Trojan Qhosts is a trojan program that prevents access to certain web sites and reroutes traffic to certain IP addresses.
It should be noted that this trojan cannot spread by itself. Infection occurs when an HTML web page containing malicious code is opened allowing the trojan to open a viral HTML file on the target computer. When the malicious executable has been created and run, the Qhost trojan alters the computer’s Domain Name Server set-up or HOSTS file. This allows an attacker to virtually hijack browser use by dictating which sites are visited. The trojan, for example, denies access to most major search engines, redirecting the user instead to different sites.
Trojan:Win32/QHosts has different versions know as:
Trojan:Win32/QHosts.BH (Microsoft)
Trojan.Hosts.6582 (Dr.Web)
Trojan.VBS.Downloader (Ikarus)
Trojan.Win32.Qhost.aexv (Kaspersky)
Trojan/Win32.Qhost (AhnLab)
Win32/Bicololo.A trojan (ESET)
winpe/Qhost.MCF (Norman)
Trojan.Hosts.6167 (Dr.Web)
Win32/Bicololo.A trojan (ESET)
Trojan.VBS.Downloader (Ikarus)
Trojan.Win32.Qhost.aeif (Kaspersky)
- Trojan:Win32/QHosts – Virus Removal Instructions
- STEP 1: Remove Trojan:Win32/QHosts trojan with Kaspersky TDSSKiller
- STEP 2: Run RKill to terminate Trojan:Win32/QHosts malicious processes
- STEP 3: Remove Trojan:Win32/QHosts virus with Malwarebytes Anti-Malware FREE
- STEP 4: Remove Trojan:Win32/QHosts rootkit with RogueKiller
- STEP 5: Remove Trojan:Win32/QHosts infection with HitmanPro
- STEP 6: Double check for any left over infections with Emsisoft Emergency Kit
- STEP 7: Remove Trojan:Win32/QHosts adware with AdwCleaner
Trojan:Win32/QHosts.BG (Microsoft)
Trojan:Win32/QHosts – Virus Removal Instructions
This page is a comprehensive guide, which will remove the Trojan:Win32/QHosts infection from your your computer. Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
STEP 1: Remove Trojan:Win32/QHosts Master Boot Record infection with Kaspersky TDSSKiller
STEP 2: Run RKill to terminate Trojan:Win32/QHosts malicious processes
STEP 3: Remove Trojan:Win32/QHosts virus with Malwarebytes Anti-Malware Free
STEP 4: Remove Trojan:Win32/QHosts trojan with RogueKiller
STEP 5: Remove Trojan:Win32/QHosts infection with HitmanPro
STEP 6: Double check for any left over infections with Emsisoft Emergency Kit
STEP 7: Remove Trojan:Win32/QHosts adware with AdwCleaner
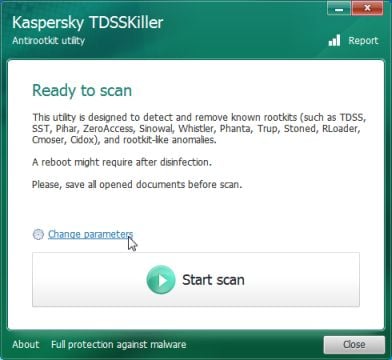
STEP 1: Remove Trojan:Win32/QHosts trojan with Kaspersky TDSSKiller
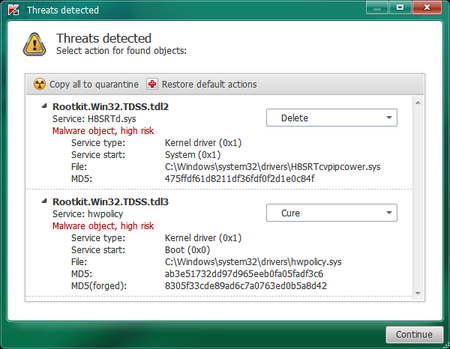
As part of its self defense mechanism, Trojan:Win32/QHosts virus will install a ZeroAccess rootkit on the infected computer.In this first step, we will run a system scan with Kaspersky TDSSKiller to remove this rookit.
- Please download the latest official version of Kaspersky TDSSKiller.
