If you have ever seen a post on X claiming Elon Musk is doing a “live” crypto giveaway, you already know how it’s framed: huge numbers, a short window to act, and a simple promise that sounds almost mechanical. Send a little crypto to “verify” your wallet, and you’ll get more back right away.
That story is the scam.
These Elon Musk X crypto giveaway scam sites are built to look official long enough to trigger one irreversible action: a transfer to a wallet you do not control. Once that happens, the page can stall, vanish, or demand more, but the outcome is almost always the same. Victims get nothing back.
Scam Overview
The “Elon Musk X crypto giveaway” scam is a repeatable, mass-produced theft playbook that rotates across domains, social posts, and landing pages. The design changes, the numbers change, and the “event” changes, but the core pitch rarely does.
You are told there is a giveaway or airdrop. You are shown a wallet address. You are instructed to send crypto first. You are promised a larger amount in return.
That is not a giveaway. It is a transfer to a scammer.
What these scams usually look like in the real world
Most people encounter this scam in one of a few ways:
- A post on X that appears to come from a recognizable account, sometimes with a verified badge
- A reply under a trending Elon Musk or crypto-related post that links to an “official claim page”
- A “livestream” style post with a banner graphic and a countdown timer
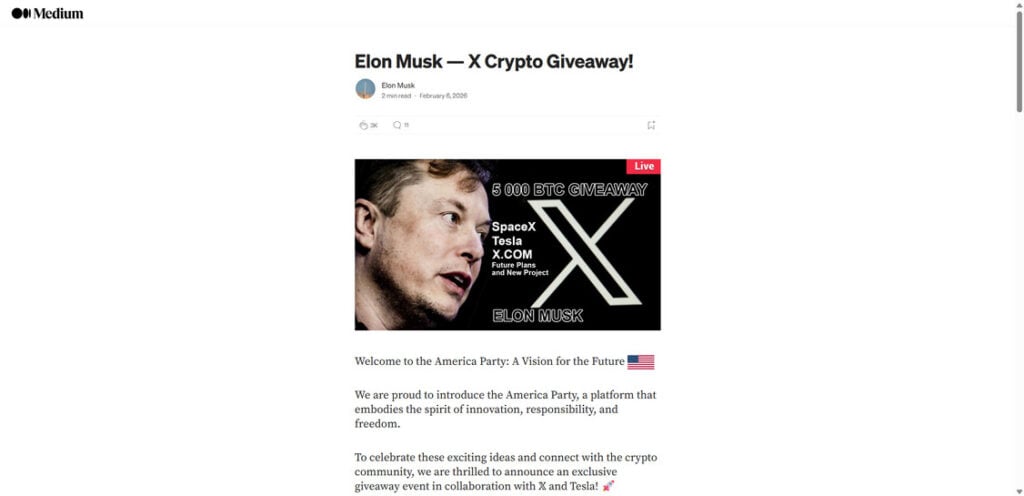
- A Medium-style story or blog page that reads like an announcement and funnels you to a claim button
- A screenshot of a supposed Elon Musk post, paired with a link and “limited allocation” language
The common thread is urgency. The scam is designed so you feel like you need to act first and verify later.
Why Elon Musk is used so often
Scammers do not choose public figures at random. They choose names that can lower skepticism in seconds.
Elon Musk has a long public association with crypto conversations, especially Dogecoin, and his name carries an “anything is possible” vibe for many readers. That makes it easier for a scammer to sell a ridiculous premise like:
- 5,000 BTC is being given away
- 100,000 ETH is being distributed today
- 50,000,000 DOGE is being “allocated to the community”
- $250,000,000 worth of a new token is being handed out
Those numbers are not meant to be realistic. They are meant to overwhelm your judgment and trigger urgency.
The giveaway promise that exposes the whole operation
There is one claim that defines this entire scam category:
“Send crypto to receive more crypto back.”
Sometimes it is phrased as “2x back.” Sometimes it is “bonus tiers.” Sometimes it is “verify your wallet address.” Sometimes it is a “refund if you are late.”
However it is phrased, it is the same mechanism: you send funds first, and the scammer keeps them.
Real promotions do not require you to pay money to receive a prize. Real airdrops do not “verify” your wallet by taking your funds. Real organizations do not run giveaways from random domains with copy-paste wallet addresses.
