TRAMP is a malicious program that encrypts the personal documents found on the victim’s computer with the “.[clevercrypt@aol.com].TRAMP” extension, then displays a message which offers to decrypt the data if payment in Bitcoin is made. The instructions are placed on the victim’s desktop as the clevercrypt@aol.com pop-up window and in the “FILES ENCRYPTED.txt” text file.
![How to remove TRAMP ransomware (Virus Removal Guide) 2 Image: [clevercrypt@aol.com].TRAMP ransomware](https://malwaretips.com/blogs/wp-content/uploads/2020/04/clevercrypt@aol.com_.TRAMP-ransomware.jpg)
What is the TRAMP ransomware?
TRAMP is a file-encrypting ransomware infection that restricts access to data (documents, images, videos) by encrypting files with the “.[clevercrypt@aol.com].TRAMP” extension. It then attempts to extort money from victims by asking for “ransom”, in the form of Bitcoin cryptocurrency, in exchange for access to data.
When you are first infected with the TRAMP ransomware it will scan your computer for images, videos, and important productivity documents and files such as .doc, .docx, .xls, .pdf. When these files are detected, the ransomware will encrypt them and change their extension to “.[clevercrypt@aol.com].TRAMP”, so that you are no longer able to be open them.
Once the TRAMP ransomware has encrypted the files on your computer, it will display the “FILES ENCRYPTED.txt” text file that contains the ransom note and instructions on how to contact the authors of this ransomware. The victims of this ransomware will be asked to contact the cyber criminals via the clevercrypt@aol.com email address.
This is the ransom note that the TRAMP ransomware will show to its victims:
YOUR FILES ARE ENCRYPTED
Don’t worry,you can return all your files!
If you want to restore them, follow this link email: De_cryption@tuta.io
If you have not been answered via the link within 12 hours, write to us by e-mail:
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
If your computer is infected with this ransomware, we recommend that you contact the following government fraud and scam sites to report this attack:
- In the United States, go to the On Guard Online website.
- In Australia, go to the SCAMwatch website.
- In Canada, go to the Canadian Anti-Fraud Centre.
- In France, go to the Agence nationale de la sécurité des systèmes d’information
- In Germany, go to the Bundesamt für Sicherheit in der Informationstechnik website.
- In Ireland, go to the An Garda Síochána website.
- In New Zealand, go to the Consumer Affairs Scams website.
- In the United Kingdom, go to the Action Fraud website.
- If your country or region isn’t listed above, we recommend that you contact your country or region’s federal police or communications authority.
Unfortunately, it is not currently possible to decrypt the files encrypted by the TRAMP ransomware. It may, though, be possible in the future if the decryption keys are recovered from the cybercriminals’ servers. Therefore, if you do not plan on paying the ransom, it is advised that you make an image of the encrypted drives so that you can possibly decrypt them in the future.
Here is a short summary for the TRAMP ransomware:
- Ransomware family: Dharma ransomware
- Extensions: .[clevercrypt@aol.com].TRAMP
- Ransomware note: FILES ENCRYPTED.txt
- Ransom: From $500 (in Bitcoins)
- Contact: clevercrypt@aol.com
- Symptoms: The images, videos, and other documents have the “.[clevercrypt@aol.com].TRAMP” extension and cannot be opened by any programs
How did the TRAMP ransomware get on my computer?
The TRAMP ransomware is distributed via spam email containing infected attachments or by exploiting vulnerabilities in the operating system and installed programs.
Here’s how the TRAMP ransomware might get on your computer:
- Cyber-criminals spam out an email, with forged header information, tricking you into believing that it is from a shipping company like DHL or FedEx. The email tells you that they tried to deliver a package to you, but failed for some reason. Sometimes the emails claim to be notifications of a shipment you have made. Either way, you can’t resist being curious as to what the email is referring to – and open the attached file (or click on a link inside the email). And with that, your computer is infected with the TRAMP ransomware.
