JS:Miner-E[Trj] is a Trojan Horse that uses the infected computer’s resources to mine digital currency (Monero, Bitcoin, DarkCoin or Ethereum) without user permission.
JS:Miner-E[Trj] will use more than 70% of your CPU’s power and graphics cards power. What this means, is that when the miners are running you will find that your computer is running slower and games are stuttering or freezing because the JS:Miner-E[Trj] is using your computer’s resources to generate revenue for themselves. This will cause your CPU to run at very hot temperatures for extended periods of time, which could shorten the life of the CPU.
When a PC is infected with JS:Miner-E[Trj] malware, common symptoms include:
- Very high CPU and graphics cards usage
- Windows minimize and maximize slowly, and programs run slower.
- Programs don’t launch as quickly.
- General slowness when using the PC.
How to remove JS:Miner-E[Trj] Adware (Virus Removal Guide)
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
- STEP 1: Use Malwarebytes to remove JS:Miner-E[Trj] Virus
- STEP 2: Use HitmanPro to Scan for Malware and Unwanted Programs
- STEP 3: Double-check for malicious programs with Emsisoft Emergency Kit
- STEP 4: Reset your browser to default settings
STEP 1: Use Malwarebytes to remove JS:Miner-E[Trj] Virus
Malwarebytes is a powerful on-demand scanner which should remove the JS:Miner-E[Trj] adware from Windows. It is important to note that Malwarebytes will run alongside antivirus software without conflicts.
- You can download download Malwarebytes from the below link.
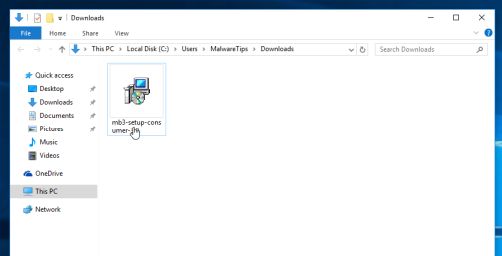
MALWAREBYTES DOWNLOAD LINK (This link open a new page from where you can download “Malwarebytes”) - When Malwarebytes has finished downloading, double-click on the “mb3-setup-consumer” file to install Malwarebytes on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
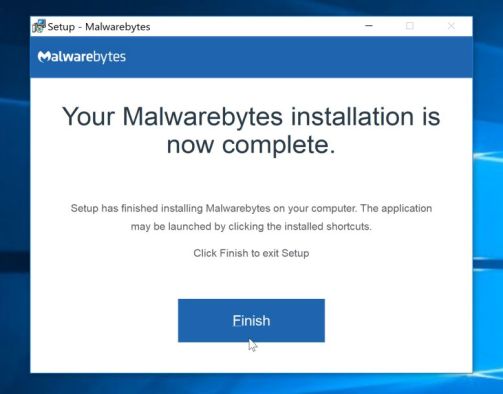
- When the Malwarebytes installation begins, you will see the Malwarebytes Setup Wizard which will guide you through the installation process.
To install Malwarebytes on your machine, keep following the prompts by clicking the “Next” button.
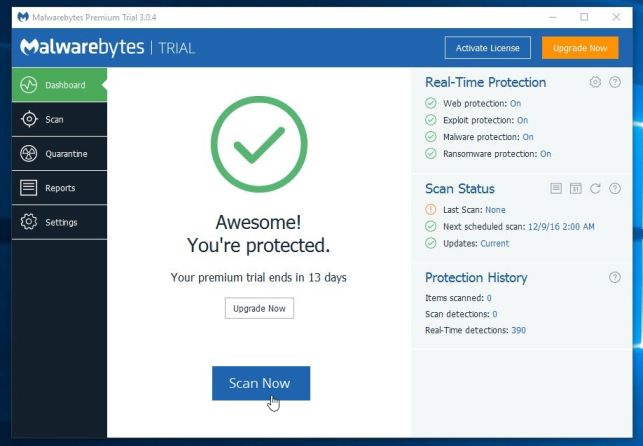
- Once installed, Malwarebytes will automatically start and update the antivirus database. To start a system scan you can click on the “Scan Now” button.
