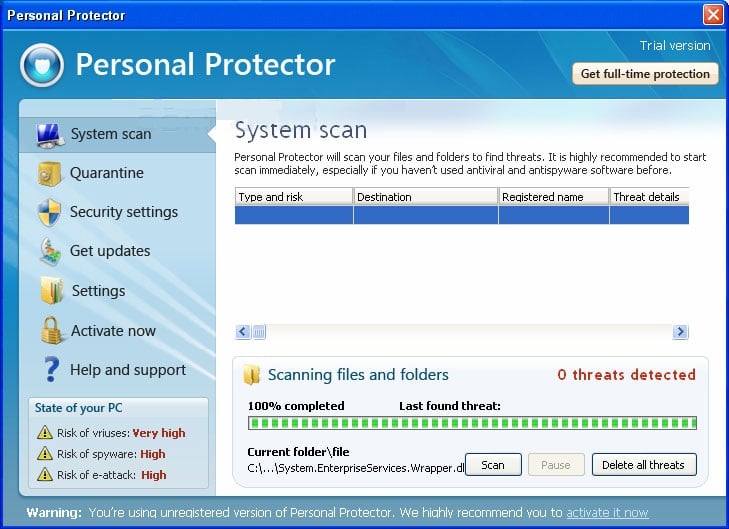
Personal Protector 2013 is a computer virus,which pretends to be a legitimate security program and after performing a quick scan, will report that trojans,worms and other malware were detected on your machine. If you try to remove these infections, Personal Protector 2013 will state that you need to purchase the full version before being able to remove these threats.
In reality, none of the reported issues are real, and are only used to scare you into buying Personal Protector 2013 and stealing your personal financial information.
As part of its self-defense mechanism,Personal Protector 2013 has disabled the Windows system utilities, including the Windows Task Manager and Registry Editor,and will block you from running certain programs that could lead to its removal.
Further more,this rogue antivirus has modified your Windows files associations and now,whenever you are trying to any programs that have a .exe extension ,Personal Protector 2013 it will display a bogus notification in which will report that the file is infected,in an attempt to scare you.

If your computer is infected with Personal Protector 2013,then you are seeing this screens:


Personal Protector 2013 is a scam and you should ignore any alerts that this malicious software might generate.
Under no circumstance should you buy this rogue security software as this could lead to identity theft,and if you have, you should contact your bank and dispute the charge stating that the program is a scam and a computer virus.
Personal Protector 2013 – Virus Removal Instructions
STEP 1: Repair your Windows Registry from Personal Protector 2013 malicious changes.
Personal Protector 2013 has changed your Windows registry settings so that when you try to run a executable file, it will instead launch the infection rather than the desired program.
- Download the registryfix.reg file to fix the malicious registry changes from Personal Protector 2013.
REGISTRYFIX.REG DOWNLOAD LINK (This link will automatically download the registry fix called registryfix.reg) - Double-click on registryfix.reg file to run it. Click “Yes” for Registry Editor prompt window,then click OK.
![Remove Personal Protector 2013 (Removal Instructions) 2 [Image: fix registry]](//malwaretips.com/blogs/wp-content/uploads/2011/12/registry.png)
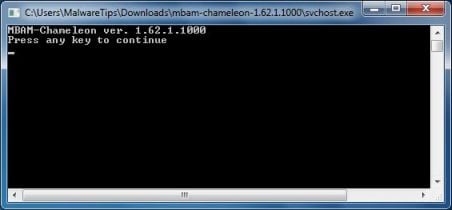
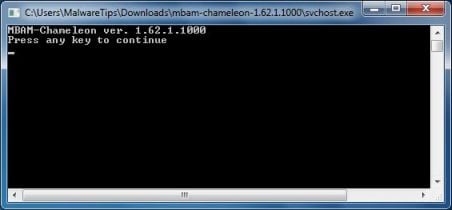
STEP 2: Remove Personal Protector 2013 malicious files with Malwarebytes Chameleon
Malwarebytes Chameleon is a powerful utility from Malwarebytes, that will stop Personal Protector 2013 malicious process from running and remove its malicious files from your computer.
