Online shopping can be convenient and fun, but it also comes with some risks. One of them is falling prey to scam shopping sites that lure customers with low prices, fake reviews, and attractive products. In this blog post, we will expose one of the most common email addresses used by these scam shopping sites: @Peachcher.com.
What are the @Peachcher.com scam shopping sites?
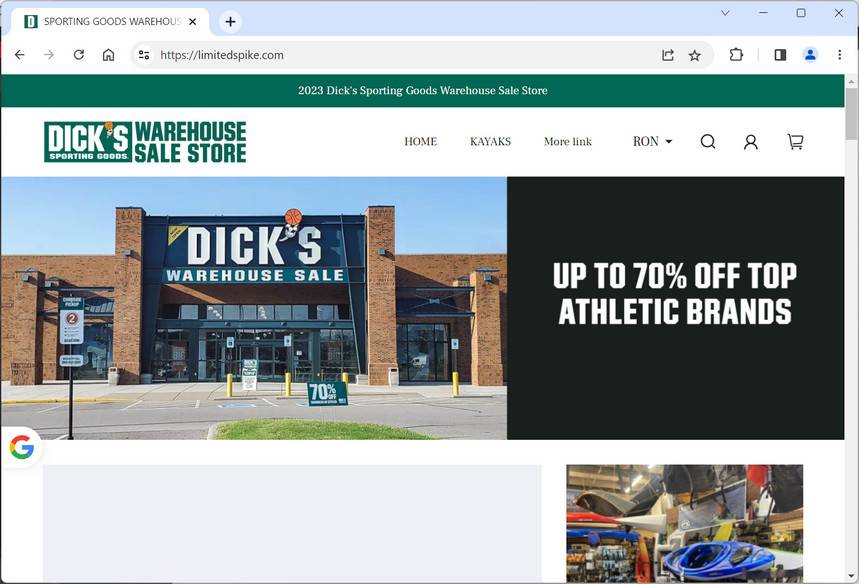
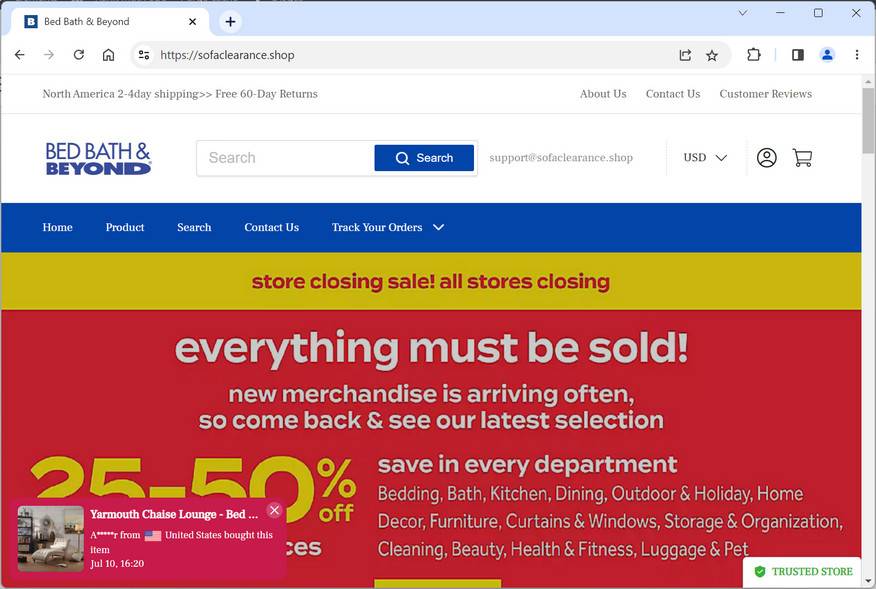
@Peachcher.com is a domain email address that appears on many websites that claim to sell various items, such as clothing, shoes, electronics, toys, and more. However, these websites are not legitimate online stores, but rather fraudulent schemes that aim to steal money and personal information from unsuspecting buyers.
