If you’re seeing a “The publisher has been blocked from running software” error when attempting to launch or install a security program, then you are most likely infected with a Trojan Horse (CertLock Trojan).
This Trojan is bundled with other free software that you download off of the Internet. Unfortunately, some free downloads do not adequately disclose that other software will also be installed and you may find that you have installed adware without your knowledge.
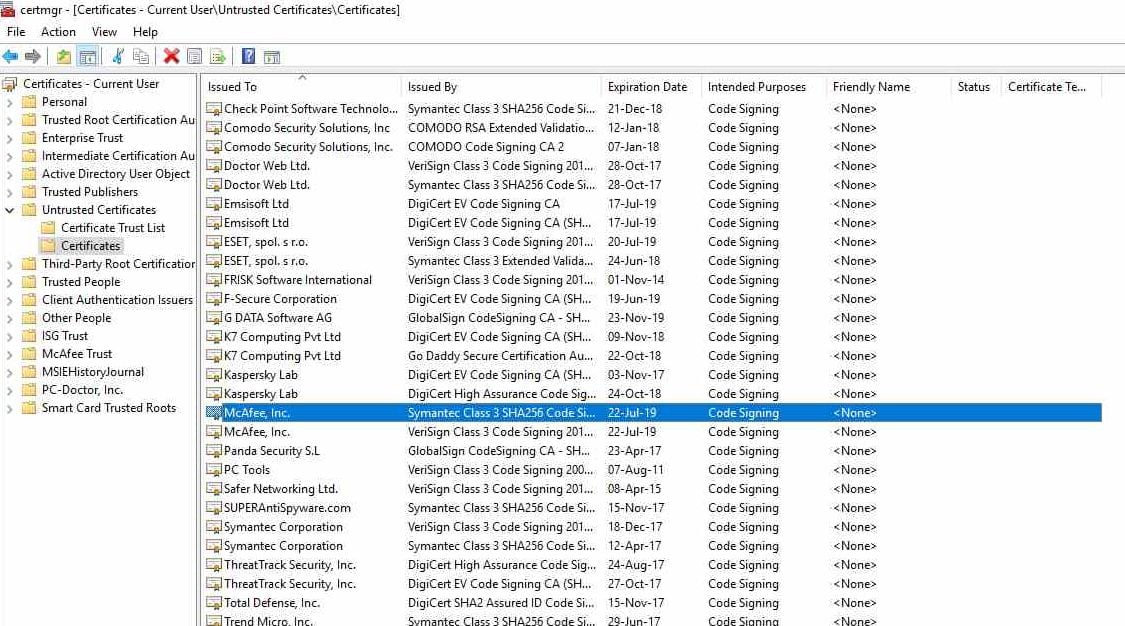
When installed, this Trojan will block users from running most antivirus programs by adding the security vendor’s certificates to a specific Windows registry key (HKLM\SOFTWARE\Microsoft\SystemCertificates\Disallowed\Certificates\).
Any software with certificates registered under the above key is not recognized as a trusted publisher and this prevents its installation or execution in the infected machine.