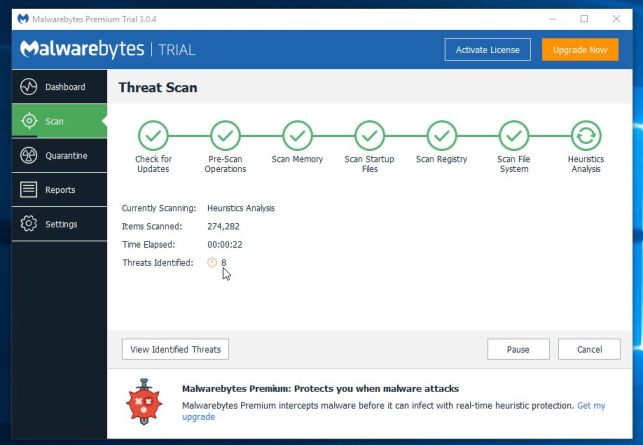
- Malwarebytes will now start scanning your computer for malicious programs.
This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
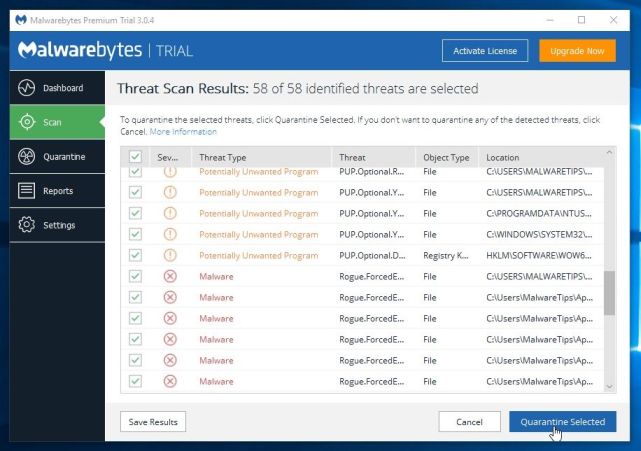
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected.
To remove the malicious programs that Malwarebytes has found, click on the “Quarantine Selected” button.
- Malwarebytes will now quarantine all the malicious files and registry keys that it has found.
To complete the malware removal process, Malwarebytes may ask you to restart your computer.
When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
STEP 2: Use HitmanPro to Scan for Malware and Unwanted Programs
HitmanPro can find and remove malware, adware, bots, and other threats that even the best antivirus suite can oftentimes miss. HitmanPro is designed to run alongside your antivirus suite, firewall, and other security tools.
- You can download HitmanPro from the below link:
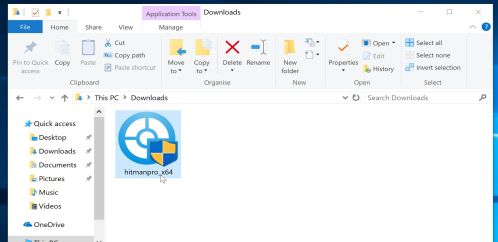
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - When HitmanPro has finished downloading, double-click on the “hitmanpro” file to install this program on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- When the program starts you will be presented with the start screen as shown below. Now click on the Next button to continue with the scan process.
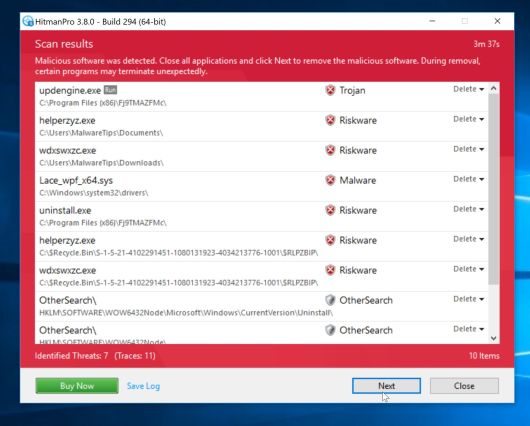
- HitmanPro will now begin to scan your computer for malware.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
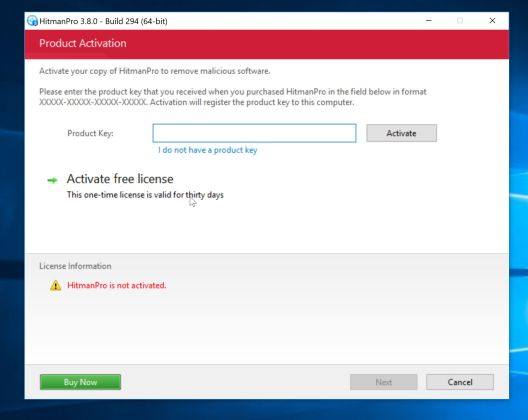
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
When the process is complete, you can close HitmanPro and continue with the rest of the instructions.
