If your computer is locked, and you are seeing a “This computer has been blocked!“ notification from the U.S. Department of Homeland Security, then your computer is infected with a piece of malware known as Trojan Urausy.
This threat is distributed through several means. Malicious websites, or legitimate websites that have been compromised, may drop this Trojan onto a compromised computer. This drive-by-download often happens surreptitiously. Another method used to propagate this type of malware is spam email containing infected attachments or links to malicious websites. The threat may also be downloaded manually by tricking the user into thinking they are installing a useful piece of software.
The U.S. Department of Homeland Security virus is also prevalent on peer-to-peer file sharing websites and is often packaged with pirated or illegally acquired software.
Once installed on your computer, the U.S. Department of Homeland Security virus will display a bogus notification that pretends to be from a law enforcement agency, and states that your computer has been blocked due to it being involved with the distribution of pornographic material, SPAM and copyrighted content.
The U.S. Department of Homeland Security virus will lock you out of your computer and applications, so whenever you’ll try to log on into your Windows operating system or Safe Mode with Networking, it will display instead a lock screen asking you to pay a non-existing fine of $300 in the form of a Green dot MoneyPak code.
Furthermore, to make this alert seem more authentic, this virus also has the ability to access your installed webcam, so that the bogus U.S. Department of Homeland Security notification shows what is happening in the room.
The U.S. Department of Homeland Security virus locks the computer and, depending on the user’s current location, displays a localized webpage that covers the entire desktop of the infected computer and demands payment for the supposed possession of illicit material.
Cyber criminals often updated the design of this lock screen, however you should always keep in mind that the police will never lock down your computer or monitor your online activities.
The message displayed by the threat can be localized depending on the user’s location, with text written in the appropriate language:
U.S. Department of Homeland Security
National Cyber Security Division
This computer has been blocked
THE WORK OF YOUR COMPUTER HAS BEEN SUSPENDED ON THE GROUNDS OF THE VIOLATION OF THE LAW OF THE UNITED STATES OF AMERICA.
Article 184. Pornography involving children
Imprisonment for the term of up to 10-15 years(The use or distribution of pornography material)
Artticle 171. Copyright
Imprisonment for the term of up to 2-5 years. (The use or sharing copyrighted files)
Article 113. The use of unlicensed software
Imprisonment for the term of up to 2 years (The use of unlicensed software)
To unlock the computer you are obliged to pay a fine of $300. You must pay the fine through MoneyPAK.
You have 48 hours to pay the fine. If the fine has not been paid, you will become the subject of criminal prosecution without the right to pay the fine. The Department for the Fight Against Cyberactivity will confiscate your computer and take You to Court.
The U.S. Department of Homeland Security lock screen is a scam, and you should ignore any alerts that this malicious software might generate.
Under no circumstance should you send any money via MoneyPak to these cyber criminals, and if you have, you can should request a refund, stating that you are the victim of a computer virus and scam.
U.S. Department of Homeland Security lock screen – Virus Removal Guide
This page is a comprehensive guide, which will remove the Homeland Security infection from your your computer. Please perform all the steps in the correct order. If you have any questions or doubt at any point STOP and ask for our assistance.
The Homeland Security will start automatically when you login to your computer and display its screen locker so that you are unable to access your computer, therefore we will need to remove this infection by using one of the below methods:
OPTION 1: Remove Homeland Security lock screen virus with System Restore
OPTION 2: Remove Homeland Security virus with with HitmanPro Kickstart
OPTION 3: Remove Homeland Security virus with Kaspersky Rescue Disk
OPTION 1: Remove Homeland Security lock screen virus with System Restore
System Restore helps you restore your computer’s system files to an earlier point in time. It’s a way to undo system changes to your computer without affecting your personal files, such as e‑mail, documents, or photos.
Because the Homeland Security virus will not allow you to start the computer in Windows regular mode, we will need to start System Restore from the Safe Mode with Command Prompt mode.
STEP 1: Restore Windows to a previous state using System Restore
- Reboot your computer into Safe Mode with Command Prompt. To do this, turn your computer off and then back on and immediately when you see anything on the screen, start tapping the F8 key on your keyboard.
