When you open the Task Manager on your Windows computer, you may come across a process called “Service Host: CNG Key Isolation” running in the background. This process might raise some questions and concerns, especially if you are not familiar with it. In this article, we will explore what the CNG Key Isolation process is, why it is running in Task Manager, and its significance in the Windows operating system.

Understanding the CNG Key Isolation Process
The CNG Key Isolation process, also known as “KeyIso,” is a crucial component of the Windows operating system. It is responsible for managing and isolating cryptographic keys and operations on a computer. Cryptographic keys are essential for secure communication, data encryption, and digital signatures.
KeyIso provides a secure environment for cryptographic operations by running in a separate process, isolated from other system processes. This isolation ensures that the keys and cryptographic operations are protected from unauthorized access and potential attacks.
Why is the CNG Key Isolation Process Running in Task Manager?
Seeing the CNG Key Isolation process running in Task Manager is completely normal and expected. It is a system process that runs in the background to provide essential cryptographic services to various applications and processes on your computer.
Many applications and services on Windows rely on cryptographic operations for secure communication and data protection. The CNG Key Isolation process acts as a mediator between these applications and the underlying cryptographic infrastructure of the operating system.
By running as a separate process, the CNG Key Isolation process ensures that cryptographic keys and operations are protected from potential vulnerabilities in other system processes. It also allows for better resource management and isolation of cryptographic operations, enhancing the overall security of the system.
Significance of the CNG Key Isolation Process
The CNG Key Isolation process plays a vital role in maintaining the security and integrity of cryptographic operations on a Windows computer. Here are some key reasons why it is significant:
- Secure Key Storage: The CNG Key Isolation process securely stores cryptographic keys, preventing unauthorized access and tampering.
- Isolation of Cryptographic Operations: By running in a separate process, the CNG Key Isolation process isolates cryptographic operations from other system processes, reducing the risk of key leakage or compromise.
- Protection against Attacks: The isolation provided by the CNG Key Isolation process helps protect cryptographic keys and operations from potential attacks, such as keyloggers or memory scraping.
- Support for Cryptographic Algorithms: The CNG Key Isolation process supports a wide range of cryptographic algorithms, ensuring compatibility with various applications and services.
Should You Be Concerned?
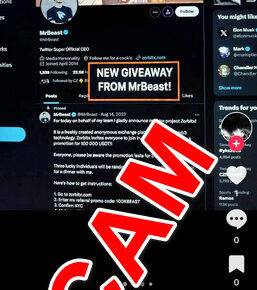
While the presence of the CNG Key Isolation process in Task Manager is normal, it is essential to be cautious of any unusual behavior or high resource usage associated with it. In some rare cases, malware or malicious software may disguise itself as the CNG Key Isolation process to evade detection.
If you suspect any malicious activity or experience performance issues, it is recommended to scan your computer for viruses and malware. Malwarebytes Free is a reliable and effective tool for scanning and removing malware from your system.
Conclusion
The CNG Key Isolation process, also known as “KeyIso,” is an essential component of the Windows operating system. It provides a secure environment for cryptographic operations and ensures the protection of cryptographic keys. Its presence in Task Manager is normal and signifies the proper functioning of cryptographic services on your computer.
Understanding the significance of the CNG Key Isolation process helps you appreciate its role in maintaining the security and integrity of your system. By isolating cryptographic operations and securely storing keys, it enhances the overall security posture of your Windows computer.
Remember to stay vigilant and monitor any unusual behavior associated with the CNG Key Isolation process. If you suspect any malicious activity, perform a thorough scan using a reliable antivirus tool like Malwarebytes Free to ensure the safety of your system.