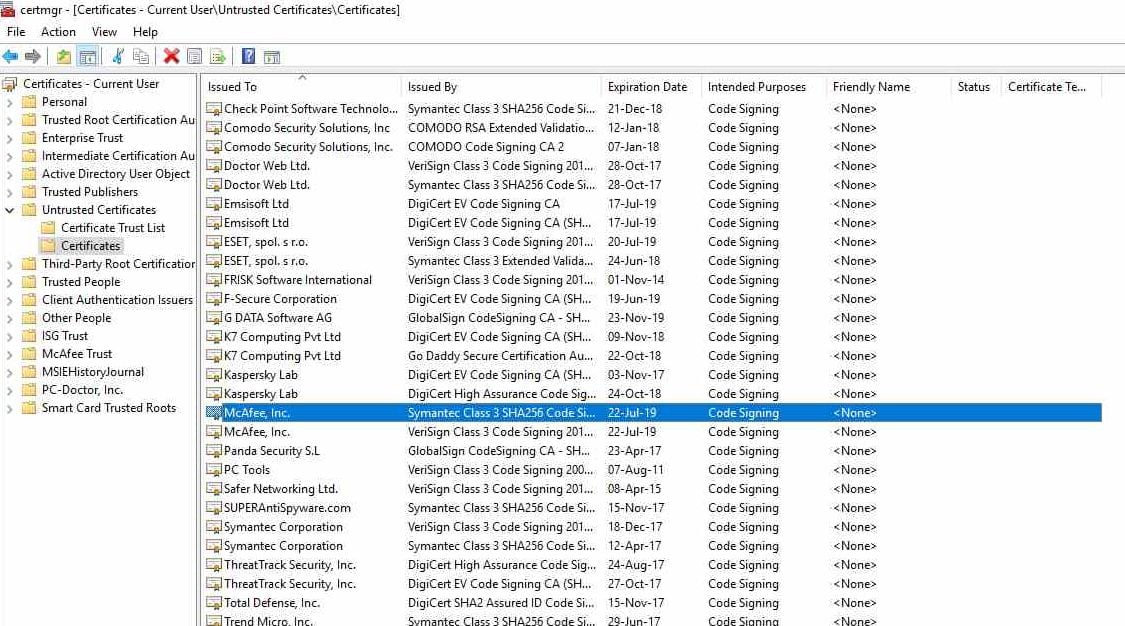
These are the antivirus programs that are currently blocked by this Trojan: AVAST, AVG, Adaware, Avira, Bitdefender, BullGuard, CURIOLAB, Check Point Software, Comodo, Doctor Web Ltd, ESET, Emsisoft, F-Secure, FRISK, GData, K7, Kaspersky Lab, Malwarebytes, McAfee, PC Tools, Panda, SUPERAntiSpyware, Safer Networking, Symantec, ThreatTrack Security, Total Defense, Trend Micro, and Webroot.
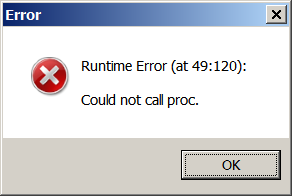
As an example, when a PC is infected with this Trojan, when attempting to start Malwarebytes you will receive an error that says: Unable to connect the Service or Runtime Error (at 49:120): Could not call proc.
Fix “The publisher has been blocked from running software” Error (Guide)
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
- STEP 1: Remove the security vendor’s certificates from the Disallowed Certificates
- STEP 2: Use Zemana AntiMalware Portable to remove “The publisher has been blocked from running software” Malware
- STEP 3: Use Malwarebytes to Scan for Malware and Unwanted Programs
- STEP 4: Double-check for malicious programs with HitmanPro
STEP 1: Remove the security vendor’s certificates from the Disallowed Certificates
To remove the security vendor’s certificates from the Disallowed Certificates we have the below options:
OPTION 1: Use AVCertClean to remove Disallowed Certificates
AVCertClean is a free tool that will scan and remove from your PC the Disallowed Certificates that were added by this Trojan.
- You can download AVCertClean from the below link.
AVCERTCLEAN DOWNLOAD LINK (This link will start the download of “AVCertClean” on your computer) - When AVCertClean has finished downloading, please double-click on the AVCertClean icon to perform a scan with this program.
If Windows prompts you as to whether or not you wish to run AVCertClean, please allow it to run.
- AVCertClean will automatically scan the Windows Registry for incorrectly disallowed certificates, and will remove them from the Disallowed key so that they are able to be used again.
OPTION 2: Manually remove the Disallowed Certificates that were installed by malware
- Press Windows Key + R to bring up the run dialog
- In the dialog window, type certmgr.msc and click Ok
- In the window that comes up, on the left side, double click Untrusted Certificates so you can see the folders beneath it
- If a Certificate folder exists, click on it.
- Delete any certificates on the right side of the window that have the following names: AVAST, AVG, Adaware, Avira, Bitdefender, BullGuard, CURIOLAB, Check Point Software, Comodo, Doctor Web Ltd, ESET, Emsisoft, F-Secure, FRISK, GData, K7, Kaspersky Lab, Malwarebytes, McAfee, PC Tools, Panda, SUPERAntiSpyware, Safer Networking, Symantec, ThreatTrack Security, Total Defense, Trend Micro, and Webroot.
