Optimizer Pro v3.2 (from PC Utilities Software Limited) is a system optimizer utility, which is promoted via other free downloads, and once installed it claims that several issues were been detected on your computer. However, if you try to fix these issues, Optimizer Pro v3.2 will state that you need to buy its full version before being able to do so.
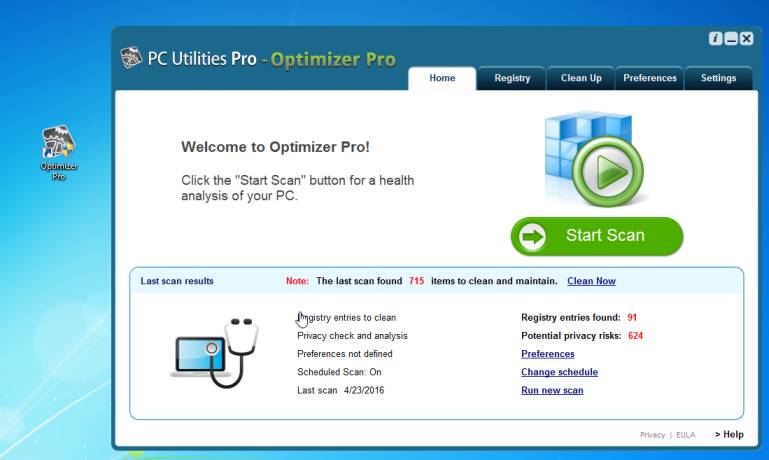
Optimizer Pro v3.2 is a paid system optimizer program that is typically added when you install another free software (video recording/streaming, download-managers or PDF creators) that had bundled into their installation this program. Very often users have no idea where did it come from, so it’s not surprising at all that most of them assume that Optimizer Pro v3.2 is a virus.
The Windows registry is a database that Windows and its applications store their settings in. It contains hundreds of thousands of entries. Some of the entries may be slightly outdated — maybe you’ve uninstalled a program and it left a key or two behind, or maybe a there’s a file extension with no associated application.
Optimizer Pro v3.2 scan your registry for these outdated entries and offer to remove them. Because there are so many registry entries to go through, this program may sometimes also remove useful registry entries, causing you problems. The Web is full of stories from people who have run a registry cleaner and encountered problems. In a best case scenario, Optimizer Pro v3.2 will remove a few hundred unnecessary entries and reduce the size of your registry by a few kilobytes. This makes no difference in perceptible performance.
If you must use a registry cleaner, you don’t have to pay anything. Using a free registry cleaner, such as the registry cleaner included with the respected CCleaner utility, is good enough.
You should always pay attention when installing software because often, a software installer includes optional installs, such as this Optimizer Pro v3.2. Be very careful what you agree to install.
Always opt for the custom installation and deselect anything that is not familiar, especially optional software that you never wanted to download and install in the first place. It goes without saying that you should not install software that you don’t trust.
How to remove Optimizer Pro v3.2 (Uninstall Guide)
This page is a comprehensive guide which will remove Optimizer Pro v3.2 and any other adware program that may be installed on your machine.
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
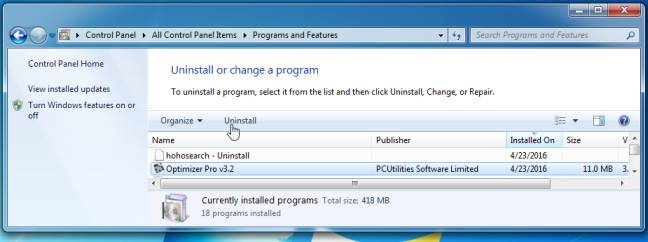
STEP 1: Uninstall Optimizer Pro v3.2 from Windows
STEP 2: Scan with Malwarebytes Anti-Malware to check for other potentially unwanted programs
STEP 3: Double-check with HitmanPro for other adware or browser hijackers
STEP 1 : Uninstall Optimizer Pro v3.2 from Windows
In this first step, we will try to identify and remove any malicious program that might be installed on your computer.
- Go to the uninstall menu.
Windows 10 or Windows 8
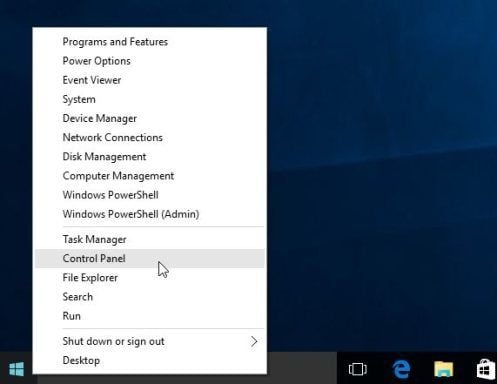
- To uninstall a program on Windows 10 or Windows 8, right-click on the Windows Start button and choose “Control Panel” from the pop-up menu.
