Internet Security designed to protect is a computer virus, which pretends to be a legitimate security program and claims that malware has been detected on your computer. If you try to remove these infections, Internet Security designed to protect will state that you need to buy its full version before being able to do so.
Internet Security designed to protect trojan targets users browsing Internet websites, and rely on social engineering to deliver its payload.
On infected or hacked websites users are prompted by a pop-up window that has been carefully crafted to resemble a legitimate security warning. These pop-up windows typically alert a user of a computer infection, and then prompt the user to download and install Internet Security designed to protect to resolve the apparent issue.
Some of the infections may have come from users downloading an infected codec file when they were trying to watch a video online, or users who receive a spam email and open an infected email attachment.
Once installed, Internet Security designed to protect will display fake security alerts that are designed to think that your data is at risk or that your computer is severely infected.These messages include:
Security Warning
Malicious program has been detected. Click here to protect your computer.Firewall Warning
Hidden file transfers to remote host has been detected.
has detected a leak of your files through the Internet. We strongly recommend that you block the attack immediately.
In reality, none of the reported issues are real, and are only used to scare you into buying Internet Security designed to protect and stealing your personal financial information.
As part of its self-defense mechanism, Internet Security designed to protect virus has disabled the Windows system utilities, including the Windows Task Manager and Registry Editor, and will block you from running certain programs that could lead to its removal.
This rogue antivirus has also modified your Windows files associations, and now whenever you are trying to open a program, Internet Security designed to protect virus will block this operation and display a bogus notification in which will report that the file is infected.
notepad.exe can not start
File notepad.exe is infected by W32/Blaster.worm. Please activate Internet Security 2012 to protect your computer.
If your computer is infected with Internet Security designed to protect virus, then you are seeing the following screen:
Internet Security designed to protect is a scam, and you should ignore any alerts that this malicious software might generate.
Under no circumstance should you buy Internet Security designed to protect as this could lead to identity theft,and if you have, you should contact your bank and dispute the charge stating that the program is a scam and a computer virus.
Registration codes for Internet Security “designed to protect”
As an optional step,you can use any of the following license keys to register Internet Security “designed to protect” and stop the fake alerts.
Internet Security “designed to protect” Activation code: Y68REW-T76FD1-U3VCF5A
Please keep in mind that entering the above registration code will NOT remove Internet Security “designed to protect” from your computer, instead this activation code will just stop the fake alerts so that you’ll be able to complete our removal guide more easily.
Internet Security designed to protect – Virus Removal Guide
This page is a comprehensive guide, which will remove the Internet Security designed to protect infection from your your computer. Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
STEP 1: Start your computer in Safe Mode with Networking (OPTIONAL)
STEP 2: Remove Internet Security designed to protect virus with Malwarebytes Anti-Malware Free
STEP 3: Remove Internet Security designed to protect rootkit with RogueKiller
STEP 4: Remove Internet Security designed to protect infection with HitmanPro
STEP 1 : Start your computer in Safe Mode with Networking (OPTIONAL)
Some variants of the Internet Security designed to protect will not allow you to start some of the below utilities while running Windows in its regular state.
If this happens, we recommend that you start your computer in Safe Mode with Networking, and try from there to perform the below scan.
To start your computer Start your computer in Safe Mode with Networking, you can follow the below steps:
- Remove all floppy disks, CDs, and DVDs from your computer, and then restart your computer.
- When the computer starts you will see your computer’s hardware being listed. When you see this information start to gently tap the F8 key repeatedly until you are presented with the Windows XP, Vista or 7 Advanced Boot Options.
If you are using Windows 8, press the Windows key + C, and then click Settings. Click Power, hold down Shift on your keyboard and click Restart, then click on Troubleshoot and select Advanced options. In the Advanced Options screen, select Startup Settings, then click on Restart. - If you are using Windows XP, Vista or 7 in the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking , and then press ENTER.
\
If you are using Windows 8, press 5 on your keyboard to Enable Safe Mode with Networking.
Windows will start in Safe Mode with Networking.
STEP 2: Remove Internet Security designed to protect virus with Malwarebytes Anti-Malware FREE
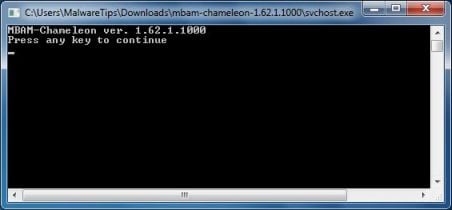
The Malwarebytes Chameleon utility will allow us to install and run a scan with Malwarebytes Anti-Malware Free without being blocked by Internet Security designed to protect rootkit.
- Right click on your browser icon, and select Run As or Run as Administrator. This should allow your browser to open so that we can then download Malwarebytes Chameleon.
If you’ll see a “Warning! The site you are trying visit may harm your computer!” message in your web browser window, you can safely click on the Ignore warnings and visit that site in the current state (not recommended) link, because this a bogus alert from Internet Security designed to protect. - Download Malwarebytes Chameleon from the below link, and extract it to a folder in a convenient location.
