Good article about Advanced persistent Threats (APTs) how to discover them and methods of metigations
dvanced persistent threats (APTs) have emerged to be legitimate concerns for all organizations. APTs are threat actors that breach networks and infrastructures and stealthily lurk within them over extended spans of time.
They typically perform complex hacks that allow them to steal or destroy data and resources.
According to Accenture, APTs have been organizing themselves into groups that enable them to share tactics and tools to carry out attacks at scale. Russian group Silence APT, for instance, has been reported to be actively targeting financial institutions and have successfully stolen millions of dollars from various banks worldwide.
Smaller organizations also need to be wary of such threats. APT groups also use automated tools and botnets to gain access to networks, and these tactics don't discriminate based on size, industry, or value. Any vulnerable infrastructure can be breached. It is now critical for all organizations to understand how APTs operate and implement the necessary security measures to mitigate them as threats.
Signs that an APT may be lurking
APTs operate covertly, so organizations may not even realize that they have been breached until something really goes awry. InfoTrax Systems, for example, was only able to detect years-long breach after its servers' storage was maxed out. IT teams have to look out for the indications that an APT might be lurking within the network.
A few distinct signs include:
Excessive logins — APTs typically rely on compromised access credentials to gain routine access to networks. They can either brute force attempts using login name and password credential dumps or legitimate credentials stolen from social engineering and phishing attacks. Excessive or suspicious login activities, especially in odd hours, are often attributable to APTs.
Explosion of malware — APTs also use various malware to perform their hacks. So, if antivirus tools often detect and remove malware, it is possible that an APT is continuously implanting trojans and remote access tools into the network.
Increased usage of computing resources — These threat actors will also have to use the network's computing resources to perform their hacks. Active malware will use computing power and memory within endpoints. Hackers may also temporarily store their stolen data within servers. Exfiltrating large volumes of data would also show up as excessive outgoing traffic.
Heightened Monitoring
Spotting these signs isn't straightforward, so IT teams must actively search for these signs. Fortunately, modern security solutions now provide capabilities that enable IT teams to monitor the potential APT presence and their activities.
Log Analysis — Logs can accurately show the various activities, events, and tasks that transpired in devices, systems, and applications. However, going through logs, which are often in unformatted plain text format, can be tedious. To help IT teams sort through the information, advanced log analysis tools now feature algorithms that can search for patterns across all IT infrastructure components.
Log management and analysis solution XpoLog, for instance, can consolidate all logs across various infrastructure components. Xpolog can automatically parse and tag the information contained in these log files. Using artificial intelligence (AI), Xpolog can then identify anomalous patterns and generate insights, including those that are indicative of security concerns.
Information such as bandwidth use, login sessions, the geographic distribution of network traffic, can all be used to reveal the presence of threats. All the data can even be visualized for easier presentation and review.
Through these findings, the platform can readily alert IT teams of potential APT attacks so that immediate action can be taken.
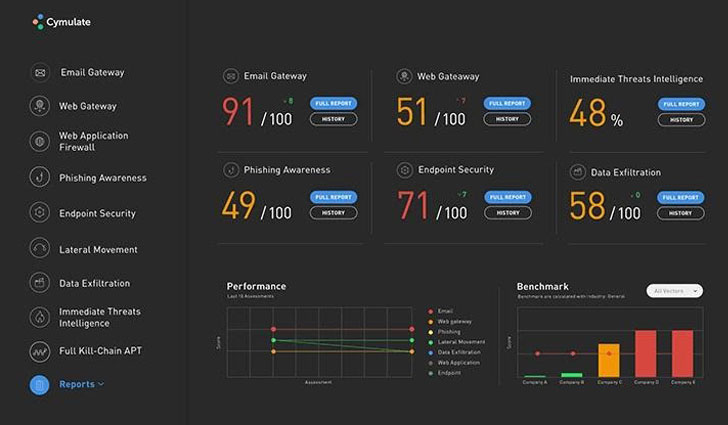
Breach and Attack Simulations — Breach and attack simulation (BAS) platforms can run routine tests that mimic actual cyberattacks to check if security measures are working as intended. They serve as alternatives to traditional penetration testing, which are challenging to perform on a routine basis.
BAS platform Cymulate, for example, offers a wide variety of tests that cover the potential vectors of attack to an infrastructure. It can test web gateways and web application firewalls for vulnerabilities. It can also deploy dummy malware into endpoints to check if anti-malware or antiviruses can detect malicious files and processes. It also has phishing attack simulations that can identify which users are susceptible to social engineering attacks.
Cymulate allows for scheduled and routine tests to be run to see if an organization's implemented security measures and tools work as intended. APTs turn off security solutions like antiviruses and firewalls, so routine tests would readily indicate if something is tampering with these solutions.
Defenses Must Be Improved
Monitoring and early detection are key to keeping a secure defensive perimeter. Organizations must integrate these efforts as part of a broader security strategy.
Increase vigilance — Actively analyzing logs and performing routine tests of security measures can inform IT teams of the potential presence of APTs, allowing them to deal with these threats immediately.
Adopt enterprise-grade security — Organizations must also use capable security solutions. The malware used by APTs can feature a polymorphic code that allows them to evade common free or cheap anti-malware solutions.
Keep systems and apps updated — APTs exploit vulnerabilities of devices and systems for many of their tactics. Developers regularly release patches and fixes to ensure that critical vulnerabilities are addressed.
Organizations must ensure that these updates are quickly applied when they become available.
Train people — APTs can also try to exploit human weaknesses through social engineering attacks. Organizations must train staff on the best security practices, including accurately identifying phishing emails and attempts, using strong passphrases, and avoiding password reuse.
Article Link:How Organizations Can Defend Against Advanced Persistent Threats