Rabbit ransomware is a Trojan Horse that will lock your computer and display a “Your Windows has been Infected by Rabbit Ransomware” screen locker instead of your normal Windows desktop.
The Rabbit ransomware is distributed through several means. Malicious websites, or legitimate websites that have been hacked, can infect your computer through exploit kits that use vulnerabilities on your computer to install this Trojan without your permission or knowledge.
The Rabbit ransomware may also be downloaded manually by tricking the user into thinking they are installing a useful piece of software, for instance a bogus update for Adobe Flash Player or another piece of software. The Rabbit ransomware is also prevalent on peer-to-peer file sharing websites and is often packaged with pirated or illegally acquired software.
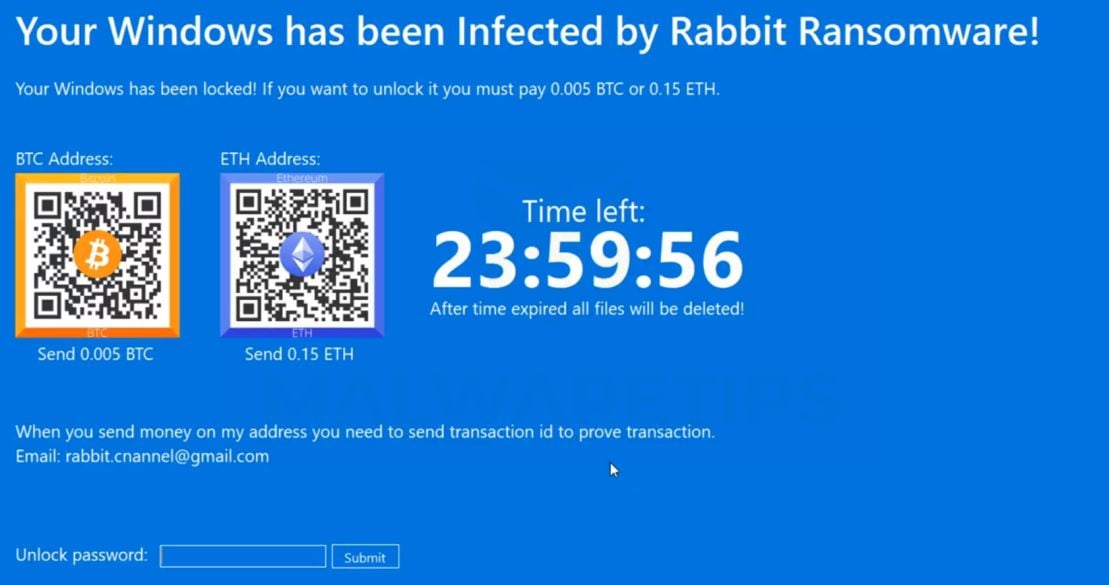
When a computer is infected, the Rabbit ransomware displays a lock screen when you start Windows which will state that the victim’s files will be deleted in 24 hours unless 0.005 BTC or 0.15 ETH are sent to an bitcoin address. The malware developers state that once they verify the payment the computer will automatically be unlocked and you will be able to access your Windows desktop again.
The text of the Rabbit ransomware screen locker is:
Your Windows has been Infected by Rabbit Ransomware!
Your Windows has been locked! If you want to unlock it you must pay 0.005 BTC or 0.15 ETH
When you send money on my address you need to send transaction id to prove transaction.
Email: rabbit.cnannel@gmail.com
Unlock password:
While the text in these messages can be scary, the good news is that the Rabbit ransomware will not delete or encrypt any files, and can be removed without paying the ransomware. To close the Rabbit ransomware screen locker, simply enter RabbCompany66 into the “Unlock password” field and the program will automatically close. If that does not work, you can reboot into safe mode and remove it from there while it is not loaded.
The Rabbit ransomware screen locker is a complete scam that is designed to scare people into paying the ransom. By paying the ransom you just encourage the malware developers to continue making malware like Rabbit ransomware.
How to remove Rabbit Ransomware (Removal Guide)
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
- STEP 1: Remove Rabbit ransomware lock screen from Windows
- STEP 2: Use Malwarebytes to remove Rabbit Ransomware
- STEP 3: Use HitmanPro to scan for malware and unwanted programs
- STEP 4: Double-check for malicious programs with Zemana AntiMalware Free
STEP 1 : Remove Rabbit ransomware lock screen from Windows
To close the Rabbit ransomware screen locker, simply enter RabbCompany66 into the “Unlock password” field and the program will automatically close. It’s important to understand that by entering this code, the Trojan will not be removed from your computer, instead it will just stop displaying the lock screen, so that you’ll be able to complete this removal guide without being interrupted by this infection.