These websites have several red flags that indicate they are not trustworthy, such as:
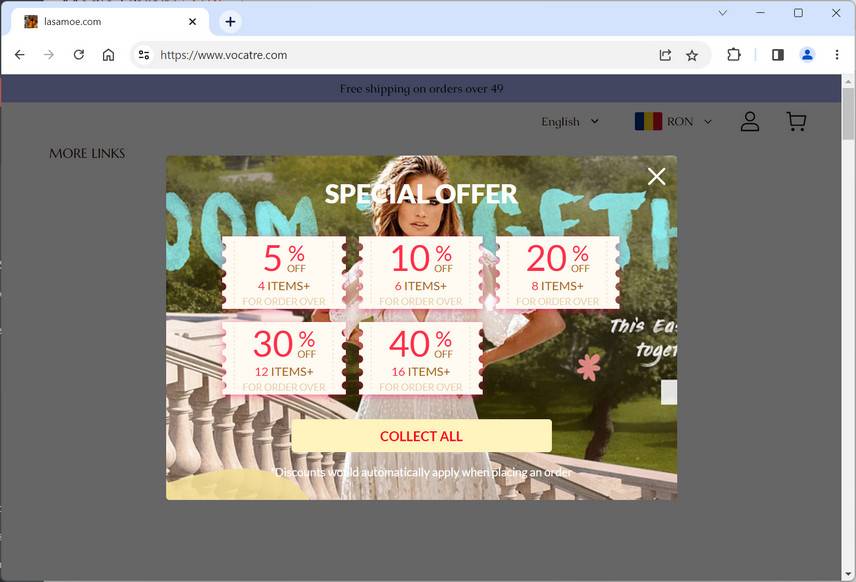
- Unrealistically low prices that are too good to be true.
- Poor grammar and spelling errors on the website content and product descriptions.
- Lack of information about the company, such as its address, phone number, or return policy.
- Fake or copied reviews from other websites or platforms.
- No secure payment methods or encryption on the checkout page.
- No customer service or response to inquiries or complaints.
How do the @Peachcher.com scam shopping sites operate?
The @Peachcher.com scam shopping sites operate by enticing customers with attractive products and discounts, and then asking them to pay with their credit card or other online payment methods. However, once the payment is made, the customer either receives nothing at all, or a low-quality or counterfeit product that does not match the description or image on the website.
In some cases, the customer may also receive an email from @Peachcher.com asking for more personal information, such as their address, phone number, or bank account details. This is a phishing attempt that tries to obtain more sensitive data that can be used for identity theft or fraud.
The @Peachcher.com scam shopping sites also use fake tracking numbers or shipping confirmation emails to make customers believe that their order is on its way. However, these tracking numbers are either invalid or belong to other unrelated shipments. The customer may also receive an email from @Peachcher.com asking for more money to cover customs fees or taxes. This is another scam tactic that tries to extort more money from the customer.
What to do if you have fallen victim?
If you have fallen victim to the @Peachcher.com scam shopping sites, you should take the following steps as soon as possible:
- Contact your bank or credit card company and report the fraudulent transaction. Ask them to cancel your card and issue a chargeback if possible.
- Change your passwords and security questions for your online accounts, especially those related to your email, payment methods, or social media platforms.
- Report the scam website to the authorities, such as the Federal Trade Commission (FTC), the Better Business Bureau (BBB), or your local consumer protection agency.
- Warn your friends and family about the scam website and advise them not to buy anything from it.
- Leave a negative review or comment on the scam website or any other platform where it is advertised.
Conclusion
@Peachcher.com is an email address that is used by many scam shopping sites that try to deceive customers with fake products and low prices. These scam shopping sites are not reliable or safe, and they should be avoided at all costs. If you have encountered any of these scam shopping sites, you should report them and take measures to protect yourself from further harm.