- Download Malwarebytes Chameleon from the below link and extract it to a folder in a convenient location.
MALWAREBYTES CHAMELEON DOWNLOAD LINK (This link will open a new web page from where you can download Malwarebytes Chameleon) - Make certain that your infected computer is connected to the internet and then open the Malwarebytes Chameleon folder and double-click on svchost.exe.

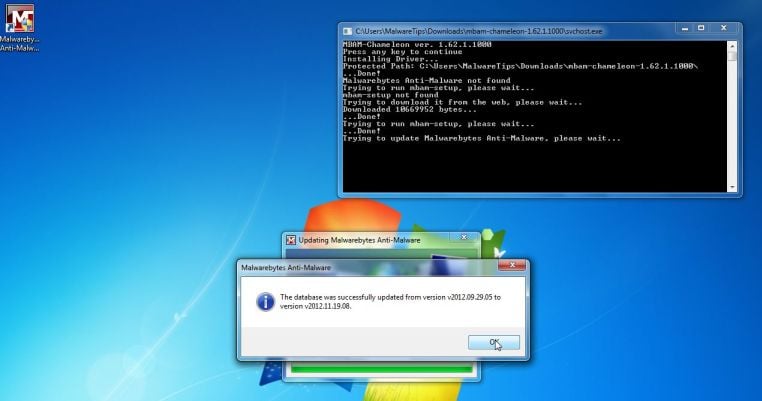
IF the Chameleon help file itself will not open, then double-click each file one by one until you find one that works, which will be indicated by a black DOS/command prompt window. - Follow the onscreen instructions to press a key to continue and Chameleon will proceed to download and install Malwarebytes Anti-Malware for you.
- Once it has done this, it will update Malwarebytes Anti-Malware, and you’ll need to click OK when it says that the database was successfully updated.
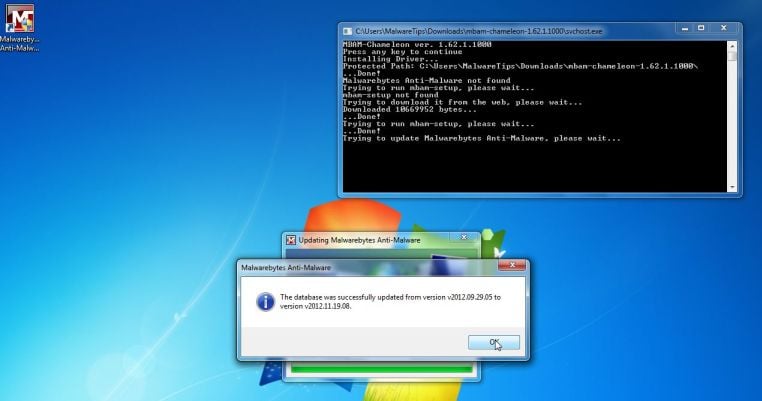
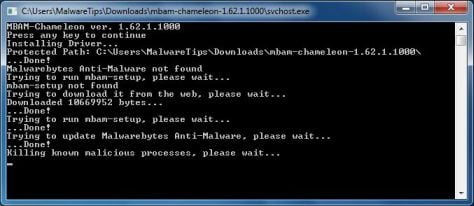
- Malwarebytes Anti-Malware will now attempt to kill all the malicious process associated with Personal Protector 2013.Please be aware that this process can take up to 10 minutes, so please be patient.
