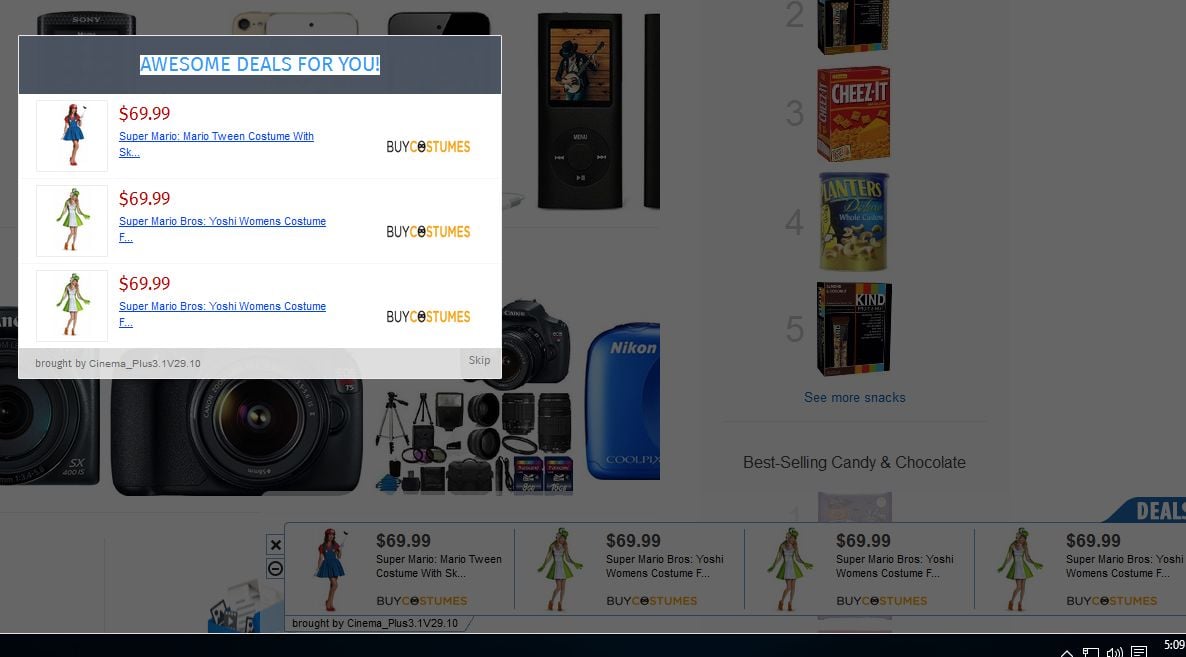
If you are seeing random pop-up ads, advertising banners or sponsored links within Internet Explorer, Firefox and Google Chrome, then your computer is infected with an adware or a potentially unwanted program.
The adware pop-ups happens regardless of the web browser or search engine, and if you are seeing ads from adware whenever you are doing a Google search or visiting a website, then your computer may be infected with adware or a potentially unwanted program.
This infection is designed specifically to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
In most cases the pop-up ads are caused by an ad-supported (users may see additional banner, search, pop-up, pop-under, interstitial and in-text link advertisements) cross web browser plugin for Internet Explorer, Firefox and Chrome, which is distributed through various monetization platforms during installation. This malicious browser extensions is typically added when you install another free software (video recording/streaming, download-managers or PDF creators) that had bundled into their installation this adware program.
Once installed, whenever you will open a new tab within Internet Explorer, Firefox and Google Chrome, a new tab with and ad from adware will pop-up.
