ZeroAccess is a sophisticated kernel-mode rootkit that is rapidly becoming one of the most widespread threats in the current malware ecosystem. ZeroAccess’ ability to run on both 32-bit and 64-bit versions of Windows, resilient peer-to-peer command and control infrastructure and constant updates to its functionality over time show that ZeroAccess is a modern threat capable of thriving on modern networks and modern Operating Systems.
ZeroAccess remains hidden on an infected machine while downloading more visible components that generate revenue for the botnet owners. Currently the downloaded malware is mostly aimed at sending spam and carrying out click fraud, but previously the botnet has been instructed to download other malware and it is likely that this will be the case again in the future. ZeroAccess should be considered an advanced and dangerous threat that requires a fully featured, multi-layered protection strategy.
ZeroAccess employs mechanisms that are themselves hard to remove such as a kernel-mode rootkit and patched driver files, patched system files such as services.exe and data hidden in NTFS Extended Attributes, removal of NTFS permissions on files used; and because ZeroAccess often employs several autostart points on an infected machine and usually other files that can re-install the malware.
How to remove ZeroAccess rootkit virus (Virus Removal Guide)
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
-
To remove ZeroAccess rootkit virus, follow these steps:
- STEP 1: Use ESETSirfefCleaner tool to remove ZeroAccess rootkit
- STEP 2: Use RKill to stop the ZeroAccess rootkit malicious processes
- STEP 3: Scan your computer with Malwarebytes Anti-Malware to remove ZeroAccess rootkit
- STEP 4: Double-check for malicious programs with HitmanPro
- (OPTIONAL) STEP 5: Use Zemana AntiMalware Portable to remove ZeroAccess rootkit
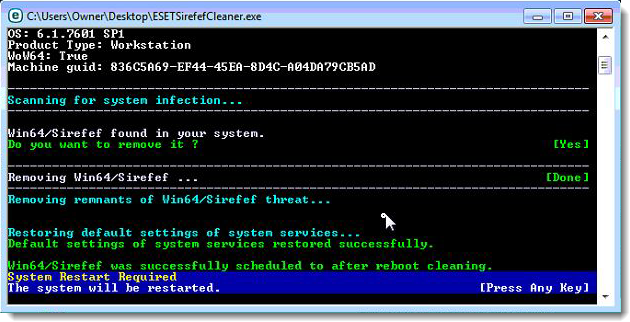
STEP 1: Use ESETSirfefCleaner tool to remove ZeroAccess rootkit
In this first step, we will use the ESETSirefefCleaner tool to remove the ZeroAccess rootkit from your computer.
- You can download ESETSirefefCleaner from the below link.
ESETSIREFEFCLEANER DOWNLOAD LINK(This link will automatically download ESETSirfefCleaner on your computer.)Unable to download “ESETSirefefCleaner.exe contained a virus and was deleted”.
More recent variants of Sirefef might prevent you from downloading this removal tool. If you cannot download the tool, follow the steps below:- Click Start → Computer → Local Disk (C:) → Program Files.
- Right-click the Windows Defender folder and select Rename from the context menu.
- Add a unique variation to the filename, such as .old (for example, Windows Defender.old).
- Click the link above to download the ESETSirefefCleaner tool.When the download is complete, make sure to rename the Windows Defender folder back to its original filename before running the ESET SirefefCleaner tool.
- Double-click on ESETSirefefCleaner.exe to start this utility. You may be presented with an User Account Control pop-up asking if you want to allow this to make changes to your device. If this happens, you should click “Yes” to continue.
- The message “Win32/Sirefef.EV found in your system” will be displayed if an infection is found. To remove ZeroAccess rootkit from your computer, press the Y key on your keyboard
- Once the tool has run, you will be prompted to restore system services after you restart your computer. Press Y on your keyboard to restore system services and restart your computer.
- Once your computer has restarted, if you are presented with a security notification click Yes or Allow. and then continue wit the next step.