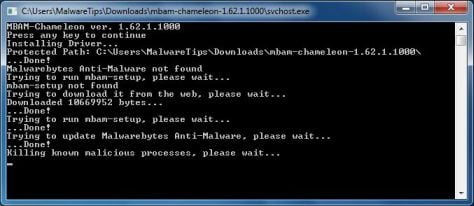
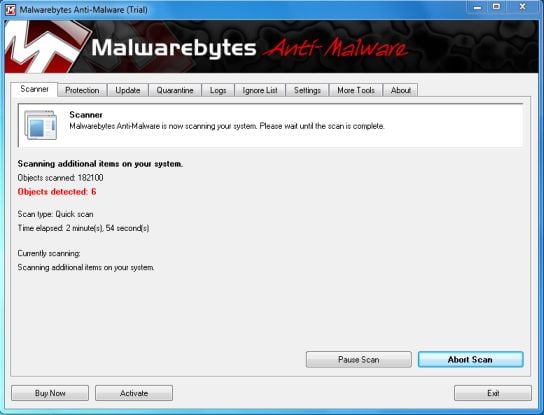
- Next, Malwarebytes Anti-Malware will automatically open and perform a Quick scan for Personal Protector 2013 malicious files as shown below.
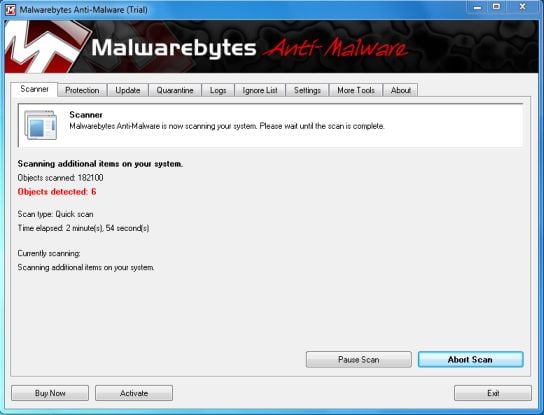
- Upon completion of the scan, click on Show Result
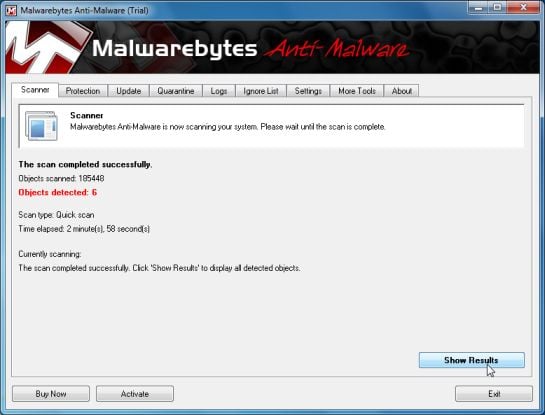
- You will now be presented with a screen showing you the malware infections that Malwarebytes Anti-Malware has detected.
Make sure that everything is Checked (ticked),then click on the Remove Selected button.
- After your computer restarts, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats
STEP 3: Remove Personal Protector 2013 rootkit with HitmanPro
In some cases,Personal Protector 2013 will also install a rootkit on victims computer.To remove this rootkit we will use HitmanPro.
- You can download the latest official version of HitmanPro from the below link.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro) - Double click on the previously downloaded fileto start the HitmanPro installation.
![HitmanPro Installer [Image: HitmanPro Icon]](//malwaretips.com/images/removalguide/hpro1.png)
IF you are experiencing problems while trying to start HitmanPro, you can use the Force Breach mode.To start HitmanPro in Force Breach mode, hold down the left CTRL-key when you start HitmanPro and all non-essential processes are terminated, including the malware process. (How to start HitmanPro in Force Breach mode – Video) - Click on Next to install HitmanPro on your system.
![HitmanPro installation process [Image: Starting HitmanPro]](//malwaretips.com/images/removalguide/hitmanpro36-start.png)
- The setup screen is displayed, from which you can decide whether you wish to install HitmanPro on your machine or just perform a one-time scan, select a option then click on Next to start a system scan.
![HitmanPro setup options [Image: HitmanPro installation screen]](//malwaretips.com/images/removalguide/hitmanpro36-installation.png)
- HitmanPro will start scanning your system for malicious files as seen in the image below.
![HitmanPro while scanning for Personal Protector 2013 virus [Image: HitmanPron scanning for Personal Protector 2013]](//malwaretips.com/images/removalguide/hitmanpro36-scan.png)
- Once the scan is complete,you’ll see a screen which will display all the malicious files that the program has found.Click on Next to remove this malicious files.
