Malware.Exploit.Agent.Generic is a heuristic detection designed to generically detect a Trojan Horse. Due to the generic nature of this threat, we are unable to provide specific information on what it does.
Typical behavior for Trojans like Malware.Exploit.Agent.Generic is one or more of the following:
- Download and install other malware.
- Use your computer for click fraud.
- Record your keystrokes and the sites you visit.
- Send information about your PC, including usernames and browsing history, to a remote malicious hacker.
- Give remote access to your PC.
- Advertising banners are injected with the web pages that you are visiting.
- Random web page text is turned into hyperlinks.
- Browser popups appear which recommend fake updates or other software.
Files reported as Malware.Exploit.Agent.Generic may not necessarily be malicious. Should you be uncertain as to whether a file is malicious or a false positive detection, you can submit the affected file to https://www.virustotal.com/en/ to be scanned with multiple antivirus engines.
To check your computer for malware and remove it for free, please use the guide below.
How to remove Malware.Exploit.Agent.Generic Trojan (Virus Removal Guide)
This malware removal guide may appear overwhelming due to the number of steps and numerous programs that are being used. We have only written it this way to provide clear, detailed, and easy-to-understand instructions that anyone can use to remove malware for free.
Please perform all the steps in the correct order. If you have any questions or doubt at any point, stop and ask for our assistance.
- STEP 1: Use Malwarebytes Free to remove Malware.Exploit.Agent.Generic Trojan
- STEP 2: Use HitmanPro to scan for malware and unwanted programs
- STEP 3: Double-check for other malicious programs with Emsisoft Emergency Kit
- STEP 4: Use AdwCleaner to remove malicious browser policies
STEP 1: Use Malwarebytes to remove Malware.Exploit.Agent.Generic Trojan
In this first step, we will install Malwarebytes to scan and remove Malware.Exploit.Agent.Generic malware completely from your computer.
Malwarebytes is one of the most popular and most used anti-malware software for Windows, and for good reasons. It is able to destroy many types of malware that other software tends to miss, without costing you absolutely nothing. When it comes to cleaning up an infected device, Malwarebytes has always been free and we recommend it as an essential tool in the fight against malware.
Download Malwarebytes Free.
You can download Malwarebytes by clicking the link below.
 MALWAREBYTES DOWNLOAD LINK
MALWAREBYTES DOWNLOAD LINK
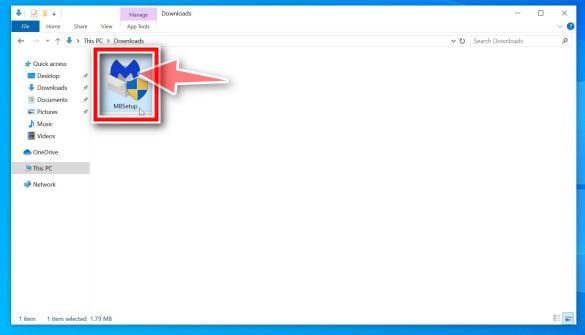
(The above link will open a new page from where you can download Malwarebytes)Double-click on the Malwarebytes setup file.
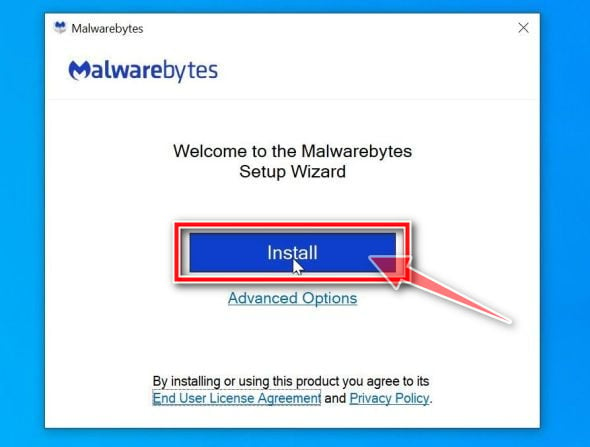
When Malwarebytes has finished downloading, double-click on the MBSetup file to install Malwarebytes on your computer. In most cases, downloaded files are saved to the Downloads folder.
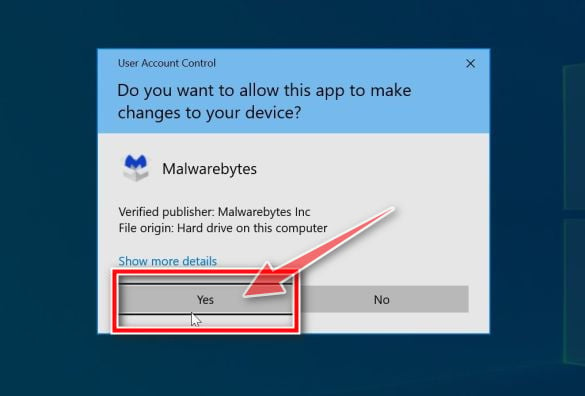
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the Malwarebytes installation.
