- Oct 23, 2012
- 12,527
CryptXXX is a new ransomware variant discovered during the past weeks, which, besides encrypting the user's data, is also capable of stealing Bitcoin from infected targets, along with passwords and other personal details, security researchers from Proofpoint have found.
The first signs of the CryptXXX ransomware appeared towards the end of March. Security experts say the ransomware is distributed via Web pages that host the Angler exploit kit. This crimeware kit uses vulnerabilities to push the Bedep click-fraud malware on the users' systems.
Bedep is also known for having "malware downloading" capabilities, so it will download the CryptXXX ransomware as a second-stage infection, dropping it as a delayed execution DLL, set to wait 62 minutes before launching.
The first signs of the CryptXXX ransomware appeared towards the end of March. Security experts say the ransomware is distributed via Web pages that host the Angler exploit kit. This crimeware kit uses vulnerabilities to push the Bedep click-fraud malware on the users' systems.
Bedep is also known for having "malware downloading" capabilities, so it will download the CryptXXX ransomware as a second-stage infection, dropping it as a delayed execution DLL, set to wait 62 minutes before launching.
CryptXXX asks for 1.2 Bitcoin
After infecting users, the ransomware changes the users' wallpaper with its ransom note and drops text and HTML ransom notes all over your computer.
You can spot CryptXXX infections by the ransom notes, which are named de_crypt_readme.txt and de_crypt_readme.html, or by the extension they add to all encrypted files, which is .crypt.
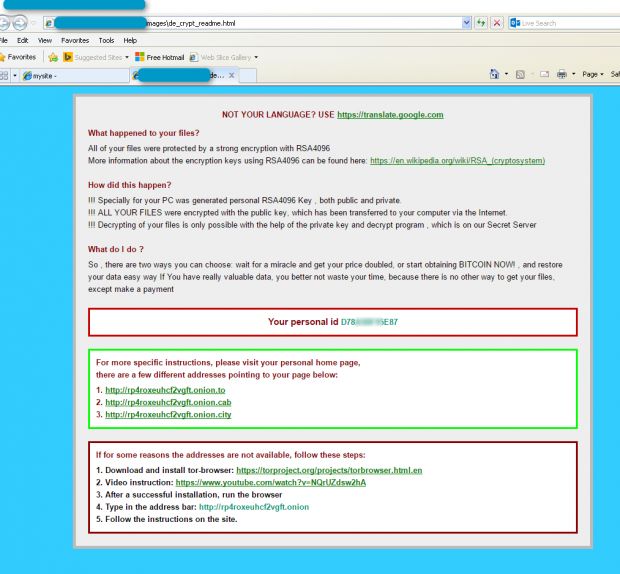
CryptXXX ransom note, HTML format
The standard ransom note asks for 1.2 Bitcoin, which is roughly $515 (€455), a sum that is well above the average of recent ransomware infections.
CryptXXX comes with a data harvesting component
In past infections with the Bedep click-fraud malware, Proofpoint said it also saw Bedep deliver an infostealer component. After an in-depth analysis, it was revealed that this is also true with CryptXXX, which too includes such a feature.
CryptXXX is capable of harvesting information and credentials about the user's local instant messenger clients, email clients, FTP clients, and Internet browsers.
Proofpoint has also said CryptXXX can "steal Bitcoin" but has not elaborated on how this takes place.
CryptXXX is from the same group that created the Angler exploit kit
But the most interesting detail about CryptXXX comes at the end of the company's analysis. Having a closer look at the big picture, Proofpoint saw similarities between CryptXXX and the older Reveton ransomware.
Similarities to Reventon include details such as the fact that both ransomware families were coded in Delphi, both use a delayed start, DLLs are called with a custom entry function, both include Bitcoin and credential stealing functions, and also use a custom C&C protocol on TCP 443.
Even worse, all clues point to the fact that CryptXXX was created by the same criminal group that came up with the Angler exploit kit itself, the Bedep click-fraud malware, and Reveton in the past.
Expect CryptXXX to have the same impact as Locky
This situation is similar to how the Locky ransomware came out of nowhere at the start of 2015 and became one of the top three ransomware families around, mainly thanks to the fact it was running on the infrastructure of the Dridex banking trojan.
Taking into account that the person behind Bedep, Angler, and Reveton is the same as he one behind even older tools such as the Cool exploit kit, CryptXXX is not your ordinary ransomware variant put together by script kiddies who stole code from open-sourced (and flawed) ransomware variants uploaded on GitHub.
"Given Reveton's long history of successful and large-scale malware distribution, we expect CryptXXX to become widespread," Proofpoint researcher Kafeine explains. "While we have observed many new ransomware instances in recent months, many have been written and/or distributed by less experienced actors and have not gained significant traction."
"Those associated with more experienced actors, however, (such as Locky) have become widespread quickly. Based on the large number of translations available for the payment page, it appears that the Reveton team shares those expectations."