Common variations you will see
Most of these pages let you choose from a menu of popular coins, because scammers want the widest audience possible. The most common options are:
- Bitcoin (BTC)
- Ethereum (ETH)
- Dogecoin (DOGE)
- Tether (USDT), often across multiple networks
- Sometimes a new token with a name that sounds official, paired with a huge dollar figure like $250,000,000
The page design often includes:
- A “Choose your cryptocurrency” section
- A minimum and maximum amount, such as 0.05 ETH to 50 ETH
- A QR code and a copy-to-clipboard wallet address
- A “waiting for your transaction…” status message
- A “recent transactions” feed that claims payouts are happening
- A comments section filled with “It worked” style messages
- A counter showing how much crypto is “left”
None of that is proof. It is conversion design.
Why the scam is so effective even when it sounds absurd
A lot of victims feel embarrassed afterward because, in hindsight, the pitch looks obvious. The reason it works is not intelligence. It is timing and pressure.
These pages are built around predictable human behavior:
- People trust familiar names, especially in a hurry
- People assume “verification” steps are normal in crypto
- People see a transaction feed and assume the system is real
- People send a small test amount “just to try,” then send more when nothing happens
- People do not realize how final crypto transfers are until it is too late
The scam also exploits a subtle misunderstanding: many users know there are real airdrops and real token distributions, but they do not know what legitimate claim flows look like. Scammers step into that gap and provide a fake “claim flow” that ends in theft.
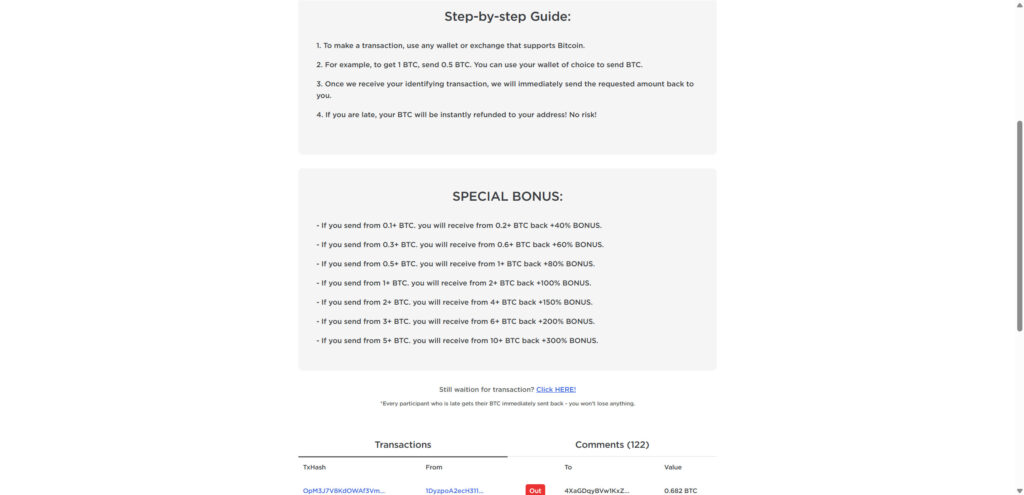
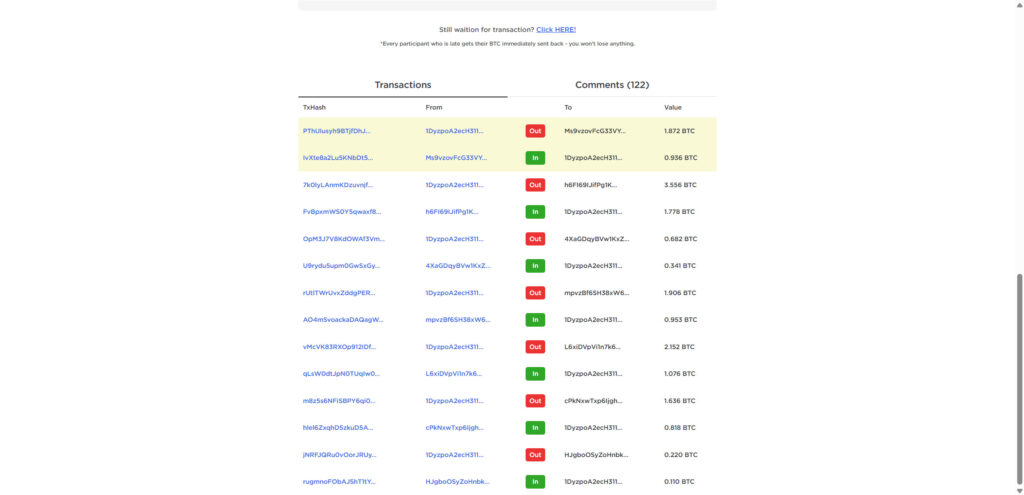
The role of fake social proof
If you look closely at these scam pages, you will see social proof everywhere. It is rarely accidental.
