3P Request Blocker (3PRB) blocks 3rd party resources
addons.mozilla.org/en-US/firefox/addon/3prb/: 3P Request Blocker (3PRB) – Add-ons for Firefox
 Version 1.0.26.11 Last updated 12 hours ago (Mar 30, 2018)
Version 1.0.26.11 Last updated 12 hours ago (Mar 30, 2018)
112.6 KiB Works with Firefox for Android 52.0 and later, Firefox 52.0 and later = Quantum Support
Source code released under MIT/X11 License
3P Request Blocker (3PRB) by 3PRB
Prevent your browser from connecting to 3rd party resource without user consent. Increase your privacy, security, and speed by blocking unnecessary requests.

This add-on block all 3rd party requests. Only you can allow|temporary allow them.
- Additionally, this add-on will protect you from these attacks:
1. Try to load http:// resource from https://
2. Try to load internet resource from file://
3. Try to trick you with punycode domain (disabled by default)
- Block resource type / MIME type to save bandwidth.
- Many options to configure.
- Nothing is sent nor collected by this add-on.
- Support "Firefox Android". Results may vary. (my primary target is PC)
To Firefox ESR 52 / Tor Browser users:
ESR52 doesn't have latest WebExt APIs, so both won't work:
1. Whitelist "export" button
2. WebSocket blocking
Upgrade your Firefox or wait for next ESR release(ESR59+).
To Tor Browser users:
1. Disable bundled NoScript. (from about:addons)
2. Turn on CSP. Go to "about:config" -> set "security.csp.enable" to true.
If you want to use 3PRB's JS Blocker (Disabled by default)
If you're using uBO, delete it. uBO will override my add-on and allow inline JS. This is called "add-on conflict".
- Convert "RequestPolicy" rule to text
- Test JavaScript
- The Internet is seriously flawed.
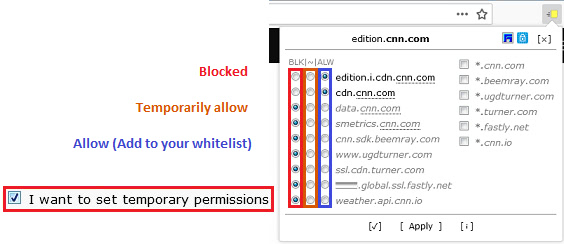
> Add website to whitelist (from toolbar button)
1. Click red icon. (Red = 3P resource detected)
2. Select some FQDN you want to allow. Click [Apply].
3.
[Default]
Your rule is added to the whitelist.
[If "I want to set temporary permissions" is selected]
ALW: Your rule is added to the whitelist. (ALW: 'ALloW')
~: Your rule is added to the "temporary whitelist". This list is not permanent.
...
- for MORE look on Mozilla add_on link...
User comments:
"This is a perfect substitute for the RequestPolicy addon..."
"Really a useful add-on. A must have for privacy and to learn about how work the Web. 5 stars I recommend !"
"TLDR: RequestPolicy + QuantumSupport + SecurityOptions = This add-on."
addons.mozilla.org/en-US/firefox/addon/3prb/: 3P Request Blocker (3PRB) – Add-ons for Firefox
112.6 KiB Works with Firefox for Android 52.0 and later, Firefox 52.0 and later = Quantum Support
Source code released under MIT/X11 License
3P Request Blocker (3PRB) by 3PRB
Prevent your browser from connecting to 3rd party resource without user consent. Increase your privacy, security, and speed by blocking unnecessary requests.
This add-on block all 3rd party requests. Only you can allow|temporary allow them.
- Additionally, this add-on will protect you from these attacks:
1. Try to load http:// resource from https://
2. Try to load internet resource from file://
3. Try to trick you with punycode domain (disabled by default)
- Block resource type / MIME type to save bandwidth.
- Many options to configure.
- Nothing is sent nor collected by this add-on.
- Support "Firefox Android". Results may vary. (my primary target is PC)
To Firefox ESR 52 / Tor Browser users:
ESR52 doesn't have latest WebExt APIs, so both won't work:
1. Whitelist "export" button
2. WebSocket blocking
Upgrade your Firefox or wait for next ESR release(ESR59+).
To Tor Browser users:
1. Disable bundled NoScript. (from about:addons)
2. Turn on CSP. Go to "about:config" -> set "security.csp.enable" to true.
If you want to use 3PRB's JS Blocker (Disabled by default)
If you're using uBO, delete it. uBO will override my add-on and allow inline JS. This is called "add-on conflict".
- Convert "RequestPolicy" rule to text
- Test JavaScript
- The Internet is seriously flawed.
> Add website to whitelist (from toolbar button)
1. Click red icon. (Red = 3P resource detected)
2. Select some FQDN you want to allow. Click [Apply].
3.
[Default]
Your rule is added to the whitelist.
[If "I want to set temporary permissions" is selected]
ALW: Your rule is added to the whitelist. (ALW: 'ALloW')
~: Your rule is added to the "temporary whitelist". This list is not permanent.
...
- for MORE look on Mozilla add_on link...
User comments:
"This is a perfect substitute for the RequestPolicy addon..."
"Really a useful add-on. A must have for privacy and to learn about how work the Web. 5 stars I recommend !"
"TLDR: RequestPolicy + QuantumSupport + SecurityOptions = This add-on."