- The TRAMP ransomware was also observed attacking victims by exploiting vulnerabilities in the program installed on the computer or the operating system itself. Commonly exploited software includes the operating system itself, browsers, Microsoft Office, and third-party applications.
Remove the TRAMP ransomware and recover the files
It’s recommended to create a backup image of the encrypted drives before proceeding with the below malware removal instructions.
This malware removal guide may appear overwhelming due to the number of steps and numerous programs that are being used. We have only written it this way to provide clear, detailed, and easy to understand instructions that anyone can use to remove malware for free.
Please perform all the steps in the correct order. If you have any questions or doubts at any point, stop and ask for our assistance.
- STEP 1: Use Malwarebytes Free to remove TRAMP ransomware
- STEP 2: Use HitmanPro to scan for Trojans and other malware
- STEP 3: Double-check for malicious programs with Emsisoft Emergency Kit
- STEP 4: Restoring the files encrypted by the TRAMP ransomware
STEP 1: Use Malwarebytes Free to remove TRAMP ransomware
Malwarebytes Free is one of the most popular and most used anti-malware software for Windows, and for good reasons. It is able to destroy many types of malware that other software tends to miss, without costing you absolutely nothing. When it comes to cleaning up an infected device, Malwarebytes has always been free and we recommend it as an essential tool in the fight against malware.
It is important to note that Malwarebytes Free will run alongside antivirus software without conflicts.
Download Malwarebytes Free.
You can download Malwarebytes by clicking the link below.
 MALWAREBYTES DOWNLOAD LINK
MALWAREBYTES DOWNLOAD LINK
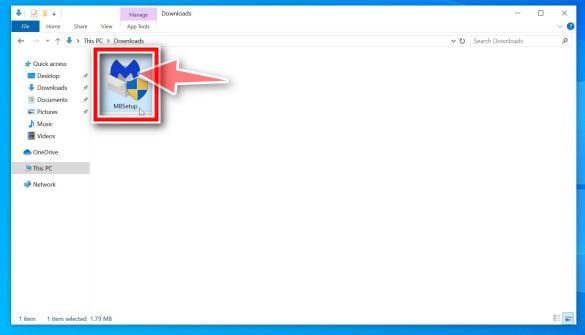
(The above link will open a new page from where you can download Malwarebytes)Double-click on the Malwarebytes setup file.
When Malwarebytes has finished downloading, double-click on the MBSetup file to install Malwarebytes on your computer. In most cases, downloaded files are saved to the Downloads folder.
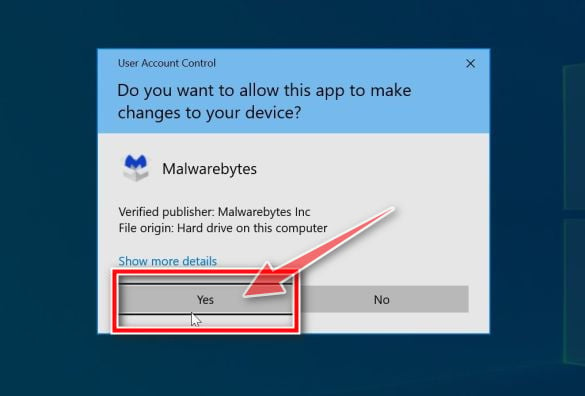
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the Malwarebytes installation.
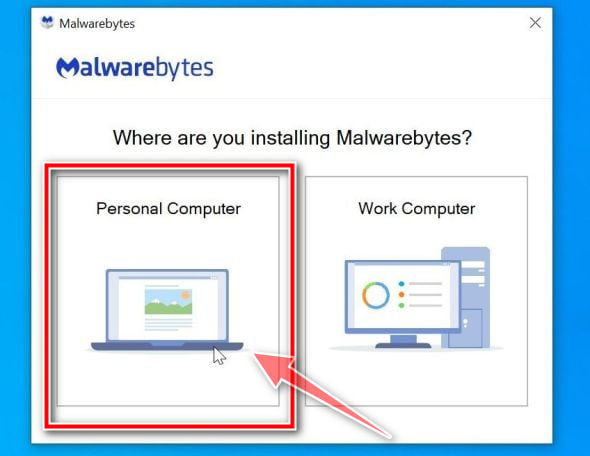
Follow the on-screen prompts to install Malwarebytes.