Common examples include:
- A “recent transactions” table with green check marks
- Status labels like “completed,” “confirmed,” or “sent”
- A scrolling ticker of usernames and amounts
- Comments claiming huge payouts, sometimes written in unnatural patterns
- “Live updates” badges
This is meant to answer your doubts without letting you leave the page. If you search the domain, the scam collapses. If you stay on the page, the scam can keep you moving.
Why domain names change constantly
One reason these scams keep working is that they are not tied to a single site. They are campaigns.
Scammers rotate domains because:
- Domains get reported and suspended
- Social platforms remove posts and accounts
- Wallet addresses get flagged
- Search results start warning people
So they rebuild the same template under a new name and start again.
You might see the same layout on 20 different domains over a few weeks. Some will look like “prize” or “event” sites. Some will mimic tech brands. Some will use short, clean names to appear official. Many will use domain age as a weapon, vanishing before reports catch up.
The biggest red flags that matter most
If you are reading this because you saw a giveaway post on X, these are the red flags that should stop you immediately:
- Any “giveaway” that requires you to send crypto first
- Any claim that a transfer “verifies” your wallet or “activates” your allocation
- A QR code and copy button as the main call to action
- Huge numbers paired with urgency, like 5,000 BTC or 100,000 ETH
- Bonus tiers that reward larger deposits with higher returns
- Vague “official” language with no verifiable source
- A domain that is not clearly tied to an official organization
The moment you are asked to send money to receive money, the giveaway is over. It was never real.
Secondary risks beyond the initial transfer
Some versions of this scam are “send-to-address” only. Others are more dangerous.
Higher-risk variations include:
- Wallet-drainer pages that ask you to connect a wallet and approve permissions
- Fake airdrop claim pages that prompt you to sign a message
- Malicious smart contracts that drain tokens after approval
- Phishing pages that try to collect seed phrases or exchange logins
- “Support” chats that push remote access software or a fake recovery service
So even if you did not send crypto, interacting with the site can still create risk if you connected a wallet or entered sensitive information.
The recovery scam that often follows
After someone loses crypto, scammers often try to extract more by posing as helpers.
They may claim:
- They can recover your funds for a fee
- They have “insider access” at an exchange
- They work in blockchain tracing
- They know the attacker and can negotiate
Most of these offers are a second scam. They are targeting someone who is stressed, embarrassed, and eager to fix the situation quickly.
How The Scam Works
This section breaks down the typical funnel step by step. The goal is to make the pattern obvious, so the next time you see it, you recognize it immediately.
Step 1: The bait appears on X where attention is already high
The scam commonly begins on X because the platform is fast-moving and trend-driven.
You might see:
- A post claiming a “live event” is happening now
- A reply under a popular crypto thread that says “official giveaway link”
- A short clip that looks like an interview or livestream overlay
- A graphic with Elon Musk’s face and a giant giveaway number
Sometimes the account looks legitimate at a glance. Sometimes it is a new account with a high-volume reply pattern. Sometimes it is a compromised account that used to post normal content.
The goal is not to convince everyone. The goal is to catch a small percentage of people at exactly the right moment.
Step 2: The link leads through redirects designed to reduce scrutiny
Many scam campaigns use redirect chains.
That means you click one link, then you bounce through one or more pages before landing on the final scam portal. This can be used to:
- Hide the final domain from automated filters
- Serve different content depending on device or region
- Make it harder for users to backtrack and report
- Replace the destination quickly without changing the original post
To the victim, it feels like a normal load. To the scammer, it is a way to keep the funnel stable while swapping pieces behind the scenes.
