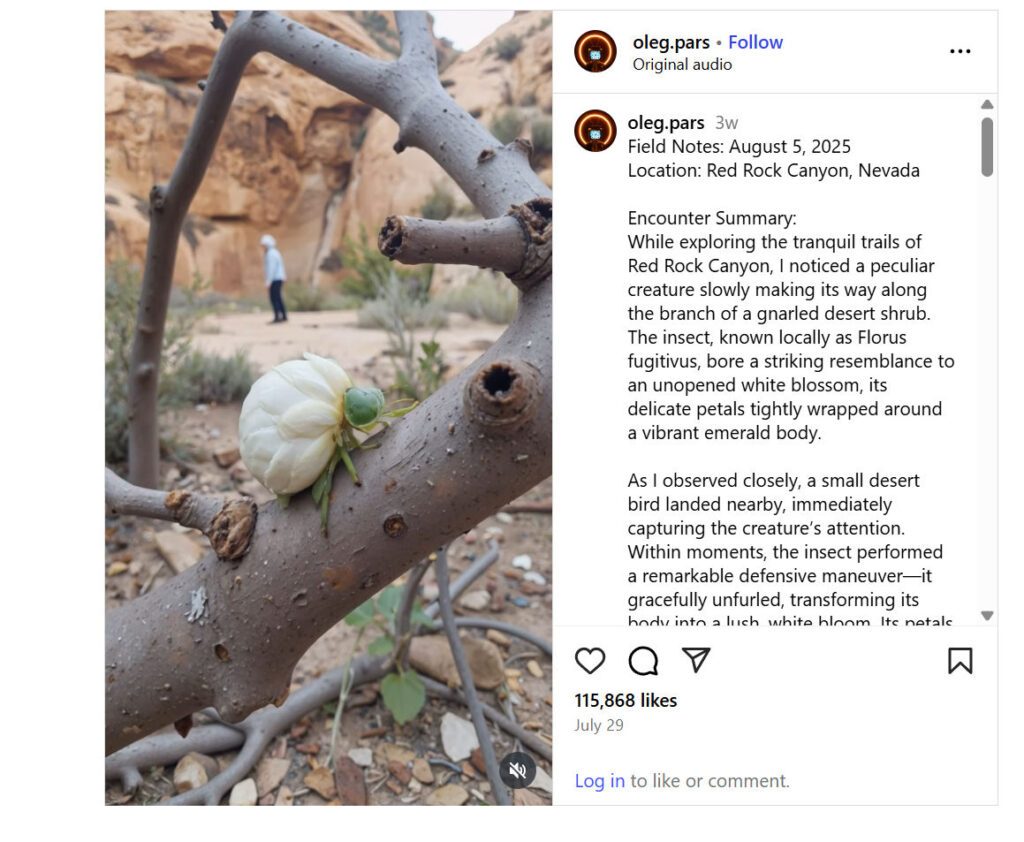
In recent weeks, social media has been captivated by a strange and mesmerizing video. It shows what appears to be an insect that slowly crawls along the branch of a desert shrub, its body resembling a tightly wrapped flower bud. Suddenly, when disturbed, the insect unfurls into what looks like a lush white blossom.
This supposed new species has been given the name Florus Fugitivus. The caption claims it was filmed at Red Rock Canyon, Nevada, a well-known desert conservation area near Las Vegas.
With over 100,000 likes and millions of views, the clip has sparked heated debate. Is this a true biological discovery, or is it another AI-generated insect-to-flower hoax like others that have gone viral in 2024 and 2025?
This article dives into the origins of Florus Fugitivus, the scientific impossibilities behind the claim, and how digital artistry and artificial intelligence have fueled a new wave of nature hoaxes online.
What the Video Claims
The Instagram post presenting the footage includes a field note-style description:
- The insect is introduced as Florus Fugitivus, allegedly observed in Red Rock Canyon.
- It is described as resembling an unopened white rosebud, with petals tightly wrapped around its green body.
- When a small desert bird approaches, the insect performs a “defensive maneuver” by unfurling into a full blossom, thereby deterring predators.
- The caption frames the event as a rare, almost magical biological behavior.
This narrative is compelling. It borrows the language of field biology and creates an aura of mystery around a supposedly undiscovered desert species.
Fact-Check: Is Florus Fugitivus Real or Fake?
The answer is straightforward: Florus Fugitivus is not real. It is part of a growing trend of AI-generated insect-flower hoaxes circulating on social media.
There is no scientific record of such a species in any entomology database. No peer-reviewed research papers, museum collections, or field surveys mention Florus Fugitivus. The story is a carefully constructed digital illusion designed to go viral.
Key Red Flags That Expose the Hoax
1. The Biological Impossibility
Insects cannot sprout flowers. Plants and animals belong to entirely separate kingdoms of life, with fundamentally different biological processes. Evolution does allow for mimicry, but an actual transformation from insect to flower is impossible.
2. The Fabricated Latin Name
The name Florus Fugitivus is constructed to sound scientific but is not recognized in zoological taxonomy.
- “Florus” suggests flower.