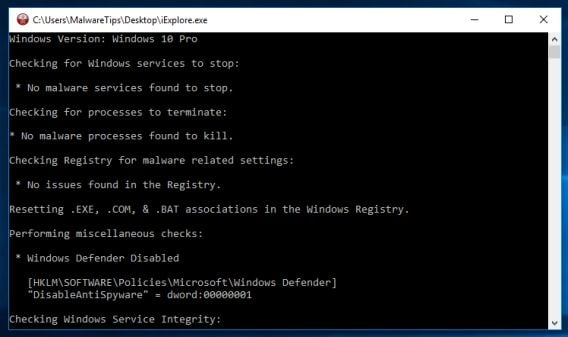
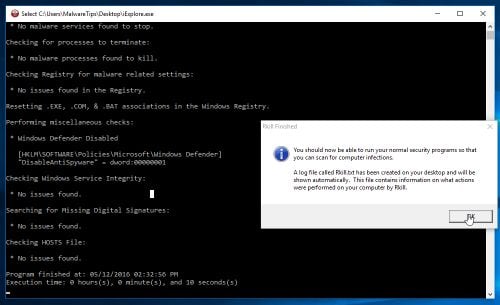
STEP 2: Use RKill to stop the ZeroAccess rootkit malicious processes
RKill is a program that will attempt to terminate all malicious processes associated with ZeroAccess rootkit, so that we will be able to perform the next step without being interrupted by this malicious software.
- You can download Rkill from the below link.
RKILL DOWNLOAD LINK (his link will open a new web page from where you can download “RKill”) - Double click on Rkill program to stop the malicious programs from running.
- RKill will now start working in the background, please be patient while this utiltiy looks for malicious process and tries to end them.
- When the Rkill tool has completed its task, it will generate a log. Do not reboot your computer after running RKill as the malware programs will start again.
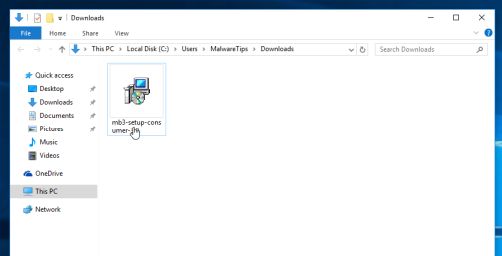
STEP 3: Scan your computer with Malwarebytes Anti-Malware to remove ZeroAccess rootkit
Malwarebytes Anti-Malware is a powerful on-demand scanner which should remove the ZeroAccess rootkit virus from your machine. It is important to note that Malwarebytes Anti-Malware will run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
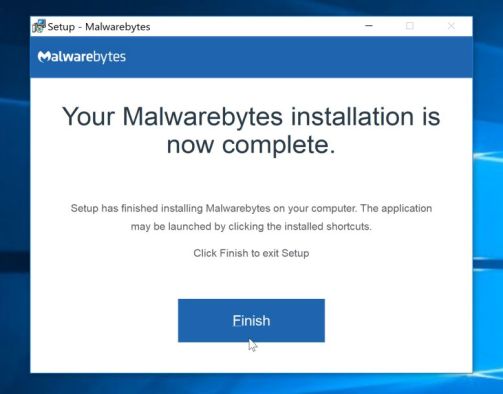
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link open a new page from where you can download “Malwarebytes Anti-Malware”) - When Malwarebytes has finished downloading, double-click on the “mb3-setup-consumer” file to install Malwarebytes Anti-Malware on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- When the Malwarebytes installation begins, you will see the Malwarebytes Setup Wizard which will guide you through the installation process.
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
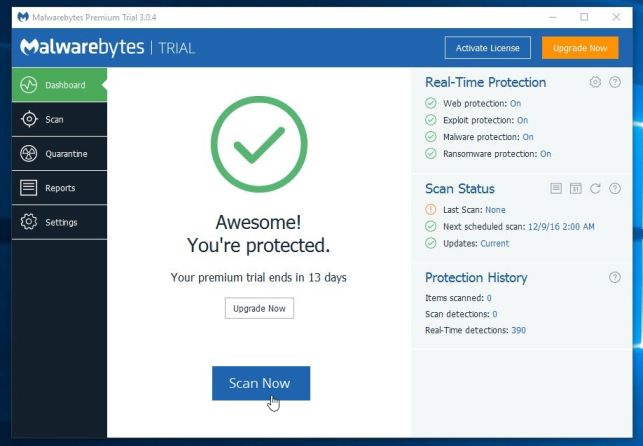
- Once installed, Malwarebytes will automatically start and update the antivirus database. To start a system scan you can click on the “Scan Now” button.