When the Malwarebytes installation begins, you will see the Malwarebytes setup wizard which will guide you through the installation process. The Malwarebytes installer will first ask you on what type of computer are you installing this program, click either Personal Computer or Work Computer.
On the next screen, click “Install” to install Malwarebytes on your computer.
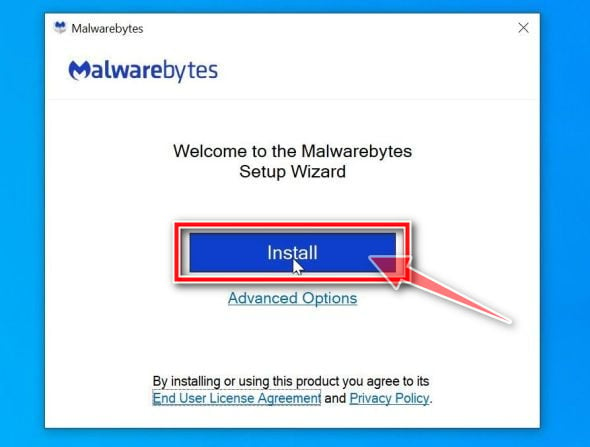
When your Malwarebytes installation completes, the program opens to the Welcome to Malwarebytes screen. Click the “Get started” button.
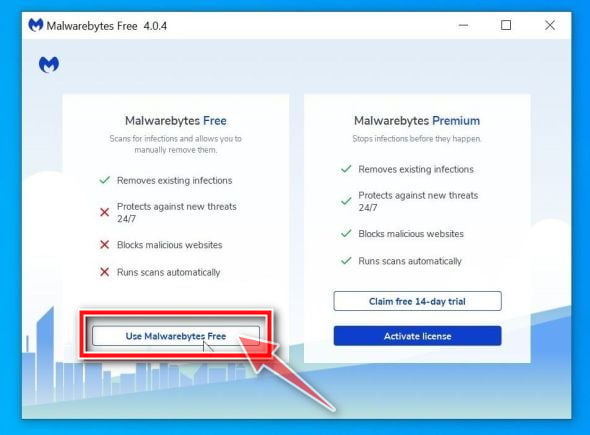
Select “Use Malwarebytes Free”.
After installing Malwarebytes, you’ll be prompted to select between the Free and the Premium version. The Malwarebytes Premium edition includes preventative tools like real-time scanning and ransomware protection, however, we will use the Free version to clean up the computer.
Click on “Use Malwarebytes Free“.
Click on “Scan”.
To scan your computer with Malwarebytes, click on the “Scan” button. Malwarebytes will automatically update the antivirus database and start scanning your computer for malware.
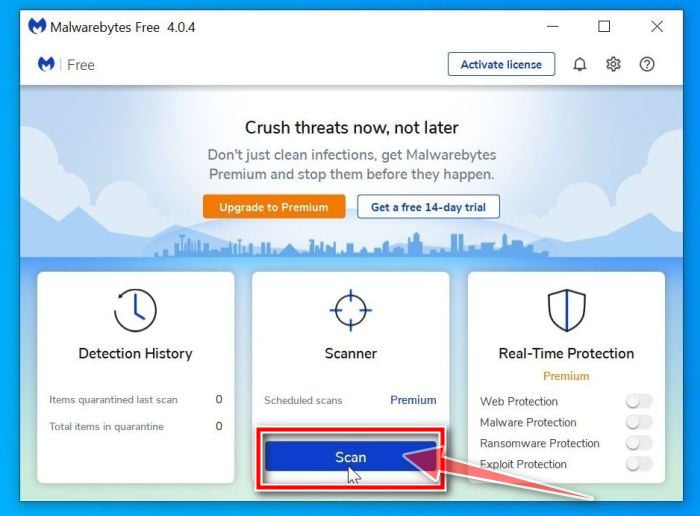
Wait for the Malwarebytes scan to complete.