- When the “Control Panel” window opens click on the “Uninstall a program” option under “Programs” category.
Windows 7 or Windows Vista
- If you are using Windows XP, Windows Vista or Windows 7, click the “Start” button, then click on the “Control Panel” menu option.
- When the “Control Panel” window opens click on the “Uninstall a program” option under “Programs” category.
- To uninstall a program on Windows 10 or Windows 8, right-click on the Windows Start button and choose “Control Panel” from the pop-up menu.
- When the “Programs and Features” screen is displayed, scroll through the list of currently installed programs and uninstall “Optimizer Pro v3.2” and “LiveSupport toolbar”.
The malicious program may have a different name on your computer. To view the most recently installed programs, you can click on the “Installed On” column to sort your program by the installation date. Scroll through the list, and uninstall any unwanted or unknown programs.If you are having issues while trying to uninstall the Optimizer Pro v3.2 program, you can use Revo Uninstaller to completely remove this unwanted program from your machine.If you cannot find any unwanted or unknown programs on your machine, then you can proceed with the next step.
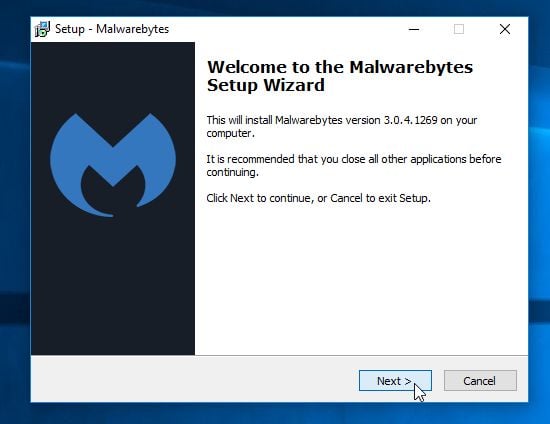
STEP 2: Scan with Malwarebytes Anti-Malware to check for other potentially unwanted programs
Malwarebytes Anti-Malware Free uses industry-leading technology to detect and remove all traces of malware, including worms, Trojans, rootkits, rogues, dialers, spyware, and more.
It is important to note that Malwarebytes Anti-Malware works well and should run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download “Malwarebytes Anti-Malware Free”) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup” to start the installation of Malwarebytes Anti-Malware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
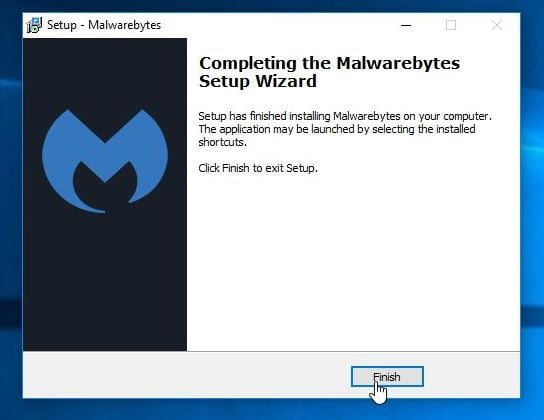
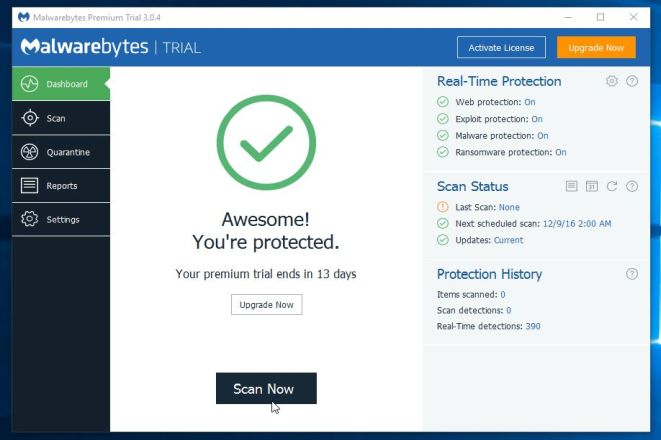
- Once installed, Malwarebytes Anti-Malware will automatically start and you will see a message stating that you should update the program, and that a scan has never been run on your system. To start a system scan you can click on the “Scan Now” button.