If you have entered the code and now you’re able to normally login into Windows, then you can skip to STEP 2 from this guide.
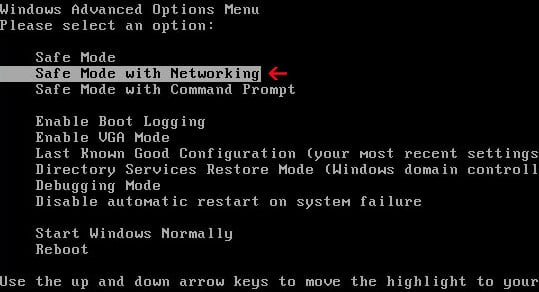
If the above code does not work, you will need to start your computer in Safe Mode with Networking to bypass the Rabbit ransomware lock screen. Safe mode starts Windows in a basic state, using a limited set of files and drivers, so this will prevent Rabbit ransomware from running at startup.
There are two versions of safe mode: Safe Mode and Safe Mode with Networking. They’re quite similar, but Safe Mode with Networking includes the network drivers and services you’ll need to access the Internet.
Windows 10 or Windows 8
Before you enter safe mode, you need to enter the Windows Recovery Environment (winRE). It’s also possible that you can repeatedly press the F8 key during boot (before the Windows logo is displayed) to access these screens. Some PC manufacturers disable this action, and on some PCs, startup is fast enough that it’s hard to hit the key at the right time. But, there’s no harm in trying.
If mashing the F8 key didn’t work, we will need to turn off and on your device twice in a row before Windows starts. Doing this should automatically present you with a “Recovery” option that lets you see advanced repair options.
- Hold down the power button for 10 seconds to turn off your device.
- Press the power button again to turn on your device.
- On the first sign that Windows has started (for example, some devices show the manufacturer’s logo when restarting) hold down the power button for 10 seconds to turn off your device.
- Press the power button again to turn on your device.
- When Windows restarts, hold down the power button for 10 seconds to turn off your device.
- Press the power button again to turn on your device.
- Allow your device to fully restart. You will enter winRE.
Now that you are in winRE, you will follow these steps to take you to safe mode:
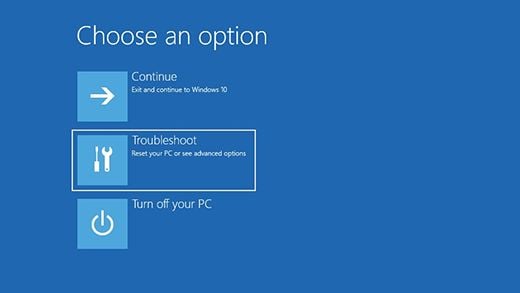
- On the Choose an option screen, select “Troubleshoot“.
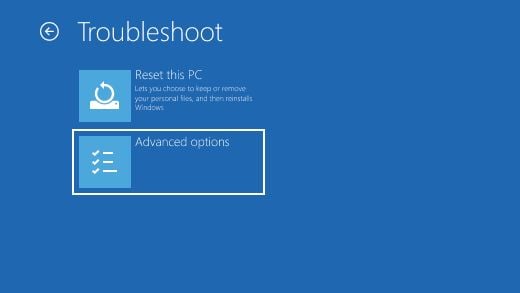
- On the “Troubleshoot” screen, click the “Advanced Options” button.
- On the “Advanced Options” page, click the “Startup Settings” option. In Windows 8, this option is labelled “Windows Startup Settings” instead.
- On the “Startup Settings” page, click the “Restart”.
- After your device restarts, you’ll see a list of options. Select option 5 from the list or press F5 for Safe Mode with Networking.
- While your computer is running in Safe Mode with Networking, we will need to download, install and run a scan with Malwarebytes (Step 2).
Windows 7
- Remove all floppy disks, CDs, and DVDs from your computer, and then restart your computer.
