L
LabZero
Thread author
File Name: PIC05042502016-JPG.com
MD5: 6b5f23f5c4a62a039132e694e8bc4f1b
SHA1: 06e80ab43e18dbf564144440251fd6b85fde72c5
SHA256: 558f1ad6c022b31d2217ad730c57b5364c671788c8975ba1684880936da9437d
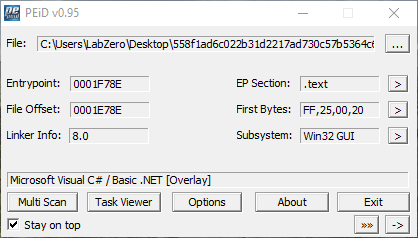
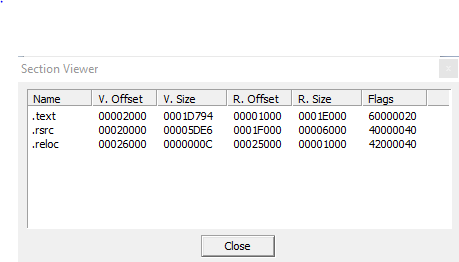
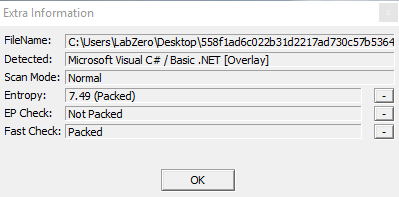
The malware is a .NET file, the linker version is 8.0; the file has 3 sections: .text, .rsrc, .reloc.
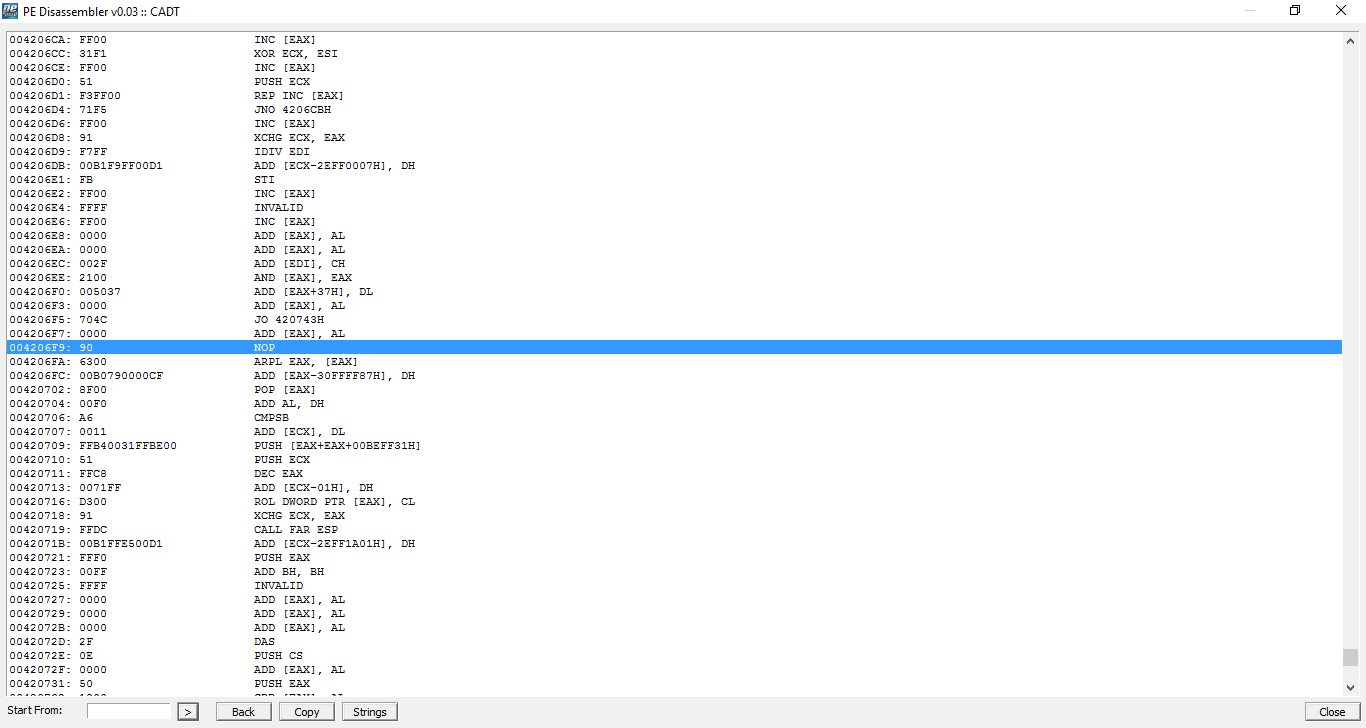
With a disassembler inspection you can see the malware uses NOP operation, which is an assembly instruction, it allows the pipeline execution unit of slack for N clock cycles according to the processor used, as noted in name so it does nothing.
