Trojan:JS/Seedabutor.C is malicious Java code that exploits a vulnerability in the Java Runtime Environment component of Oracle Java SE and Java for Business that allows the execution of arbitrary code.
Trojan:JS/Seedabutor.C was developed in Russia and is used by hackers to infect computers with old versions of Java via malicious scripts planted on compromised websites. When the page is visited by a user running vulnerable versions of Java, the malicious Java class runs and allows the execution of arbitrary code.
The JavaScript is usually found in webpages compromised through SQL Injection attacks or through Blackhat search engine optimization (SEO) poisoning. This detection may also be triggered if the webpage containing this script is stored in the browser’s cache.
- Trojan:JS/Seedabutor.C – Virus Removal Guide
- STEP 1: Delete Trojan:JS/Seedabutor.C Temporary Internet files with Temp File Cleaner
- STEP 2: Remove Trojan:JS/Seedabutor.C infection with Kaspersky TDSSKiller
- STEP 3 : Remove Trojan:JS/Seedabutor.C malicious files with RogueKiller
- STEP 4: Remove Trojan:JS/Seedabutor.C virus with Malwarebytes Anti-Malware Free
- STEP 5: Remove the Trojan:JS/Seedabutor.C infection with HitmanPro
- STEP 3: Remove Trojan:JS/Seedabutor.C redirect with AdwCleaner and Junkware Removal Tool
The Trojan:JS/Seedabutor.C is a dangerous threat that has been circulating for several years. In the time that Trojan:JS/Seedabutor.C has been in the wild there have been a number of revisions, with modifications to its functionality, infection strategy and its persistence mechanisms on an infected machine. However, the core purpose has remained: to assume full control of the machine by adding it to the ZeroAccess botnet and to monetize the new asset by downloading additional malware.
Primarily, Trojan:JS/Seedabutor.C is a kernel-mode rootkit, similar in ethos to the TDL family of rootkits. It uses advanced techniques to hide its presence, is capable of functioning on both 32 and 64-bit flavors of Windows from a single installer, contains aggressive self defense functionality and acts as a sophisticated delivery platform for other malware.
The Trojan:JS/Seedabutor.C virus is distributed through several means. Malicious websites, or legitimate websites that have been hacked, can infect your machine through exploit kits that use vulnerabilities on your computer to install this Trojan without your permission of knowledge.
Another method used to propagate this type of malware is spam email containing infected attachments or links to malicious websites. Cyber-criminals spam out an email, with forged header information, tricking you into believing that it is from a shipping company like DHL or FedEx. The email tells you that they tried to deliver a package to you, but failed for some reason. Sometimes the emails claim to be notifications of a shipment you have made. Either way, you can’t resist being curious as to what the email is referring to – and open the attached file (or click on a link embedded inside the email). And with that, your computer is infected with the Trojan:JS/Seedabutor.C virus.
The threat may also be downloaded manually by tricking the user into thinking they are installing a useful piece of software, for instance a bogus update for Adobe Flash Player or another piece of software.
The Trojan:JS/Seedabutor.C virus is also prevalent on peer-to-peer file sharing websites and is often packaged with pirated or illegally acquired software.
When the computer is infected with the Trojan:JS/Seedabutor.C virus, if you visit a website containing this malicious JavaScript, the browser is redirected to dsparking.com/?epl=.
This JavaScript is usually found in webpages compromised through SQL Injection attacks or through Blackhat search engine optimization (SEO) poisoning. This detection may also be triggered if the webpage containing this script is stored in the browser’s cache.
Trojan:JS/Seedabutor.C is a dangerous threat that uses advanced stealth techniques in order to hinder its detection and removal. As a consequence of being infected with this threat, you may need to repair and reconfigure some Windows security features.