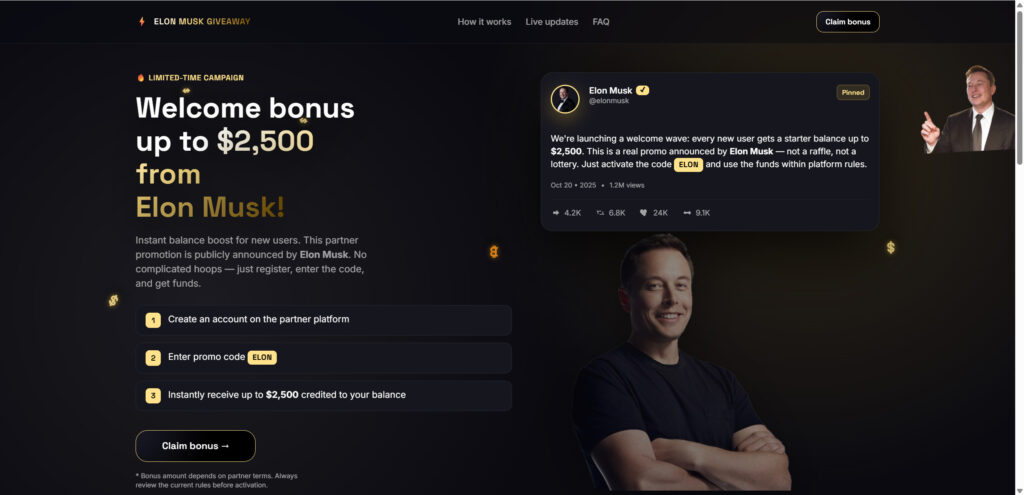
Step 3: A trust-building page makes the story feel official
Not every scam sends you directly to the wallet address. Many use a “pre-sell” page first.
This pre-sell page may look like:
- A blog announcement explaining why the giveaway is happening
- A Medium-style article with a headline like “X Crypto Giveaway”
- A “press release” page with formal language and a hero image
- A fake thread embed showing a supposed Elon Musk announcement
The job of this page is simple: give your brain a reason to stop questioning the premise.
It often includes phrases like:
- “In celebration of a major milestone”
- “To support the crypto community”
- “Limited allocation”
- “First come, first served”
- “Official claim link below”
The page is not there to inform you. It is there to push you one click closer to the wallet address.
Step 4: The giveaway portal asks you to select a coin and amount
Once inside the portal, the scam becomes more mechanical.
You are typically shown:
- A list of supported cryptocurrencies
- A minimum and maximum deposit range
- A clean set of steps that look like a checkout flow
- A promise like “get 2x back instantly”
Sometimes it is framed as an “airdrop.” Sometimes it is framed as a “giveaway.” The name does not matter. The mechanics do.
This step is designed to create momentum. It turns a questionable story into a “process.”
Step 5: The page presents the wallet address, QR code, and the real ask
This is the moment where the scam becomes theft.
The portal will show:
- A wallet address
- A copy button
- A QR code
- A “waiting for transaction” indicator
- Sometimes a countdown timer or “left” counter
This layout exists because it reduces friction. There is no form to fill out, no identity to verify, no real eligibility to prove.
The only requirement is your money.
Step 6: “Wallet verification” language is used to justify an upfront transfer
At this point, many people feel a flicker of doubt. The scam anticipates that doubt and offers a story that sounds technical.
Common justifications include:
- “Verify your wallet address”
- “Activate your allocation”
- “Confirm eligibility”
- “Anti-bot measure”
- “Network validation”
- “Refund if late”
This is where people get tricked, because it is presented as a temporary step, not a payment.
In reality, the transfer is the whole scam. There is no verification system on the other side that sends rewards. There is only a wallet that receives deposits.
Step 7: Fake proof is shown to keep you from leaving
The scam wants you to stay on the page long enough to send.
So it gives you “evidence” that feels real:
- A transactions feed showing “payouts”
- Status markers and green check icons
- Comments from supposed participants
- A counter showing the giveaway is almost over
This proof is often fabricated or misleading.
Even if a transaction feed includes real on-chain activity, that activity can simply be deposits flowing into the scam wallet. A scammer can also move funds between wallets to simulate “payouts.”
The point is not truth. The point is comfort.