MALWAREBYTES CHAMELEON DOWNLOAD LINK (This link will open a new web page from where you can download Malwarebytes Chameleon)
- Make certain that your infected computer is connected to the internet and then open the Malwarebytes Chameleon folder, and double-click on the svchost.exe file.
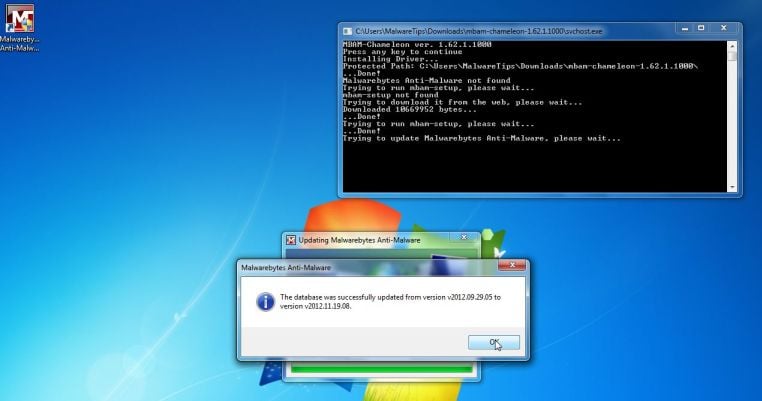
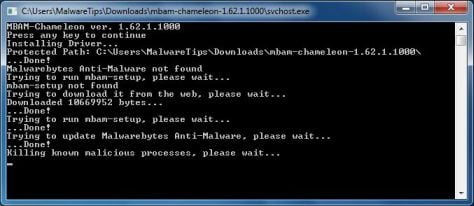
IF Malwarebytes Anti-Malware will not start, double-click on the other renamed files until you find one will work, which will be indicated by a black DOS/command prompt window. - Follow the onscreen instructions to press a key to continue and Chameleon will proceed to download and install Malwarebytes Anti-Malware for you.
- Once it has done this, it will update Malwarebytes Anti-Malware, and you’ll need to click OK when it says that the database was updated successfully.
- Malwarebytes Anti-Malware will now attempt to kill all the malicious process associated with Internet Security designed to protect.Please keep in mind that this process can take up to 10 minutes, so please be patient.
- Next, Malwarebytes Anti-Malware will automatically open and perform a Quick scan for Internet Security designed to protect malicious files as shown below.
- Upon completion of the scan, click on Show Result
- You will now be presented with a screen showing you the malware infections that Malwarebytes Anti-Malware has detected.
Make sure that everything is Checked (ticked),then click on the Remove Selected button.
- After your computer will start in Windows regular mode, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats
STEP 3: Remove Internet Security designed to protect rootkit with RogueKiller
RogueKiller is a utility that will scan for the Internet Security designed to protect virus, registry keys and any other malicious files on your computer.
- You can download the latest official version of RogueKiller from the below link.
ROGUEKILLER DOWNLOAD LINK (This link will automatically download RogueKiller on your computer) - Double click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds, then click on the Scan button to perform a system scan.
- After the scan has completed, press the Delete button to remove Internet Security designed to protect malicious registry keys or files.
STEP 4: Remove Internet Security designed to protect infection with HitmanPro
Some variants of the Internet Security designed to protect virus will install on victims computers a ZeroAccess rootkit. To remove this nasty piece of malware, we will perform a system scan with HitmanPro.
HitmanPro is a cloud on-demand scanner, which will scan your computer with 5 antivirus engines (Emsisoft, Bitdefender, Dr. Web, G-Data and Ikarus) for the Internet Security designed to protect infection.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a web page from where you can download HitmanPro) - Double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.
Click on the Next button, to install HitmanPro on your computer.
- HitmanPro will now begin to scan your computer for Internet Security designed to protect trojan.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the Next button, to remove Internet Security designed to protect virus.
- Click on the Activate free license button to begin the free 30 days trial, and remove all the malicious files from your computer.
Your computer should now be free of the Internet Security designed to protect infection. If your current anti-virus solution let this infection through, you may want to consider purchasing the PRO version of Malwarebytes Anti-Malware to protect against these types of threats in the future, and perform regular computer scans with HitmanPro.
If you are still experiencing problems while trying to remove Internet Security designed to protect from your machine, please start a new thread in our Malware Removal Assistance forum.