- Restart your PC
STEP 2: Use Zemana AntiMalware Portable to remove “The publisher has been blocked from running software” Malware
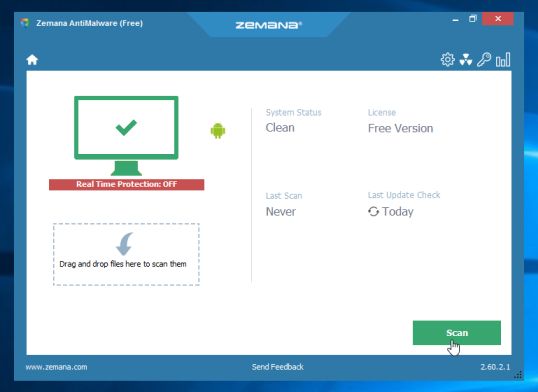
Zemana AntiMalware Portable is a free utility that will scan your computer for the CertLock Trojan and other malicious programs.
- You can download Zemana AntiMalware Portable from the below link:
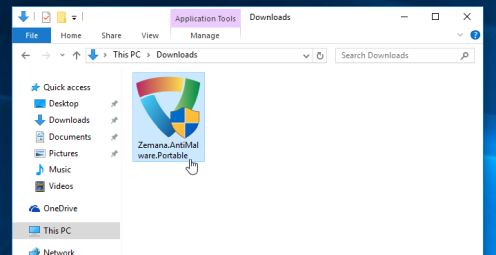
ZEMANA ANTIMALWARE PORTABLE DOWNLOAD LINK (This link will open a new web page from where you can download “Zemana AntiMalware Portable”) - Double-click on the file named “Zemana.AntiMalware.Portable” to perform a system scan with Zemana AntiMalware Free.
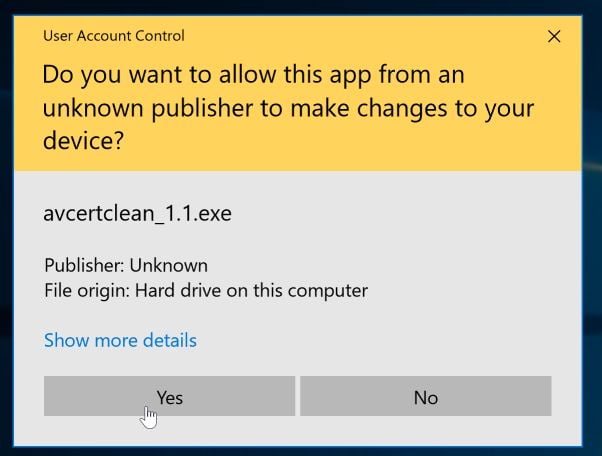
You may be presented with a User Account Control dialog asking you if you want to run this program. If this happens, you should click “Yes” to allow Zemana AntiMalware to run.
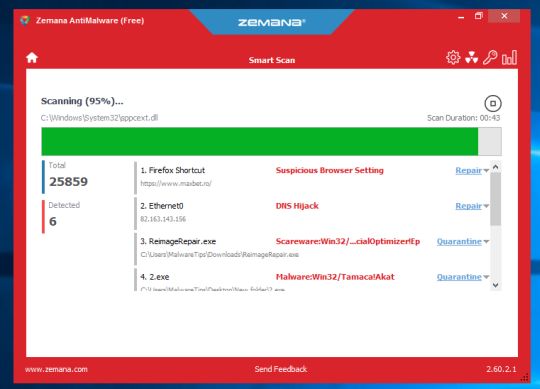
In some cases, this Trojan may block you from installing Zemana, if that’s the case then you will need to right click on “Zemana.AntiMalware.Portable” and rename it to “eXplorer.exe” or “iexplorer.exe”. - When Zemana AntiMalware will start, click on the “Scan” button to perform a system scan.
- Zemana AntiMalware will now scan your computer for malicious programs. This process can take up to 10 minutes.