Step 8: The victim sends crypto, then the page stalls
After a victim sends crypto, most outcomes fall into a small set of patterns:
- The page stays stuck on “waiting for your transaction”
- A message appears blaming network congestion
- The page claims the transfer was “not detected” and asks to resend
- A chat widget appears offering help
- The scammer asks for a second payment to “unlock” the payout
Victims often wait because crypto networks can be slow sometimes, and scammers rely on that uncertainty. It gives them room to push the next stage.
Step 9: The second-stage extraction begins
Once someone has already sent crypto, they are more likely to send again. Scammers know this, and they exploit it.
Second-stage tactics include:
- Claiming you must send a “verification fee”
- Claiming you must pay a “release fee”
- Claiming your deposit was below the minimum
- Claiming your wallet is “unverified” until you send more
- Offering a “bonus” if you top up quickly
This is where losses can grow from a small test deposit to a major hit.
If you see any demand for an additional payment, assume you are dealing with a scammer trying to maximize your loss.
Step 10: In more advanced versions, the scam shifts from transfers to wallet draining
Some Elon Musk X giveaway scam sites are not limited to “send crypto to this address.” Instead, they try to get direct control over your wallet permissions.
These variants may ask you to:
- Connect your wallet
- Approve a token spend
- Sign a message to “verify”
- Interact with a contract to claim a reward
If you approve a malicious contract, the scam can drain tokens without another obvious action from you.
This is one of the reasons it is dangerous to interact with any “giveaway” page that is not clearly tied to an official project, even if you never hit send.
Step 11: The scam ends with domain rotation and rapid fund movement
Once the campaign has extracted enough deposits, the domain may:
- Go offline
- Redirect to a new domain
- Show a generic error page
- Switch to a different coin or “event” theme
Meanwhile, funds are usually moved quickly across wallets. The goal is to reduce the chance of tracing and freezing, especially if victims report to exchanges.
This is why time matters when reporting, and why prevention is so important.
What To Do If You Have Fallen Victim to This Scam
If you sent crypto to one of these giveaway pages, the most helpful thing you can do is shift from hope to containment. Here is a practical path that prioritizes what actually helps.
- Stop sending money, even if the page claims you are close to receiving the payout
If you already sent once, the highest risk is sending again. Do not pay “verification fees,” “release fees,” or “gas fees” tied to the giveaway. - Document everything before it disappears
Take screenshots of:
- The giveaway page
- The domain name
- The wallet address and QR code
- Any bonus tiers or rules
- Any chat messages or prompts
Save:
- Transaction hash (TXID)
- Amount sent
- Date and time
- The network used (important for coins like USDT)
- If you sent from an exchange, contact the exchange immediately
Open a support ticket and include:
- TXID
- Destination address
- Amount
- The scam domain
Ask if they can flag the destination address and provide any additional reporting guidance. Recovery is not guaranteed, but fast reporting improves the odds of catching funds while they are still in an exchange-controlled environment.
- If you sent from your own wallet, assume the transfer is final and focus on preventing further loss
Most crypto transactions are irreversible after confirmation. The priority becomes protecting remaining assets and preventing additional compromise. - If you connected a wallet to the scam site, treat it as urgent
If you connected a wallet or approved anything:
- Move remaining assets to a fresh wallet that has not interacted with the scam site
- Revoke any suspicious approvals on the affected wallet
- Do not reconnect to the scam site to “undo” anything
- If you entered a seed phrase or private key anywhere, act immediately
If you typed a seed phrase, private key, or recovery phrase into any site:
- Consider that wallet fully compromised
- Move all funds out immediately to a new wallet
- Do not reuse that seed phrase again
- Secure your email and exchange accounts
Even if this scam started as a wallet transfer, some campaigns pivot to account takeover.
Do the basics:
- Change passwords for your email and exchange accounts
- Enable 2FA wherever possible
- Check account login history for unusual activity
- Remove suspicious authorized apps or devices
- Check your device for malicious extensions or downloads
If the scam site prompted you to install anything, assume risk.
- Remove unknown browser extensions
- Uninstall unfamiliar programs
- Run a reputable security scan
- Update your browser and OS
- Watch for recovery scammers
After crypto theft, victims often receive messages offering recovery services. Common hooks include:
- “Blockchain investigator”
- “Chargeback specialist”
- “Exchange insider”
- “We found your funds”
Do not pay upfront fees, do not share sensitive information, and do not install remote access tools.
- Report the scam
Reporting helps build case volume and can support takedowns.
