- Aug 17, 2014
- 11,108
A fully undetectable (FUD) malware obfuscation engine named BatCloak is being used to deploy various malware strains since September 2022, while persistently evading antivirus detection.
The samples grant "threat actors the ability to load numerous malware families and exploits with ease through highly obfuscated batch files," Trend Micro researchers said.
About 79.6% of the total 784 artifacts unearthed have no-detection across all security solutions, the cybersecurity firm added, highlighting BatCloak's ability to circumvent traditional detection mechanisms.
The BatCloak engine forms the crux of an off-the-shelf batch file builder tool called Jlaive, which comes with capabilities to bypass Antimalware Scan Interface (AMSI) as well as compress and encrypt the primary payload to achieve heightened security evasion.
The open-source tool, although taken down since it was made available via GitHub and GitLab in September 2022 by a developer named ch2sh, has been advertised as an "EXE to BAT crypter." It has since been cloned and modified by other actors and ported to languages such as Rust.
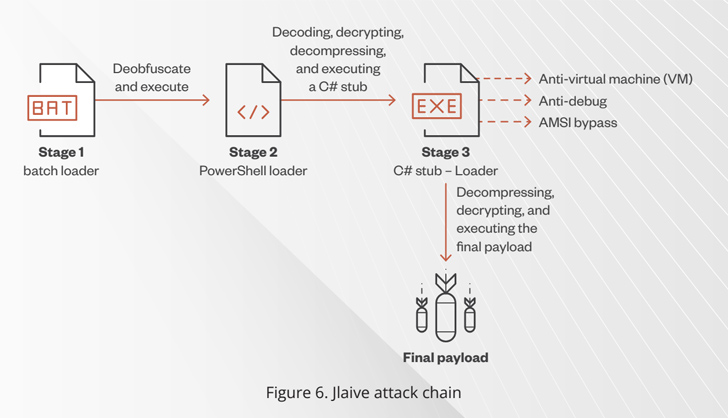
The final payload is encapsulated using three loader layers – a C# loader, a PowerShell loader, and a batch loader – the last of which acts as a starting point to decode and unpack each stage and ultimately detonate the concealed malware.
"The batch loader contains an obfuscated PowerShell loader and an encrypted C# stub binary," researchers Peter Girnus and Aliakbar Zahravi said. "In the end, Jlaive uses BatCloak as a file obfuscation engine to obfuscate the batch loader and save it on a disk."

Analyzing the FUD Malware Obfuscation Engine BatCloak
We look into BatCloak engine, its modular integration into modern malware, proliferation mechanisms, and interoperability implications as malicious actors take advantage of its fully undetectable (FUD) capabilities.