If you are using Windows 8, the trick is to hold the Shift button and gently tap the F8 key repeatedly, this will sometimes boot you into the new advanced “recovery mode”, where you can choose to see advanced repair options. On the next screen, you will need to click on the Troubleshoot option, then select Advanced Options and select Windows Startup Settings. Click on the Restart button, and you should now be able to see the Advanced Boot Options screen. - Using the arrow keys on your keyboard, select Safe Mode with Command Prompt and press Enter on your keyboard.
- At the command prompt, type rstrui.exe, and then press ENTER.
Alternatively, if you are using Windows Vista, 7 and 8, you can type: C:\windows\system32\rstrui.exe , and press Enter. And if you are a Windows XP user, type C:\windows\system32\restore\rstrui.exe, then press Enter. - System Restore should start, and you will display also a list of restore points. Try using a restore point created just before the date and time the Homeland Security lock screen virus has infected your computer.
- When System Restore has completed its task, start your computer in Windows regular mode, and perform a scan with Malwarebytes Anti-Malware and HitmanPro, as seen in the next step.
STEP 2: Remove Homeland Security malicious files with Malwarebytes Anti-Malware Free
Even after using System Restore,
- You can download Malwarebytes Anti-Malware Free from the below link, then double-click on the icon named mbam-setup.exe to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK(This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process, then at the last screen click on the Finish button.
- On the Scanner tab, select Perform quick scan, and then click on the Scan button to start searching for the Homeland Security malicious files.
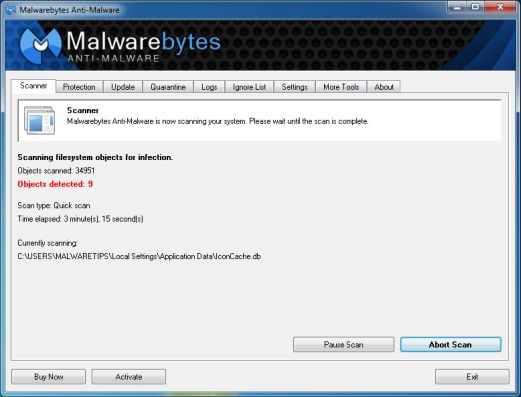
- Malwarebytes’ Anti-Malware will now start scanning your computer for Homeland Security virus as shown below.
- When the Malwarebytes Anti-Malware scan has finished, click on the Show Results button.
- You will now be presented with a screen showing you the computer infections that Malwarebytes Anti-Malware has detected. Make sure that everything is Checked (ticked), then click on the Remove Selected button.
STEP 3: Double-check for the Homeland Security virus with HitmanPro
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a web page from where you can download HitmanPro) - Double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.
Click on the Next button, to install HitmanPro on your computer.
- HitmanPro will now begin to scan your computer for Homeland Security malicious files.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the Next button, to remove Homeland Security virus.
- Click on the Activate free license button to begin the free 30 days trial, and remove all the malicious files from your computer.
OPTION 2: Remove Homeland Security virus with with HitmanPro Kickstart
If you cannot start your computer into Safe Mode with Command Prompt mode, we can use the HitmanPro Kickstart program to bypass Homeland Security lock screen.
As the Homeland Security ransomware infection locks you out of your computer, you will need to create a bootable USB drive that contains the HitmanPro Kickstart program.
We will then boot your computer using this bootable USB drive and use it to clean the infection so that you are able to access Windows normally again.
You will also need a USB drive, which will have all of its data erased and will then be formatted. Therefore, only use a USB drive that does not contain any important data.
- Using a “clean” (non-infected) computer, please download HitmanPro Kickstart from the below link.
HITMANPRO DOWNLOAD LINK (This link will open a download page in a new web page from where you can download HitmanPro Kickstart) - Once HitmanPro has been downloaded, please insert the USB flash drive that you would like to erase and use for the installation of HitmanPro Kickstart. Then double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows).
To create a bootable HitmanPro USB drive, please follow the instructions from this video:
- Now, remove the HitmanPro Kickstart USB drive and insert it into the Homeland Security infected computer.
- Once you have inserted the HitmanPro Kickstart USB drive, turn off the infected computer and then turn it on. As soon as you power it on, look for text on the screen that tells you how to access the boot menu.