KASPERSKY TDSSKILLER DOWNLOAD LINK(This link will automatically download Kaspersky TDSSKiller on your computer.) - Double-click on tdsskiller.exe to open this utility, then click on Change Parameters.
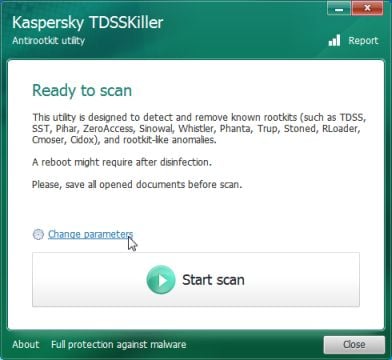
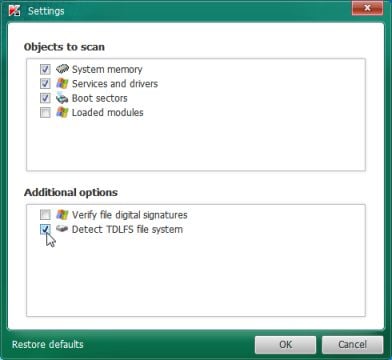
- In the new open window,we will need to enable Detect TDLFS file system, then click on OK.
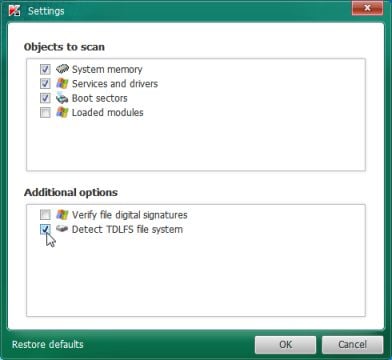
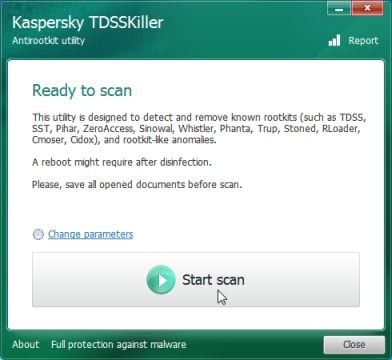
- Next,we will need to start a scan with Kaspersky, so you’ll need to press the Start Scan button.
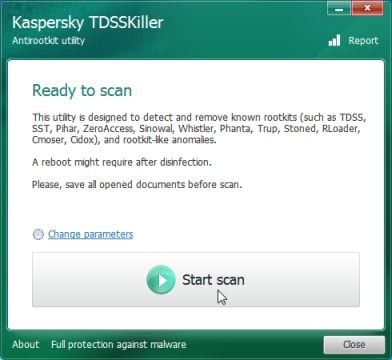
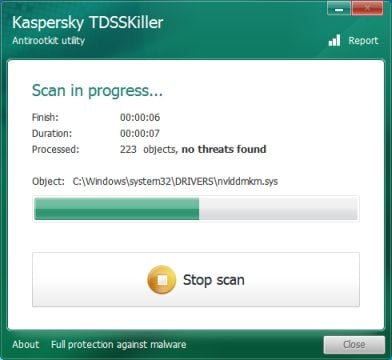
- Kaspersky TDSSKiller will now scan your computer for Trojan Trojan:Win32/QHosts infection.
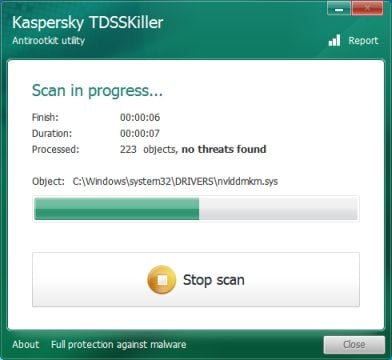
- When the scan has finished it will display a result screen stating whether or not the infection was found on your computer. If it was found it will display a screen similar to the one below.