Trojan:JS/Seedabutor.C – Virus Removal Guide
This page is a comprehensive guide, which will remove the Trojan:JS/Seedabutor.C infection from your your computer. Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
STEP 1: Delete Trojan:JS/Seedabutor.C Temporary Internet files with Temp File Cleaner
STEP 2: Remove Trojan:JS/Seedabutor.C infection with Kaspersky TDSSKiller
STEP 3: STEP 3 : Remove Trojan:JS/Seedabutor.C malicious files with RogueKiller
STEP 4: Remove Trojan:JS/Seedabutor.C virus with Malwarebytes Anti-Malware Free
STEP 5: Remove the Trojan:JS/Seedabutor.C infection with HitmanPro
STEP 6: Remove Trojan:JS/Seedabutor.C redirect with AdwCleaner and Junkware Removal Tool
STEP 1: Delete Trojan:JS/Seedabutor.C Temporary Internet files with Temp File Cleaner
This threat may be present in your Temporary Internet Files folder. We recommend that you delete your temporary Internet files to prevent the persistent detection of this threat from within the Temporary Internet Files folder.
- You can download Temp File Cleaner from the below link:
TEMP FILE CLEANER DOWNLOAD LINK (This link will automatically download Temp File Cleaner (TFC.exe) on your computer) - Right click on the TFC.exe icon, and if you using Windows XP select Run As, or if you are a Windows Vista, 7 or 8 user, select Run as Administrator.
![Temp File Cleaner icon [Image: TFC.exe icon]](//malwaretips.com/blogs/wp-content/uploads/2013/05/temp-file-cleaner-icon.jpg)
If Windows prompts you as to whether or not you wish to run TFC.exe, please allow it to run. - Close your browser and save any other documents that you might have open, then click the Start button to begin the removal process.
![Click on Start to remove Trojan:JS/Seedabutor.C [Image: Temp File Cleaner starting removal process]](//malwaretips.com/blogs/wp-content/uploads/2013/05/temp-file-cleaner-utility.jpg)
Depending on how often you clean temp files, execution time should be anywhere from a few seconds to a minute or two. Let it run uninterrupted to completion. - Once Temp File Cleaner has completed its task, it should reboot your computer. If it does not, please manually reboot the machine yourself to ensure a complete clean.
![Temp File Cleaner Report [Image: Temp File Cleaner logs]](//malwaretips.com/blogs/wp-content/uploads/2013/05/temp-file-cleaner-log.jpg)
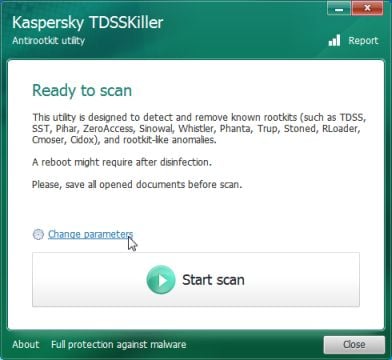
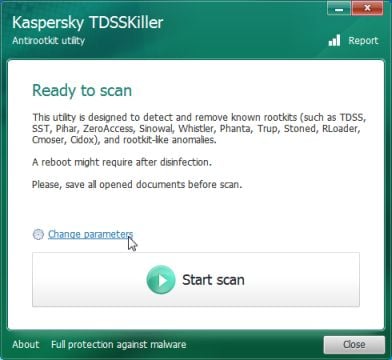
STEP 2: Remove Trojan:JS/Seedabutor.C infection with Kaspersky TDSSKiller
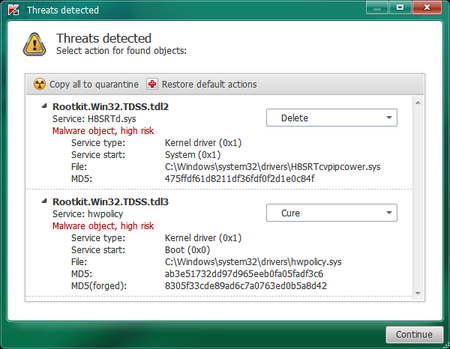
As part of its self defense mechanism, Trojan:JS/Seedabutor.C will install a rootkit on the infected computer.In this first step, we will run a system scan with Kaspersky TDSSKiller to remove this rookit.