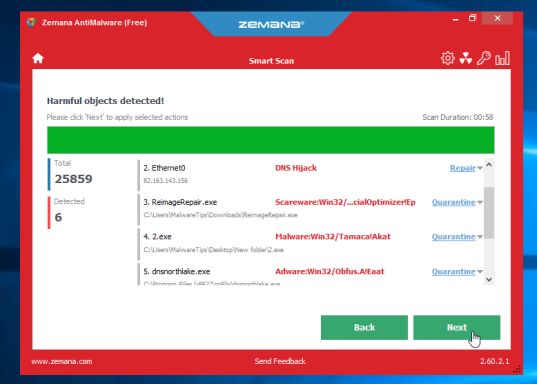
- When Zemana has finished finished scanning it will show a screen that displays any malware that has been detected. To remove all the malicious files, click on the “Next” button.
Zemana AntiMalware will now start to remove all the malicious programs from your computer. When the process is complete, you can close Zemana AntiMalware and continue with the rest of the instructions.
STEP 3: Use Malwarebytes to Scan for Malware and Unwanted Programs
Malwarebytes is a powerful on-demand scanner which should remove the CertLock Trojan and other unwanted programs from Windows. It is important to note that Malwarebytes will run alongside antivirus software without conflicts.
- You can download download Malwarebytes from the below link.
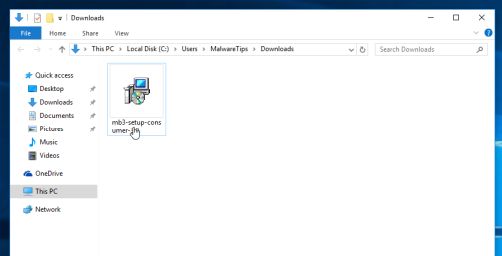
MALWAREBYTES DOWNLOAD LINK (This link open a new page from where you can download “Malwarebytes”) - When Malwarebytes has finished downloading, double-click on the “mb3-setup-consumer” file to install Malwarebytes on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- When the Malwarebytes installation begins, you will see the Malwarebytes Setup Wizard which will guide you through the installation process.
To install Malwarebytes on your machine, keep following the prompts by clicking the “Next” button.
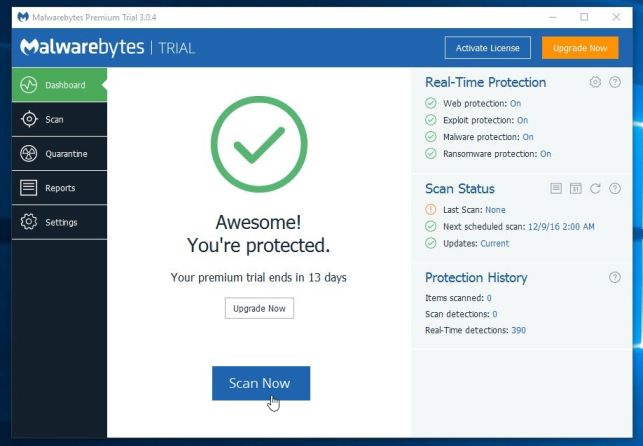
- Once installed, Malwarebytes will automatically start and update the antivirus database. To start a system scan you can click on the “Scan Now” button.
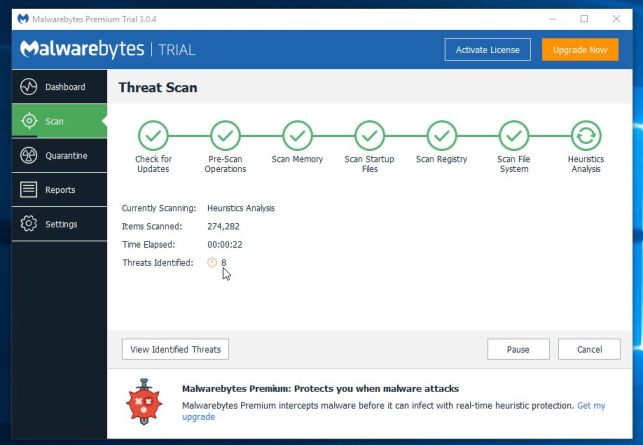
- Malwarebytes will now start scanning your computer for malicious programs.