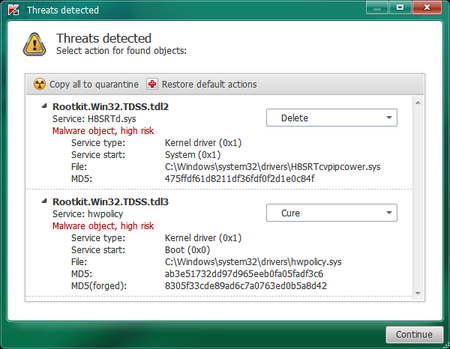
- To remove the infection simply click on the Continue button and TDSSKiller will attempt to clean the infection.A reboot will be require to completely remove any infection from your system.
STEP 2: Run RKill to terminate Trojan:Win32/QHosts malicious processes
RKill is a program that will attempt to terminate all malicious processes associated with Trojan:Win32/QHosts infection, so that we will be able to perform the next step without being interrupted by this malicious software.
Because this utility will only stop Trojan:Win32/QHosts running process, and does not delete any files, after running it you should not reboot your computer as any malware processes that are configured to start automatically will just be started again.
- While your computer is in Safe Mode with Networking ,please download the latest official version of RKill.Please note that we will use a renamed version of RKILL so that Proven Antivirus Protection won’t block this utility from running.
RKILL DOWNLOAD LINK (This link will automatically download RKILL renamed as iExplore.exe) - Double click on iExplore.exe to start RKill and stop any processes associated with Trojan:Win32/QHosts.
![Rkill renamed to iExplore.exe [Image: RKILL Program]](//malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-run-as-admin.jpg)
- RKill will now start working in the background, please be patient while the program looks for Trojan:Win32/QHosts malicious process and tries to end them.
![RKill while killing Trojan:Win32/QHosts malicious process [Image: RKILL stoping malware]](//malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-program.jpg)
- When the Rkill utility has completed its task, it will generate a log. Do not reboot your computer after running RKill as the malware programs will start again.
![RKill Log [Image: RKill Report]](//malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-report.jpg)
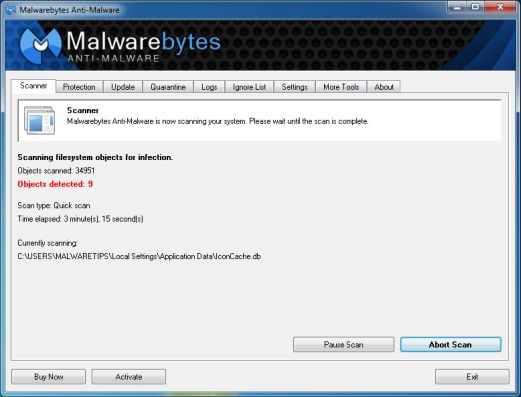
STEP 3: Remove Trojan:Win32/QHosts virus with Malwarebytes Anti-Malware FREE
Malwarebytes Anti-Malware Free is a powerful on-demand scanner which will remove Trojan:Win32/QHosts malicious files from your computer.
- You can download Malwarebytes Anti-Malware Free from the below link, then double-click on the icon named mbam-setup.exe to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK(This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process, then at the last screen click on the Finish button.
![Malwarebytes Anti-Malware installation screen [Image: Malwarebytes Anti-Malware final installation screen]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
- On the Scanner tab, select Perform quick scan, and then click on the Scan button to start searching for the Trojan:Win32/QHosts malicious files.
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
- Malwarebytes’ Anti-Malware will now start scanning your computer for Trojan:Win32/QHosts virus as shown below.
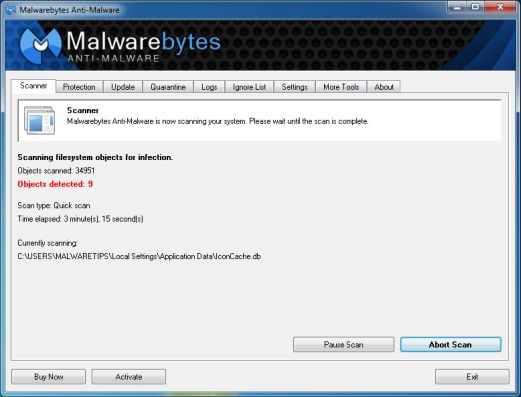
- When the Malwarebytes Anti-Malware scan has finished, click on the Show Results button.