STEP 3: Double-check for malicious programs with Emsisoft Emergency Kit
The Emsisoft Emergency Kit Scanner includes the powerful Emsisoft Scanner complete with graphical user interface. Scan the infected PC for Viruses, Trojans, Spyware, Adware, Worms, Dialers, Keyloggers and other malicious programs.
- You can download Emsisoft Emergency Kit from the below link.
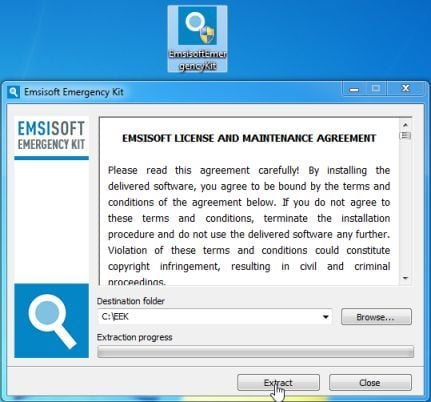
EMSISOFT EMERGENCY KIT DOWNLOAD LINK (This link will open a new web page from where you can download Emsisoft Emergency Kit) - Double-click on the “EmsisoftEmergencyKit” icon, then click on the “Extract” button.
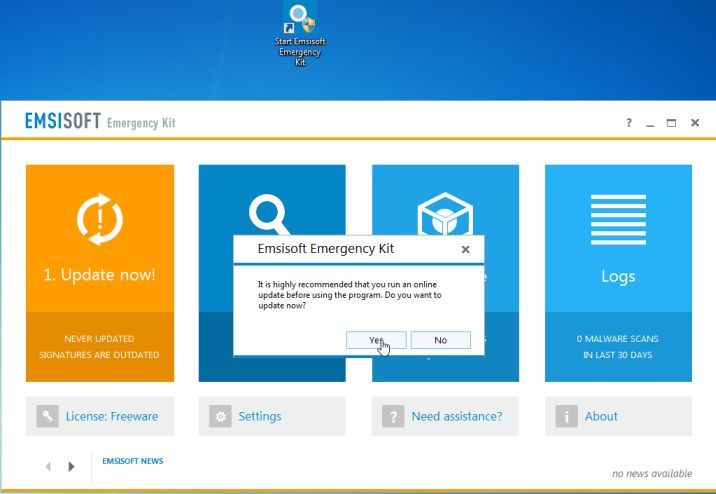
- On your desktop you should now have a “Start Extract Emsisoft Emergency Kit” icon, double-click on it, then when the program will start allow it to update its database.
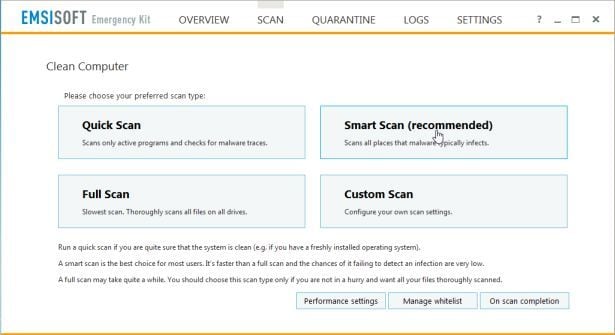
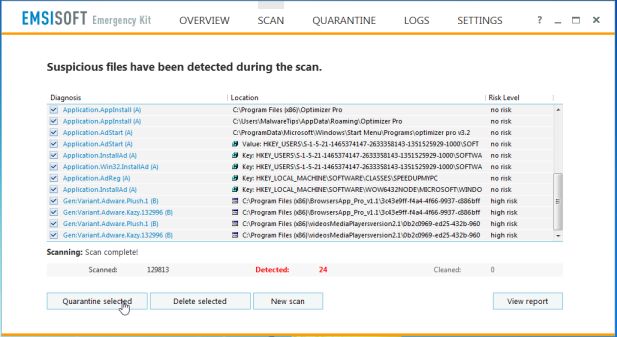
- Once the Emsisoft Emergency Kit has update has completed,click on the “Scan” tab, and perform a “Smart Scan“.
- When the scan will be completed,you will be presented with a screen reporting which malicious files has Emsisoft detected on your computer, and you’ll need to click on Quarantine selected objects to remove them.
STEP 4: Reset your browser to default settings
This step should be performed only if your issues have not been solved by the previous steps.