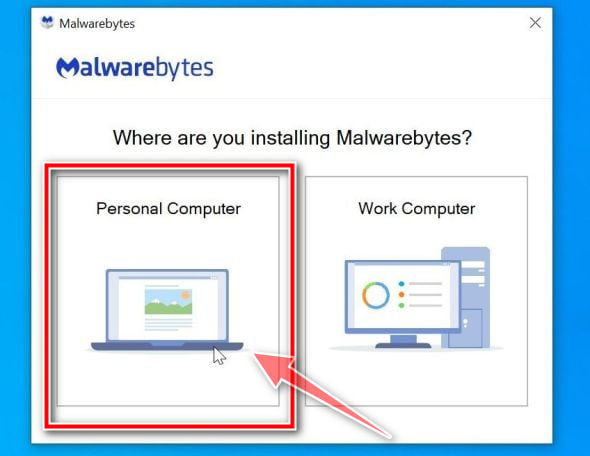
Follow the on-screen prompts to install Malwarebytes.
When the Malwarebytes installation begins, you will see the Malwarebytes setup wizard which will guide you through the installation process. The Malwarebytes installer will first ask you on what type of computer are you installing this program, click either Personal Computer or Work Computer.
On the next screen, click “Install” to install Malwarebytes on your computer.
When your Malwarebytes installation completes, the program opens to the Welcome to Malwarebytes screen. Click the “Get started” button.
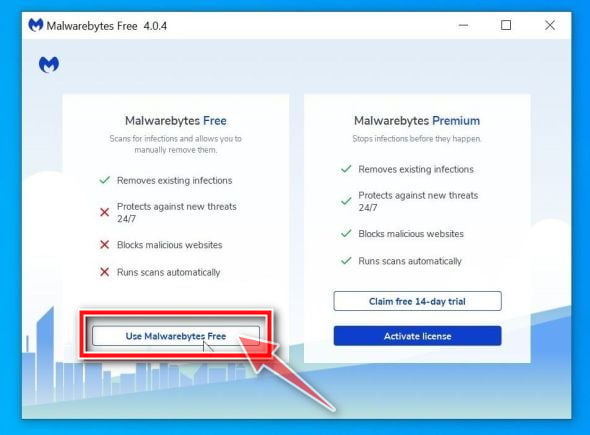
Select “Use Malwarebytes Free”.
After installing Malwarebytes, you’ll be prompted to select between the Free and the Premium version. The Malwarebytes Premium edition includes preventative tools like real-time scanning and ransomware protection; however, we will use the Free version to clean up the computer.
Click on “Use Malwarebytes Free“.
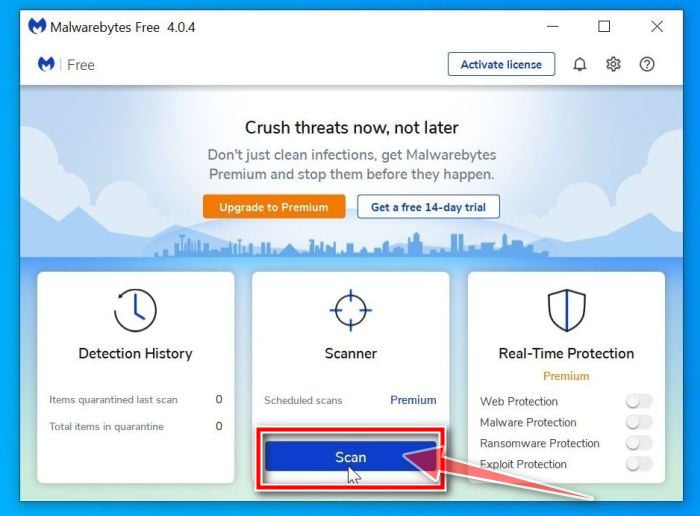
Click on “Scan”.
To scan your computer with Malwarebytes, click on the “Scan” button. Malwarebytes will automatically update the antivirus database and start scanning your computer for Malware.Exploit.Agent.Generic virus and other malicious programs.