Malwarebytes will scan your computer for adware and other malicious programs. This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
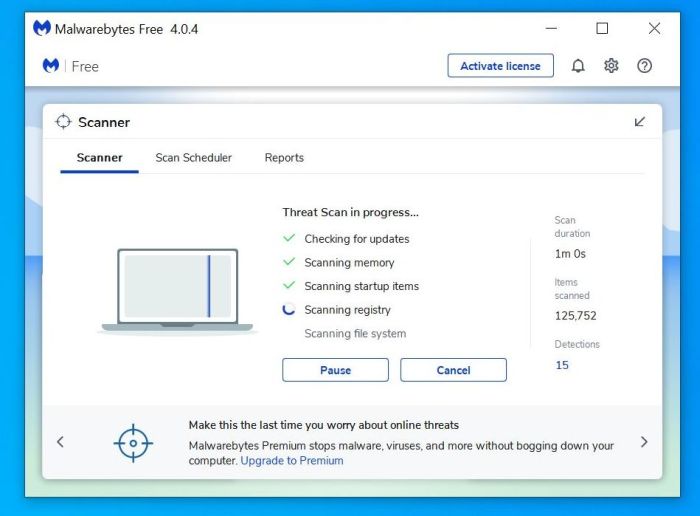
Click on “Quarantine”.
When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected. To remove the malicious programs that Malwarebytes has found, click on the “Quarantine” button.
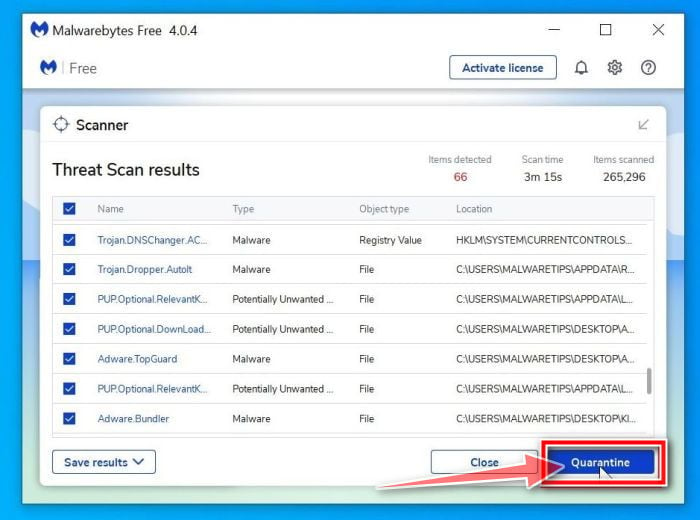
Restart computer.
Malwarebytes will now remove all the malicious files and registry keys that it has found. To complete the malware removal process, Malwarebytes may ask you to restart your computer.
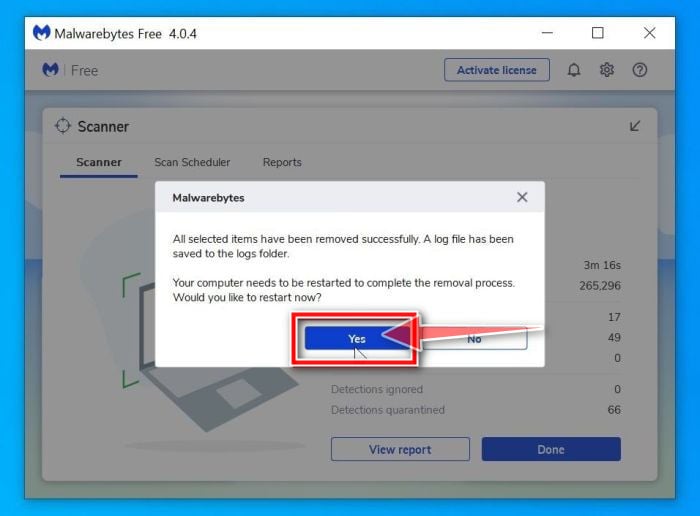
When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
STEP 2: Use HitmanPro to scan for Trojans and other malware
HitmanPro is a second opinion scanner that takes a unique cloud-based approach to malware scanning. HitmanPro scans the behavior of active files and also files in locations where malware normally resides for suspicious activity. If it finds a suspicious file that’s not already known, HitmanPro sends it to their clouds to be scanned by two of the best antivirus engines today, which are Bitdefender and Kaspersky.