The keys that are commonly associated with enabling the boot menu are F10, F11 or F12. - Once you determine the proper key (usually the F11 key) that you need to press to access the Boot Menu, restart your computer again and start immediately tapping that key. Next, please perform a scan with HitmanPro Kickstart as shown in the video below.
- HitmanPro will now reboot your computer and Windows should start normally. Then please Malwarebytes Anti-Malware and HitmanPro, and scan your computer for any left over infections.
OPTION 3: Remove Homeland Security virus with Kaspersky Rescue Disk
If any of the above methods did not clean your infected computer, we can use a Kaspersky Rescue Disk Bootable to clean the Windows registry and to perform a system scan to remove the Homeland Security virus.
To create a bootable Kaspersky Rescue Disk, we will need the following items:
- A clean (non-infected) computer with Internet access
- A blank DVD or CD
- A computer with a DVD or CD burner
STEP 1: Download and create a bootable Kaspersky Rescue Disk CD
- You can download Kaspersky Rescue Disk utility from link below:
KASPERSKY RESCUE DISK DOWNLOAD LINK (This link will automatically download Kaspersky Rescue Disk (kav_rescue_10.iso) on your computer.) - To create the bootable rescue disk, we will need to use the ImgBurn program. You can download ImgBurn from the below link, then install this program.
IMGBURN DOWNLOAD LINK (This link will open a new page from where you can download the ImgBurn program) - Insert your blank DVD or CD in your burner, then start ImgBurn and click on the Write image file to disc button.
- Under Source click on the Browse for file button, then navigate to the location where you previously saved the Kaspersky Rescue Disk utility (kav_rescue_10.iso), then click on the Write button.
That’s it, ImgBurn will now begin writing your bootable Kaspersky Rescue Disk.
STEP 2: Start your computer using the Kaspersky Rescue Disk
- Once you’ve got the Kasperky Rescue Disk in hand, insert it into the infected computer, and turn off and then turn it on again.
- As soon as you power it on, you will see a screen that tells you to press any key to enter the menu, so please tap any key to boot your machine from the Kaspersky Rescue Disk.
- In the next screen, you will need to chose a language, then you click on Kaspersky Rescue Disk. Graphic Mode and press ENTER, to start the Kaspersky Rescue Disk.
STEP 3: Scan your system with Kaspersky Rescue Disk
- Within a few short seconds you should see the full working environment, with the Kaspersky Rescue Disk screen front and center as shown below.
- Switch tabs over to the My Update Center, and then click the Start update button to load the latest anti-virus definitions. Please be patience while this process its completed.
- Switch back over to the Objects Scan tab, select the drives you want to scan, and then click the Start Objects Scan button.
- When Kaspersky Antivirus will detect the Homeland Security virus, you’ll be prompted to select an action. When this happens, please select Quarantine or Delete to remove this infection from your computer.
- When the antivirus scan has completed, you can restart back into Windows regular mode, by clicking on the Kaspersky Start button
(lower left corner), and selecting Restart.
Once your computer will start in Windows regular more, download Malwarebytes Anti-Malware and HitmanPro, and scan your computer for any left over infections.
Your computer should now be free of the Homeland Security infection. If your current anti-virus solution let this infection through, you may want to consider purchasing the PRO version of Malwarebytes Anti-Malware to protect against these types of threats in the future, and perform regular computer scans with HitmanPro.
If you are still experiencing problems while trying to remove Homeland Security Moneypak virus from your machine, please start a new thread in our Malware Removal Assistance forum.