- “Fugitivus” translates to fugitive or elusive.
Put together, it means “elusive flower,” which feels poetic rather than scientific.
3. Lack of Scientific Documentation
If a creature like this truly existed, it would be a global scientific sensation. The discovery would be covered in journals like Nature or Science, not just in Instagram posts.
4. Signs of Digital Creation
Close analysis of the footage reveals AI-generated traits:
- The “flower” unfurling sequence looks too symmetrical and smooth.
- The lighting on the petals doesn’t match the natural desert shadows.
- The insect’s body proportions shift unnaturally, resembling CGI animation.
5. Source of the Video
The account behind the video, oleg.pars, is known for producing insect-flower hybrid content using AI art platforms like Krea AI. Many of these clips have gone viral in the past, including other fake species like Mantiflora Aurantia and Nymphaeomorphus Vigilis.
Why Red Rock Canyon Was Chosen as the Location
Choosing Red Rock Canyon, Nevada adds an air of credibility. This is a real conservation area famous for its sandstone formations, desert wildlife, and hiking trails. It is plausible that an unusual insect might be discovered in such a rugged, biodiverse environment.
But here’s the truth: no official survey of Red Rock Canyon has ever reported such a species. By attaching a real place to a fake insect, the hoax gains authenticity without evidence.
Comparison With Real Insects
While Florus Fugitivus is fabricated, real insects exhibit remarkable camouflage and mimicry. This is why the hoax feels believable at first glance.
- Orchid Mantis (Hymenopus coronatus): Mimics orchid petals to lure prey.
- Leaf Insects (Phyllium): Look exactly like leaves, complete with veins and brown “bite marks.”
- Flower Beetles (Cetoniinae): Brightly colored beetles that feed on blossoms, often mistaken for petals themselves.
- Jewel Beetles (Buprestidae): Iridescent beetles with metallic exoskeletons.
These species show how evolution produces astonishing disguises. But none of them cross the boundary into flower-blooming transformations.
The Role of AI in Creating Nature Hoaxes
AI platforms like Krea AI, MidJourney, and Stable Diffusion make it possible to generate ultra-realistic insect hybrids. Artists use them to produce imaginative visuals, but once these clips are reposted without disclaimers, they are mistaken for real discoveries.
The rise of such hoaxes reflects how blurred the line between digital art and scientific fact has become.
Why People Believe the Florus Fugitivus Hoax
- Scientific-Sounding Name: Latinized species names carry authority.
- Exotic Location: Red Rock Canyon is believable as a site for discovery.
- Visual Shock Value: A flower emerging from an insect is mesmerizing.
- Pattern of Realism: Nature already contains convincing mimics like orchid mantises, so viewers find it plausible.
The Psychology of Viral Nature Hoaxes
These viral clips thrive on human psychology:
- Wonder and Curiosity: People want to believe there are still secrets in nature.
- Visual Virality: Eye-catching transformations spread rapidly on TikTok and Instagram.
- Authority Illusion: Pseudo-scientific captions and “field notes” lend credibility.
- Community Buzz: Debates in comment sections drive engagement, further boosting the video.
The Consequences of Misinformation
While some may dismiss Florus Fugitivus as harmless fun, these hoaxes do cause problems:
- They mislead the public about science and evolution.
- They weaken trust in real biological research.
- They distract from pressing conservation issues like habitat loss and species extinction.
- They create confusion between genuine discovery and digital fabrication.
How to Identify Fake Species in the Future
To avoid being misled by viral hoaxes like Florus Fugitivus, here are some practical tips:
- Search the Name in Scientific Databases – Real species are listed in official taxonomic resources.
- Check for Peer-Reviewed Sources – True discoveries appear in journals and reputable media.
- Look for AI Watermarks – Many viral videos carry subtle “Made with Krea AI” tags.
- Analyze the Footage – Watch for lighting inconsistencies and overly perfect symmetry.
- Be Wary of Instagram or TikTok-Only Claims – Extraordinary scientific discoveries are never revealed solely on social media.
Lessons From the Florus Fugitivus Hoax
- Digital Creativity is Powerful – AI allows artists to create stunning illusions.
- Critical Thinking is Vital – The public must learn to separate art from science.
- Nature is Already Amazing – Real species offer extraordinary adaptations that rival fiction.
Final Verdict: Real or Fake?
After reviewing the evidence, the conclusion is clear: Florus Fugitivus is fake.
- The name is fabricated.
- The video shows AI-generated sequences.
- No scientific record exists.
- The account that posted it has a history of AI insect-flower creations.
While entertaining, Florus Fugitivus is not a real insect at Red Rock Canyon or anywhere else.
Conclusion: The Real Wonders of Nature
The story of Florus Fugitivus reminds us of two things:
- The power of digital art to capture imaginations and spread across the world.
- The unmatched beauty of real biodiversity, from mantises disguised as orchids to beetles shimmering like jewels.
We don’t need fictional hybrids to marvel at nature. The real world already holds enough wonder.
The next time you see a beetle blossoming into a flower on your feed, remember: if it seems too magical to be true, it probably is.