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
- You will now be presented with a screen showing you the computer infections that Malwarebytes Anti-Malware has detected. Make sure that everything is Checked (ticked), then click on the Remove Selected button.
![Malwarebytes Anti-Malwar removing Trojan:Win32/QHosts virus [Image: Malwarebytes Anti-Malwar removing Trojan:Win32/QHosts virus]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)
- Once your computer will restart in Windows regular mode, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats.
STEP 4: Remove Trojan:Win32/QHosts rootkit with RogueKiller
RogueKiller is a utility that will scan for the Trojan:Win32/QHosts rootkit, registry keys and any other malicious files on your computer.
- You can download the latest official version of RogueKiller from the below link.
ROGUEKILLER DOWNLOAD LINK (This link will open a new web page from where you can download RogueKiller on your computer) - Double-click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds, then click on the Scan button to perform a system scan.
![Click on the Start button to perform a system scan [Image: RogueKiller scaning for Trojan:Win32/QHosts virus]](//malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-scan.jpg)
- After the scan has completed, press the Delete button to remove Trojan:Win32/QHosts malicious registry keys or files.
![Press Delete to remove Luhe.Sirefef.A [Image: RogueKiller Detele button]](//malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-delete.jpg)
STEP 5: Remove Trojan:Win32/QHosts infection with HitmanPro
HitmanPro is a second opinion scanner, designed to rescue your computer from malware (viruses, trojans, rootkits, etc.) that have infected your computer despite all the security measures you have taken (such as anti virus software, firewalls, etc.).