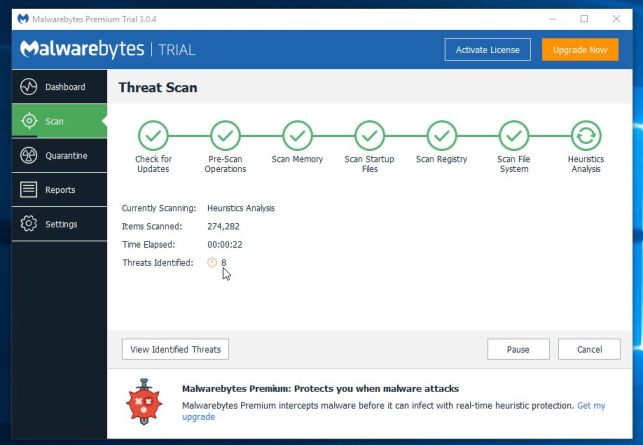
- Malwarebytes Anti-Malware will now start scanning your computer for malicious programs.
This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
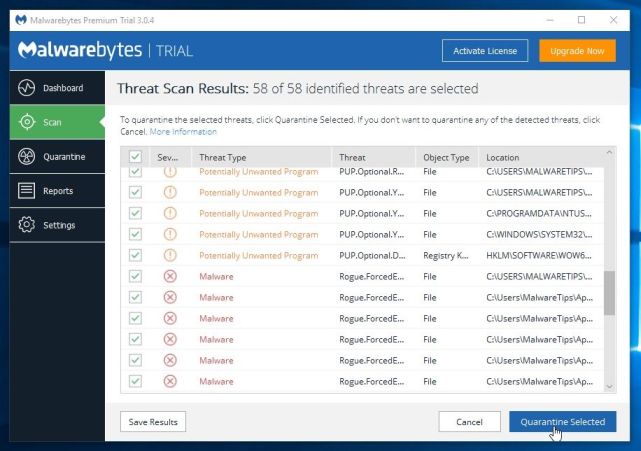
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes Anti-Malware has detected.
To remove the malicious programs that Malwarebytes has found, click on the “Quarantine Selected” button.
- Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found.
To complete the malware removal process, Malwarebytes may ask you to restart your computer.
When the malware removal process is complete, you can close Malwarebytes Anti-Malware and continue with the rest of the instructions.
STEP 4: Double-check for malicious programs with HitmanPro
HitmanPro can find and remove malware, adware, bots, and other threats that even the best antivirus suite can oftentimes miss. HitmanPro is designed to run alongside your antivirus suite, firewall, and other security tools.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - When HitmanPro has finished downloading, double-click on the “hitmanpro” file to install this program on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- When the program starts you will be presented with the start screen as shown below. Now click on the Next button to continue with the scan process.
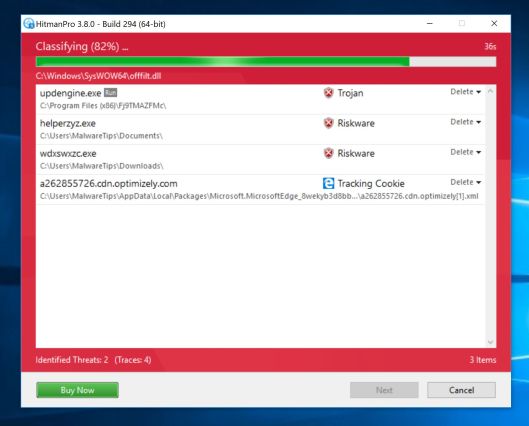
- HitmanPro will now begin to scan your computer for malware.
