Firefox Data“. If the reset didn’t fix your problem you can restore some of the information not saved by copying files to the new profile that was created. If you don’t need this folder any longer, you should delete it as it contains sensitive information.
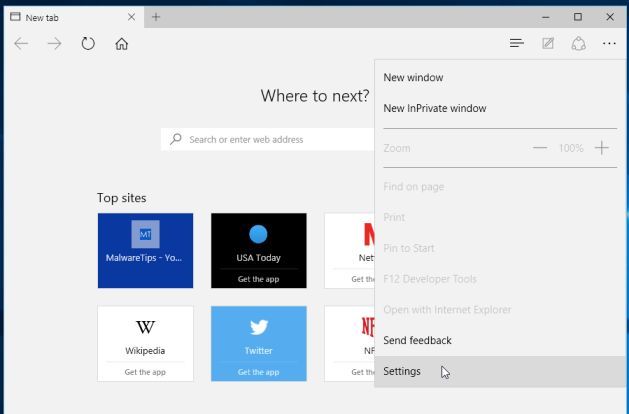
Microsoft Edge
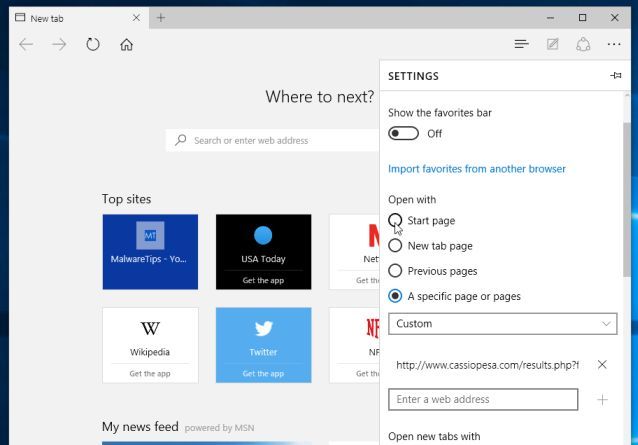
- In the upper-right corner of the Microsoft Edge window, click the “More actions” icon (three dots), then click on the “Settings” option.
- Under the section labeled “Open With“, select the option “Start page“.
Your computer should now be free of the Perfecthosting.co redirect. You can remove AdwCleaner from your machine, however we recommend that you keep Malwarebytes Anti-Malware and HitmanPro installed to perform regular computer scans.
If you are still experiencing problems while trying to remove Perfecthosting.co pop-ups from your machine, please do one of the following:
- Run a system scan with Zemana AntiMalware
- Ask for help in our Malware Removal Assistance forum.