Google Chrome
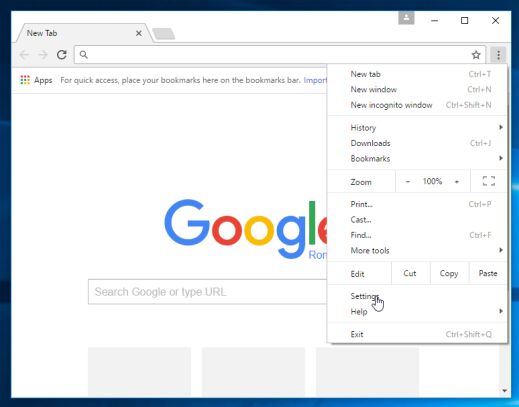
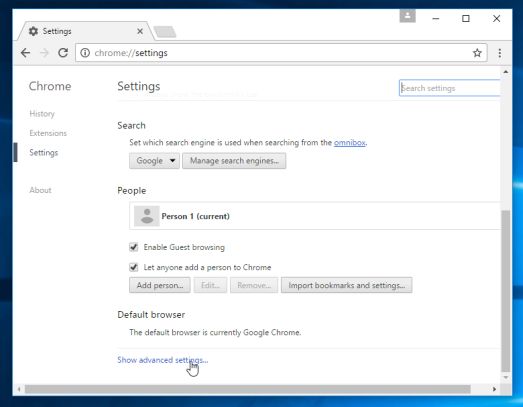
- On your computer, open Google Chrome.
- At the top right, click “More” (represented by the three dots) and then “Settings”
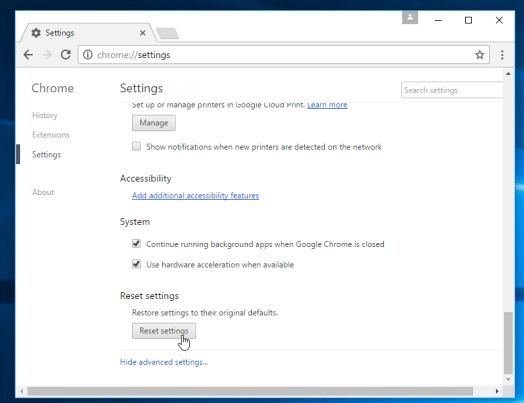
- At the bottom, click “Show advanced settings”.
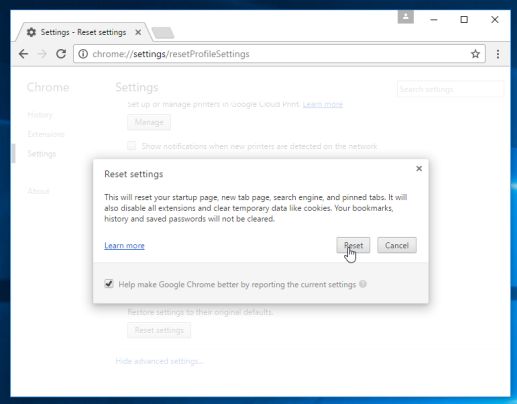
- Under the section “Reset settings”, click Reset settings.
- In the box that appears, click Reset.
Internet Explorer
- Open Internet Explorer, click on the “gear icon” in the upper right part of your browser, then click again on Internet Options.
- In the “Internet Options” dialog box, click on the “Advanced” tab, then click on the “Reset” button.
- In the “Reset Internet Explorer settings” section, select the “Delete personal settings” check box, then click on “Reset” button.
- When Internet Explorer has completed its task, click on the “Close” button in the confirmation dialogue box. You will now need to close your browser, and then you can open Internet Explorer again.
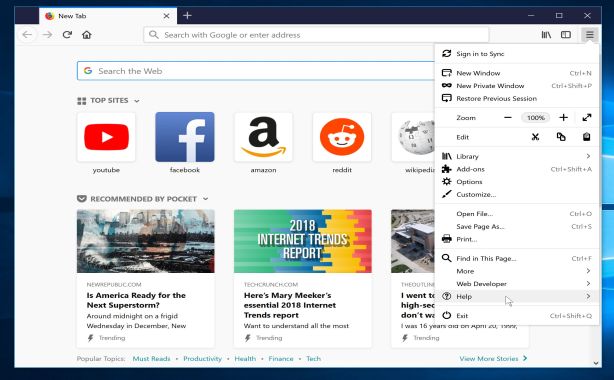
Mozilla Firefox
- In the upper-right corner of the Firefox window, click the Firefox menu button, then click on the “Help”
button.
