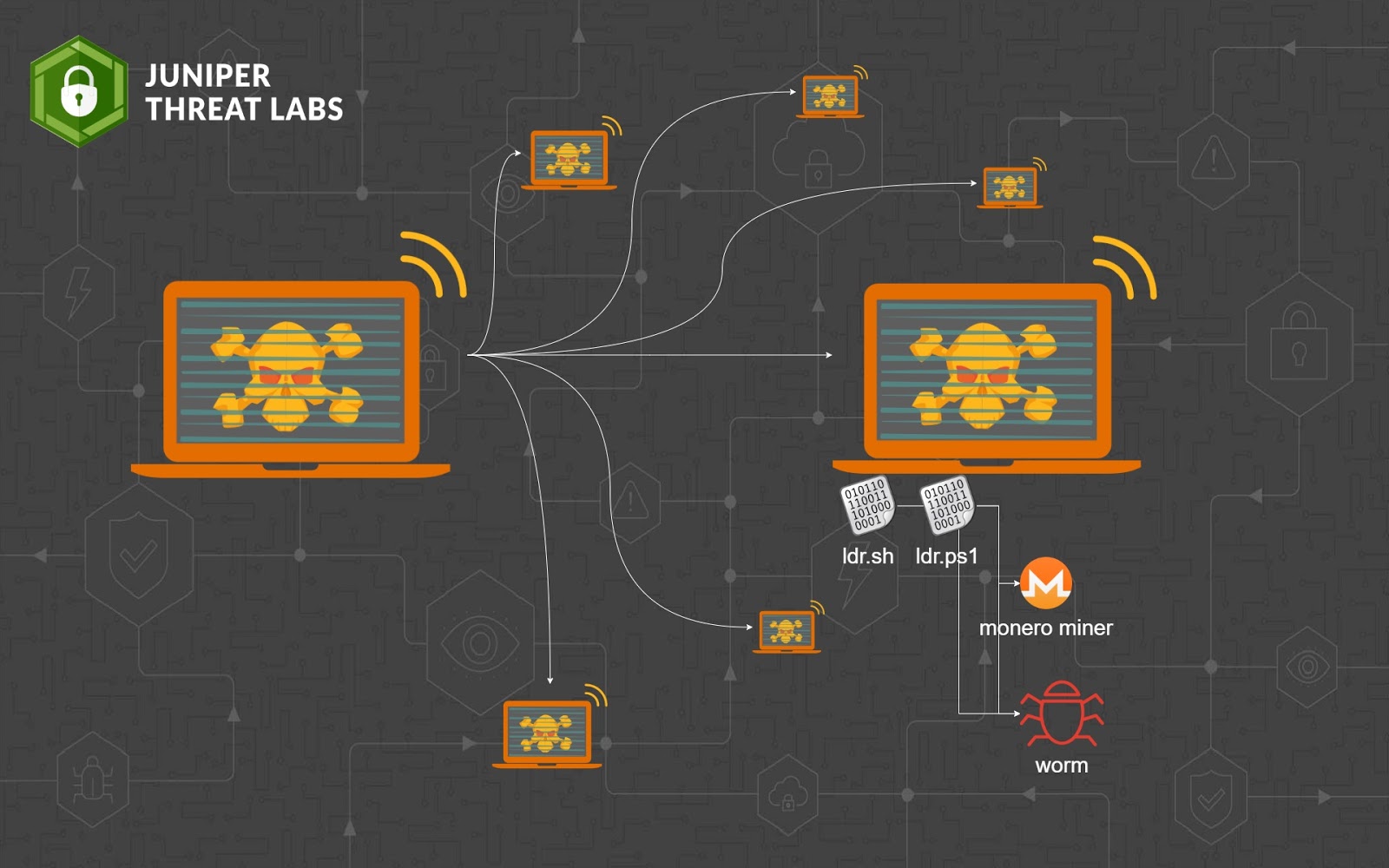
Research company Juniper started monitoring what it’s calling the Sysrv botnet in December. One of the botnet’s malware components was a worm that spread from one vulnerable device to another without requiring any user action. It did this by scanning the Internet for vulnerable devices and, when found, infecting them using a list of exploits that has increased over time. The malware also included a cryptominer that uses infected devices to create the Monero digital currency. There was a separate binary file for each component.
The Sysrv binary is a 64-bit Go binary that’s packed with the open source UPX executable packer. There are versions for both Windows and Linux. Two Windows binaries chosen at random were detected by 33 and 48 of the top 70 malware protection services, according to VirusTotal. Two randomly picked Linux binaries had six and nine.

Windows and Linux devices are under attack by a new cryptomining worm
With new exploits and capabilities, the Sysrv botnet poses a growing threat.
 arstechnica.com
arstechnica.com
Sysrv Botnet Expands and Gains Persistence
Juniper Threat Labs identified a surge of activity of the Sysrv botnet. The botnet spread itself into Windows and Linux systems by exploiting multiple vulnerabilities, which we will cover in this blog. The threat actor’s objective is to install a Monero cryptominer.