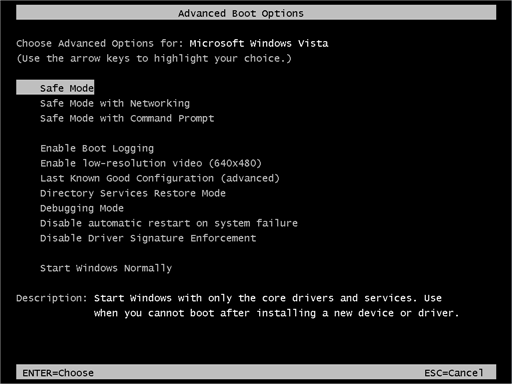
- When the computer starts you will see your computer’s hardware being listed. When you see this information start to press the F8 key repeatedly until you are presented with the Advanced Boot Options.
- In the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking and then press Enter.
STEP 2: Use Malwarebytes to remove Rabbit Ransomware
Malwarebytes is one of the most popular and most used anti-malware software for Windows, and for good reasons. It is able to destroy many types of malware that other software tends to miss, without costing you absolutely nothing. When it comes to cleaning up an infected device, Malwarebytes has always been free and we recommend it as an essential tool in the fight against malware.
The first time you install Malwarebytes, you’re given a free 14-day trial of the premium edition, which includes preventative tools like real-time scanning and specific protection from ransomware. After two weeks, it automatically reverts to the basic free version that will detect and clean up malware infections only when you run a scan. It is important to note that Malwarebytes will run alongside antivirus software without conflicts.
-
Download Malwarebytes.
You can download Malwarebytes by clicking the link below.
MALWAREBYTES DOWNLOAD LINK
(The above link will open a new page from where you can download Malwarebytes) -
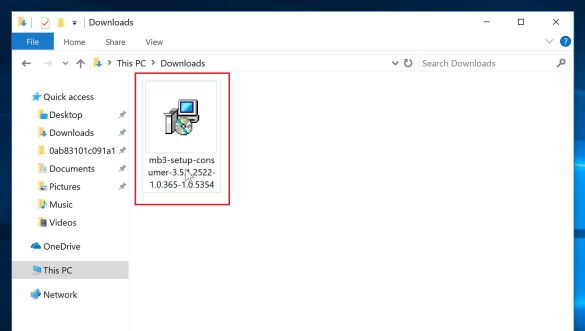
Double-click on the Malwarebytes setup file.
When Malwarebytes has finished downloading, double-click on the mb3-setup-consumer-x.x.x.xxxx.exe file to install Malwarebytes on your PC. In most cases, downloaded files are saved to the Downloads folder.
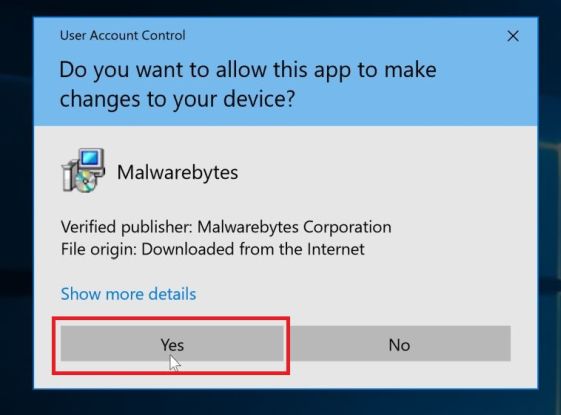
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
-
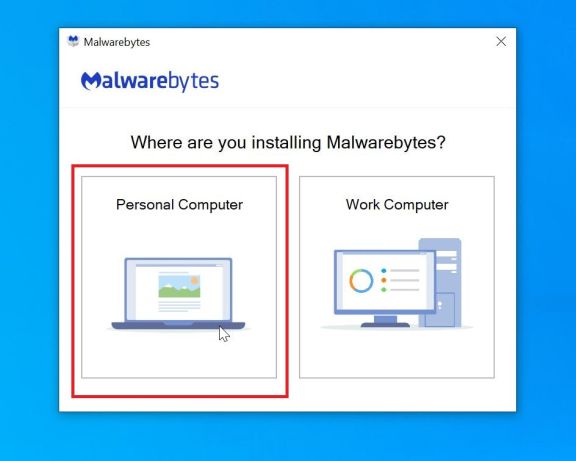
Follow the on-screen prompts to install Malwarebytes.
When the Malwarebytes installation begins, you will see the Malwarebytes Setup Wizard which will guide you through the installation process. To install Malwarebytes on your PC, click on the “Agree and Install” button.