Although HitmanPro is shareware and costs $24.95 for 1 year on 1 PC, there is actually no limit in scanning. The limitation only kicks in when there is a need to remove or quarantine detected malware by HitmanPro on your system and by then, you can activate the one time 30-days trial to enable the clean up.
Download HitmanPro.
You can download HitmanPro by clicking the link below.
 HITMANPRO DOWNLOAD LINK
HITMANPRO DOWNLOAD LINK
(The above link will open a new web page from where you can download HitmanPro)Install HitmanPro.
When HitmanPro has finished downloading, double-click on “hitmanpro.exe” (for 32-bit versions of Windows) or “hitmanpro_x64.exe” (for 64-bit versions of Windows) to install this program on your PC. In most cases, downloaded files are saved to the Downloads folder.
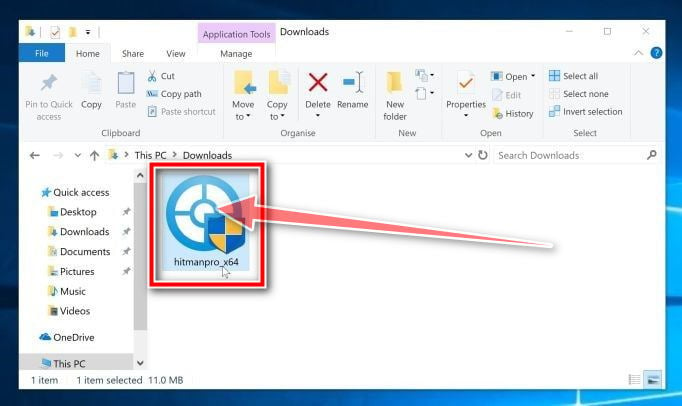
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation.

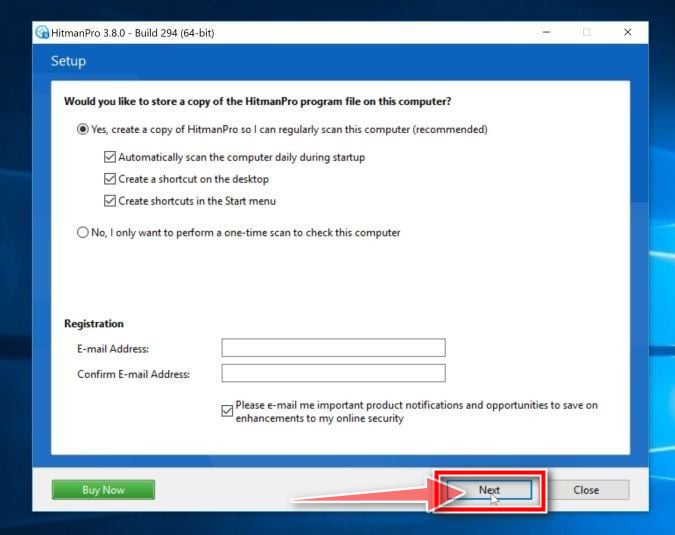
Follow the on-screen prompts.
When HitmanPro starts you will be presented with the start screen as shown below. Click on the “Next” button to perform a system scan.

Wait for the HitmanPro scan to complete.
HitmanPro will now begin to scan your computer for malicious programs. This process will take a few minutes.