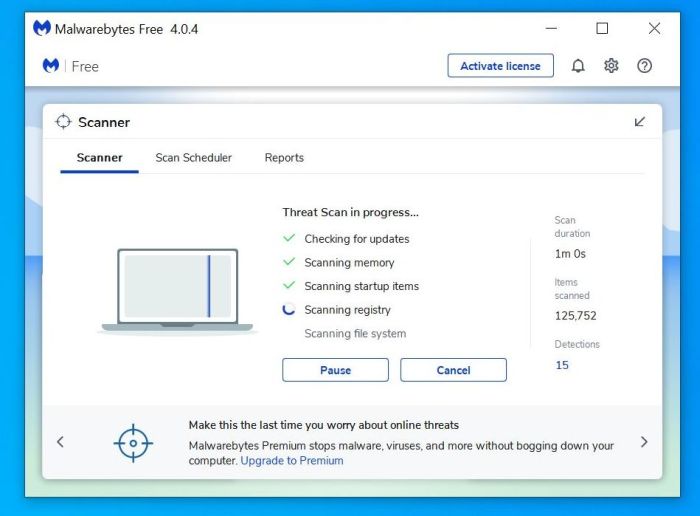
Wait for the Malwarebytes scan to complete.
Malwarebytes will scan your computer for Malware.Exploit.Agent.Generic malware and other malicious programs. This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
Click on “Quarantine”.
When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected. To remove the Malware.Exploit.Agent.Generic extension and other malicious programs that Malwarebytes has found, click on the “Quarantine” button.
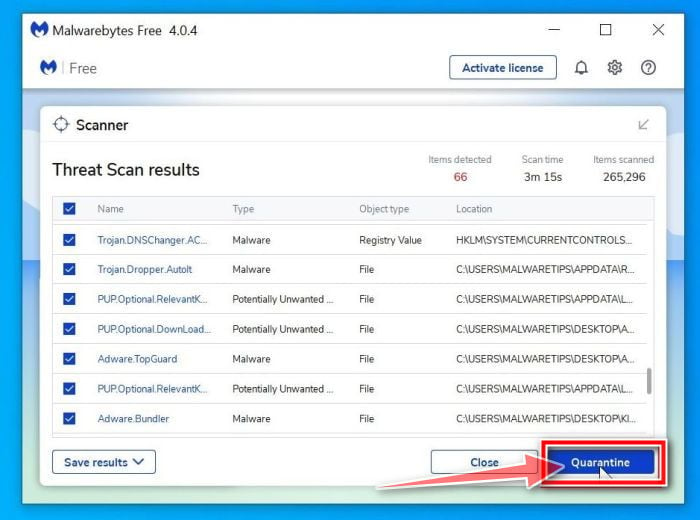
Restart computer.
Malwarebytes will now remove all the malicious files and registry keys that it has found. To complete the malware removal process, Malwarebytes may ask you to restart your computer.
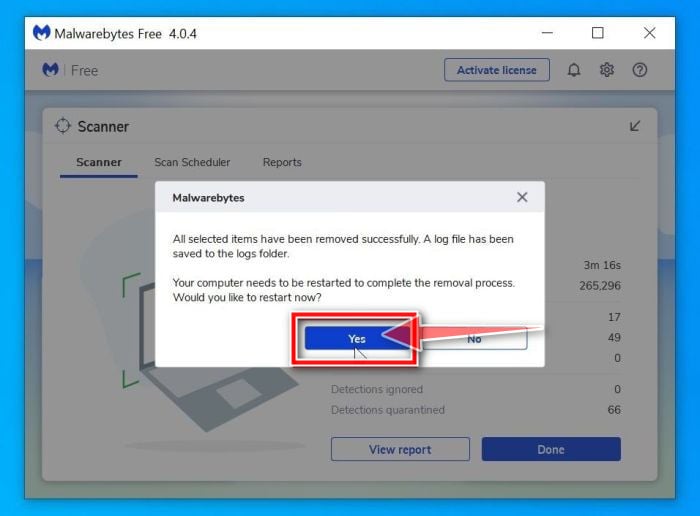
When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
STEP 2: Use HitmanPro to scan your computer for Malware.Exploit.Agent.Generic Trojan
In this next step, we will scan the computer with HitmanPro to ensure that no other malicious programs are installed on your device.
HitmanPro is a second opinion scanner that takes a unique cloud-based approach to malware scanning. HitmanPro scans the behavior of active files and also files in locations where malware normally resides for suspicious activity. If it finds a suspicious file that’s not already known, HitmanPro sends it to its clouds to be scanned by two of the best antivirus engines today, which are Bitdefender and Kaspersky.
Although HitmanPro is shareware and costs $24.95 for 1 year on 1 PC, there is actually no limit in scanning. The limitation only kicks in when there is a need to remove or quarantine detected malware by HitmanPro on your system and by then, you can activate the one time 30-days trial to enable the cleanup.
Download HitmanPro.
You can download HitmanPro by clicking the link below.
 HITMANPRO DOWNLOAD LINK
HITMANPRO DOWNLOAD LINK
(The above link will open a new web page from where you can download HitmanPro)Install HitmanPro.
When HitmanPro has finished downloading, double-click on “hitmanpro.exe” (for 32-bit versions of Windows) or “hitmanpro_x64.exe” (for 64-bit versions of Windows) to install this program on your PC. In most cases, downloaded files are saved to the Downloads folder.