- Please download the latest official version of Kaspersky TDSSKiller.
KASPERSKY TDSSKILLER DOWNLOAD LINK(This link will automatically download Kaspersky TDSSKiller on your computer.) - Before you can run Kaspersky TDSSKiller, you first need to rename it so that
you can get it to run. To do this, right-click on the TDSSKiller.exe icon and select Rename.
Edit the name of the file from TDSSKiller.exe to iexplore.exe, and then double-click on it to launch. - Kaspersky TDSSKiller will now start and display the welcome screen and we will need to click on Change Parameters.
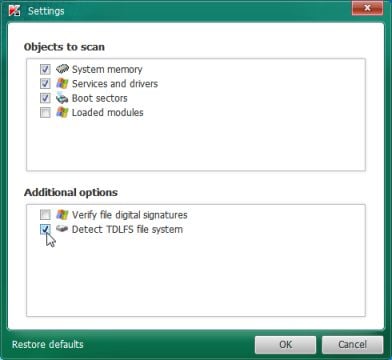
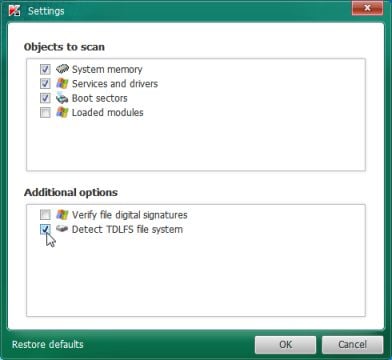
- In the new open window,we will need to enable Detect TDLFS file system, then click on OK.
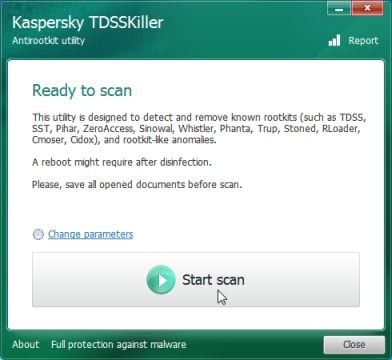
- Next,we will need to start a scan with Kaspersky, so you’ll need to press the Start Scan button.
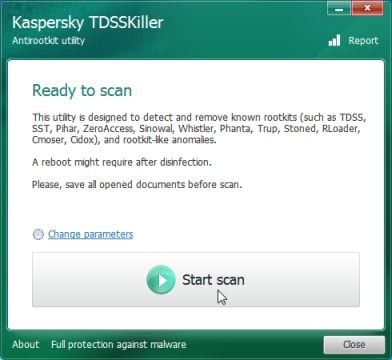
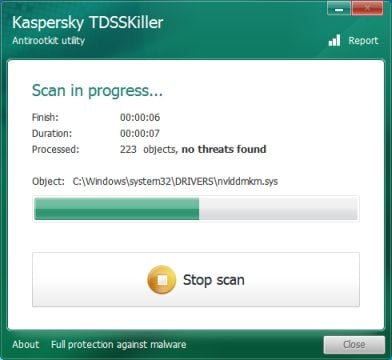
- Kaspersky TDSSKiller will now scan your computer for Trojan:JS/Seedabutor.C infection.
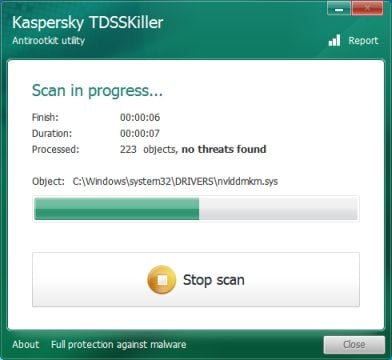
- When the scan has finished it will display a result screen stating whether or not the infection was found on your computer. If it was found it will display a screen similar to the one below.
