- Aug 17, 2014
- 11,108
A new malware campaign has been observed using sensitive information stolen from a bank as a lure in phishing emails to drop a remote access trojan called BitRAT.
The unknown adversary is believed to have hijacked the IT infrastructure of a Colombian cooperative bank, using the information to craft convincing decoy messages to lure victims into opening suspicious Excel attachments.
The discovery comes from cybersecurity firm Qualys, which found evidence of a database dump comprising 418,777 records that's said to have been obtained by exploiting SQL injection faults.
The leaked details include Cédula numbers (a national identity document issued to Colombian citizens), email addresses, phone numbers, customer names, payment records, salary details, and addresses, among others.
There are no signs that the information has been previously shared on any forums in the darknet or clear web, suggesting that the threat actors themselves got access to customer data to mount the phishing attacks.
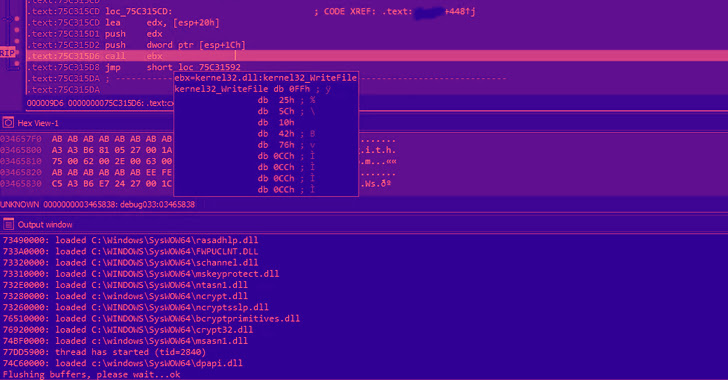
The Excel file, which contains the exfiltrated bank data, also embeds within it a macro that's used to download a second-stage DLL payload, which is configured to retrieve and execute BitRAT on the compromised host.
Hackers Using Stolen Bank Information to Trick Victims into Downloading BitRAT Malware
Cybercriminals Using Stolen Bank Information to Trick Victims into Downloading BitRAT Malware