In this case it seems the malware uses NOP to perform buffer overflow attacks, if the attackers don't have perfect control of the exploitation and probably this prevents also the malfunction of the malicious code.
There are also XOR, INC and PUSH operations, and it is clear that the malware performs byte mathematical functions and operates on byte buffers.
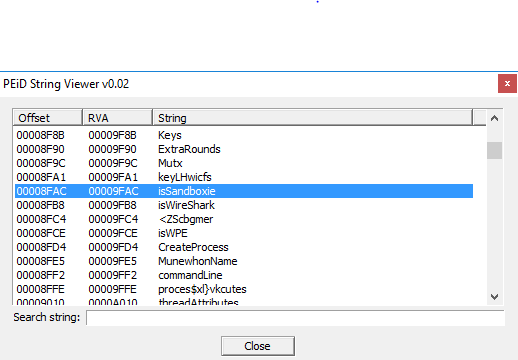
A really interesting point of this analysis is the strings of the malware because it detects if it was launched in a sandboxed environment; for this purpose it uses a function called isSandBoxie, in addition it also tries to detect WireShark in the same way with a function "isWireShark" this because this code probably tries to connect to a IRC server.
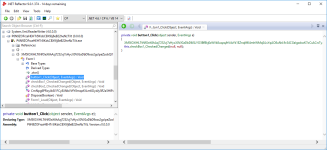
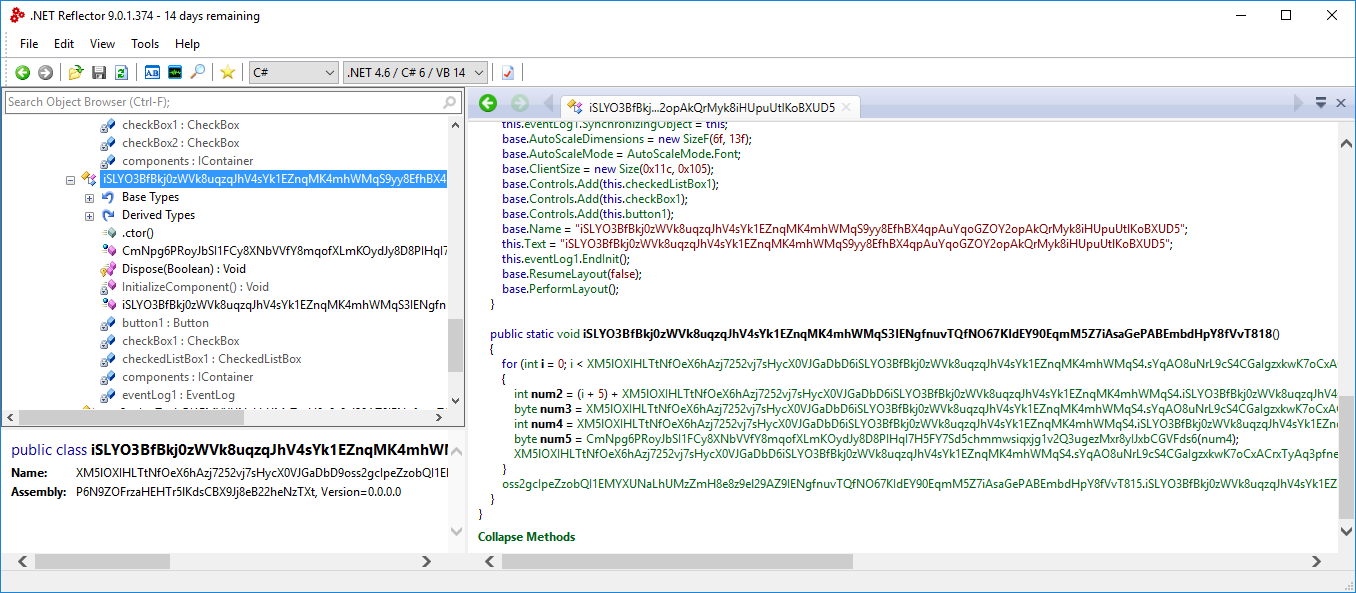
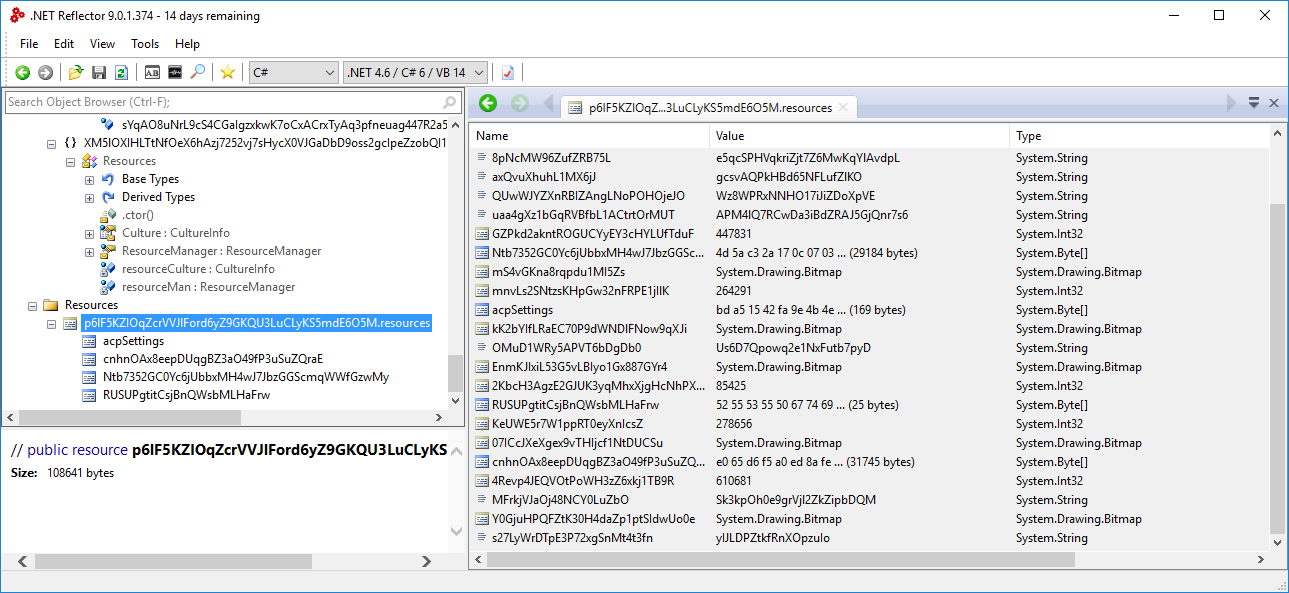
The malware is packed, with an analysis of the malicious code by using .NET Reflector 9.0 you can see that the malware is obfuscated and the function "isSandBoxie" and "isWireShark" are probably referred to the click event of the button1 variable, but unfortunatey studying the code we can't establish where that functions are used.
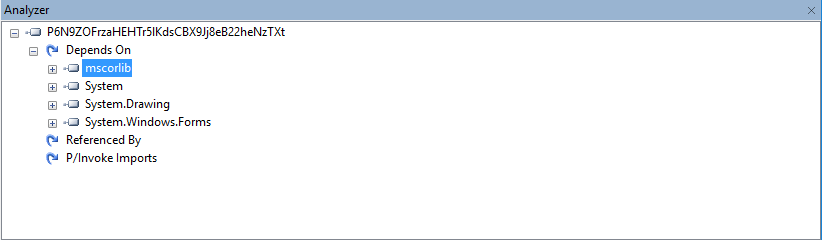
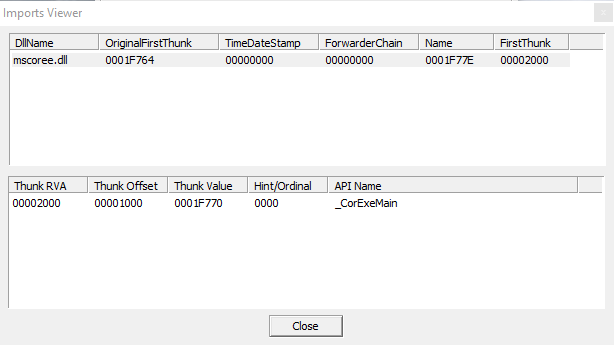
Imports (mscoree.dll):
Finally, also the resources are encrypted.
MD5: 6b5f23f5c4a62a039132e694e8bc4f1b
SHA1: 06e80ab43e18dbf564144440251fd6b85fde72c5
SHA256: 558f1ad6c022b31d2217ad730c57b5364c671788c8975ba1684880936da9437d
The malware is a .NET file, the linker version is 8.0; the file has 3 sections: .text, .rsrc, .reloc.
With a disassembler inspection you can see the malware uses NOP operation, which is an assembly instruction, it allows the pipeline execution unit of slack for N clock cycles according to the processor used, as noted in name so it does nothing.
In this case it seems the malware uses NOP to perform buffer overflow attacks, if the attackers don't have perfect control of the exploitation and probably this prevents also the malfunction of the malicious code.
There are also XOR, INC and PUSH operations, and it is clear that the malware performs byte mathematical functions and operates on byte buffers.
A really interesting point of this analysis is the strings of the malware because it detects if it was launched in a sandboxed environment; for this purpose it uses a function called isSandBoxie, in addition it also tries to detect WireShark in the same way with a function "isWireShark" this because this code probably tries to connect to a IRC server.
The malware is packed, with an analysis of the malicious code by using .NET Reflector 9.0 you can see that the malware is obfuscated and the function "isSandBoxie" and "isWireShark" are probably referred to the click event of the button1 variable, but unfortunatey studying the code we can't establish where that functions are used.
Imports (mscoree.dll):
Finally, also the resources are encrypted.