-
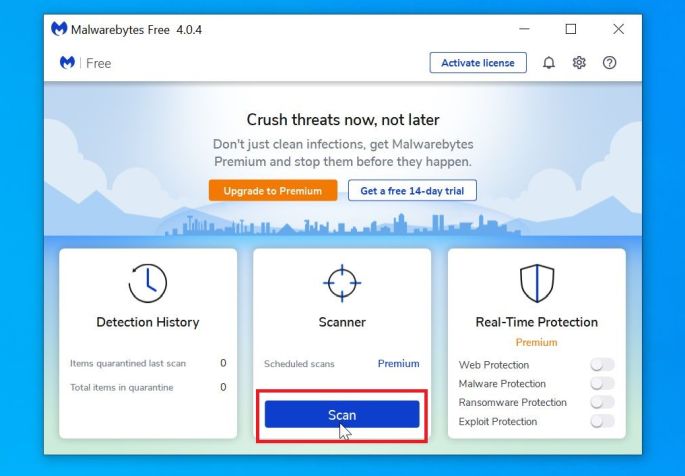
Click on “Scan Now”.
Once installed, Malwarebytes will automatically start and update the antivirus database. To perform a system scan, click on the “Scan Now” button.
-
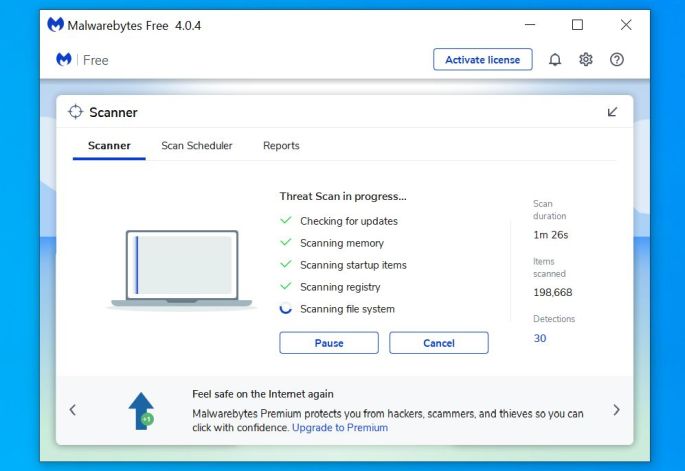
Wait for the Malwarebytes scan to complete.
Malwarebytes will now start scanning your computer for adware and other malicious programs. This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
-
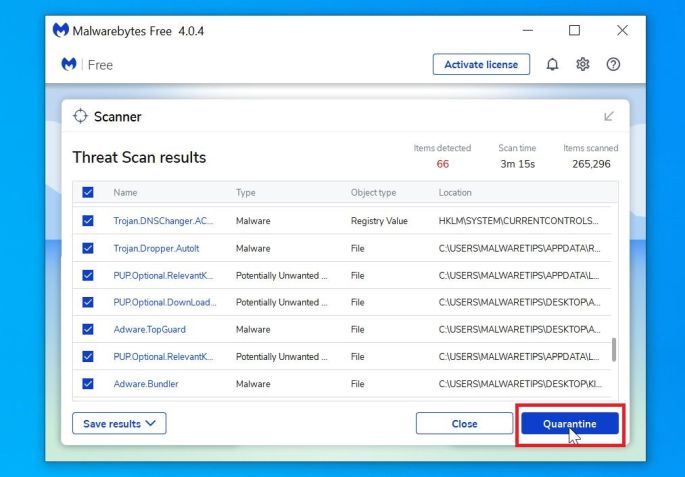
Click on “Quarantine Selected”.
When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected. To remove the malicious programs that Malwarebytes has found, click on the “Quarantine Selected” button.
-
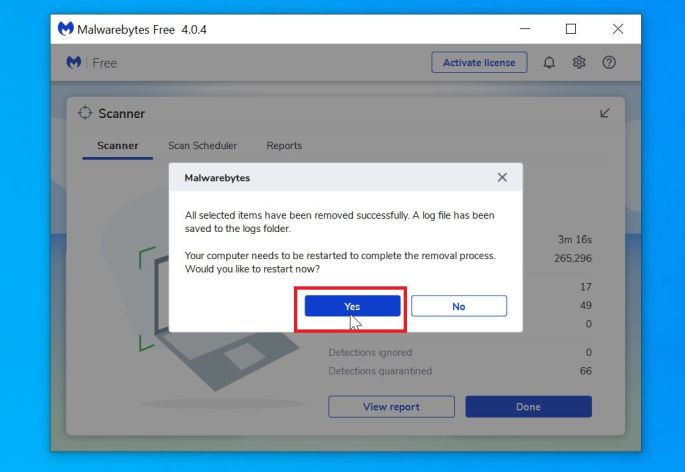
Reboot your computer.
