Facebook works hard to promote user safety and prevent scams. However, as with any major platform, malevolent actors are constantly developing new ways to exploit users. The ‘Violations detected on your Page’ scam is one of the latest and most common Facebook frauds circulating.
This article will provide an in-depth look at how the scam operates, the red flags to watch for, and actionable advice to protect yourself and your account. We’ll also explore what you can do if you fallen victim, how to regain control of your account, and steps to prevent future compromise.
Overview of the Facebook ‘Violations Detected On Your Page’ Scam
This scam typically begins with an unsolicited Facebook message claiming your page has been reported for terms of service violations. The message appears to come directly from Facebook, warning that your account will be permanently disabled if you do not immediately confirm your identity.
A link is provided supposedly leading to Facebook’s ‘Account Confirmation’ page. However, the URL actually directs to a convincing phishing site designed to steal login credentials and compromise accounts.
The scam message is carefully crafted to cause panic and urgency. Threats of disabling your account sabotage critical thinking and lead users to react impulsively by clicking the deceptive link.
Once at the fake confirmation page, you are prompted to input your Facebook login details which are then stolen by scammers. From here, fraudsters can gain full access to post content or ads using your identity and connections.
This scam represents a serious threat given the immense reach of Facebook. A single successful message can lead to account compromise, identity theft, distribution of malware, and major embarrassment.
Understanding exactly how this con operates is the first step in protecting yourself and others. Let’s break down the process from start to finish.
How the Facebook ‘Violations Detected On Your Page’ Scam Works
The scam typically operates in five stages:
1. The inciting message
The first component is an unsolicited Facebook message delivered to your inbox:
Your Page Has Been Reported Seven Times. We are constantly updating our Meta Privacy Policy and Terms of Service. We have temporarily suspended your page because someone told us that you violated our terms and conditions of service.
If you believe this is an error in our system, please verify your account at the link below.
Account Confirmation: https://facebook.violations-on-page.support/.com
Confirm your account within the next 24 hours otherwise our your Page may be permanently disabled.
Security Team
This message is designed to instill fear of losing your account. Threatening language pressures victims to act quickly without thinking.
2. The deceptive link
The message includes an official looking link purportedly leading to Facebook’s Account Confirmation page. However, the URL actually directs to a fake phishing site controlled by scammers.
The domain name is designed to appear authentic. For example:
- facebook.violations-on-page.support
- account-confirmation.facebook.com
In reality, these lead to fraudulent pages unrelated to Facebook.
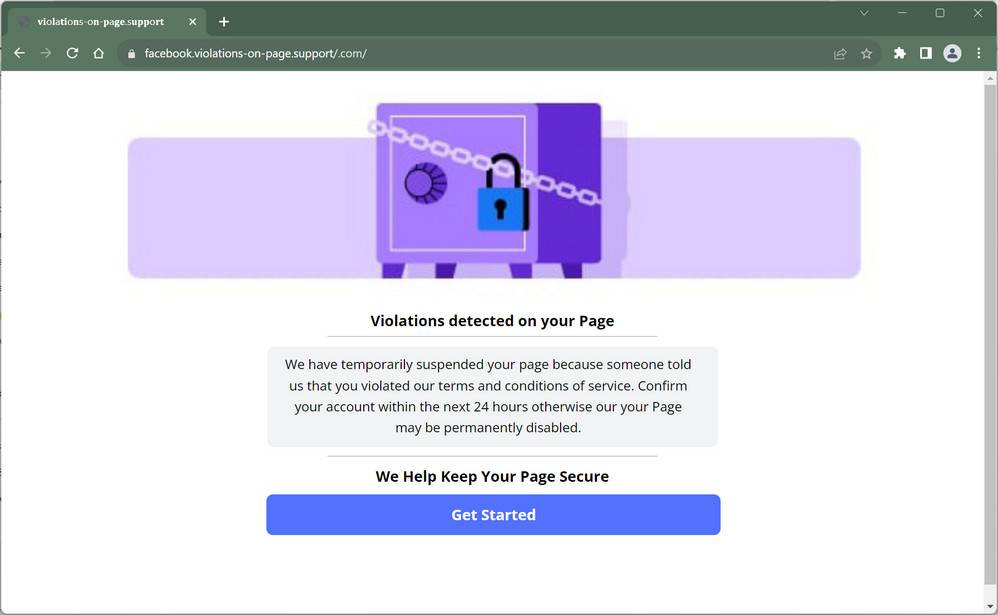
3. The fake confirmation page
Upon clicking the link, you are directed to a web page mimicking Facebook’s design. The site asks you to login to ‘Confirm your Account’ and avoid disablement.
The page appears legitimate with Facebook branding and web address. But in the background, any information entered is harvested by scammers.
Here is the typical text that you will find:
Violations detected on your Page
We have temporarily suspended your page because someone told us that you violated our terms and conditions of service. Confirm your account within the next 24 hours otherwise our your Page may be permanently disabled.
4. Account compromise
If you submit your username and password, criminals immediately gain full access to your account. They can now post content or ads, message friends, access personal data, and exploit your identity.
Stolen accounts can also be sold on dark web marketplaces. Compromised pages spread the scam message further increasing the scam’s reach.
5. Difficult account recovery
Once your account is hacked, recovering it can be challenging. Scammers often change contact email and enable two-factor authentication to lock out the original owner. Regaining access requires submitting ID to Facebook through a complex process.
This rigorous sequence allows a single scam message to create widespread account breaches. Awareness of each step is critical to recognizing and avoiding this con.