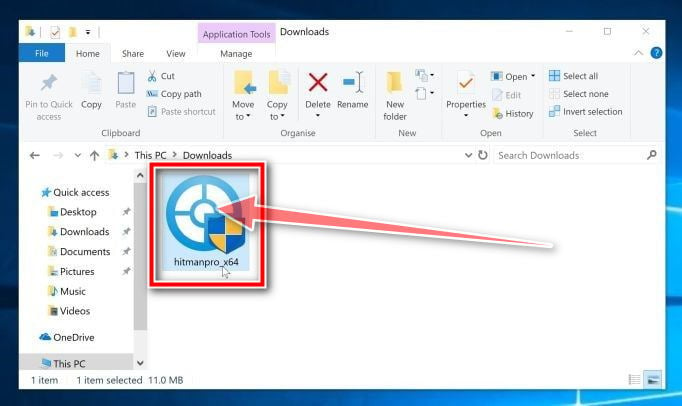
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation.

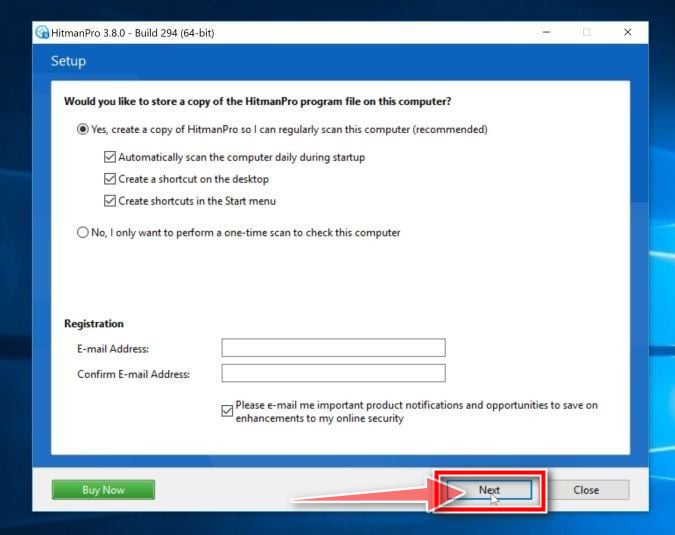
Follow the on-screen prompts.
When HitmanPro starts you will be presented with the start screen as shown below. Click on the “Next” button to perform a system scan.

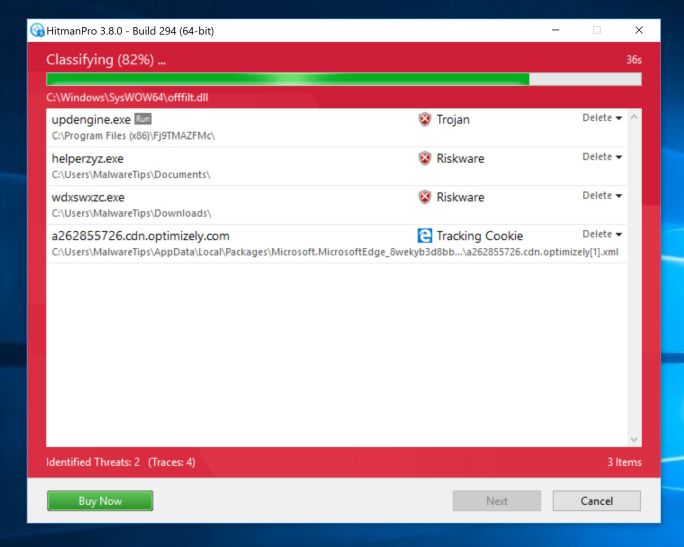
Wait for the HitmanPro scan to complete.
HitmanPro will now begin to scan your computer for Malware.Exploit.Agent.Generic malware and other malicious programs.
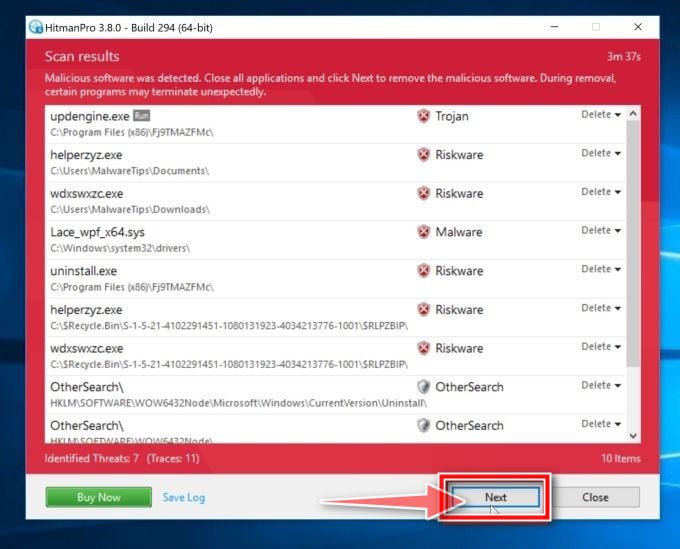
Click on “Next”.