Malwarebytes will now remove all the malicious files and registry keys that it has found. To complete the malware removal process, Malwarebytes may ask you to restart your computer.
When the malware removal process is complete, you can exit Safe Mode with Networking and continue with the rest of the instructions.
STEP 3: Use HitmanPro to scan for malware and unwanted programs
HitmanPro is a second opinion scanner that takes a unique cloud-based approach to malware scanning. HitmanPro scans the behavior of active files and also files in locations where malware normally resides for suspicious activity. If it finds a suspicious file that’s not already known, HitmanPro sends it to their clouds to be scanned by two of the best antivirus engines today, which are Bitdefender and Kaspersky.
Although HitmanPro is shareware and costs $24.95 for 1 year on 1 PC, there is actually no limit in scanning. The limitation only kicks in when there is a need to remove or quarantine detected malware by HitmanPro on your system and by then, you can activate the one time 30 day trial to enable the clean up.
-
Download HitmanPro.
You can download HitmanPro by clicking the link below.
HITMANPRO DOWNLOAD LINK
(The above link will open a new web page from where you can download HitmanPro) -
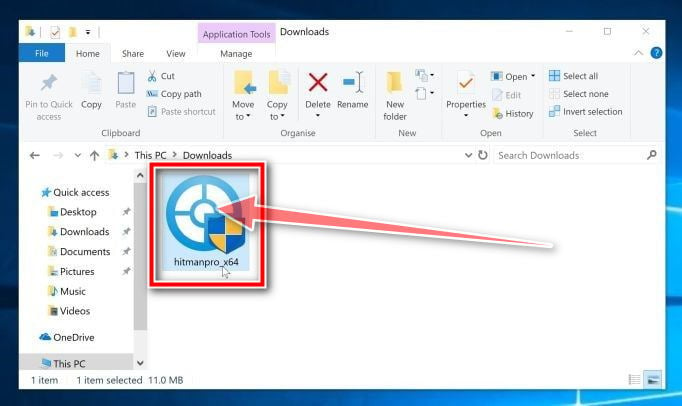
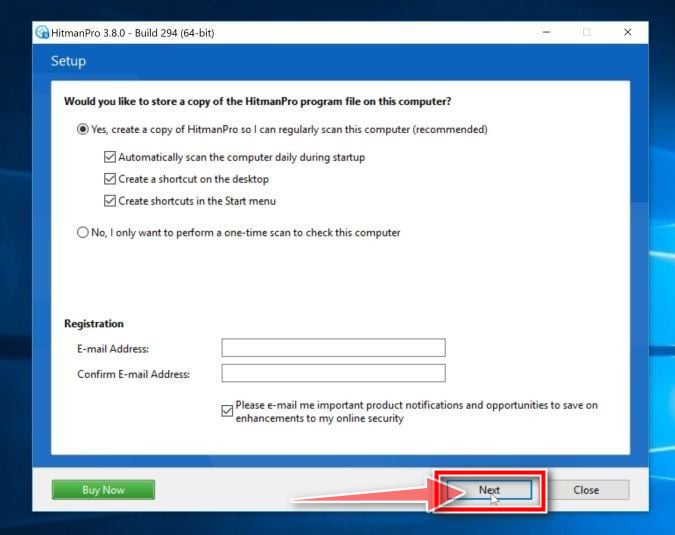
Install HitmanPro.
When HitmanPro has finished downloading, double-click on “hitmanpro.exe” (for 32-bit versions of Windows) or “hitmanpro_x64.exe” (for 64-bit versions of Windows) to install this program on your PC. In most cases, downloaded files are saved to the Downloads folder.
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation. -
Follow the on-screen prompts.
When HitmanPro starts you will be presented with the start screen as shown below. Click on the “Next” button to perform a system scan.