5 Red Flags to Spot the Facebook ‘Violations Detected On Your Page’ Scam
The scam message and phishing site closely mimic Facebook’s official branding. But upon closer inspection, several subtle indicators reveal the deception. Watch for these 5 red flags to detect fake violation warnings:
1. Generic greetings
Legitimate messages from Facebook directly address you by name or username. Scam messages use generic greetings like “Dear user” to mask their impersonation.
2. Suspicious links
Scrutinize the embedded URL for odd domain names unrelated to Facebook. Look for misspellings or extra words indicating a fake site.
3. Typos and poor grammar
Scam messages often contain spelling, grammar or formatting errors. Facebook’s official communications are professionally written and error-free.
4. Illogical threats
Facebook will not immediately disable your account without reason. Policy violations lead to warnings and temporary restrictions first. Illogical threats indicate a scam.
5. Requests for sensitive information
Facebook will never ask for your password or disablement repeal through an unsolicited message. Any request for login credentials is a huge red flag.
Stay vigilant for these signs of a counterfeit message. Avoid clicking questionable links or providing personal information. If unsure, contact Facebook directly through the official help center.
What to Do If You Are a Victim of the Violations Detected On Your Page Scam
If you suspect your Facebook account has been compromised by the ‘Violations detected’ scam or another phishing attack, take these steps immediately:
- Log out of all active sessions – This kicks the scammers out of your account preventing further misuse.
- Change your password – Assign a new complex password that scammers won’t be able to guess. Make sure you haven’t used it anywhere else.
- Enable two-factor authentication – Adding another layer of verification prevents repeated hacks by requiring an access code.
- Check connected apps – Remove any unknown or suspicious third-party services linked to your account which may be used maliciously.
- Review recent posts and messages – Scan your feed and communications for any embarrassing, explicit or malware-laden content sent from your account while compromised. Report suspicious posts.
- Submit ID to Facebook – Facebook requires ID verification to prove you are the rightful account owner. Expect delays recovering access.
- Warn contacts – Let friends know to be wary of dubious messages appearing to come from your account.
- Run an antivirus scan – If you suspect your device is infected with malware, you should run a scan with Malwarebytes Anti-Malware Free.
With scammer access revoked, focus next on damage control and preventing additional exploits. Be vigilant for secondary schemes targeting you after the initial hack.
How to Prevent Falling Victim to This Scam
Avoiding this insidious phishing technique requires knowledge, vigilance, and healthy skepticism. Implement these proactive measures to keep your account secure:
- Enable login approvals – Require an additional code with each login attempt to block unauthorized access.
- Use unique passwords – Each of your online accounts should have its own complex password that’s difficult to crack.
- Beware unsolicited messages – Don’t open random messages from unknown users and never click included links.
- Inspect URLs – Check that embedded links match the legitimate Facebook domain before clicking.
- Report suspicious messages – If an odd message appears to come from Facebook, report it through the app.
- Monitor notifications – Watch for alerts about unrecognized logins which may indicate compromise.
- Review privacy settings – Restrict account visibility and sharing to decrease exploitation risks.
Staying several steps ahead of scammers is the most effective defense. Combining smart password hygiene, extra login protections, and heightened vigilance will keep your account secure.
The Bottom Line – Key Takeaways to Avoid This Scam
The ‘Violations detected on your Page’ tactic capitalizes on fear to lower defenses and steal login credentials. Avoid becoming a victim using these takeaways:
- Facebook will not randomly disable your account – Policy violations lead to warnings first before any disablement.
- Look for red flags in messages – Poor grammar, odd threats, and generic greetings signal a scam attempt.
- Inspect links closely – Fake URLs pretend to be Facebook but lead to phishing sites.
- Never enter your password – Facebook will never request your password be entered through a message link.
- Enable added login security – Two-factor approvals block unauthorized access even with a stolen password.
- Report suspicious messages – Flag dubious communications pretending to be from Facebook.
- If hacked, revoke access immediately – Log out of all sessions, change your password, and submit ID proof to Facebook.
Staying informed makes you a harder target for this scam. Share this advice with Facebook friends and community groups to prevent wider victimization.
Frequently Asked Questions (FAQ)
How do scammers send the fake ‘Violations Detected On Your Page’ messages?
Scammers often hijack other compromised accounts to spread messages. They also use bot networks capable of spamming thousands of users.
Does clicking the link infect my device?
The phishing site itself does not contain malware. However, any credentials entered could provide account access enabling scammers to post malicious links that do infect devices.
Why does Facebook allow these scams?
No platform can prevent all scams as malicious actors are constantly evolving new tactics. Facebook dedicates substantial resources toward fraud detection but persistence of bad actors requires vigilance by all users.
What information can scammers access in my Facebook account?
Full account access enables seeing all profile info, posts, photos, contacts, messages, and groups you are part of. Significant personal data is at risk.
Can I tell if my account is compromised?
Watch for unfamiliar posts or messages sent from your account. Getting logged out unexpectedly or password change notifications can also indicate unauthorized access.
How long does it take to recover a hacked Facebook account?
It depends on response time submitting ID proof to Facebook. The process averages 1-2 weeks but can take over a month if documentation is lacking.
Final Thoughts
As one of the most widespread Facebook scams currently circulating, the ‘Violations Detected On Your Page’ ploy succeeds by instilling fear and urgency in victims. However, by spotting the deception methods and understanding the mechanics behind this scam, Facebook users can mitigate risks.
Implement the recommendations outlined in this guide to lock down your account, recognize fake messages, avoid phishing links, and monitor for compromise. Share this advice across your networks to prevent scammers from profiting off misinformation.
With increased awareness and vigilance by the community, we can work together with Facebook to frustrate these fraudsters and eliminate this scam from the platform.