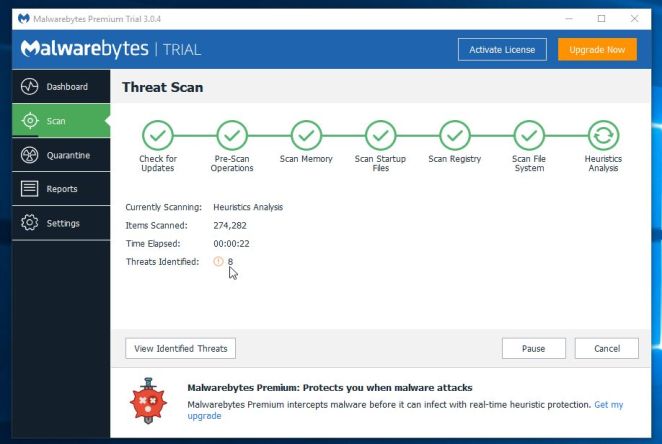
- Malwarebytes Anti-Malware will now start scanning your computer for the Optimizer Pro v3.2 adware. When Malwarebytes Anti-Malware is scanning it will look like the image below.
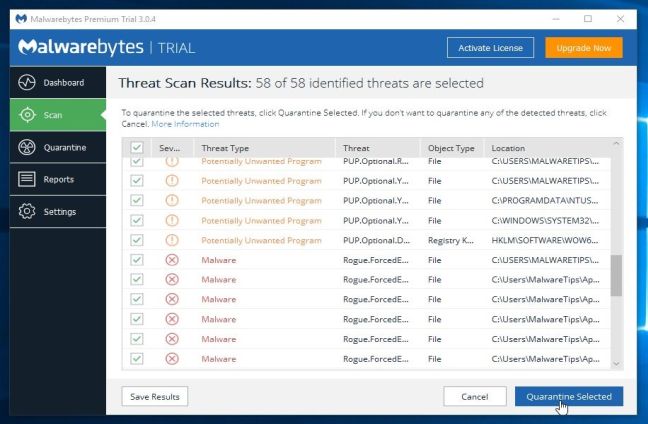
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Remove Selected” button.
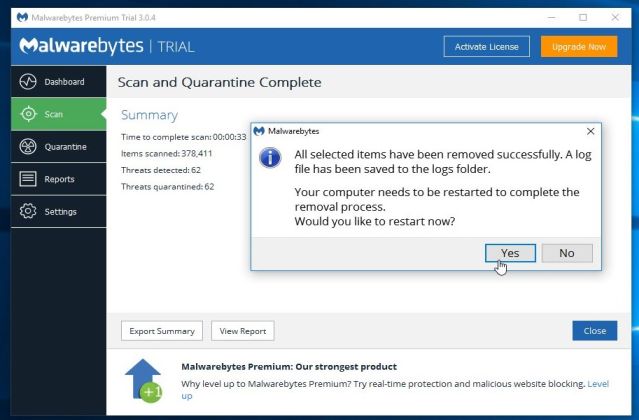
Please note that the infections found may be different than what is shown in the image. - Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
After your computer will restart, you should open Malwarebytes Anti-Malware and perform another “Threat Scan” scan to verify that there are no remaining threats
STEP 3: Double-check with HitmanPro for other adware or browser hijackers
HitmanPro is a second opinion scanner, designed to rescue your computer from malware (viruses, trojans, rootkits, etc.) that have infected your computer despite all the security measures you have taken (such as anti-virus software, firewalls, etc.). HitmanPro is designed to work alongside existing security programs without any conflicts. It scans the computer quickly (less than 5 minutes) and does not slow down the computer.
- You can download HitmanPro from the below link:
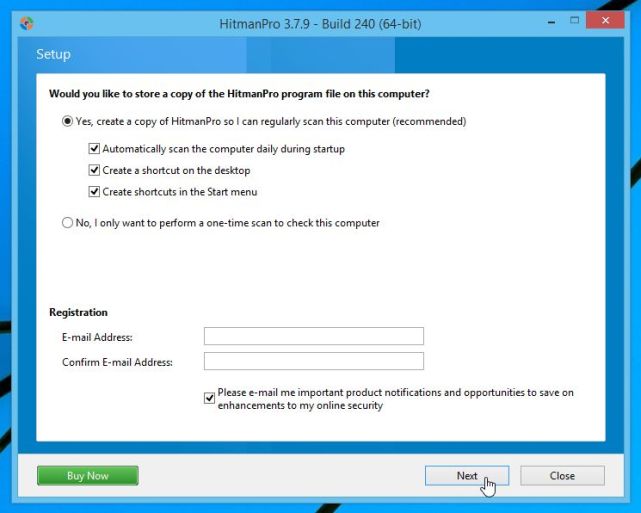
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.