-
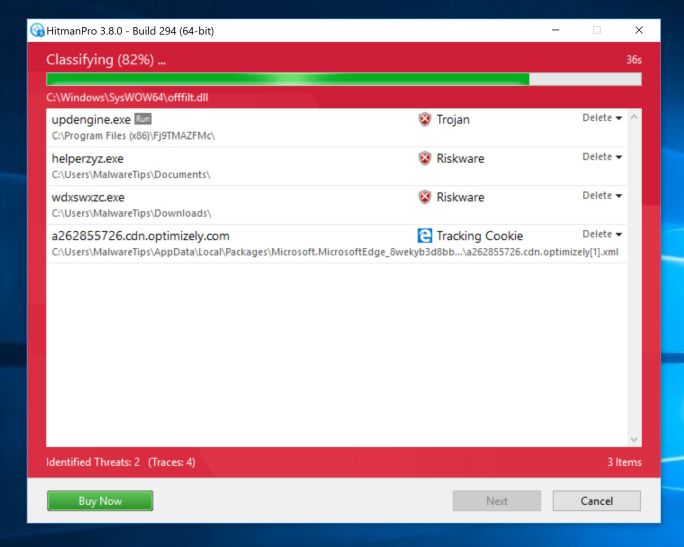
Wait for the HitmanPro scan to complete.
HitmanPro will now begin to scan your computer for malicious programs. This process will take a few minutes.
-
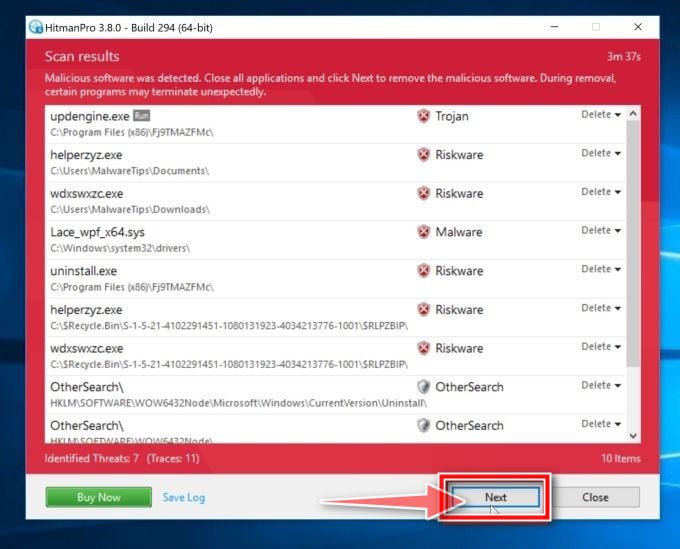
Click on “Next”.
When HitmanPro has finished the scan, it will display a list of all the malware that the program has found. Click on the “Next” button to remove the malicious programs.
-
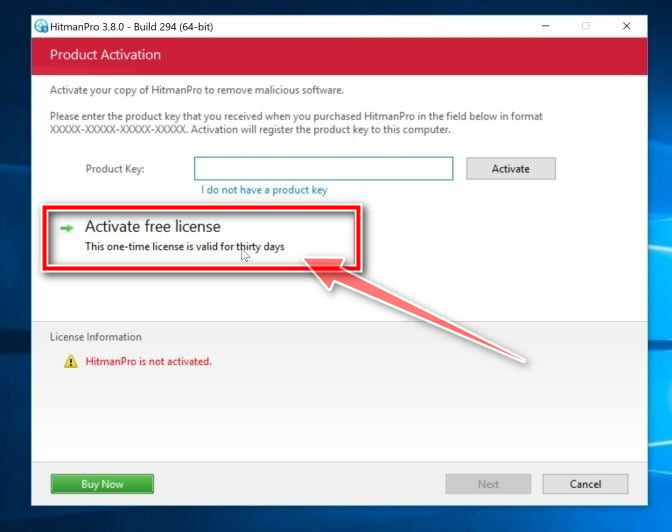
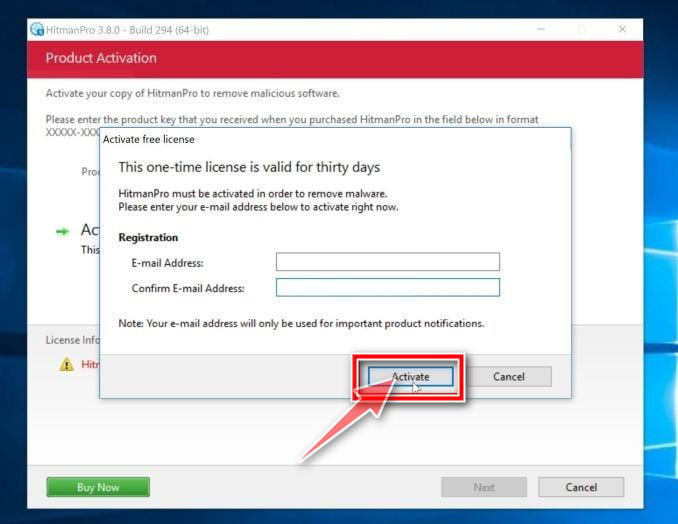
Click on “Activate free license”.