When HitmanPro has finished the scan, it will display a list of all the malware that the program has found. Click on the “Next” button to remove Malware.Exploit.Agent.Generic malware and other malicious programs.
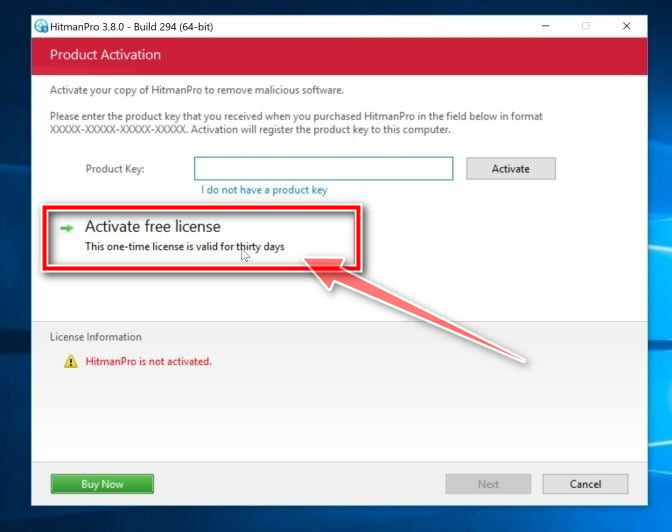
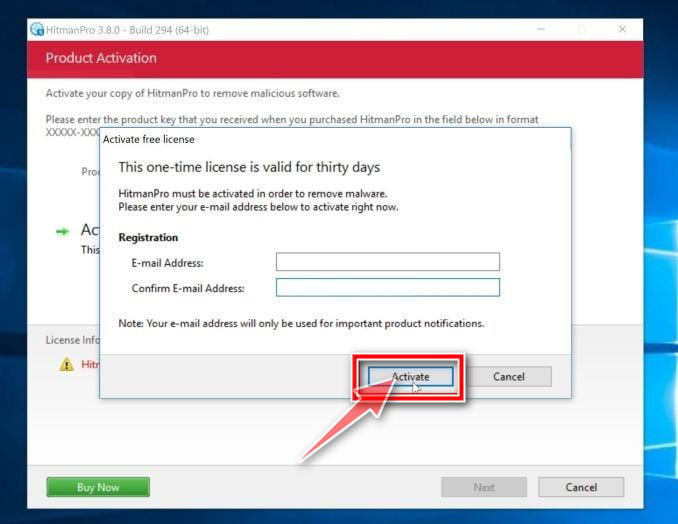
Click on “Activate free license”.
Click on the “Activate free license” button to begin the free 30 days trial and remove all the malicious files from your PC.
When the malware removal process is complete, you can close HitmanPro and continue with the next step.
STEP 3: Double-check for other malicious programs with Emsisoft Emergency Kit
In this third step, we will download, install and run a scan with Emsisoft to search and remove any other malicious file or registry key that might be installed on your computer.
Emsisoft Emergency Kit is a free and powerful on-demand scanner that can be used to remove viruses, trojans, spyware, adware, worms, and other malicious programs.
Download Emsisoft Emergency Kit.
You can download Emsisoft Emergency Kit by clicking the link below.
 EMSISOFT EMERGENCY KIT DOWNLOAD LINK
EMSISOFT EMERGENCY KIT DOWNLOAD LINK
(The above link will open a new web page from where you can download Emsisoft Emergency Kit)Install Emsisoft Emergency Kit.
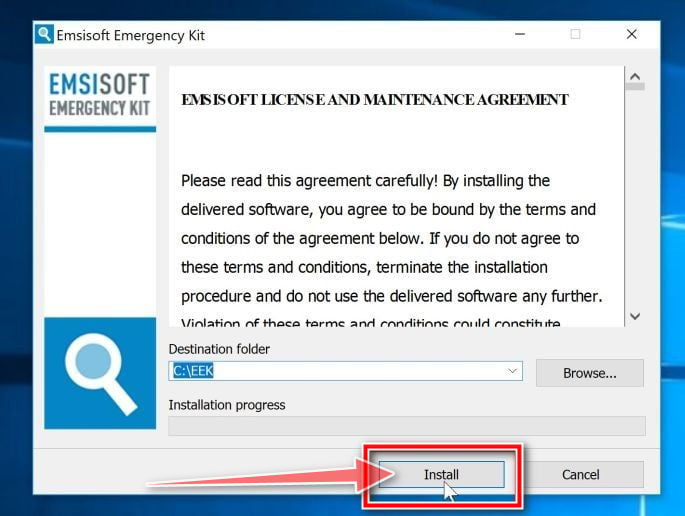
Double-click on the EmsisoftEmergencyKit setup file to start the installation process, then click on the “Install” button.