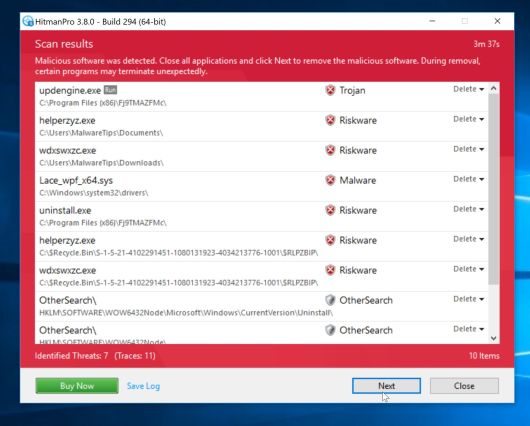
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
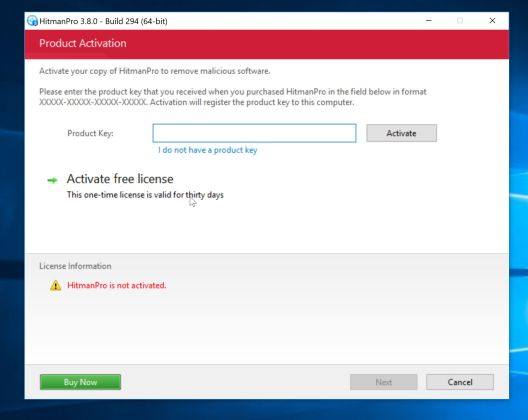
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
When the process is complete, you can close HitmanPro and continue with the rest of the instructions.
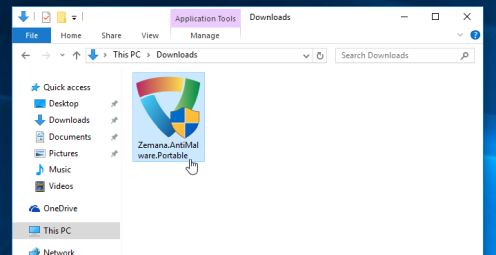
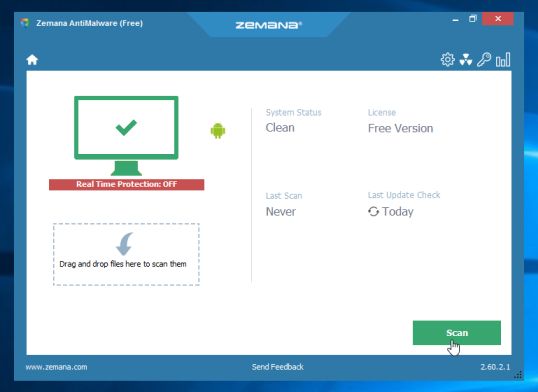
(OPTIONAL) STEP 5: Use Zemana AntiMalware Portable to remove ZeroAccess rootkit
This step should be performed only if your issues have not been solved by the previous steps.
- You can download Zemana AntiMalware Portable from the below link:
ZEMANA ANTIMALWARE PORTABLE DOWNLOAD LINK (This link will open a new web page from where you can download “Zemana AntiMalware Portable”) - Double-click on the file named “Zemana.AntiMalware.Portable” to perform a system scan with Zemana AntiMalware Free.
You may be presented with a User Account Control dialog asking you if you want to run this program. If this happens, you should click “Yes” to allow Zemana AntiMalware to run.
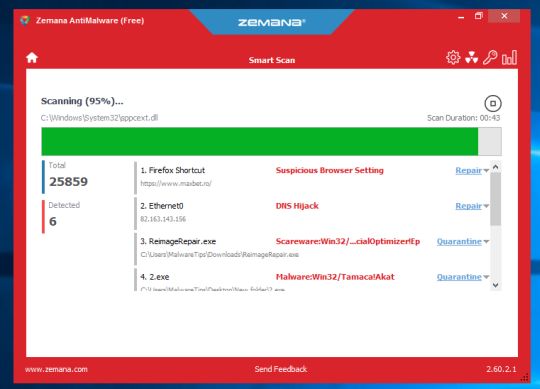
- When Zemana AntiMalware will start, click on the “Scan” button to perform a system scan.