![U.S. Department of Homeland Security virus [Image: Homeland Security This computer has been blocked virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/03/Homeland-Security-virus.jpg)
![Windows F8 key [Image: F8 key]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/F8-key.jpg.png)
![Advanced Boot Options screen [Image: Starting computer in Safe Mode with Command Prompt]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Safe-Mode-with-Command-Prompt.jpg)
![rstrui.exe command in Safe Mode with Command Prompt [Image: Start System Restore to remove lock screen virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/system-restore-command.jpg)
![Restore your computer's system files to an earlier point in time [Image: Restore settings to remove ransomware]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/system-restore.jpg)
![Malwarebytes Anti-Malware installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Malwarebytes Anti-Malwar removing Homeland Security virus [Image: Malwarebytes Anti-Malwar removing Homeland Security virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)




![HitmanPro free 30 days trial [Image: HitmanPro 30 days activation button]](http://malwaretips.com/blogs/wp-content/uploads/2012/11/hitmanpro-activation.jpg)
![Windows Boot Menu screens [Image: Windows Boot Menu screens]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/windows-boot-manager.jpg)
![Creating Kaspersky Rescue Disk bootable CD [Image: Bootable Kaspersky Rescue CD]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/creating-bootable-kaspersky-rescue-disk.jpg)
![Starting infected computer from Kaspersky Rescue Disk [Image: Starting infected computer from Kaspersky Rescue Disk]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-boot.png)
![Kaspersky Rescue Disk Graphic Mode screen [Image: Kaspersky Rescue Disk Graphic Mode screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-graphic-mode.png)
![Kaspersky Rescue Disk scanner [Image: Kaspersky Rescue Disk scanner]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk.jpg)
![Updating Kaspersky Rescue Disk antivirus definitions [Image: Updating Kaspersky Rescue Disk antivirus definitions]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-update.jpg)
![Kaspersky Rescue Disk scan [Image: Kaspersky Rescue Disk scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-scan.jpg)
![Kaspersky Rescue Disk when detecting malware [Image: Kaspersky Rescue Disk prompt]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-alarm.png)










Hello Paul,
While your computer in Safe Mode with Command Prompt, type msconfig in the Command prompt box.
This should start the Windows System Configuration tool.
Go to the Start-up tab, and search for any suspicious or unknown entries (random numbers or letter, ctfmon.exe and other suspicious entries) and uncheck them from start-up. Basically, you can uncheck everything apart from your antivirus.
Next, start your computer in normal mode and perform a scan HitmanPro and Malwarebytes Anti-Malware as seen in this guide.
Good luck! Waiting for your reply to see how everything is working!
hi, my system restored failed for some reason can you help?
Hello Steve,
Have you tried to create a bootable HitmanPro USB or a Kaspersky Rescue Disk?
Stay safe!
Was trying to talk my college kid through using your fix for this bugger of a virus. But even opening in safe mode with command prompt she is redirected to the user login page and once she types her pass word system restarts with virus.
Yes, your computer should be clean!
Please note that this infection is usually installed via a Java exploit. So if you have Java installe make sure its updated to its latest version!
Stay safe!
Thank you! I did the malwarebytes and was goid to go with the quick and full scan. havent done hitmanpro I should still be good to go right?
Hello,
None of these options will affect your personal documents. Good luck!
Hello,
Apart from locking your desktop, this virus won’t do any other damage. However depending on what has installed the screenlocker, you might have a a ZeroAccess rootkit on your machine, but HitmanPro should be able to find it if its there!
Stay safe!
Hello,
Yes, the screen locker would have remained on your machine. Basically, this 48 hours limit is set because they want to rush the users into paying.
Stay safe!
what would happen if you did not do this by the time period the virus gave you for example the virus said I have 48 hours to do this or it will be lock forever
Hello,
Another option is to use the WinUnlocker command to disinfect your registry.
If you booted Kaspersky Rescue Disk in the graphic mode, click the button К ; in the bottom right corner of the screen and in the menu select Terminal.
In the command prompt enter the command windowsunlocker and press Enter on the keyboard.
Alternatively, you could browse to the infected file, and just delete it from your machine, if you know what you are doing then this is the most fastest way to solve this issue.
Here are the usual locations for this type of infections. Depending on what operating system are you using, browse to the following paths and search for any randomly named file (eg: daxssda.exe, 1232.exe or skype.dat)
For Windows XP:
C:Documents and Settings(Current User random-file.exe
C:Documents and SettingsAll UsersApplication Datarandom-file.exe
C:Documents and Settings(Current User)Application Datarandom-file.exe
For Windows Vista, 7 and 8:
C:Users(Current User)random-file.exe
C:ProgramDatarandom-file.exe
C:Users(Current User)AppDataRoamingrandom-file.exe
C:Users(Current User)AppDataLocalrandom-file.exe
C:Documents and Settings(Current User)Local SettingsApplication Datarandom-file.exe
If you will still have issues, then you will have to create a thread in our Malware Removal Assistance forum: http://malwaretips.com/Forum-Malware-Removal-Assistance
Stay safe!