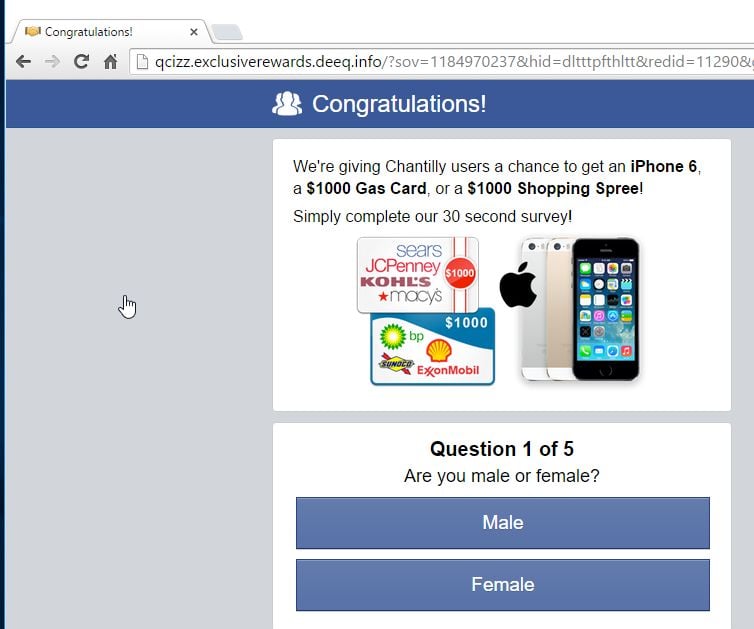
The malicious browser extension may also display a pop-up box stating that you need to updated or install a piece of software (eg: Java, Flash Player, Web browser). If you click on the “Download”, “Run Update” or “Click to install now” button, instead of installing an update, you’ll agree to download an adware or a malicious programs onto your computer.
The malicious link from a pop-up ad may install on your computer potentially unwanted programs like: toolbars (Sweet-Page Toolbar, Delta Toolbar), adware (WebCake, EnhanceTronic, CouponBuddy) or other forms of malware.
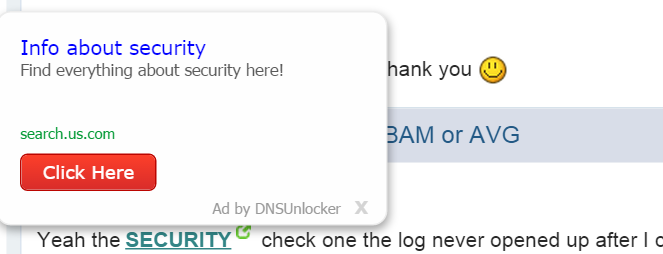
Adware infections will also display advertising banners on the webpages that you are visiting, and as you browse Internet, it will show coupons and other deals available on different websites.
You should always pay attention when installing software because often, a software installer includes optional installs, such as this adware pop-up ads. Be very careful what you agree to install.
Always opt for the custom installation and deselect anything that is not familiar, especially optional software that you never wanted to download and install in the first place. It goes without saying that you should not install software that you don’t trust.
How to remove pop-up ads and other malware from Google Chrome
This page is a comprehensive guide, which will remove “Google Chrome” virus from your computer and any other adware program that may have been installed during the setup process.
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
STEP 1: Remove unwanted ads from Google Chrome with Chrome Cleanup Tool
STEP 2: Remove adware from Google Chrome with AdwCleaner
STEP 3: Remove browser hijackers from Windows with Junkware Removal Tool
STEP 4: Remove pop-up ads from Google Chrome Malwarebytes Anti-Malware
STEP 5: Remove trojans and other malware from Google Chrome with HitmanPro
(Optional) STEP 6: Double-check for Google Chrome malware with Zemana AntiMalware
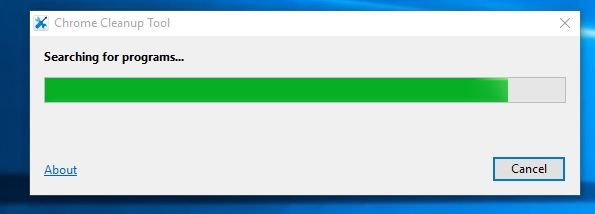
STEP 1: Remove unwanted ads from Google Chrome with Chrome Cleanup Tool
This application will scan and remove software that may cause problems with Chrome, such as crashes, unusual startup pages or toolbars, unexpected ads you can’t get rid of, or otherwise changing your browsing experience. It’s important to be remember that this program is not an antivirus application for your entire system, it only scans for programs interfering with your Google Chrome experience.
- You can download Chrome Cleanup Tool from the below link.