- Zemana AntiMalware will now scan your computer for malicious programs. This process can take up to 10 minutes.
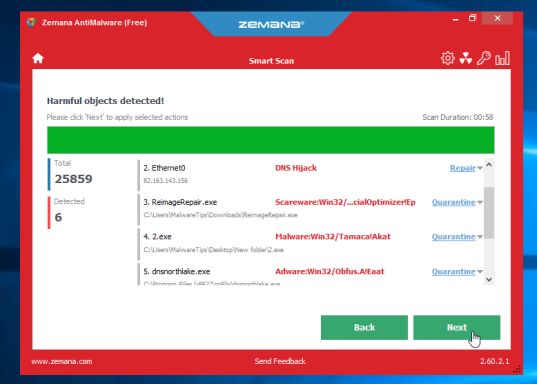
- When Zemana has finished finished scanning it will show a screen that displays any malware that has been detected. To remove all the malicious files, click on the “Next” button.
Zemana AntiMalware will now start to remove all the malicious programs from your computer.















AWESOME!!!!
Hello,
Yes, you can skip the Combofix scan, and run it later if need it.
Lets check if you really have a ZeroAccess rootkit:
Lets run a scan with ESETSirefefCleaner tool:
1.Click the link below to download the ESETSirefefCleaner tool, and save the file to your Desktop.
ESET SIREFEFCLEANER TOOL DOWNLOAD LINK : http://download.eset.com/special/ESETSirefefCleaner.exe
2.From your Desktop, double-click ESETSirefefCleaner utility. If security notifications appear, click Continue or Run.
3.The message “Win32/Sirefef.EV found in your system” will be displayed If an infection is found. Press Y on your keyboard to remove the infection.
4.Once the tool has run, you will be prompted to restore system services after you restart your computer. Press Y on your keyboard to restore system services and restart your computer.
5.Once your computer has restarted, if you are presented with a security notification click Yes or Allow.
6.Click Yes at the ESET Services Repair tool window.
7.Once the ESET Services Repair process is complete, you will again be prompted to restart your computer, to do so click Yes.
Next, please run a scan with the other tools from this article.
Stay safe!
Excellent – even Eset found 4 the others had missed!!
Great article!!!. AVG found 3 Rootkit viruses on all 3 of our computers. Can anyone tell me……should reinstall all of our operating systems, or are they safe now.
We also have an android (phone) and kindle that were regularly plugged in to one or more of the infected machines and a Apple/macbook. The Android, Kindle and Macbook were all scanned but the scanners returned that “there were no viruses detected”.
Am I safe, or should I go forward with (reinstallation hell) reinstalling all of my OS’s.
I don’t know what to do about the devices as they would have to be reinstalled via manufacture.
Any help would be greatly appreciated. This feels like a nightmare. Help!!!!!
ComboFix had deleted basically all my program files. I had to do a System Restore to earlier today because I had no web browser to get back online. Does that mean the virus had spread everywhere already? Is it possible to skip step 2 and move on?
Hello danielle,
That’s very strange….Yes,skip step 2 and go ahead with the other steps!
First off, THANK YOU so much for all your help. It has gotten me part way through solving my PC’s issues. Unfortunately, I’m experiencing problems with running some of these tools. Here’s what I know:
A threat identified as ZeroAccess by McAfee Labs’ Rootkit Remover tool has completely disabled my Total Protection software, corrupted the DAT files and, possibly, even disabled my Windows XP firewall. McAfee’s standalone tools are about as effective as their virus protection which, in the case of my PC, is not at all.
TDSS Killer found and removed 14 items, none of which were ZeroAccess, unless it is going by another name. Rogue Killer will not run. It claims that it is missing a driver. ComboFix found and did a lot of things that I don’t understand. Malwarebytes scanned everything and found nothing. Hitman Pro found and removed 84 tracking cookies. Stinger found nothing. And, like McAfee’s Rootkit Remover, Symantec’s Zero Access Fix Tool doesn’t work.