![HitmanPro displaying scan results [Image: HitmanPro scan results]](//malwaretips.com/images/removalguide/hitmanpro36-results.png)
- Click Activate free license to start the free 30 days trial and remove the malicious files.
![Activate the HitmanPro free 30 days trial to remove any detected infections [Image: Activate HitmanPro license]](//malwaretips.com/images/removalguide/hitmanpro36-activation.png)
- HitmanPro will now start removing the infected objects.If this program will ask you to restart your computer,please allow this request.
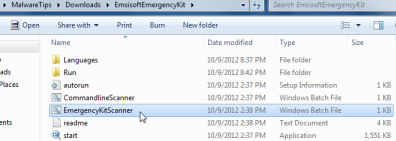
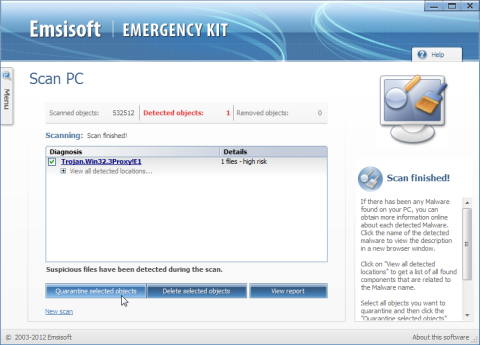
STEP 4: Double check for any left over infections with Emsisoft Emergency Kit
- You can download the latest official version of Emsisoft Emergency Kit from the below link.
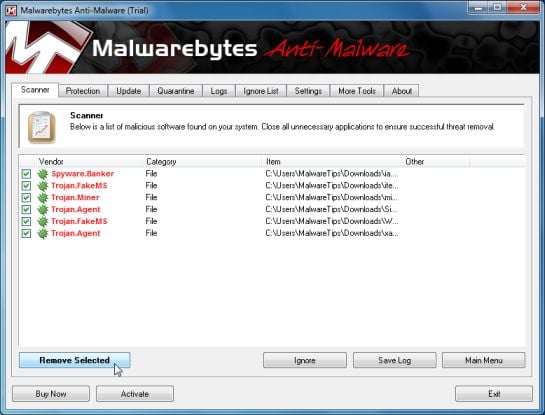
EMSISOFT EMERGENCY KIT DOWNLOAD LINK ((This link will open a new web page from where you can download Emsisoft Emergency Kit) - After the download process will finish , you’ll need to unpack EmsisoftEmergencyKit.zip
- Open the Emsisoft Emergency Kit folder and double click EmergencyKitScanner.bat.
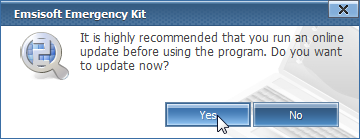
- A pop-up will prompt you to update Emsisoft Emergency Kit,and you’ll need to click the Yes button to allow this request.
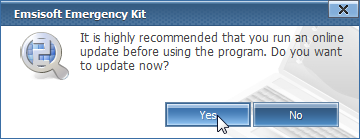
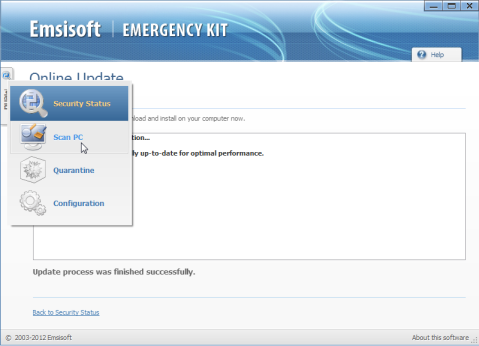
- After the Update process has completed,click on the Menu tab and then select Scan PC.