Click on the “Activate free license” button to begin the free 30 days trial and remove all the malicious files from your PC.
When the process is complete, you can close HitmanPro and continue with the rest of the instructions.
STEP 4: Double-check for malicious programs with Zemana AntiMalware Free
Zemana AntiMalware is a free popular on-demand antivirus scanner which can detect and remove malware that even the most well-known anti-virus and anti-malware applications fail to find.
While the Malwarebytes and HitmanPro scans are more than enough, we’re recommending Zemana AntiMalware to users who still have malware related issues or just want make sure their PC is 100% clean.
-
Download Zemana AntiMalware.
You can download Zemana AntiMalware Free by clicking the link below.
ZEMANA ANTIMALWARE DOWNLOAD LINK
(The above link will open a new web page from where you can download Zemana AntiMalware) -
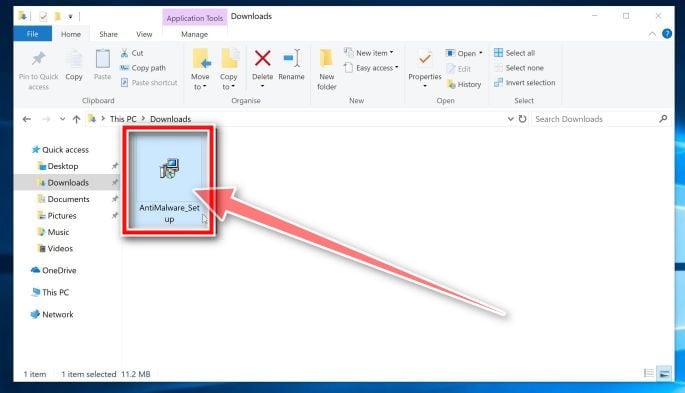
Double-click on the setup file.
Double-click on the file named “Zemana.AntiMalware.Setup.exe” to start the installation of Zemana AntiMalware. In most cases, downloaded files are saved to the Downloads folder.
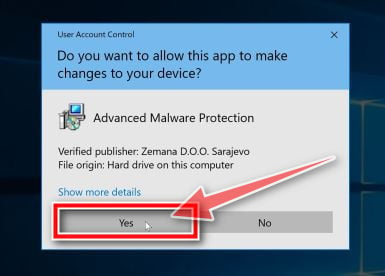
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
-
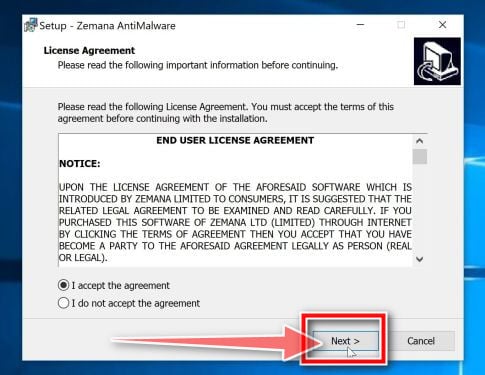
Install Zemana AntiMalware Free.
Click on the “Next” button to install Zemana AntiMalware on your PC. Follow the on-screen prompts to complete the install process.
-
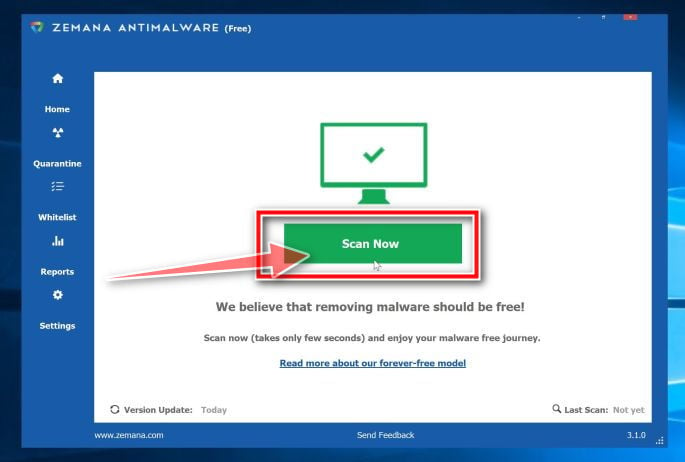
Click on “Scan Now”.