Right now, I’m in the process of downloading ESET’s signature database (I’m on my Smartphone and doing everything on my PC in Safe Mode with Networking), but I’m not sure it will work. It’s detecting my McAfee Total Protection, even though its been disabled both by me and the infection. I know the UI settings I see, when the program states that it’s on, are false. In the settings window, every option has been hijacked and is grayed out.
I really think that I need to get Rogue Killer, or something like it, to work. ESET is now scanning. So far, no threats have been found. When ESET is done, I plan to unpack and run the Emsisoft Emergency Kit.
All the tools I’m using were downloaded one after the other, before beginning the steps to remove ZeroAccess from my PC. I thought that, in the event that I lost and could not recover web access, at least some of the tools might work.
Please, help. I’m open to any and all advice. I’m even considering uninstalling and re-installing Total Protection, even though I must do it from McAfee’s site. I’ve not yet spoken to their Tech Support. In the past, they’ve proven fairly useless. I think they’re interested mainly in selling services, not providing them.
Thank you,
Geri
Hello Geri,
What’s the current status after the ESET scan?What issues are you experiencing?
ESET found and removed three JAVA exploit variant trojans, Agent.F and A.B. However, it did not find ZeroAccess, which McAfee’s ineffective Rootkit Removal Tool claims is still in my PC; and my McAfee Total Protection is still wonky. I’m going to unpack and try the Emsisoft next. All scanners, but McAfee’s RMT, are reporting my system as clean. This thing is a bear! I’ll let you know what happens, if I don’t chuck my CPU out a window first.
Followed the instructions in the guide, within two steps the PC was able to do Microsoft updates again. ZeroAccess Rootkit virus/trojans removed. Completed the full the regimen of exercises, PC now back to normal. Great information to have when you run into this type of trouble.
Thank you SO much! I thought I had gotten rid of this frickin virus, but it sneaked back I guess. I think it’s finally gone this time, and your instructions were so clear and easy to follow.
I have run all of this step by step. when i ran Kaspersky, Combo fix, Rouge killer, malwarebytes, hitman pro, they all found the viruses and said they either deleted or quarantined them and i started to run the eset scanner. When i ran the eset scanner it was still showing a lot of the viruses on my laptop and i waited 10 and a half hours for it to finish scanning but it was stuck at 28%. i stoped it and started my computer over and started everything over starting with kaspersky and as i went through each program none of them detected any threats so i thought i was in the clear until i started running the eset scanner again. as it ran it was still finding all the viruses. I was going to go ahead and do the emisoft but have no clue how to unpack it and im not sure if its what i need for the viruses eset keeps finding.
Here is what eset shows that i have: C:\ProgramData\Tarma Installer\{889DF117-14D1-44EE-9F31-C5FB5D47F68B}\_Setupx.dll a variant of Win32/Adware.Yontoo.B application
C:\ProgramData\Tarma Installer\{DA00D550-BB91-4A26-AAE5-9172D626CAAE}\_Setupx.dll a variant of Win32/Adware.Yontoo.B application
etc
is my laptop just too far gone to fix?? please help!!!
Hello Monica,
Apart from this ESET detection on your computer, how is everything running??Any issues?
Let remove the adware from your computer computer:
Please download AdwCleaner by Xplode onto your desktop.
Waiting your reply to tell me if everything is ok… :)
Hi Stelian Pilici!!
Wow you guys respond fast, I’m used to having to wait days to get a reply on other websites. I downloaded the adwclener.exe and it did exactly what you said it would. I’m running the ESET Scanner again to see if there is anymore adware on my laptop.
My laptop is running fine it even runs bit faster esp when its booting up but I’m pretty sure i still have the redirectware because when i use search engines i cant click on a site without it redirecting me to another page.
Before i ran the Kaspersky, Combo fix, Rouge killer, malwarebytes, hitman pro, my firewall was down and i couldn’t put it back up but afterwords i could control all of my security settings and i no longer have that problem.
the only other thing is when i go to uninstall things an error message pops up that says The windows installer can not be accessed.
Also I’m not sure if it matters but I’m doing everything through sandboxie now, i don’t use my web browser without it. I just thought id ask you guys if that’s a good idea or if that could be causing any problems I’m unaware of.