Click on the “Next” button, to install HitmanPro on your computer.
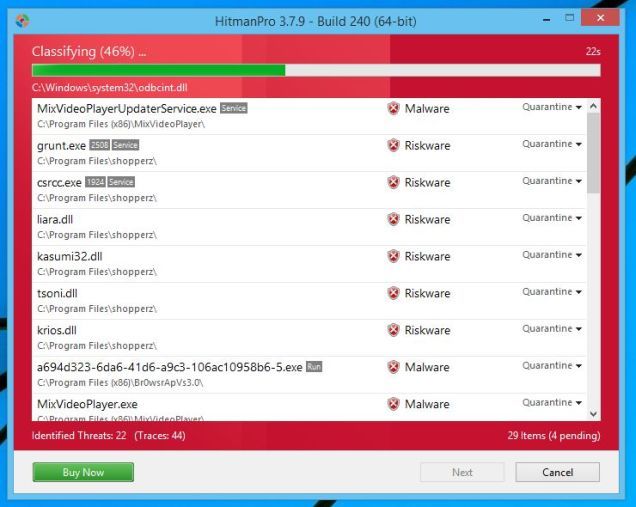
- HitmanPro will now begin to scan your computer for the Optimizer Pro v3.2 malware.
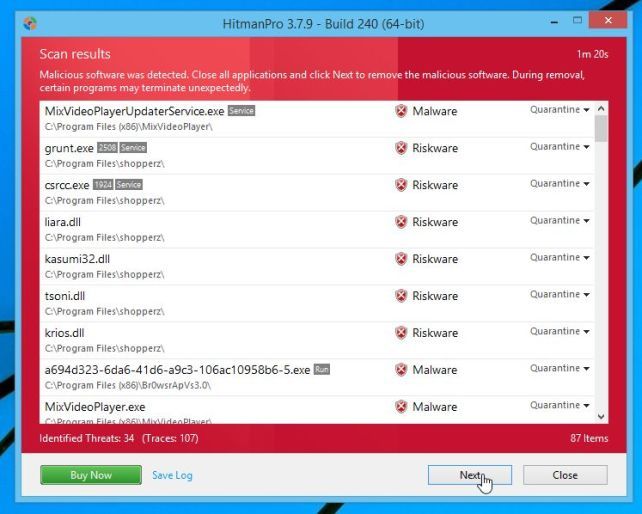
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
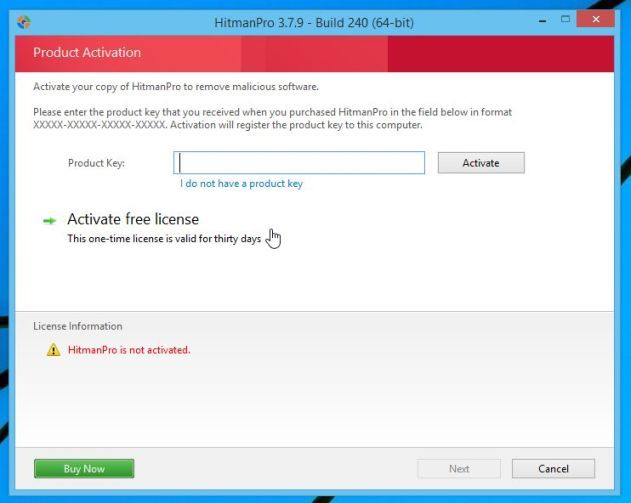
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
Your computer should now be free of the Optimizer Pro v3.2.
If you are still experiencing problems while trying to remove Optimizer Pro v3.2 from your machine, please do one of the following:
- Run a system scan with Emsisoft Emergency Kit.
- Start a new thread in our Malware Removal Assistance forum.

![Control Panel in Windows Start Menu [Image: Control Panel in Windows Start Menu]](https://malwaretips.com/blogs/wp-content/uploads/2014/08/windows-start-menu-control-panel.jpg)
![Click on Uninstall a program [Image: Uninstall a program]](https://malwaretips.com/blogs/wp-content/uploads/2013/03/uninstall-a-program-windows.jpg)