With the rise of technology and the increasing reliance on digital platforms, cybercriminals have found new ways to exploit unsuspecting individuals. One such scam that has gained popularity in recent years is the ‘Account Accessed In Another Location’ Apple phishing scam. This article aims to provide a comprehensive overview of this scam, including what it is, how it works, what to do if you have fallen victim, and other relevant data.

What is the ‘Account Accessed In Another Location’ Apple Phishing Scam?
The ‘Account Accessed In Another Location’ Apple phishing scam is a type of cyber attack where scammers attempt to trick Apple users into revealing their personal information, such as login credentials and financial details. The scam typically starts with an email or text message that appears to be from Apple, informing the user that their Apple ID has been accessed from a different location.
The message often includes alarming language, such as “Your account has been compromised” or “Unauthorized access detected.” The scammers aim to create a sense of urgency and panic in the recipient, prompting them to take immediate action without thinking critically.
How Does the Scam Work?
Once the user receives the phishing message, they are usually directed to click on a link or download an attachment to verify their account or secure their Apple ID. These links and attachments are designed to look legitimate, often mimicking Apple’s official website or login page.
However, these websites and login pages are cleverly crafted by scammers to capture the user’s login credentials and other sensitive information. When the user enters their details, the scammers gain access to their Apple account, allowing them to steal personal information, make unauthorized purchases, or even commit identity theft.
Signs of a Phishing Scam
It is crucial to be able to identify phishing scams to protect yourself from falling victim. Here are some signs that can help you recognize a phishing attempt:
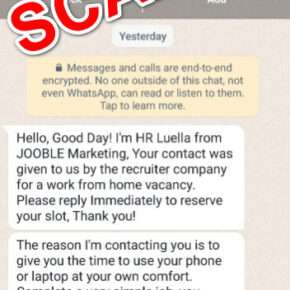
- Generic greetings: Phishing emails often use generic greetings like “Dear Customer” instead of addressing you by name.
- Urgency: Scammers create a sense of urgency, pressuring you to take immediate action without thinking.
- Spelling and grammar mistakes: Phishing emails often contain spelling and grammar errors, indicating a lack of professionalism.
- Unusual sender email address: Check the sender’s email address carefully. Phishing emails often use email addresses that are slightly different from the official ones.
- Request for personal information: Legitimate companies will never ask you to provide personal information via email or text message.
What to Do If You Have Fallen Victim?
If you have fallen victim to the ‘Account Accessed In Another Location’ Apple phishing scam, it is essential to take immediate action to minimize the damage. Here are the steps you should follow:
- Change your Apple ID password: Go to the official Apple website and change your password immediately. Make sure to choose a strong and unique password.
- Contact Apple Support: Inform Apple about the scam and provide them with any relevant information. They can guide you on further steps to secure your account.
- Monitor your accounts: Keep a close eye on your bank accounts, credit cards, and other financial accounts for any suspicious activity. Report any unauthorized transactions immediately.
- Scan your device for malware: Run a scan with Malwarebytes Free or any reputable antivirus software to ensure your device is free from malware.
- Enable two-factor authentication: Enable two-factor authentication for your Apple ID to add an extra layer of security.
Protecting Yourself from Phishing Scams
Prevention is always better than cure when it comes to phishing scams. Here are some measures you can take to protect yourself:
- Be cautious of unsolicited emails and text messages: Do not click on links or download attachments from unknown sources.
- Verify the sender’s identity: Double-check the sender’s email address and contact the company directly if you are unsure about the legitimacy of the message.
- Keep your software up to date: Regularly update your operating system, web browsers, and antivirus software to ensure you have the latest security patches.
- Use strong and unique passwords: Avoid using common passwords and consider using a password manager to generate and store complex passwords.
- Educate yourself: Stay informed about the latest phishing techniques and scams to recognize and avoid them.
Summary
The ‘Account Accessed In Another Location’ Apple phishing scam is a prevalent cyber attack that aims to deceive Apple users into revealing their personal information. By understanding how this scam works and being able to identify phishing attempts, individuals can protect themselves from falling victim. If you have fallen victim, it is crucial to take immediate action by changing your password, contacting Apple Support, monitoring your accounts, scanning your device for malware, and enabling two-factor authentication. By following these steps and implementing preventive measures, you can safeguard yourself against phishing scams and maintain your online security.