Report to:
- The social platform where you saw it
- The domain registrar or hosting provider
- Your local cybercrime reporting system
- If you are in the United States, the FBI Internet Crime Complaint Center (IC3)
Even if you cannot recover funds, reporting helps reduce future victims and improves the chance that a destination wallet gets flagged.
- Tell others where you found it, without amplifying the scam link
A short warning can protect others, especially if the scam is spreading through replies or reposts.
If you post about it:
- Do not include the clickable link
- Share the domain as plain text, or in a screenshot
- Encourage others to report the post
The Bottom Line
Elon Musk X crypto giveaway scam sites are not complicated once you know what to look for. They dress up a simple theft request with branding, urgency, and fake proof.
The moment a “giveaway” asks you to send crypto first, it stops being a giveaway. It is a scam.
If you already sent funds, do not chase the payout with more payments. Lock down what you can, document everything, contact your exchange if one was involved, and report the scam. And going forward, keep one rule in place no matter how polished the page looks: you never need to send crypto to receive free crypto.
FAQ
Is the Elon Musk X crypto giveaway real?
No. These are scam campaigns that use Elon Musk’s name and X-style branding to steal cryptocurrency. The “giveaway” story is the hook, and the wallet address is the trap.
Does Elon Musk have anything to do with these giveaway sites?
No. Scammers impersonate him and borrow credibility from X (and often Tesla or SpaceX) to make the offer feel legitimate.
Why do these pages say “send crypto to verify your wallet”?
Because “verification” sounds like a normal step. In reality, it is just a request to send funds to a scammer-controlled address. Legit giveaways do not verify wallets by taking your crypto.
How does the “send crypto and get 2x back” part work?
It does not. Once you send crypto to their address, you have completed the scammer’s goal. The promise of “2x back” is the bait that makes the transfer feel like a transaction instead of a loss.
What coins do these scams usually target?
Most versions offer multiple options to capture more victims, commonly:
- BTC
- ETH
- DOGE
- USDT (often across different networks)
The coin list changes, but the pattern stays the same: send first, receive nothing.
The site shows “recent transactions” and payouts. Is that proof?
No. Those tables can be fake, staged, or misleading. Even if the wallet shows real incoming deposits on-chain, that proves only that victims are sending funds, not that payouts are happening.
Why do they use QR codes and copy buttons so prominently?
To reduce friction and speed up the transfer. The fewer steps it takes to send, the less time you have to stop and verify the domain or search for warnings.
Some pages show a countdown timer or “crypto left” counter. Is that real?
Usually not. Timers and “left” counters are used to create urgency and push you into acting before you think.
I sent crypto. Can I get it back?
In most cases, no. Crypto transfers are generally irreversible once confirmed. If you sent from an exchange, contact the exchange support team immediately with the transaction ID (TXID) and destination address. It rarely leads to recovery, but reporting quickly is still important.
I sent from my own wallet. Can they drain the rest of my wallet?
If you only sent a transfer to their address, they usually cannot drain your wallet automatically from that alone.
However, if you connected your wallet to the site or approved token permissions, the risk increases.
The site says my payout is “pending” and asks me to send more for a fee. Should I?
No. That is a classic second-stage tactic. “Verification fees,” “release fees,” “gas fees,” or “top-ups” are attempts to extract more money after the first transfer.
What if I connected my wallet or clicked “Connect Wallet”?
Assume elevated risk:
- Move remaining assets to a fresh wallet
- Revoke any suspicious token approvals on the affected wallet
- Stop interacting with the scam site and any related links
How can I tell a real giveaway from a scam quickly?
Use this rule: Any giveaway that requires you to send crypto first is a scam.
Legitimate promotions do not ask for upfront transfers to a random wallet address.
Why do the scam sites keep changing domains?
To evade takedowns and reports. The same template gets cloned and relaunched under new domains as old ones are flagged.
Are there “recovery services” that can get my crypto back?
Be careful. Many recovery offers are follow-up scams aimed at victims. Do not pay upfront fees, do not share seed phrases, and do not install remote access software.
Where should I report these scams?
Report:
Local cybercrime reporting channels
If you are in the United States, report to FBI Internet Crime Complaint Center (IC3).
The social post or account on X
The domain to the registrar/hosting provider
The scam as phishing in your browser