This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
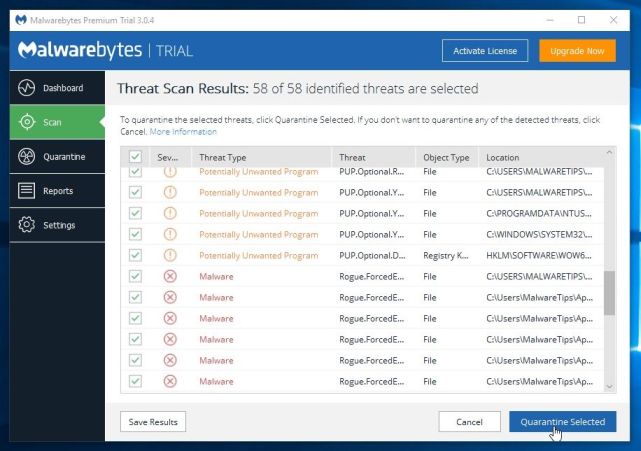
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected.
To remove the malicious programs that Malwarebytes has found, click on the “Quarantine Selected” button.
- Malwarebytes will now quarantine all the malicious files and registry keys that it has found.
To complete the malware removal process, Malwarebytes may ask you to restart your computer.
When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
STEP 4: Double-check for malicious programs with HitmanPro
HitmanPro can find and remove malware, adware, bots, and other threats that even the best antivirus suite can oftentimes miss. HitmanPro is designed to run alongside your antivirus suite, firewall, and other security tools.
- You can download HitmanPro from the below link:
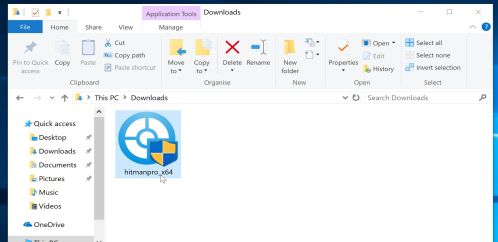
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - When HitmanPro has finished downloading, double-click on the “hitmanpro” file to install this program on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- When the program starts you will be presented with the start screen as shown below. Now click on the Next button to continue with the scan process.
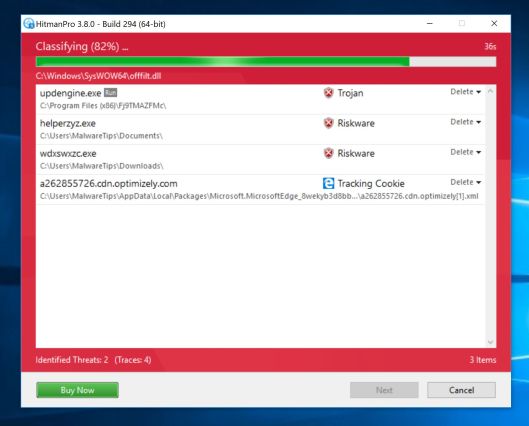
- HitmanPro will now begin to scan your computer for malware.
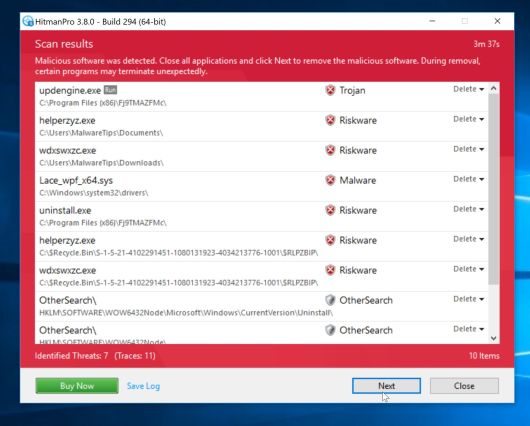
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
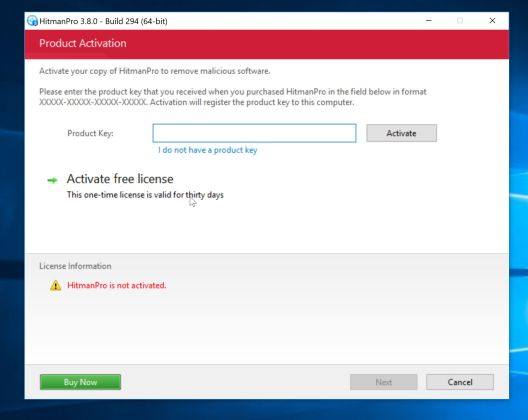
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
When the process is complete, you can close HitmanPro and continue with the rest of the instructions.