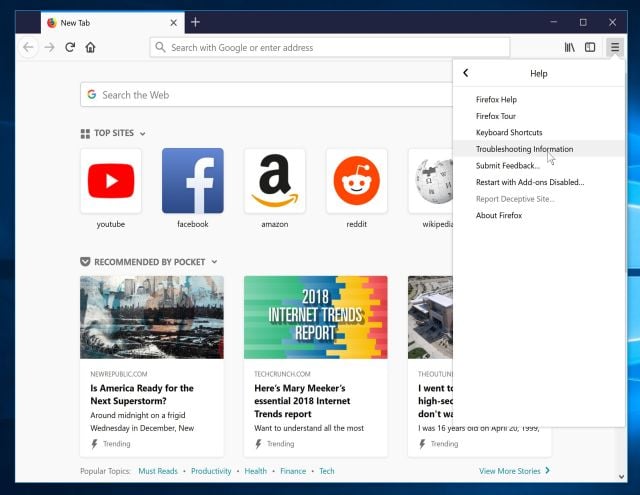
- From the Help menu, choose Troubleshooting Information.
If you’re unable to access the Help menu, type about:support in your address bar to bring up the Troubleshooting information page.
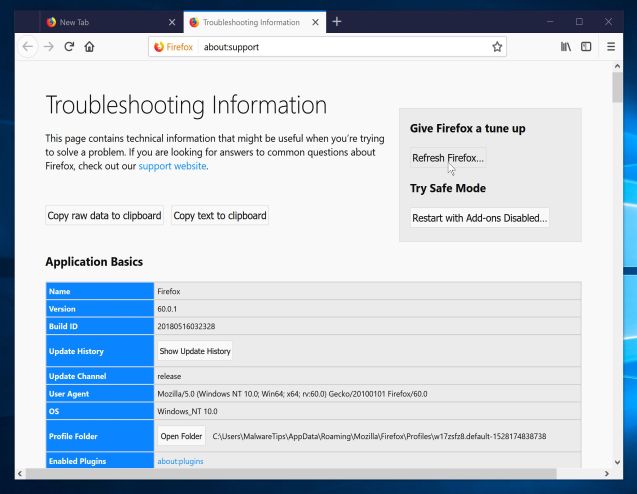
- Click the “Refresh Firefox” button in the upper-right corner of the “Troubleshooting Information” page.
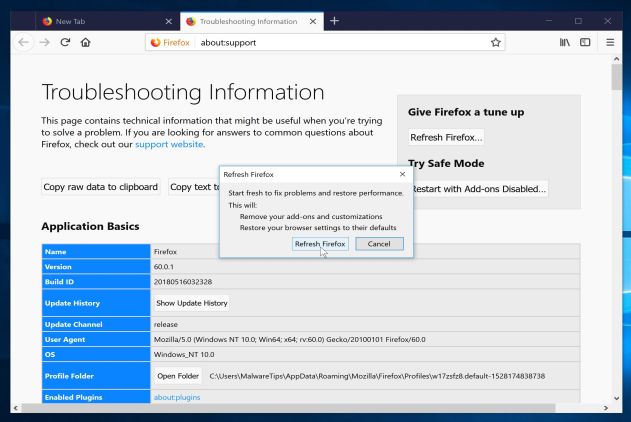
- To continue, click on the “Refresh Firefox” button in the new confirmation window that opens.
- Firefox will close itself and will revert to its default settings. When it’s done, a window will list the information that was imported. Click on the “Finish“.
If you are still experiencing problems while trying to remove JS:Miner-E[Trj] adware from your device, please do one of the following:
- Run a computer scan with ESET Online Scanner
- Ask for help in our Malware Removal Assistance forum.





![How to remove JS:Miner-E[Trj] Trojan (Virus Removal Guide) 1 HitmanPro scanning for JS:Miner-E[Trj] virus](https://malwaretips.com/blogs/wp-content/uploads/2016/08/HitmanPro-Scan.jpg)
![Click on the Gear Icon then on Internet Options [Image: Internet Options in Internet Explorer]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/Internet-Options-Internet-Explorer.jpg)
![In the Advanced tab click on the Reset button [Image: Reset Internet Explorer]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/Reset-Internet-Explorer.jpg)
![Click on the Reset button to revert IE to its default settings [Image: Reset Internet Explorer to its default settings]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/reset-button-Internet-Explorer.jpg)
![Click on the Close button [Image Reset Internet Explorer settings]](https://malwaretips.com/blogs/wp-content/uploads/2014/03/Close-button-Reset.jpg)