When Zemana AntiMalware will start, click on the “Scan Now” button to perform a system scan.
-
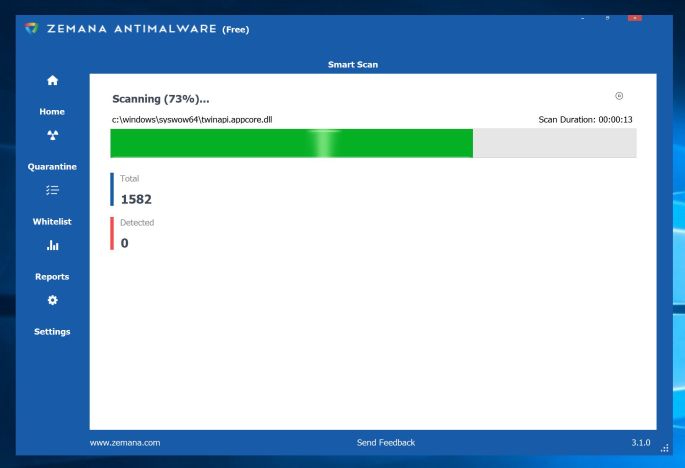
Wait for the Zemana AntiMalware scan to complete.
Zemana AntiMalware will now scan your PC for malicious files. This process can take a few minutes.
-
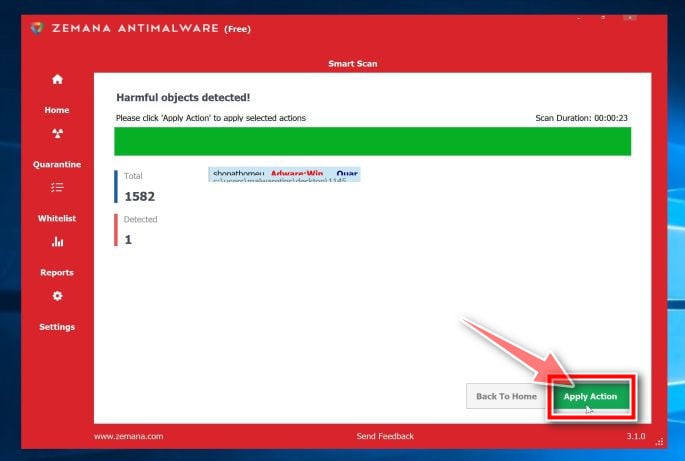
Click on “Apply Action”.
When Zemana AntiMalware has finished it will display a list of all the malware that the program found. Click on the “Apply Action” button to remove the malicious files from your computer.
-
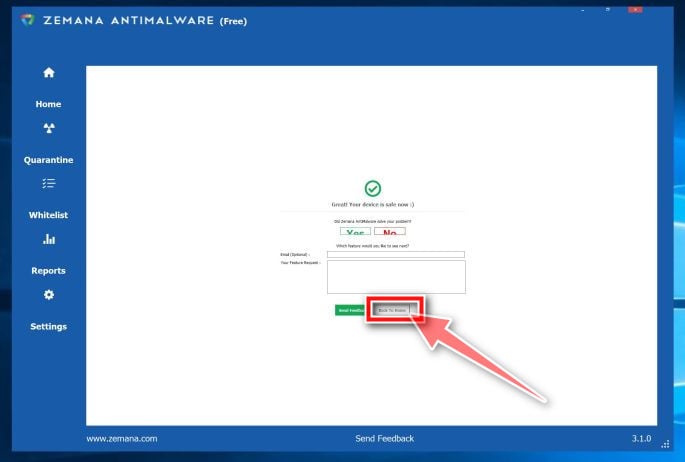
Restart your PC.
When the malware removal process is complete, Zemana AntiMalware may need to restart your computer. Click on the “Reboot” button to reset your PC.
Your computer should now be free of the Rabbit Ransomware. If you are still experiencing problems while trying to remove the Rabbit Ransomware from your PC, please do one of the following:
- Run a system scan with Emsisoft Emergency Kit
- Ask for help in our Malware Removal Assistance for Windows forum.