- Aug 17, 2014
- 11,114
The Bad Rabbit ransomware attack that hit Russia and Ukraine on Tuesday has been linked to the recent NotPetya outbreak, but the number of infections appears to be far smaller.
Several cybersecurity firms have conducted an initial analysis of the threat, including Cisco Talos, Kaspersky, Malwarebytes, ESET, McAfee, Bitdefender and Trend Micro.
Bad Rabbit distribution
Researchers say the malware spreads via watering hole attacks that deliver a fake Flash Player installer. The malicious file has been delivered from compromised websites in Denmark, Ireland, Bulgaria, Turkey and Russia.
Several cybersecurity firms have conducted an initial analysis of the threat, including Cisco Talos, Kaspersky, Malwarebytes, ESET, McAfee, Bitdefender and Trend Micro.
Bad Rabbit distribution
Researchers say the malware spreads via watering hole attacks that deliver a fake Flash Player installer. The malicious file has been delivered from compromised websites in Denmark, Ireland, Bulgaria, Turkey and Russia.
Researchers pointed out that victims need to manually launch the fake Flash installer to get infected, and the file needs to obtain administrative privileges, which causes Windows to display a User Account Control (UAC) prompt. The attackers have not made any effort to bypass UAC.
Once executed, the dropper copies the main module (infpub.dat) to the Windows folder and executes it through rundll32.exe, a Windows component used to run code in DLL files. Scheduled tasks, which have been given dragon names from the “Game of Thrones” TV show, are used to execute other malware components and reboot the system.
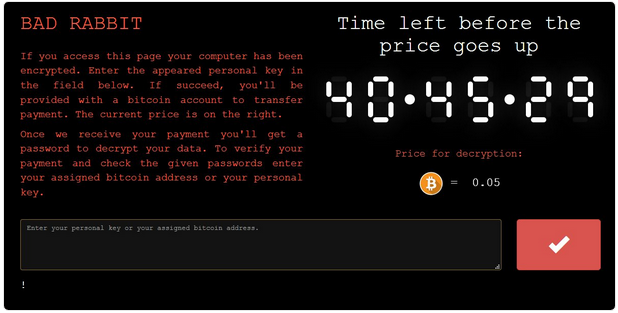
The ransom note is displayed in both text files dropped onto the system and via a bootlocker screen.
Similar to NotPetya, Bad Rabbit does appear to rely on SMB to spread, but, contrary to initial reports, it does not use the NSA-linked EternalBlue exploit.
The malware scans the internal network for open SMB shares with a specific name. The threat relies on the Mimikatz post-exploitation tool to harvest credentials, but it also includes a hardcoded list of usernames and passwords.
Bad Rabbit file encryption
Once it infects a system, Bad Rabbit encrypts more than 100 file types, including archives, backups, databases, images, documents, source code, and virtual disk images. The encrypted files are given a .encrypted extension. Kaspersky’s Costin Raiu pointed out that the file types are similar to the ones targeted by NotPetya, but not identical.
Bad Rabbit clears security logs and deletes the update sequence number (USN) change journal, which logs all changes made to files on the volume, to prevent recovery.
The encryption relies on DiskCryptor, an open source full disk encryption software, and the attackers have used the AES-128-CBC cipher and an RSA-2048 public key.
It’s still unclear if files can be recovered without paying the ransom. However, unlike NotPetya, which made it impossible to decrypt files even if the ransom had been paid, researchers confirmed that data encrypted by Bad Rabbit is recoverable with the right key.
Victims are asked to pay 0.05 bitcoin, worth roughly $280, to get their files back, but the amount increases if the ransom is not paid within two days.
Bad Rabbit victims
A majority of the victims are in Russia, where the ransomware hit several media outlets, including Interfax and Fontanka. A significant number of Infections has also been observed in Ukraine, where the malware reportedly hit the airport in Odessa, the Kiev subway, the State Aviation Service of Ukraine, and the Transport Ministry of Ukraine. Infections have also been spotted in Bulgaria, Turkey, Germany, Japan and other countries.
Some of the organizations whose systems have been compromised reported suffering significant disruptions.
Unlike the NotPetya attack, which hit tens of thousands of systems in more than 65 countries, Kaspersky reported that it had only seen roughly 200 victims. The security firm believes this may have been a targeted attack aimed at corporate networks.
Bad Rabbit links to NotPetya
Several security firms have classified Bad Rabbit as a variant of NotPetya, the malware that hit numerous organizations in late June and caused losses of millions of dollars for several major companies. NotPetya has also been tracked as Diskcoder, Petya, Petrwrap, exPetr and GoldenEye.
While NotPetya initially also appeared to be a piece of ransomware, researchers noticed that the encrypted files could not have been recovered even if the ransom had been paid. The malware was later reclassified as a wiper.
The list of similarities between NotPetya and Bad Rabbit includes the fact that both use SMB to spread, they create scheduled tasks to reboot the system, the ransom screen is very similar, both use .dat files as the main component, and some of the functionality and code is almost identical.
On the other hand, unlike NotPetya, Bad Rabbit does not use the EternalBlue exploit, its encryption functionality works properly and a more advanced crypter is used, it uses a different kernel and bootloader, and the attacks appear to have been more targeted. Another significant difference is the fact that NotPetya was delivered via a Ukraine-based company’s update server, while Bad Rabbit leverages drive-by attacks.