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a web page from where you can download HitmanPro) - Double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.

Click on the Next button, to install HitmanPro on your computer.

- HitmanPro will now begin to scan your computer for Trojan:Win32/QHosts trojan.

- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the Next button, to remove Trojan:Win32/QHosts virus.

- Click on the Activate free license button to begin the free 30 days trial, and remove all the malicious files from your computer.
![HitmanPro free 30 days trial [Image: HitmanPro 30 days activation button]](//malwaretips.com/blogs/wp-content/uploads/2012/11/hitmanpro-activation.jpg)
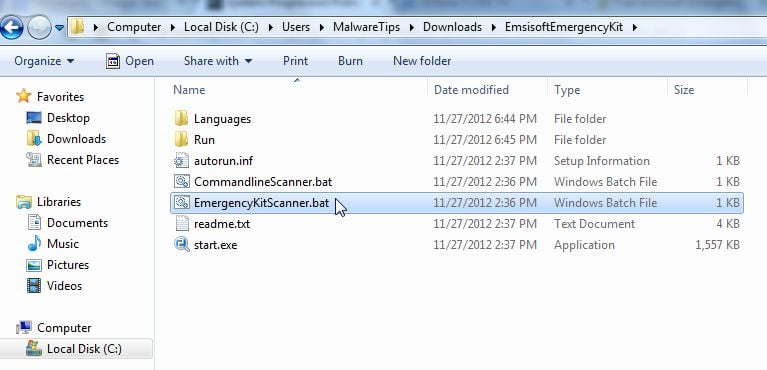
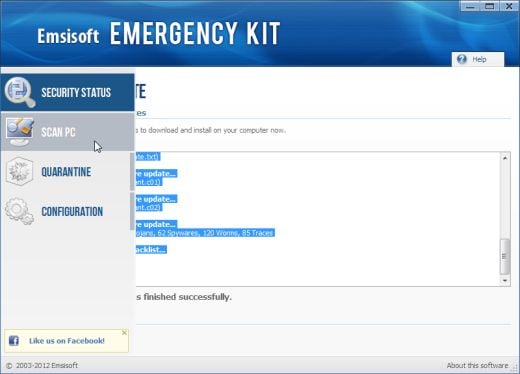
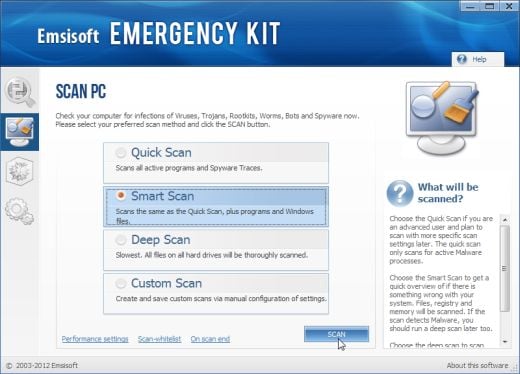
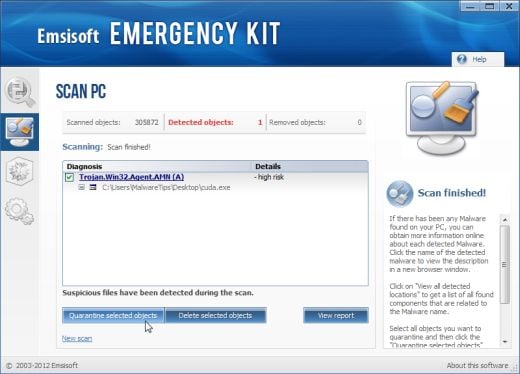
STEP 6: Double check for any left over infections with Emsisoft Emergency Kit
The Emsisoft Emergency Kit Scanner includes the powerful Emsisoft Scanner complete with graphical user interface. Scan the infected PC for Viruses, Trojans, Spyware, Adware, Worms, Dialers, Keyloggers and other malicious programs.
- You can download Emsisoft Emergency Kit from the below link,then extract it to a folder in a convenient location.
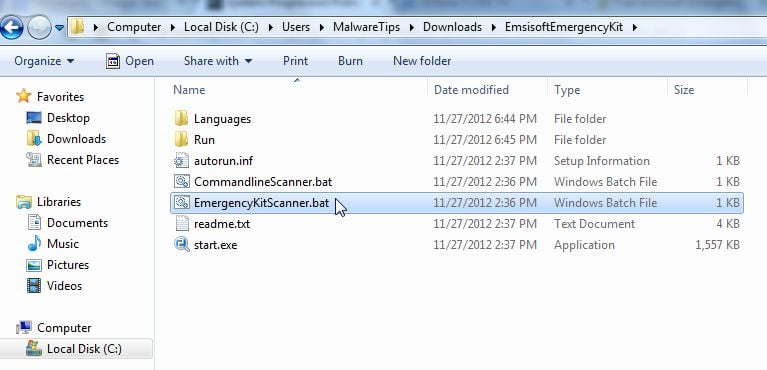
EMSISOFT EMERGENCY KIT DOWNLOAD LINK ((This link will open a new web page from where you can download Emsisoft Emergency Kit) - Open the Emsisoft Emergency Kit folder and double click EmergencyKitScanner.bat, then allow this program to update itself.
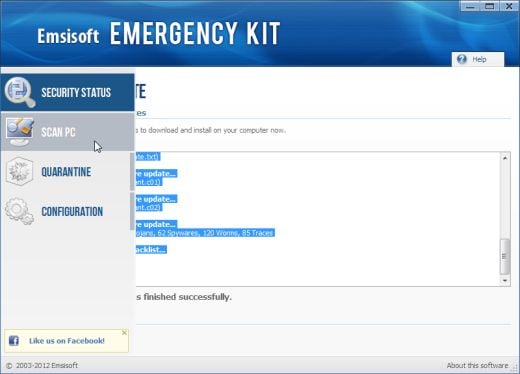
- After the Emsisoft Emergency Kit has update has completed,click on the Menu tab,then select Scan PC.
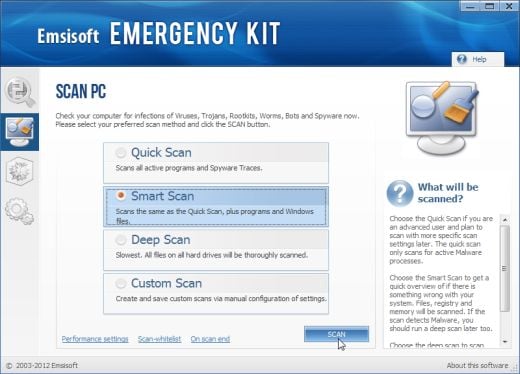
- Select Smart scan and click on the SCAN button to search for “Antivirus Security 2013” malicious files.