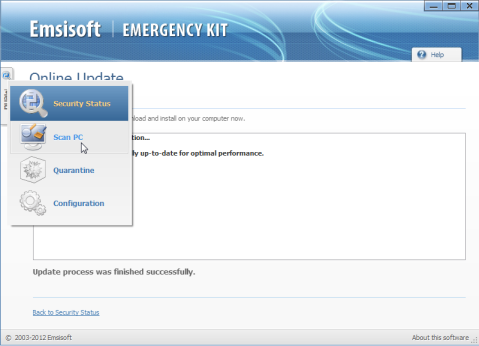
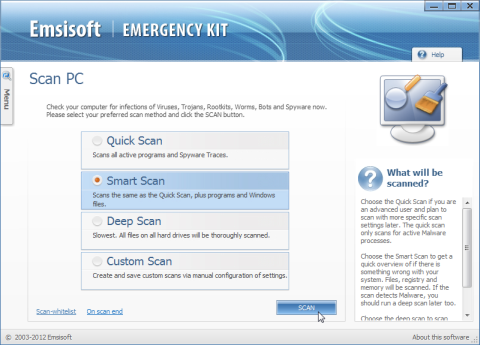
- Select Smart scan and click on the SCAN button to search for Personal Protector 2013 malicious files.
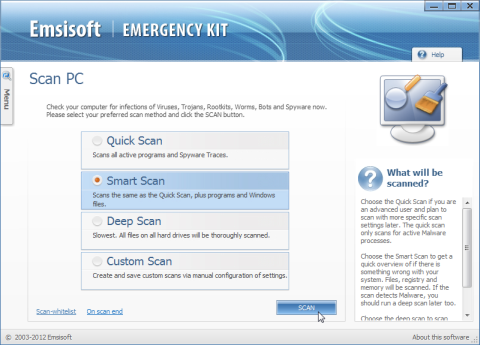
- Emsisoft will now start scanning your computer for malicious files.When the scan will be completed,you will be presented with a screen showing you the infections that Emsisoft has detected.
Make sure that everything is Checked (ticked) and then click on Quarantine selected objects.
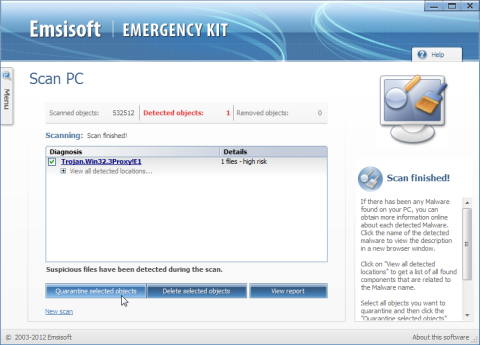
- Emsisoft Emergency Kit will now start removing the malicious files.If during the removal process Emsisoft will display a message stating that it needs to reboot, please allow this request.

![Remove Personal Protector 2013 (Removal Instructions) 2 [Image: fix registry]](http://malwaretips.com/blogs/wp-content/uploads/2011/12/registry.png)

![HitmanPro Installer [Image: HitmanPro Icon]](http://malwaretips.com/images/removalguide/hpro1.png)
![HitmanPro installation process [Image: Starting HitmanPro]](http://malwaretips.com/images/removalguide/hitmanpro36-start.png)
![HitmanPro setup options [Image: HitmanPro installation screen]](http://malwaretips.com/images/removalguide/hitmanpro36-installation.png)
![HitmanPro while scanning for Personal Protector 2013 virus [Image: HitmanPron scanning for Personal Protector 2013]](http://malwaretips.com/images/removalguide/hitmanpro36-scan.png)
![HitmanPro displaying scan results [Image: HitmanPro scan results]](http://malwaretips.com/images/removalguide/hitmanpro36-results.png)
![Activate the HitmanPro free 30 days trial to remove any detected infections [Image: Activate HitmanPro license]](http://malwaretips.com/images/removalguide/hitmanpro36-activation.png)
![Remove Corphthele.com Pop-up Ads [Virus Removal Guide] 4 McAfee scam 4](https://malwaretips.com/blogs/wp-content/uploads/2023/08/McAfee-scam-4-290x290.jpg)
