If your computer is infected with a Police Ukash Virus, your machine will be blocked by a bogus notification, that pretends to be from a local law enforcement agency and states that your computer has been blocked due to it being involved with the distribution of pornographic material, SPAM and copyrighted content.
The Police Ukash Ransom virus will lock you out of your computer and applications, so whenever you’ll try to log on into your Windows operating system, it will display instead a lock screen asking you to pay 100 Euro in the form of a Ukash or PaySafeCard code.
Furthermore, to make its alert seem more authentic, this virus also has the ability to access your installed webcam ,so that the bogus Police virus notification shows what is happening in the room.
Below you can see some types of lock screens which the Police Ukash Virus will generate, please note that are just examples and cyber criminals are always updating the graphics so it might not match with your bogus notification however it’s good to know that your local law enforcement agency will NEVER lock down your computer so if you see one, then you are infected with this virus.




Police Ukash Virus – Removal Instructions
HitmanPro has recently updated their program and now we can easily fight ransomware using Kickstart to bypass this infection and access a computer to scan for malware.
STEP 1: Create a HitmanPro.Kickstart USB flash drive
- While you are using a “clean” (non-infected) computer, download HitmanPro from the below link.
HITMANPRO DOWNLOAD LINK (This link will open a download page in a new window from where you can download HitmanPro) - Insert your USB flash drive into your computer and then follow the instructions from the below video:
STEP 2: Remove Police Ukash virus with HitmanPro.Kickstart
- After you have create the HitmanPro.Kickstart USB flash drive, you can insert this USB drive into the infected machine and start your computer
- Once the computer starts repeatedly tap the F11 key (on some machines its F10 or F2),which should bring up the Boot Menu, from there you can select to boot from your USB.
Next,you’ll need to perform a system scan with HitmanPro as see in the below video:
STEP 3: Scan your computer for malware
Because there might be some left over malicious files on your system,we strongly recommend that you perform a system scan with the following on-demand scanners.
Run a computer scan with Malwarebytes Anti-Malware FREE
- You can download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - Start the Malwarebytes’ Anti-Malware installation process by double clicking on mbam-setupfile.
- When the installation begins, keep following the prompts in order to continue with the setup process. Do not make any changes to default settings and when the program has finished installing, make sure you leave both the Update Malwarebytes’ Anti-Malware and Launch Malwarebytes’ Anti-Malware checked. Then click on the Finish button. If Malwarebytes’ prompts you to reboot, please do not do so.
- Malwarebytes Anti-Malware will now start and you’ll be prompted to start a trial period , please select ‘Decline‘ as we just want to use the on-demand scanner.
- On the Scanner tab,select Perform full scan and then click on the Scanbutton to start scanning your computer.
- Malwarebytes’ Anti-Malware will now start scanning your computer for Police Ukash virus malicious files as shown below.
- When the scan is finished a message box will appear, click OK to continue.
- You will now be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected.Please note that the infections found may be different than what is shown in the image.Make sure that everything is Checked (ticked) and click on the Remove Selected button.
Run a computer scanwith Emsisoft Emergency Kit
- You can download Emsisoft Emergency Kit from the below link,then extract it to a folder in a convenient location.
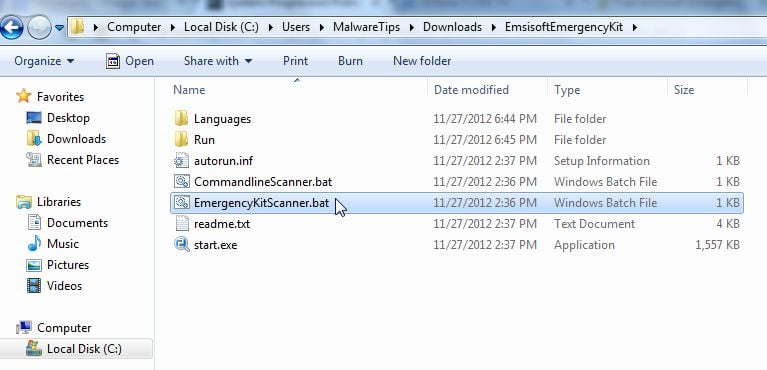
EMSISOFT EMERGENCY KIT DOWNLOAD LINK ((This link will open a new web page from where you can download Emsisoft Emergency Kit) - Open the Emsisoft Emergency Kit folder and double click EmergencyKitScanner.bat, then allow this program to update itself.
