When it comes to computer processes and files, it’s not uncommon to come across unfamiliar names that may raise concerns. One such file is mdm.exe, which often leaves users wondering about its purpose and whether it should be removed. In this article, we will delve into the details of mdm.exe, explore its functions, and help you make an informed decision about its removal.

What is mdm.exe?
Mdm.exe stands for Machine Debug Manager, and it is a legitimate Windows process that is part of the Microsoft Visual Studio suite. Its primary function is to assist developers in debugging applications and scripts. The process runs in the background and provides debugging support for various programming languages, including Visual Basic, C++, and Java.
Machine Debug Manager is typically installed alongside Microsoft Visual Studio or other development tools. It is not a critical system process and is not required for the normal functioning of your computer. However, it is essential for developers who rely on debugging tools to identify and fix issues in their software.
Should I remove mdm.exe?
Whether you should remove mdm.exe depends on your specific needs and usage of your computer. Here are a few factors to consider:
1. Are you a developer?
If you are not a developer and do not use any debugging tools or programming languages, you can safely remove mdm.exe without any adverse effects on your system. Since it is not a critical process, removing it will not impact the performance or stability of your computer.
2. Do you experience any issues?
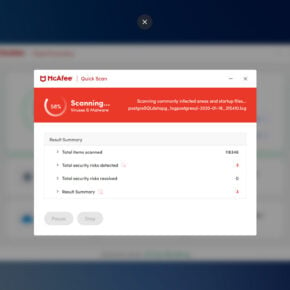
If you are experiencing any unusual behavior or performance issues on your computer, it is worth investigating whether mdm.exe is causing the problem. While mdm.exe itself is not known to be malicious, malware or viruses can sometimes disguise themselves as legitimate processes. Therefore, it is recommended to scan your system with a reliable antivirus or anti-malware software, such as Malwarebytes Free, to ensure your system is clean.
3. Disk and CPU usage
If you notice that mdm.exe is consuming a significant amount of disk space or CPU resources, it could indicate an issue. High resource usage by mdm.exe may be a sign of a problem with the debugging process or an underlying software issue. In such cases, it is advisable to seek assistance from a professional or consult relevant online forums for guidance.
How to remove mdm.exe?
If you have determined that mdm.exe is not necessary for your system or suspect it may be causing issues, you can remove it. Here are the steps to remove mdm.exe:
- Open the Control Panel on your Windows computer.
- Select “Programs” or “Programs and Features,” depending on your version of Windows.
- Locate and select “Microsoft Visual Studio” or any other development tool that includes mdm.exe.
- Click on the “Uninstall” or “Remove” button.
- Follow the on-screen instructions to complete the uninstallation process.
It is important to note that removing Microsoft Visual Studio or any other development tool will also remove other associated components and features. Therefore, make sure to consider the potential impact on your development environment before proceeding with the removal.
Conclusion
Mdm.exe, or Machine Debug Manager, is a legitimate Windows process that assists developers in debugging applications and scripts. If you are not a developer or do not use any debugging tools, you can safely remove mdm.exe without any adverse effects on your system. However, if you experience any issues or suspect malware, it is recommended to scan your system with reliable antivirus or anti-malware software, such as Malwarebytes Free. High resource usage or persistent issues may require further investigation or professional assistance. Always consider the potential impact on your development environment before removing mdm.exe or any associated development tools.