CHROME CLEANUP TOOL DOWNLOAD LINK (This link will open a new web page from where you can download “Chrome Cleanup Tool”) - When Chrome Cleanup Tool has finished downloading, start this program by double-clicking on the chrome_cleanup_tool icon as seen below.
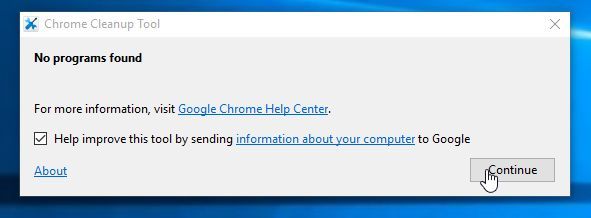
- Chrome Cleanup Tool will now scan Google Chrome for adware and browser hijackers. The scan should take less than 1 minute, and will report whether it found any malicious programs or not. If any malicious programs were detected, click on the “Remove suspicious programs” button and wait for the tool to tell you it has completed the process.
If Chrome Cleanup Tool has not detected anything suspicious, then you can click on the “Continue” button and move to the next step.
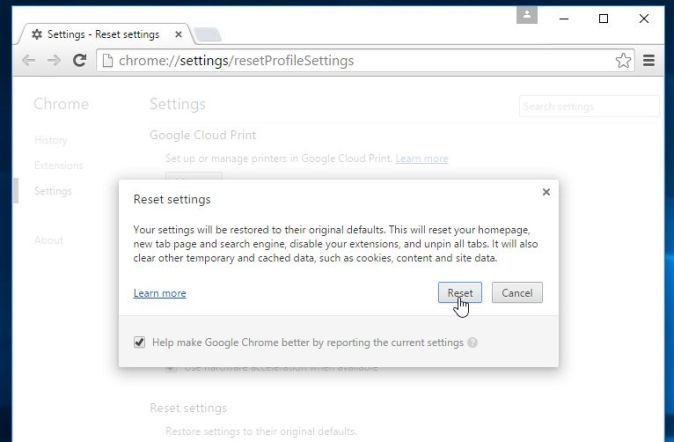
- Next, a new tab in Google Chrome will open, prompting you to reset Chrome to default settings. We recommend that you perform this reset as usually this will remove any browser hijackers that might affect your browser.
STEP 2: Remove adware from Google Chrome with AdwCleaner
The AdwCleaner utility will scan your computer and web browser for malicious files, browser extensions and registry keys, that may have been installed on your computer without your knowledge.
- You can download AdwCleaner from the below link.
ADWCLEANER DOWNLOAD LINK (This link will open a new web page from where you can download “AdwCleaner”) - Before starting AdwCleaner, close all open programs and internet browsers, then double-click on the AdwCleaner icon.
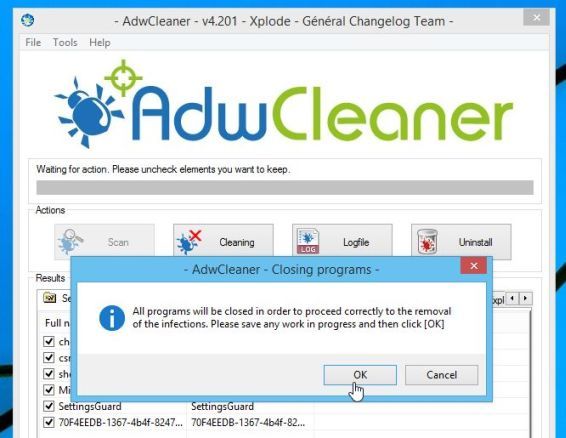
If Windows prompts you as to whether or not you wish to run AdwCleaner, please allow it to run. - When the AdwCleaner program will open, click on the “Scan” button as shown below.
AdwCleaner will now start to search for adware that may be installed on your computer. - To remove the adware that were detected in the previous step, please click on the “Clean” button.
- AdwCleaner will prompt you to save any open files or documents, as the program will need to reboot the computer. Please do so and then click on the OK button.
STEP 3: Remove browser hijackers from Windows with Junkware Removal Tool
Junkware Removal Tool is a powerful utility, which will remove browser extensions from Google Chrome, Firefox or Google Chrome, and also check your computer other malicious software.