Start Emsisoft Emergency Kit.
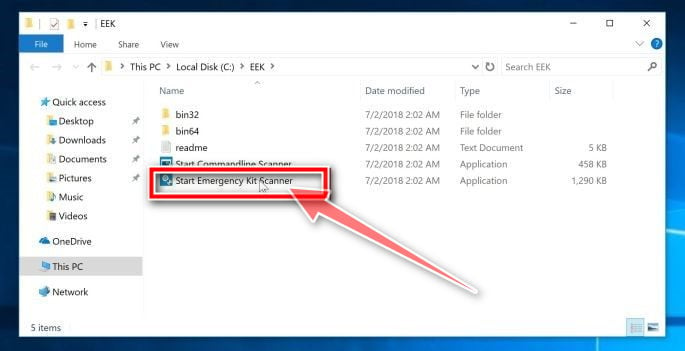
On your desktop the “EEK” folder (C:\EEK) should now be open. To start Emsisoft, click on the “Start Emsisoft Emergency Kit” file to open this program.
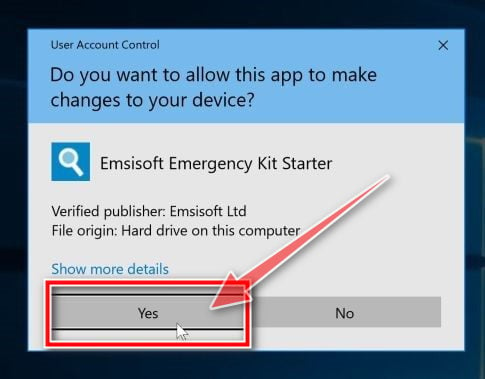
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
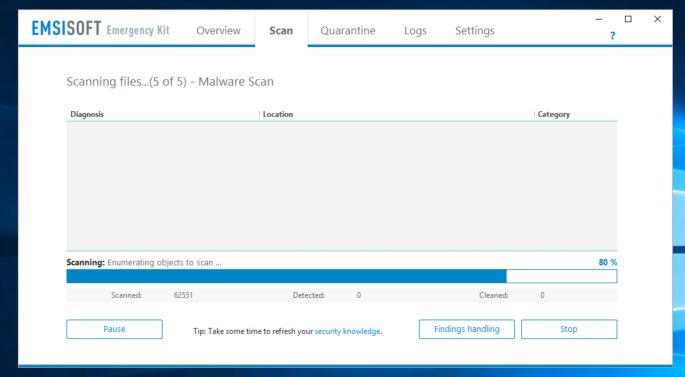
Click on “Malware Scan”.
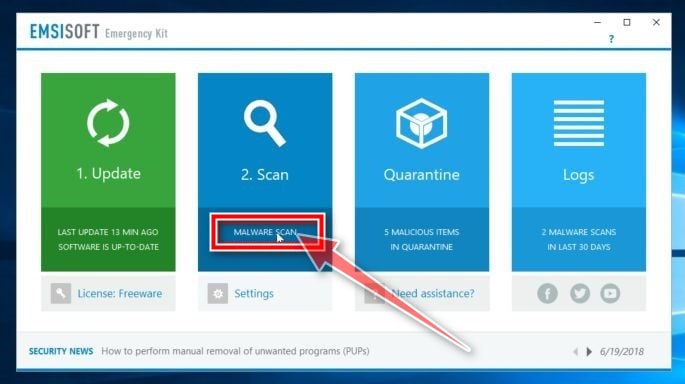
Emsisoft Emergency Kit will start and it will ask you for permission to update itself. Once the update process is complete, click on the “Scan” tab, and perform a “Malware Scan“.
Emsisoft Emergency Kit will now scan your computer for the Malware.Exploit.Agent.Generic mawlare. This process can take a few minutes.
Click on “Quarantine selected”.
When the Emsisoft scan has finished, you will be presented with a screen reporting which malicious files were detected on your computer. To remove the Malware.Exploit.Agent.Generic malicious programs, click on the “Quarantine selected“.