Thank you guys so much for taking the time out to help!!!
The ESET scanner just finished and didn’t find any threats on my computer but i still have problems with being redirected to another site when i use the search engine and cant uninstall anything.
Hello Monica,
Can you please start a thread in our Malware Removal Assistance forum, so that we may take a look at the Combofix logs and try to help you: http://malwaretips.com/Forum-Malware-Removal-Assistance
Hello,
God bless you! I bought an expensive laptop and i care it really hard. I tried to download a movie and zeroacess sneak into my system. I was getting mad and you saved my life! Thank you again and again!
Just want to say a big “Thank You” for providing this step-by-step guide to removing the ZeroAccess rootkit. My anti-virus program and it’s so-called Support team [which shall remain nameless, to save them embaressment – but I’ve passed on your link, so they can learn what real ‘Support’ looks like ; -) ] were incapable of detecting, let alone removing this vicous and very damaging little cancer bug. So thank you very much for all your help! : -)
Well, I don’t even finished the process yet but my problem is already solved! I was unable to acess windows firewall and that prevented me from saving the changes made in the net discovery options on windows.
I’ in the malware bytes step now but I just noticed that my firewall is working again!
The only nitpick is tha my network icon in the tray is showing that I’m not connected, but I can live with that!
Thanks a lot!!!
Well, took like two days to run everything but it seems like I’m finally clean. It was a little scary, considering that every process seemed to find something. Thanks, the guide was unbelievably thorough and helpful. Now I can finally get back to the problem of figuring out why Youtube and Netflix aren’t working on my computer (which seems to have to do with not being able to install a more recent version of Silverlight, as it keeps claiming that my computer isn’t compatible with the program).
I had to write to THANK YOU for saving me a lot of time and money with your articulate explanation of how to get rid of the win64.zaccess.a virus. It took most of an entire day, but I followed every single direction you gave to a “t”, and the virus is gone. I figured I’d have to pay to have the OS completely removed and reinstalled. I am very grateful for the help, and for no charge – greatly appreciated.
My trojan was removed at the first step itself. Though instead of calling the file as given in the guide, it called it zeroaccess
I downloaded TDSSkiller onto another computer. It runs happily on that. I renamed it and burnt it to a discc. Inserting that into my infected computer, I click on the icon. “User Access Control” asks if I want it to run. I get a short hour glass, and nothing else happens. When I try again, the whole computer crashes instantly to zero. Its impressively quick.
A complete reboot restores the system to “normal”.
HELP. What should I do now?
Many Thanks.
Hello Nigel,
Can you please go ahead and run Combofix and copy/paste the log in your next reply!
I wish it was that easy. I ran combo fix a couple of days ago. I do not know where the report is now. I have just tried downloading again, and started to run it. It got to the end of backing up registry files. I then got six warnings “iexplore.exe. A problem has caused the program to stop working correctly. etc etc.” Then two more “internet explorer has stopped working.” finally I got “You cannot rename Combifix as Combifix (1). After that nothing.
Two days ago, I ran Rogue killer:
Log one: RogueKiller V8.4.0 [Dec 12 2012] by Tigzy
mail : tigzyRKgmailcom
Feedback : http://www.geekstogo.com/forum/files/file/413-roguekiller/
Website : http://tigzy.geekstogo.com/roguekiller.php
Blog : http://tigzyrk.blogspot.com/
HELP PLEASE!!!!!!
Thank you!!
Hello Nigel,
You have a serious infection which needs several steps to be completly removed, so because this is just a basic comment section, I’ll ask you to start a thread in our Malware Removal Assistance forum, where we can properly guide you through all the steps!
Stay safe and see you on the forums!
I never comment… but on this occasion I absolutely must. Thank you for taking the time to create such a useful and well written guide. All of the links and downloads worked beautifully, the software worked incredibly well without any issues and without asking me to pay to get them to clean up what they found. Without this quality of information I would probably have not got my PC back to the exceptional health it is now enjoying. Brilliant job and thanks to everyone involved in creating these products.