- You can download the Junkware Removal Tool utility from the below link:
JUNKWARE REMOVAL TOOL DOWNLOAD LINK (This link will automatically download the Junkware Removal Tool utility on your computer) - Once Junkware Removal Tool has finished downloading, please double-click on the JRT.exe icon as seen below.
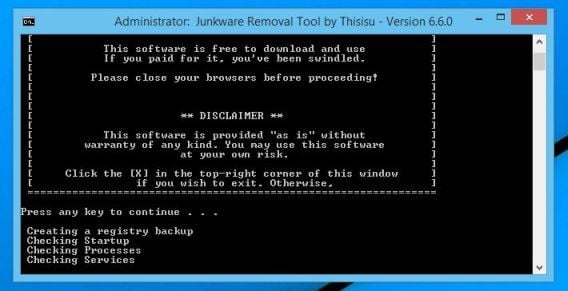
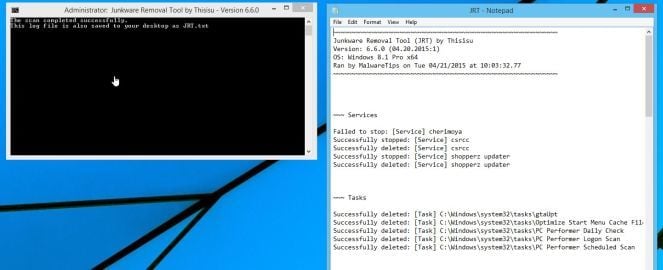
If Windows prompts you as to whether or not you wish to run Junkware Removal Tool, please allow it to run. - Junkware Removal Tool will now start, and at the Command Prompt, you’ll need to press any key to perform a scan for the browser hijackers.
Please be patient as this can take a while to complete (up to 10 minutes) depending on your system’s specifications. - When the scan Junkware Removal Tool will be completed, this utility will display a log with the malicious files and registry keys that were removed from your computer.
STEP 4: Remove pop-up ads from Google Chrome Malwarebytes Anti-Malware
Malwarebytes Anti-Malware uses industry-leading technology to detect and remove all traces of malware, including worms, Trojans, rootkits, rogues, dialers, spyware, and more.
It is important to note that Malwarebytes Anti-Malware works well and should run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
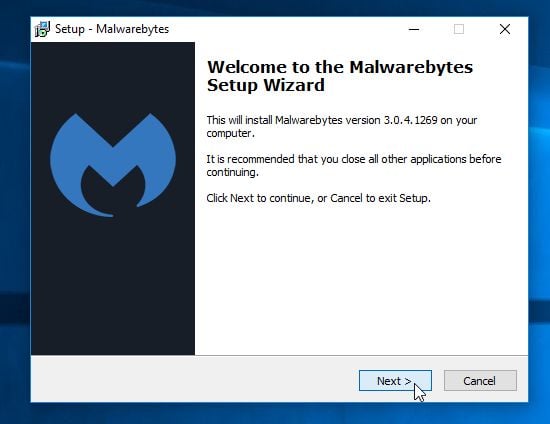
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download “Malwarebytes Anti-Malware Free”) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup” to start the installation of Malwarebytes Anti-Malware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
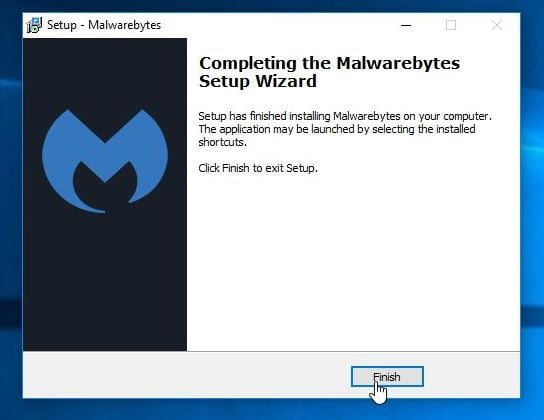
- When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
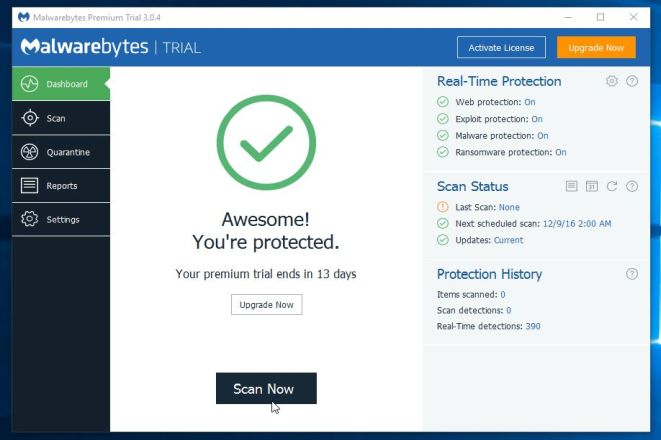
- Once installed, Malwarebytes Anti-Malware will automatically start and you will see a message stating that you should update the program, and that a scan has never been run on your system. To start a system scan you can click on the “Scan Now” button.