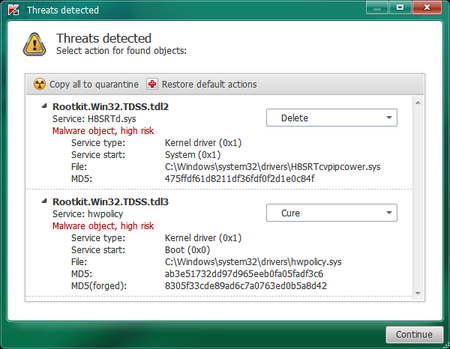
- To remove the infection simply click on the Continue button and TDSSKiller will attempt to clean the infection.A reboot will be require to completely remove any infection from your system.
STEP 3 : Remove Trojan:JS/Seedabutor.C malicious files with RogueKiller
Trojan:JS/Seedabutor.C has added some malicious registry keys to your Windows installation, to remove them we will need to perform a scan with RogueKiller.
- You can download RogueKiller from the below link.
ROGUEKILLER DOWNLOAD LINK (This link will automatically download RogueKiller on your computer) - Double click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds and then you can click the Start button to perform a system scan.
![Click on the Start button to perform a system scan [Image: RogueKiller while scanning]](//malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-1.png)
- After the scan has completed, press the Delete button to remove any malicious registry keys.
![Press Delete to remove the malicious registry keys [Image: RogueKiller removing Trojan:JS/Seedabutor.C]](//malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-2.png)
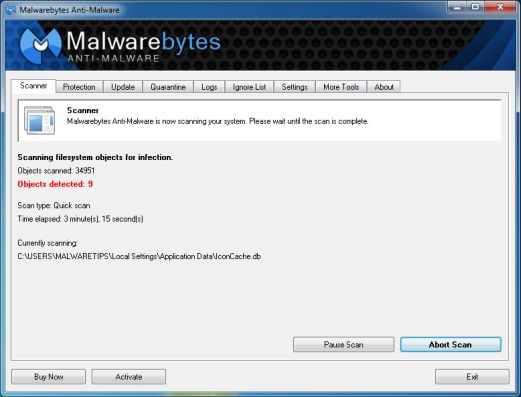
STEP 4: Remove Trojan:JS/Seedabutor.C virus with Malwarebytes Anti-Malware Free
Malwarebytes Anti-Malware Free is a powerful on-demand scanner which will remove Trojan:JS/Seedabutor.C malicious files from your computer.
- You can download Malwarebytes Anti-Malware Free from the below link, then double-click on the icon named mbam-setup.exe to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK(This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process, then at the last screen click on the Finish button.
![Malwarebytes Anti-Malware installation screen [Image: Malwarebytes Anti-Malware final installation screen]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
- On the Scanner tab, select Perform quick scan, and then click on the Scan button to start searching for the Trojan:JS/Seedabutor.C malicious files.
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
- Malwarebytes’ Anti-Malware will now start scanning your computer for Trojan:JS/Seedabutor.C virus as shown below.
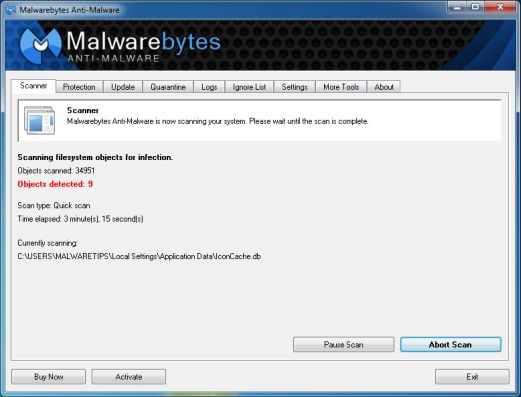
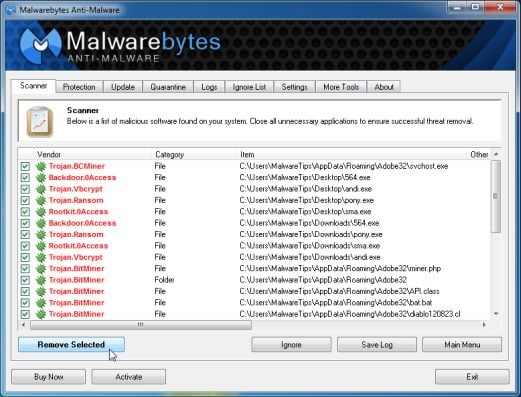
- When the Malwarebytes Anti-Malware scan has finished, click on the Show Results button.