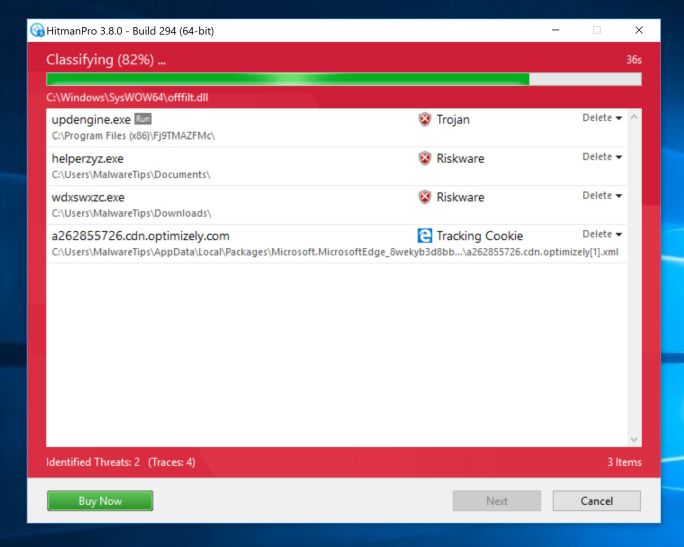
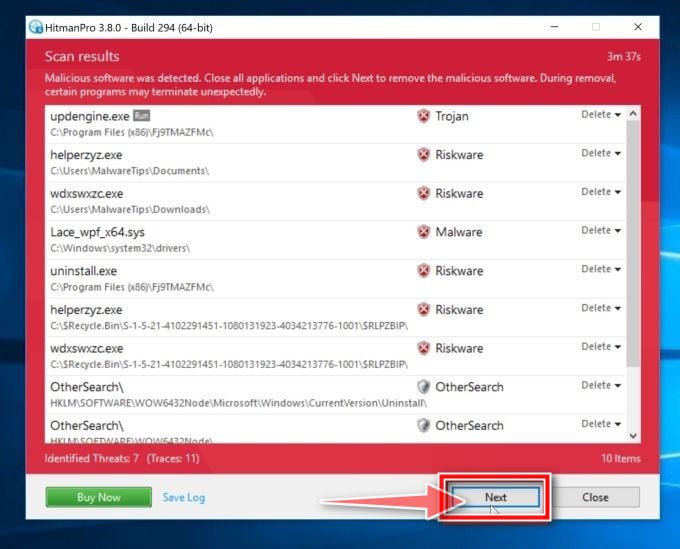
Click on “Next”.
When HitmanPro has finished the scan, it will display a list of all the malware that the program has found. Click on the “Next” button to remove the malicious programs.
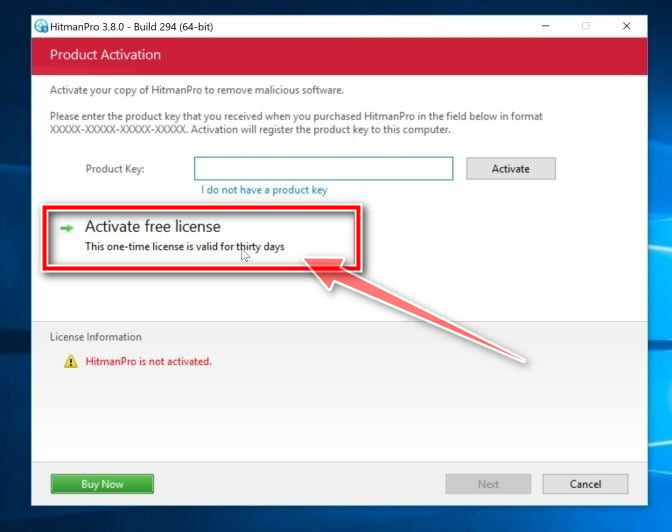
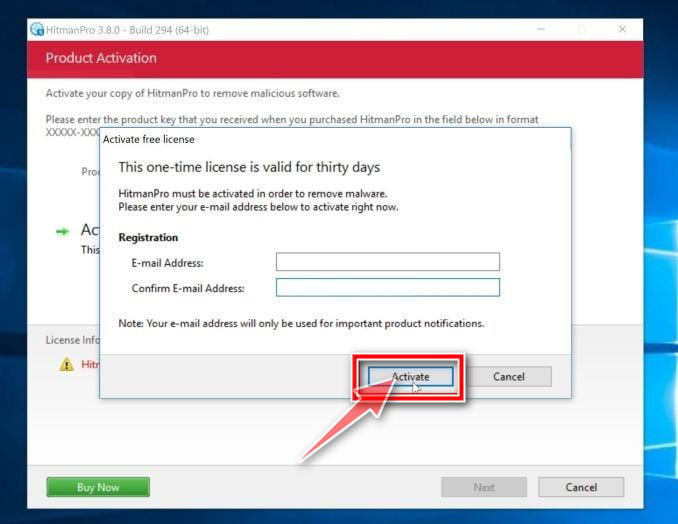
Click on “Activate free license”.