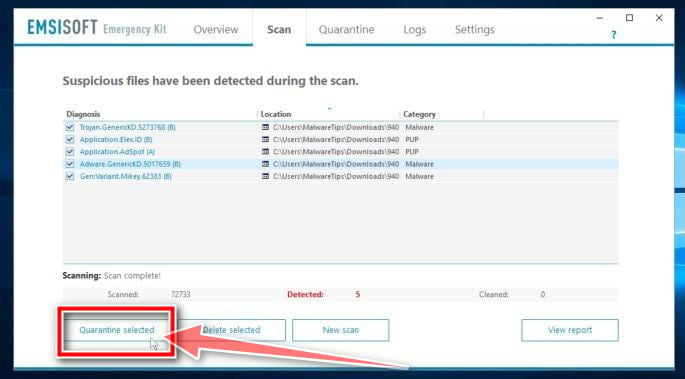
When the malware removal process is complete, Emsisoft Emergency Kit may need to restart your computer. Click on the “Reebot” button to restart your computer.
STEP 4: Use AdwCleaner to remove malicious browser policies
In this final step, we will use AdwCleaner to remove malicious browser policies and unwanted browser extensions from your computer.
AdwCleaner is a free popular on-demand scanner that can detect and remove malware that even the most well-known anti-virus and anti-malware applications fail to find. This on-demand scanner includes a lot of tools that can be used to fix the side effects of browser hijackers.
Download AdwCleaner.
You can download AdwCleaner by clicking the link below.
 ADWCLEANER DOWNLOAD LINK
ADWCLEANER DOWNLOAD LINK
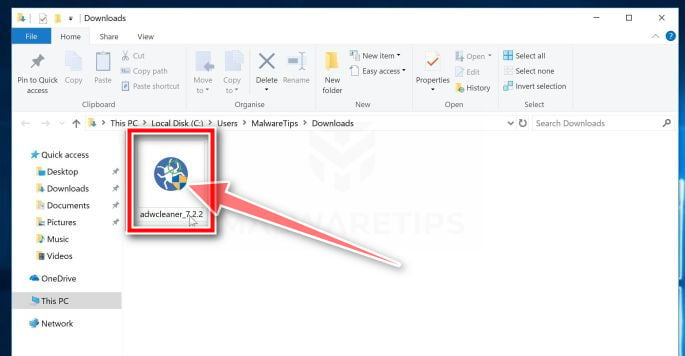
(The above link will open a new web page from where you can download AdwCleaner)Double-click on the setup file.
Double-click on the file named “adwcleaner_x.x.x.exe” to start AdwCleaner. In most cases, downloaded files are saved to the Downloads folder.
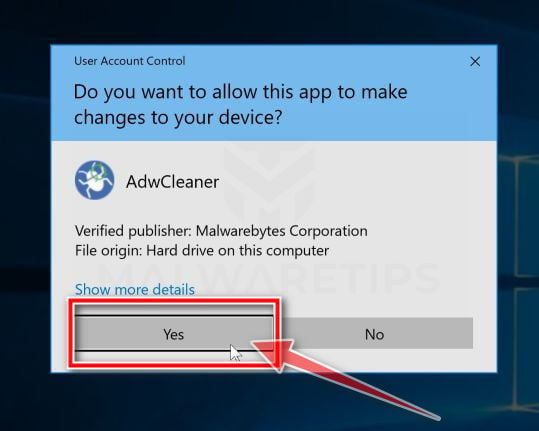
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
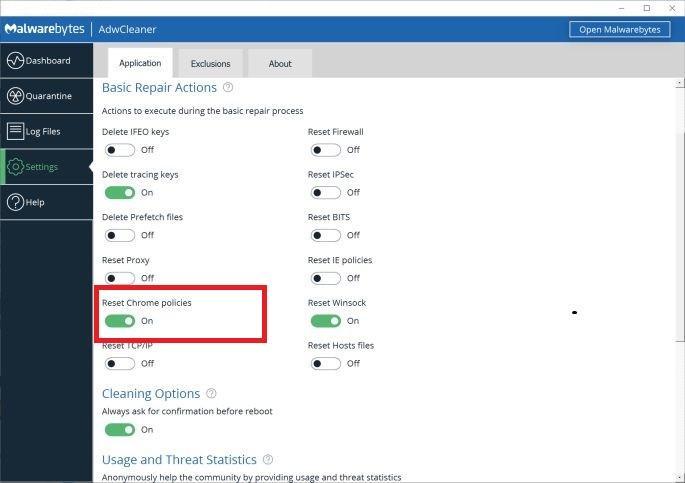
Enable “Reset Chrome policies”.
When AdwCleaner starts, on the left side of the window, click on “Settings” and then enable “Reset Chrome policies“.