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
- You will now be presented with a screen showing you the computer infections that Malwarebytes Anti-Malware has detected. Make sure that everything is Checked (ticked), then click on the Remove Selected button.
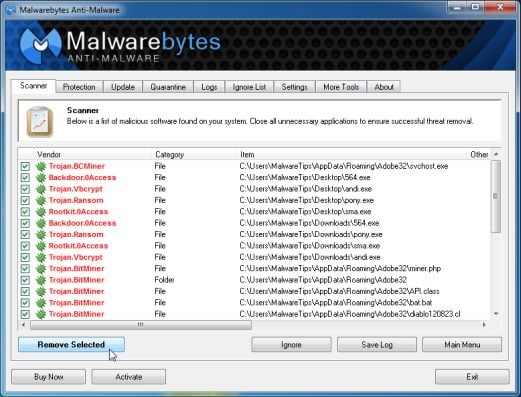
- Once your computer will restart, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats.
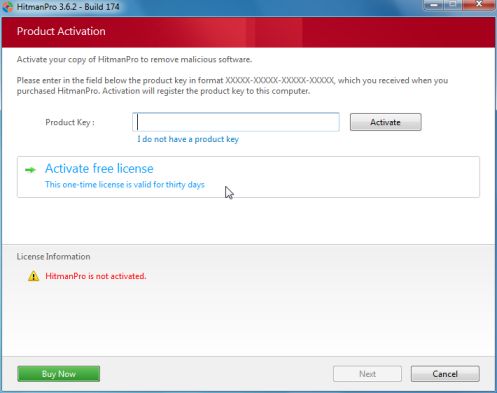
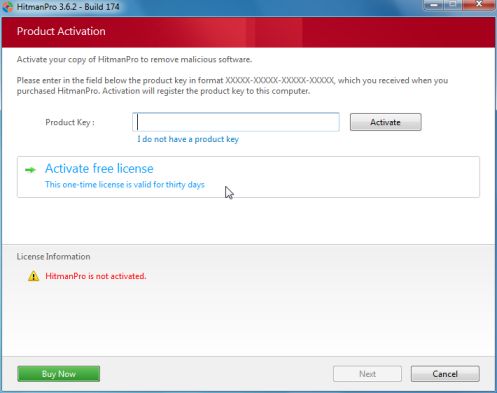
STEP 5: Remove the Trojan:JS/Seedabutor.C infection with HitmanPro
HitmanPro is a cloud on-demand scanner, which will scan your computer with 5 antivirus engines for the Trojan:JS/Seedabutor.C virus and was deleted” infection.
- Download HitmanPro from the below link, then double-click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.

- HitmanPro will start scanning your computer for Trojan:JS/Seedabutor.C malicious files as seen in the image below.

- Once the scan is complete,you’ll see a screen which will display all the infected files that this utility has detected, and you’ll need to click on Next to remove this malicious files.

- Click Activate free license to start the free 30 days trial and remove all the malicious files from your computer.
STEP 3: Remove Trojan:JS/Seedabutor.C redirect with AdwCleaner and Junkware Removal Tool
Run a computer scan with AdwCleaner to remove Trojan:JS/Seedabutor.Cr
The AdwCleaner utility will scan your computer for Trojan:JS/Seedabutor.C malicious files and registry keys, that may have been installed on your computer without your knowledge.
- You can download AdwCleaner utility from the below link.
ADWCLEANER DOWNLOAD LINK (This link will automatically download AdwCleaner on your computer) - Before starting AdwCleaner, close all open programs and internet browsers, then double-click on the AdwCleaner icon.