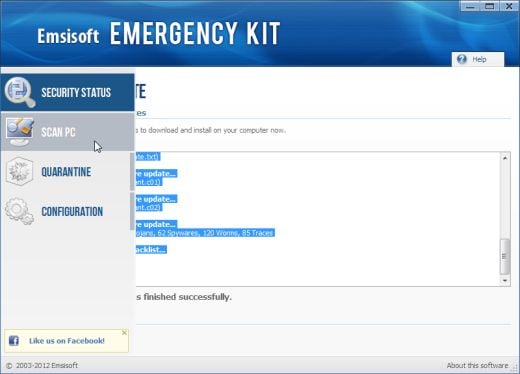
- After the Emsisoft Emergency Kit has update has completed,click on the Menu tab,then select Scan PC.
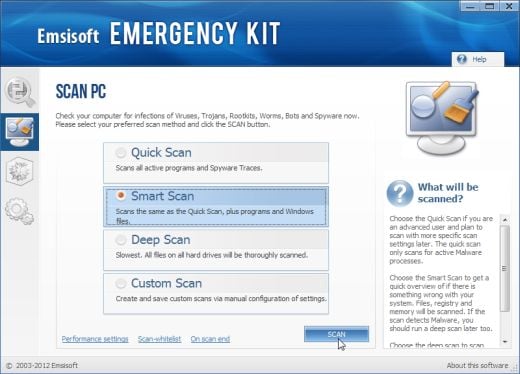
- Select Smart scan and click on the SCAN button to search for Police Ukash virus malicious files.
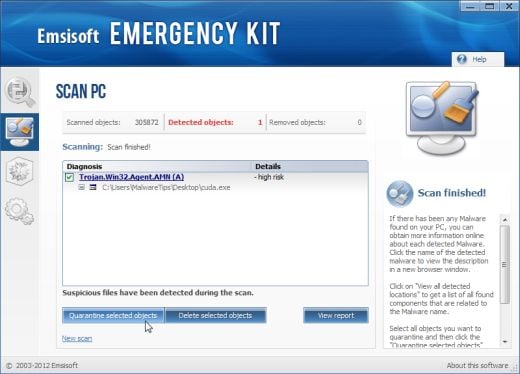
- When the scan will be completed,you will be presented with a screen reporting which malicious files has Emsisoft detected on your computer, and you’ll need to click on Quarantine selected objects to remove them.
![Malwarebytes Anti-Malware Installer [Image: Malwarebytes Installer]](http://malwaretips.com/images/removalguide/malwarebytes-setup.png)
![Malwarebytes last setup screen [Image: Finishing Malwarebytes installation]](http://malwaretips.com/images/removalguide/update-malwarebytes.png)
![Decline trial period in Malwarebytes Anti-Malware [Image: Decline Malwarebytes trial]](http://malwaretips.com/images/removalguide/malwarebytes-trial.png)
![Perform a Full System Scan with Malwarebytes Anti-Malware [Image: Starting a full system sca]](http://malwaretips.com/images/removalguide/start-scan-malwarebytes.png)
![Malwarebytes Anti-Malware scanning for [Image: Malwarebytes scanning for malicious files]](http://malwaretips.com/images/removalguide/scan-malwarebytes.png)
![Malwarebytes when the system scan has finished [Image: Malwarebytes scan results]](http://malwaretips.com/images/removalguide/results-malwarebytes.png)
![Removing the infections found by Malwarebytes [Image: Infections found by Malwarebytes]](http://malwaretips.com/images/removalguide/detection-malwarebytes.png)