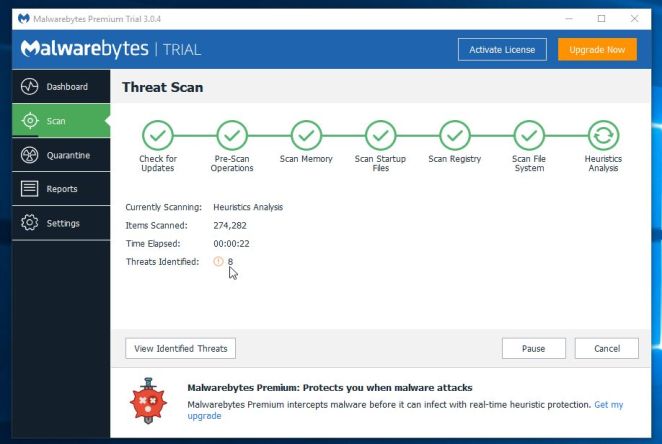
- Malwarebytes Anti-Malware will now start scanning your computer for the malicious programs. When Malwarebytes Anti-Malware is scanning it will look like the image below.
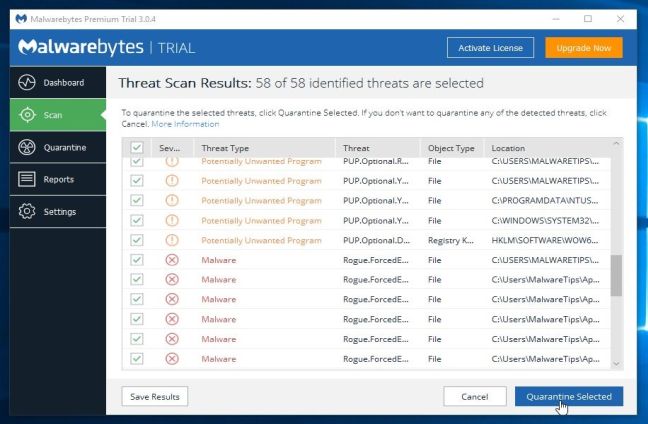
- When the scan has completed, you will now be presented with a screen showing you the malware infections that Malwarebytes Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Remove Seletected” button.
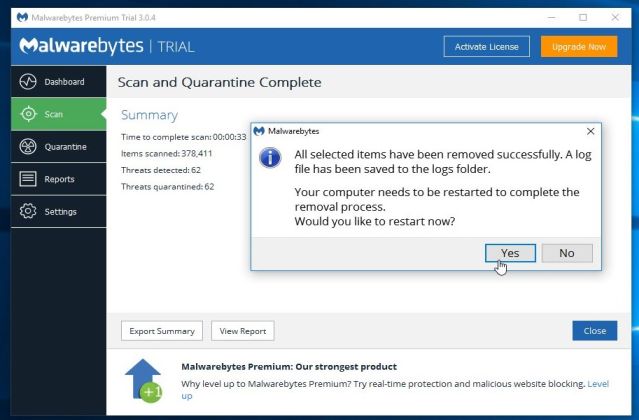
Please note that the infections found may be different than what is shown in the image. - Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
After your computer will restart, you should open Malwarebytes Anti-Malware and perform another “Threat Scan” scan to verify that there are no remaining threats
STEP 5: Remove trojans and other malware from Google Chrome with HitmanPro
HitmanPro is a second opinion scanner, designed to rescue your computer from malware (viruses, trojans, rootkits, etc.) that have infected your computer despite all the security measures you have taken (such as anti-virus software, firewalls, etc.). HitmanPro is designed to work alongside existing security programs without any conflicts. It scans the computer quickly (less than 5 minutes) and does not slow down the computer.