![virus [Image: virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/internet-security-designed-to-protect-virus.jpg)
![Alert [Image: Alert]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/Internet-Security-designed-to-protect-alert.jpg)
![Internet Security Firewall Warning [Image: Internet Security Firewall Warning]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/Internet-Security-Firewall-Warning.jpg)
![Internet Security designed to protect Activation code [Image: Internet Security designed to protect Activation code]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/Internet-Security-designed-to-protect-activation.jpg)
![Windows F8 key [Image: F8 key]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/F8-key.jpg.png)
![Safe Mode with Networking screen [Image: Safemode.jpg]](http://malwaretips.com/images/removalguide/safemode.jpg) \
\![Right click on your Web Browser icon and click on Run As Administrator [Image: Starting web browse on infected computer]](http://malwaretips.com/blogs/wp-content/uploads/2013/03/open-web-browser.jpg)
![Extract Malwarebytes Chameleon utility [Image: Extract Malwarebytes Chameleon utility]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/malwarebytes-chameleon-zip.jpg)
![Double click on svchost.exe [Image: Double click on svchost.exe]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/malwarebytes-chameleon-svchost.jpg)
![Malwarebytes Anti-Malware scanning for Internet Security designed to protect [Image: Malwarebytes Anti-Malware scanning for Internet Security designed to protect]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Click on Remove Selected to get rid of Internet Security designed to protect [Image:Malwarebytes removing virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)
![Click on the Start button to perform a system scan [Image: RogueKiller scaning for Internet Security designed to protect virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-scan.jpg)
![Press Delete to remove Internet Security designed to protect [Image: RogueKiller Detele button]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/roguekiller-delete.jpg)




![HitmanPro free 30 days trial [Image: HitmanPro 30 days activation button]](http://malwaretips.com/blogs/wp-content/uploads/2012/11/hitmanpro-activation.jpg)








Hi,
When I try to unzip the chameleon zip file, “Extract all” produces an empty folder for me even though when I look inside the zip I can see the files. Any advice ?
Hello,
Lets run these scan:
STEP 1: Run a scan with ESET Rogue Application Remover
1. Download the ESET Rogue Application Remover by clicking the appropriate link for your system version below
For 32-bit (x86) – http://download.eset.com/special/ERARemover_x86.exe
For 64-bit (x64) – http://download.eset.com/special/ERARemover_x64.exe
2.Save the file to your Desktop. When the download completes, navigate to the file, right-click it and select Run as administrator.
3.Click Accept to accept the End-User License Agreement (EULA).
4. Please be patience while this utility scans for malware, then press any key on your keyboard to exit the tool.
Next please run scan with Malwarebytes Anti-Malware, HitmanPro and RogueKiller. Waiting your reply to see how everything is going.
Stay safe!
Hello,
First off all, scan your computer with Malwarebytes Anti-Malware and HitmanPro, to be on the safe side.
Next, you should report this to your bank, stating that you are the victim of a scam, and you want a refund.
Stay safe!
Hi, my laptop was infected with this Internet Security virus last night, so I’m going to try to remove it using your steps/process outlined above – but one question – do you recommend downloading the various programs first before you start the removal process (i.e., Malwarebytes Anti-Malware, RogueKiller, HitmanPro) OR do you suggest downloading them via links provided while you’re doing the removal process in order of steps outlined above? does it matter? Thanls
Hello,
It does not really matter, but I suppose that it would be better if you first downloaded all the tools, then run them.
Stay safe~!
Hello,
You can use any random email. Eg: any@email.com
Stay safe!
Thanks a lot you saved my office cpu, great tutorial. I discovered real antiviruses. THANK YOU!
thank You
Hello Joel,
Please try to perform the Malwarebytes scan while your computer is in Windows Safe Mode with Networking.
To start your PC in Safe mode with Networking, press and hold the F8 key as your computer restarts.Please keep in mind that you need to press the F8 key before the Windows start-up logo appears.
Note: With some computers, if you press and hold a key as the computer is booting you will get a stuck key message. If this occurs, instead of pressing and holding the “F8 key”, tap the “F8 key” continuously until you get the Advanced Boot Options screen.
In addition, to make the malware removal process easier, you can use this Internet Security Activation code: Y68REW-T76FD1-U3VCF5A .
Waiting for your reply. Stay safe!
Thank you so much! I knew it was a Scam beforehand when I didn’t download it and was asking for money but wasn’t sure how to fix it since I already had Malware Anti-byte nothing came up, and McAfee is truly shocking alot of the time so Ill proberly Installing Norton soon but Thanks ALOT! ~ Australia
Brilliant!! Thanks a lot – RogueKiller seems to have done the job!
I started to go about removing it and I stopped the scan and then found this site. I went to enter in the activation code and the program disappeared. It even went away from the files when I opened the file location. Should I still go through all these steps? It seems to be gone but I’m not sure. My browser is working, and if I try to open anything it also works. Really confused that it’s just gone.
Hello Kate,
I would advise you to run a scan with Malwarebytes and HitmanPro, just to make sure that there aren’t any left over files on your computer.
Stay safe!
thank you soooo much for this!!!!
Thanks so much!
Excellent directions! Thank you. The malware developers are getting ever-more clever. I appreciated finding this at the top of my web search when I became suspicious of the generic name “Internet Security”.
Thanks. This seemed to work based on the steps listed.
Thank you so much for the easy to follow steps to get Internet security malware off my computer!