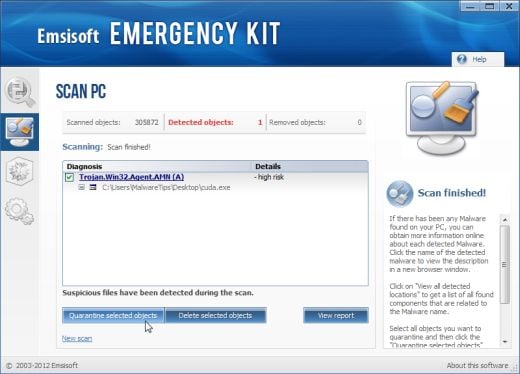
- When the scan will be completed,you will be presented with a screen reporting which malicious files has Emsisoft detected on your computer, and you’ll need to click on Quarantine selected objects to remove them.
STEP 7: Remove Trojan:Win32/QHosts adware with AdwCleaner
The AdwCleaner utility will scan your computer for Trojan:Win32/QHosts malicious files that may have been installed on your computer without your knowledge.
- You can download AdwCleaner utility from the below link.
ADWCLEANER DOWNLOAD LINK (This link will automatically download AdwCleaner on your computer) - Before starting AdwCleaner, close all open programs and internet browsers, then double-click on the AdwCleaner icon.
![AdwCleaner Icon [Image: AdwCleaner Icon]](//malwaretips.com/blogs/wp-content/uploads/2013/08/adwcleaner-icon.jpg)
If Windows prompts you as to whether or not you wish to run AdwCleaner, please allow it to run. - When the AdwCleaner program will open, click on the Scan button as shown below.
![Click on Scan button to search for Trojan:Win32/QHosts infection [Image: Adwcleaner Scan]](//malwaretips.com/blogs/wp-content/uploads/2013/08/adwcleaner-scan.jpg)
AdwCleaner will now start to search for Trojan:Win32/QHosts malicious files that may be installed on your computer. - To remove the Trojan:Win32/QHosts malicious files that were detected in the previous step, please click on the Clean button.
![Click on the Clean button to remove Trojan:Win32/QHosts virus [Image: AdwCleaner removing infections]](//malwaretips.com/blogs/wp-content/uploads/2013/08/adwcleaner-cleanup.jpg)
AdwCleaner will now prompt you to save any open files or data as the program will need to reboot the computer. Please do so and then click on the OK button.
Your computer should now be free of the Trojan:Win32/QHosts infection. If your current anti-virus solution let this infection through, you may want to consider purchasing the PRO version of Malwarebytes Anti-Malware to protect against these types of threats in the future, and perform regular computer scans with HitmanPro.
If you are still experiencing problems while trying to remove Trojan:Win32/QHosts from your machine, please start a new thread in our Malware Removal Assistance forum.

![Rkill renamed to iExplore.exe [Image: RKILL Program]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-run-as-admin.jpg)
![RKill while killing Trojan:Win32/QHosts malicious process [Image: RKILL stoping malware]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-program.jpg)
![RKill Log [Image: RKill Report]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-report.jpg)
![Malwarebytes Anti-Malware installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Malwarebytes Anti-Malwar removing Trojan:Win32/QHosts virus [Image: Malwarebytes Anti-Malwar removing Trojan:Win32/QHosts virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)
![Click on the Start button to perform a system scan [Image: RogueKiller scaning for Trojan:Win32/QHosts virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-scan.jpg)
![Press Delete to remove Luhe.Sirefef.A [Image: RogueKiller Detele button]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-delete.jpg)




![HitmanPro free 30 days trial [Image: HitmanPro 30 days activation button]](http://malwaretips.com/blogs/wp-content/uploads/2012/11/hitmanpro-activation.jpg)
![Click on Scan button to search for Trojan:Win32/QHosts infection [Image: Adwcleaner Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/08/adwcleaner-scan.jpg)
![Click on the Clean button to remove Trojan:Win32/QHosts virus [Image: AdwCleaner removing infections]](http://malwaretips.com/blogs/wp-content/uploads/2013/08/adwcleaner-cleanup.jpg)