- You can download HitmanPro from the below link:
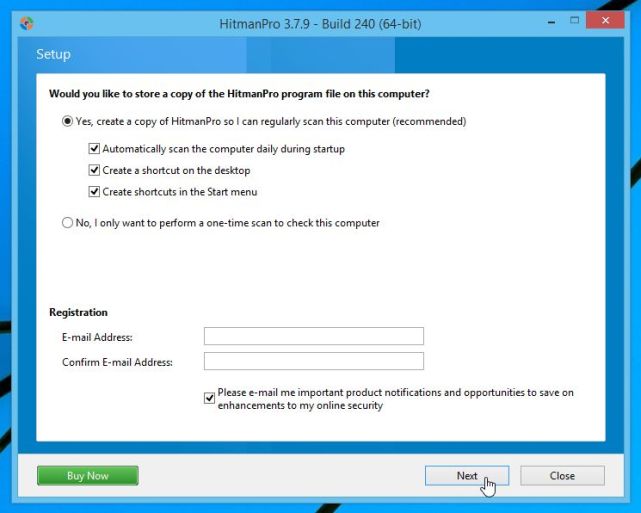
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.
Click on the “Next” button, to install HitmanPro on your computer.
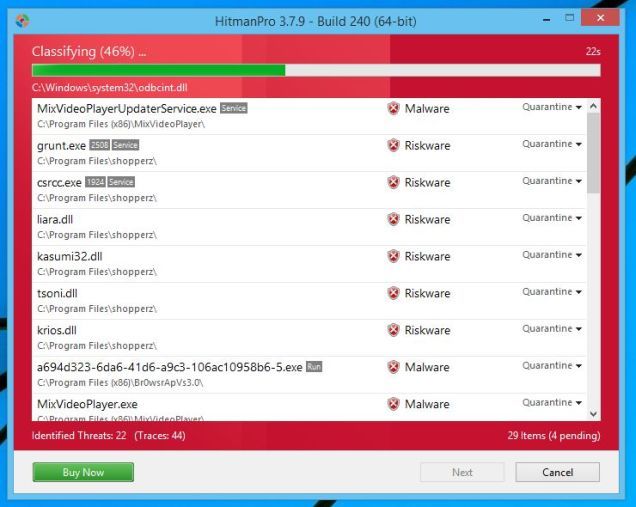
- HitmanPro will now begin to scan your computer for Google Chrome malicious files.
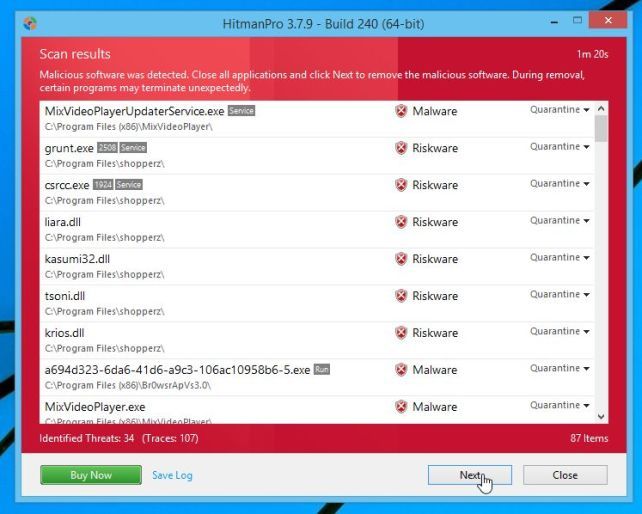
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove Google Chrome virus.