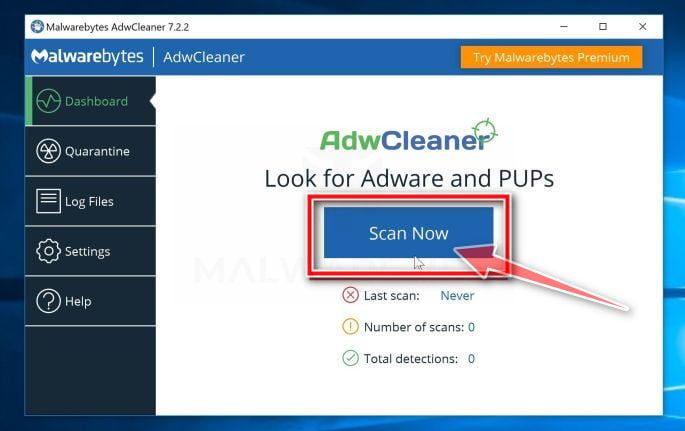
Click on “Scan Now”.
On the left side of the window, click on “Dashboard” and then click “Scan Now” to perform a system scan.
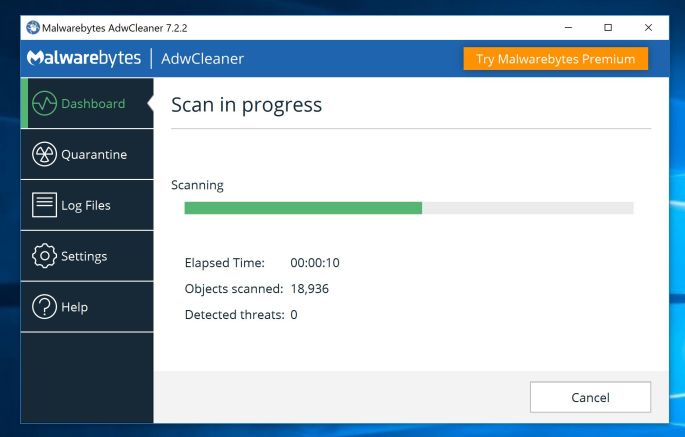
Wait for the AdwCleaner scan to complete.
AdwCleaner will now scan your computer for the Malware.Exploit.Agent.Generic Trojan and other malicious programs. This process can take a few minutes.
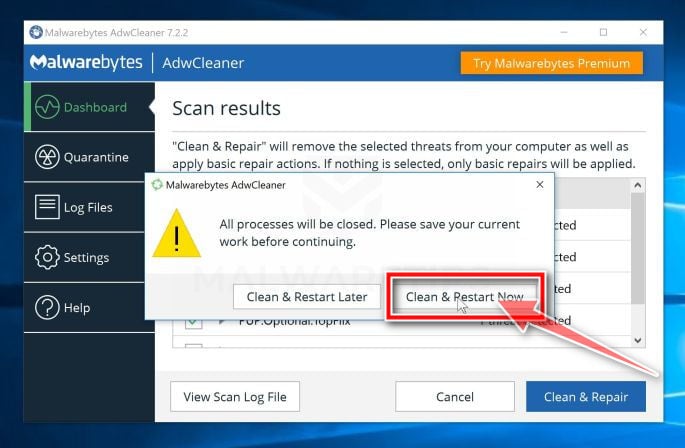
Click on “Clean & Repair”.
When AdwCleaner has finished it will display a list of all the malware that the program found. Click on the “Clean & Repair” button to remove the Malware.Exploit.Agent.Generic Trojan and other malicious programs from your computer.
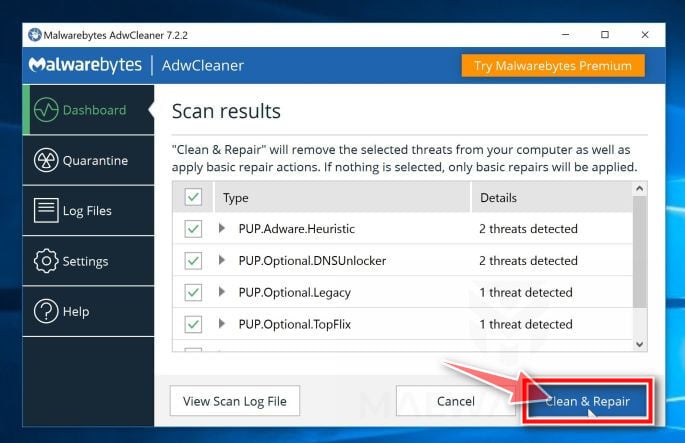
Click on “Clean & Restart Now”
When the malware removal process is complete, AdwCleaner may need to restart your device. Click on the “Clean & Restart Now” button to finish the removal process.
Your computer should now be free of the Malware.Exploit.Agent.Generic malware and other malicious programs. If your current antivirus allowed this malicious program on your computer, you may want to consider purchasing the full-featured version of Malwarebytes Anti-Malware to protect against these types of threats in the future.
If you are still having problems with your computer after completing these instructions, then please follow one of the steps:
- Run a computer scan with ESET Online Scanner
- Ask for help in our Malware Removal Assistance for Windows forum.