silversurfer
Super Moderator
Thread author
Verified
Top Poster
Staff Member
Malware Hunter
Forum Veteran
- Aug 17, 2014
- 12,726
- 123,827
- 8,399
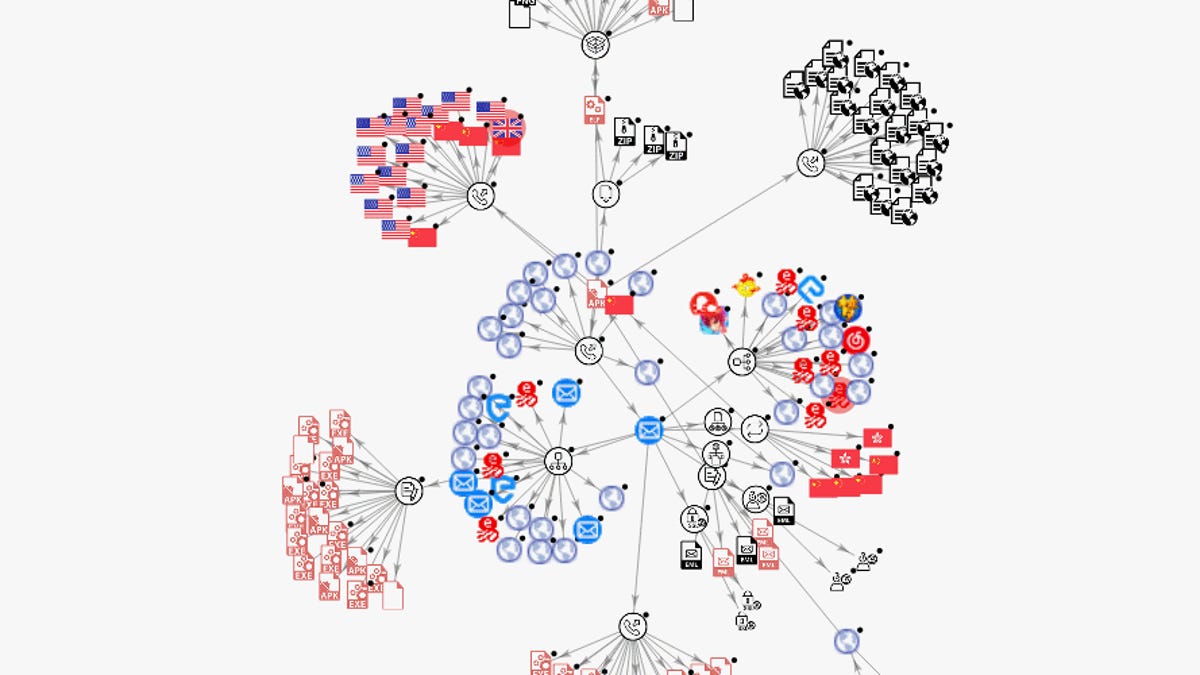
Cobalt Strike and Metasploit, two penetration testing toolkits usually employed by security researchers, have been used to host more than a quarter of all the malware command and control (C&C) servers that have been deployed in 2020, threat intelligence firm Recorded Future said in a report today.
The security firm said it tracked more than 10,000 malware C&C servers last year, across more than 80 malware strains.
The malware operations were the work of both state-sponsored and financially-motivated hacking groups.
These groups deployed malware using various methods. If the malware managed to infect victim devices, it would report back to a command and control server from where it would request new commands or upload stolen information.
But the Recorded Future report also looked at other facets of a malware C&C server's operations. Other observations include:
- On average, command and control servers had a lifespan (that is, the amount of time the server hosted the malicious infrastructure) of 54.8 days.
- Monitoring only "suspicious" hosting providers can leave blindspots, as 33% of C&C servers were hosted in the US, many on reputable providers.
- The hosting providers that had the most command and control servers on their infrastructure were all U.S.-based: Amazon, Digital Ocean, and Choopa.
Cobalt Strike and Metasploit accounted for a quarter of all malware C&C servers in 2020
Security firm Recorded Future said it tracked more than 10,000 malware command and control servers last year, used across more than 80 malware families.
 www.zdnet.com
www.zdnet.com