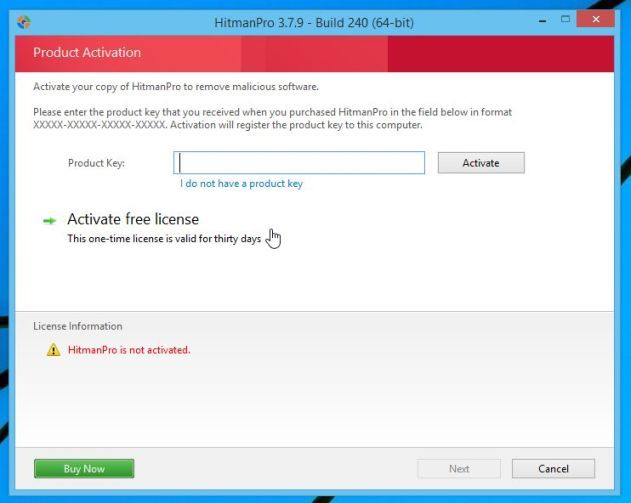
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
(Optional) STEP 6: Double-check for Google Chrome malware with Zemana AntiMalware
Zemana AntiMalware is a powerful utility, which will remove malicious browser extensions from Internet Explorer, Firefox or Google Chrome, and also check your computer other malicious software.
- You can download Zemana AntiMalware from the below link:
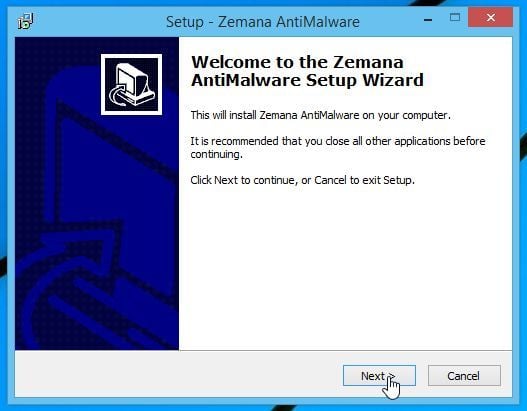
ZEMANA ANTIMALWARE DOWNLOAD LINK (This link will open a new web page from where you can download “Zemana AntiMalware”) - Double-click on the file named “Zemana.AntiMalware.Setup.exe” to install Zemana AntiMalware on your computer. When the program starts you will be presented with the start screen as seen below.
Click on the “Next” button, to install Zemana AntiMalware on your computer.
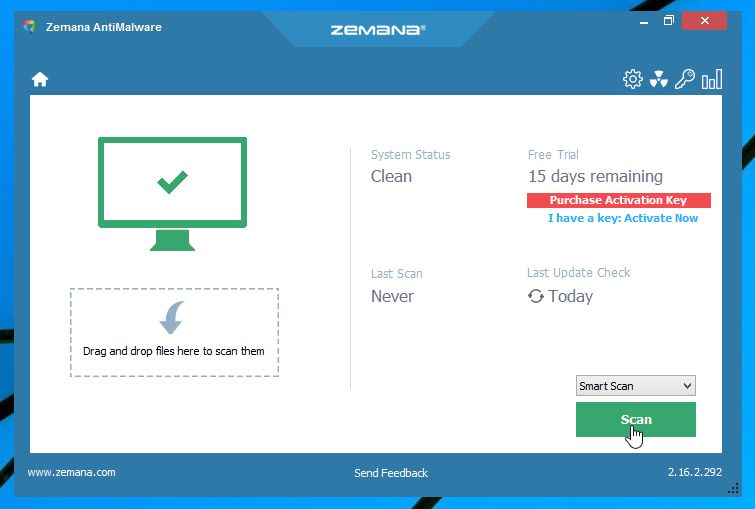
- When Zemana AntiMalware will start, click on the “Scan” button.