![AdwCleaner Icon [Image: AdwCleaner Icon]](//malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-icon.jpg)
If Windows prompts you as to whether or not you wish to run AdwCleaner, please allow it to run. - When the AdwCleaner program will open, click on the Search button as shown below.
![Click on Search to scan for Trojan:JS/Seedabutor.C [Image: AdwCleaner scanning for Trojan:JS/Seedabutor.C]](//malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-scan.jpg)
The program will now start to search for Trojan:JS/Seedabutor.C malicious files that may be installed on your computer. When it has finished it will display a notepad screen that contains a log file of all the Mediaget extensions, files, and registry keys that have been detected. - To remove the Trojan:JS/Seedabutor.C malicious files that were detected in the previous step, please click on the Delete button on the AdwCleaner screen.
![Click on Delete to remove Trojan:JS/Seedabutor.C virus [Image: Adwcleaner removing Trojan:JS/Seedabutor.C]](//malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-virus-removal.jpg)
AdwCleaner will now prompt you to save any open files or data as the program will need to reboot the computer. Please do so and then click on the OK button.
Remove Trojan:JS/Seedabutor.C hijack with Junkware Removal Tool
Junkware Removal Tool is a powerful utility, which will remove Trojan:JS/Seedabutor.C virus from Internet Explorer, Firefox or Google Chrome.
- You can download the Junkware Removal Tool utility from the below link:
JUNKWARE REMOVAL TOOL DOWNLOAD LINK (This link will automatically download the Junkware Removal Tool utility on your computer) - Once Junkware Removal Tool has finished downloading, please double-click on the JRT.exe icon as seen below.
![Double-click on the Junkware Removal Tool utility [Image: Junkware Removal Tool]](//malwaretips.com/blogs/wp-content/uploads/2013/06/Junkware-icon.jpg)
If Windows prompts you as to whether or not you wish to run Junkware Removal Tool, please allow it to run. - Junkware Removal Tool will now start, and at the Command Prompt, you’ll need to press any key to perform a scan for the Trojan:JS/Seedabutor.C.
![Junkware Removal Tool scanning for Trojan:JS/Seedabutor.C [Image: Junkware Removal Tool scanning for Trojan:JS/Seedabutor.C virus]](//malwaretips.com/blogs/wp-content/uploads/2013/06/junkware-removal-tool.jpg)
Please be patient as this can take a while to complete (up to 10 minutes) depending on your system’s specifications. - When the scan Junkware Removal Tool will be completed, this utility will display a log with the malicious files and registry keys that were removed from your computer.
![Junkware Removal Tool final log [Image: Junkware Removal Tool final log]](//malwaretips.com/blogs/wp-content/uploads/2013/06/Junkware-log.jpg)

![Click on Start to remove Trojan:JS/Seedabutor.C [Image: Temp File Cleaner starting removal process]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/temp-file-cleaner-utility.jpg)
![Temp File Cleaner Report [Image: Temp File Cleaner logs]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/temp-file-cleaner-log.jpg)
![Click on the Start button to perform a system scan [Image: RogueKiller while scanning]](http://malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-1.png)
![Press Delete to remove the malicious registry keys [Image: RogueKiller removing Trojan:JS/Seedabutor.C]](http://malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-2.png)
![Malwarebytes Anti-Malware installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)



![Click on Search to scan for Trojan:JS/Seedabutor.C [Image: AdwCleaner scanning for Trojan:JS/Seedabutor.C]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-scan.jpg)
![Click on Delete to remove Trojan:JS/Seedabutor.C virus [Image: Adwcleaner removing Trojan:JS/Seedabutor.C]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-virus-removal.jpg)
![Junkware Removal Tool scanning for Trojan:JS/Seedabutor.C [Image: Junkware Removal Tool scanning for Trojan:JS/Seedabutor.C virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/junkware-removal-tool.jpg)
![Junkware Removal Tool final log [Image: Junkware Removal Tool final log]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Junkware-log.jpg)