Hello Norah,
Yes, if you have made a system scan with Malwarebytes Anti-Malware and HitmanPro, then your computer should be clean and safe!
You personal documents should not have been compromised in any way!
Stay
Thanks! your steps was most helpful and ez to follow. i did the restore and did the malawarebytes after and sas good to go. Was on YouTube also when this happened. Does this virus look to just try to get you to give them money or are they trying to get information from your PC? After removal is your PC good to go as it was previously? I guess my question is are your documents etc safe after removal or do these hackers gain access to your personal files? Thanks
doing a Hitman Pro kickstart did the trick for me! Great info….Thanks a ton!
Hello Geri,
Yes, it will work. Just follow an option, and you’ll be fine!:)
Stay safe!
Omg yes im 17 and imgoingthrough tnis rightnow im so scared ):
Hello,
If you have managed to avoid the lock screen then its fine! You should run a scan with HitmanPro and Malwarebytes Anti-Malware just to be on the safe side!
Stay safe!
So i think i just got rid of the virus. However, does it make a difference if i used an update that was the SECOND most recent update instead of the MOST recent? I am currently doing a full comp scan after i just did a quick scan from Malwarebytes. How can i be sure that the virus is gone?
Hello Moshe,
If the Kaspersky Rescue Disk cannot detect you C: drive in Graphic mode, you can use the Text mode. http://support.kaspersky.com/8097
Another option is to use the WinUnlocker command to disinfect your registry.
If you booted Kaspersky Rescue Disk in the graphic mode, click the button К ; in the bottom right corner of the screen and in the menu select Terminal.
In the command prompt enter the command windowsunlocker and press Enter on the keyboard.
Alternatively, you could browse to the infected file, and just delete it from your machine, if you know what you are doing then this is the most fastest way to solve this issue.
Here are the usual locations for this type of infections. Depending on what operating system are you using, browse to the following paths and search for any randomly named file (eg: daxssda.exe, 1232.exe or skype.dat)
For Windows XP:
C:Documents and Settings(Current User random-file.exe
C:Documents and SettingsAll UsersApplication Datarandom-file.exe
C:Documents and Settings(Current User)Application Datarandom-file.exe
For Windows Vista, 7 and 8:
C:Users(Current User)random-file.exe
C:ProgramDatarandom-file.exe
C:Users(Current User)AppDataRoamingrandom-file.exe
C:Users(Current User)AppDataLocalrandom-file.exe
C:Documents and Settings(Current User)Local SettingsApplication Datarandom-file.exe
If you will still have issues, then you will have to create a thread in our Malware Removal Assistance forum.
Stay safe!
You literally described my entire experience word for word except my parents recognized it for what it was when i showed it to them and told me not to worry about it
Thanks for your help!
Hello,
Please create a HitmanPro Kickstart USB as seen here: http://malwaretips.com/blogs/remove-police-trojan/#hitmanpro
OR
Please create a bootable Kaspersky Rescue Disk as seen here: http://malwaretips.com/blogs/remove-police-trojan/#kaspersky
Stay safe!
when i said downloaded “malware” i meant Malwarebytes…. (sheesh)
I got the HLS virus in “user A” part of my computer. ‘user B’ section was unaffected and i downloaded the malware and it seemed to have cleaned the virus. Still can’t get into “user A” section. It says a document with an exe file is not recognized. I went into start up and don’t see any files that look ‘funky’. I want to try to restore. When i go there “C” drive is checked but “D” drive is not. I cannot check “D” drive, though the program says I need to protect it. When I go to look at “D” drive under ‘user B’ it says it is a recovery disc and not to alter anything. QUESTION: should i go ahead with the recovery and hope D drive isn’t damaged?
I also had luck using the repair drive feature. I was unable to startup with the command prompt, but was able to access the system restore through the repair computer option in the safe mode option startup screen. Unfortunately the system restore didn’t work on my machine, but the fix startup option did work. Hope this helps.