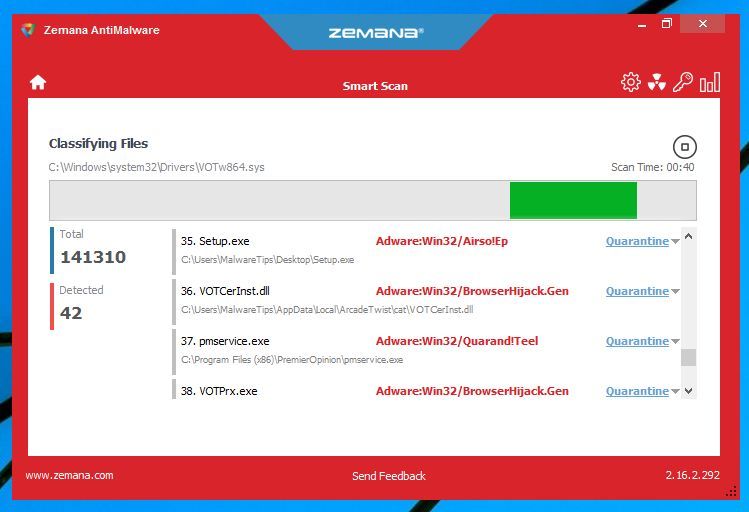
- Zemana AntiMalware will now scan computer for any malicious files. This process can take up to 10 minutes.
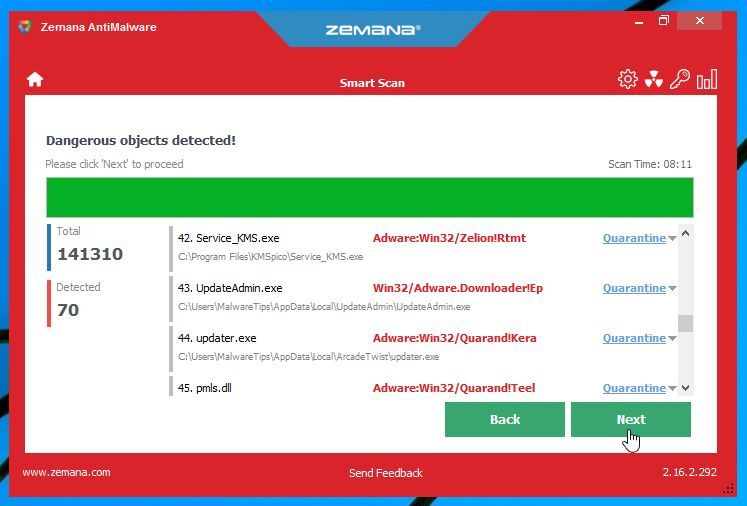
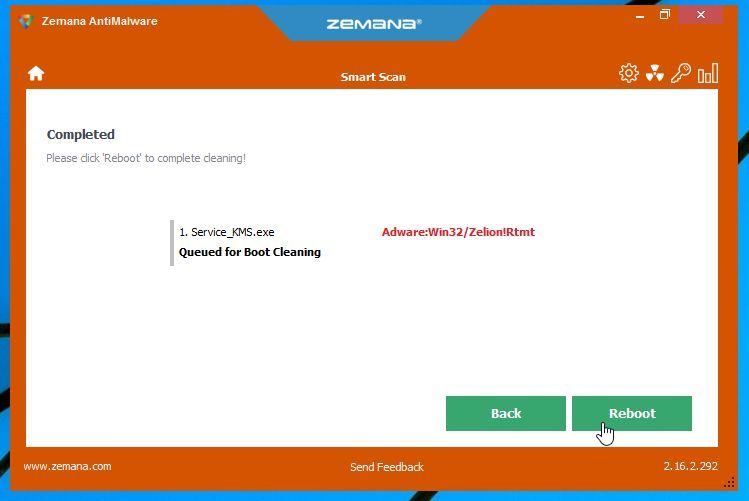
- When Zemana AntiMalware has finished it will display a list of all the malware that the program found. Click on the “Next” button, to remove the malicious files from your computer.
- Zemana AntiMalware will now remove all the detected malicious files, and at the end a system reboot may be required to remove all traces of malware.
If you are still experiencing problems while trying to remove pop-up ads, adware, browser hijackers or other malware from Google Chrome, please do one of the following:
- Run a system scan with Emsisoft Emergency Kit.
- Start a new thread in our Malware Removal Assistance forum.