When you open the Task Manager on your Windows computer, you may notice a process called “Service Host: Task Scheduler” running in the background. This process is an essential part of the Windows operating system and plays a crucial role in managing scheduled tasks and system maintenance. In this article, we will explore why the Service Host: Task Scheduler process is running in Task Manager and its significance in maintaining a healthy and efficient system.
![Service Host: Task Scheduler [Process Explained] 1 Windows Task Manager](https://malwaretips.com/blogs/wp-content/uploads/2023/06/Windows-Task-Manager.jpg)
Understanding the Task Scheduler
The Task Scheduler is a built-in Windows utility that allows users to schedule tasks to run automatically at specific times or in response to certain events. These tasks can include system maintenance activities, software updates, backups, and various other operations. The Task Scheduler ensures that these tasks are executed efficiently and without user intervention.
When you schedule a task using the Task Scheduler, it creates an entry in the Windows Registry and stores the necessary information about the task, such as the program to run, the trigger conditions, and the user account under which the task should be executed. The Task Scheduler service is responsible for managing these tasks and ensuring they are executed as scheduled.
The Service Host: Task Scheduler Process
The Service Host: Task Scheduler process, also known as “svchost.exe,” is a system process that hosts multiple Windows services, including the Task Scheduler service. It acts as a container for these services, allowing them to run in the background without interfering with the user’s activities.
By hosting the Task Scheduler service within the Service Host process, Windows can efficiently manage and allocate system resources. This approach improves system performance and stability by preventing a single service from consuming excessive resources or causing system crashes.
Why Is the Service Host: Task Scheduler Process Running?
The Service Host: Task Scheduler process is running in Task Manager because it is responsible for managing all scheduled tasks on your computer. Even if you haven’t explicitly scheduled any tasks yourself, various system processes and applications rely on the Task Scheduler to perform essential operations.
Here are some common reasons why the Service Host: Task Scheduler process may be running:
- System Maintenance: Windows uses the Task Scheduler to perform routine maintenance tasks, such as disk defragmentation, system backups, and Windows updates. These tasks are crucial for keeping your system running smoothly and protecting it from security vulnerabilities.
- Application Updates: Many software applications use the Task Scheduler to check for updates and install them automatically. These updates often include bug fixes, security patches, and new features, ensuring that your applications are up to date and functioning optimally.
- Background Services: Some background services, such as antivirus scans, system diagnostics, and performance optimizations, rely on the Task Scheduler to run at specific times or intervals. These services help keep your system secure, stable, and performing at its best.
Should You Be Concerned?
Seeing the Service Host: Task Scheduler process running in Task Manager is completely normal and not a cause for concern. It is an integral part of the Windows operating system and plays a vital role in maintaining system health and performance.
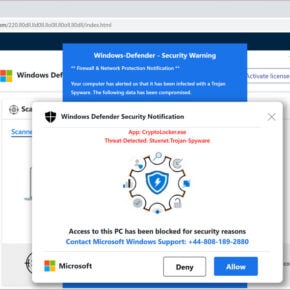
However, it is essential to ensure that the process is not being abused by malware or viruses. Malicious software can disguise itself as legitimate processes to avoid detection. Therefore, it is always a good practice to regularly scan your system for malware and viruses using reliable security software like Malwarebytes Free.
Conclusion
The Service Host: Task Scheduler process running in Task Manager is a critical component of the Windows operating system. It manages scheduled tasks, system maintenance activities, and background services, ensuring that your computer runs smoothly and efficiently.
While the presence of the Service Host: Task Scheduler process is normal, it is essential to remain vigilant and regularly scan your system for malware and viruses. By doing so, you can ensure that your system remains secure and protected from potential threats.
Remember, the Service Host: Task Scheduler process is just one of the many processes running on your computer, each serving a specific purpose. Understanding these processes and their significance can help you make informed decisions about system optimization and troubleshooting.


![Remove Trahingly.com Pop-up Ads [Virus Removal Guide] 7 McAfee scam 4](https://malwaretips.com/blogs/wp-content/uploads/2023/08/McAfee-scam-4-290x290.jpg)