Click on the “Activate free license” button to begin the free 30 days trial and remove all the malicious files from your PC.
When the process is complete, you can close HitmanPro and continue with the rest of the instructions.
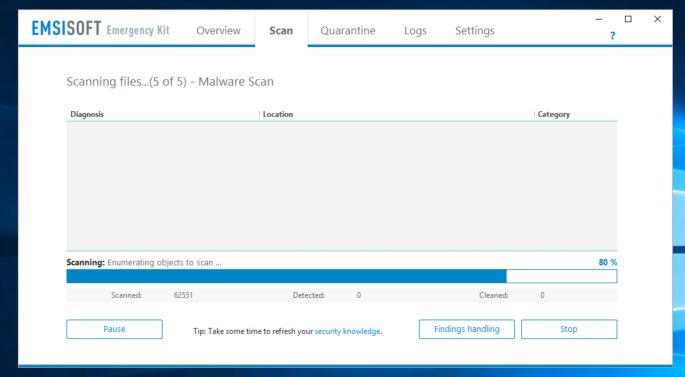
STEP 3: Double-check for malicious programs with Emsisoft Emergency Kit
Emsisoft Emergency Kit is a free second opinion scanner that can be used without installation to scan and clean infected computers. Emsisoft scans the behavior of active files and also files in locations where malware normally resides for suspicious activity.
While the Malwarebytes and HitmanPro scans are more than enough, we’re recommending Emsisoft Emergency Kit to users who still have malware related issues or just want to make sure their computer is 100% clean.
Download Emsisoft Emergency Kit.
You can download Emsisoft Emergency Kit by clicking the link below.
 EMSISOFT EMERGENCY KIT DOWNLOAD LINK
EMSISOFT EMERGENCY KIT DOWNLOAD LINK
(The above link will open a new web page from where you can download Emsisoft Emergency Kit)Install Emsisoft Emergency Kit.
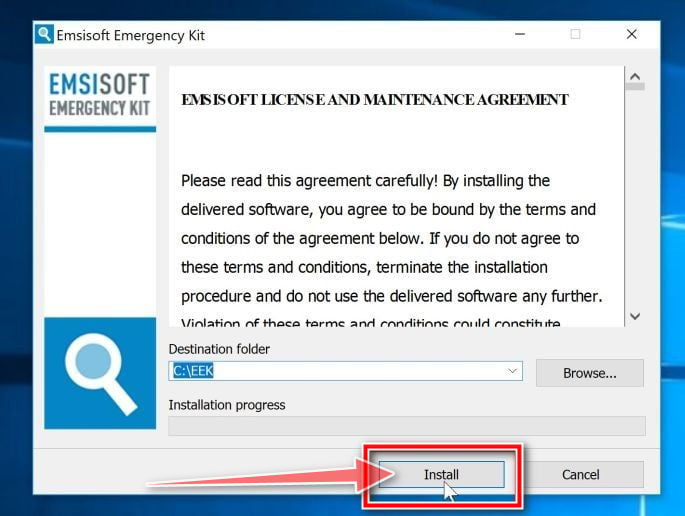
Double-click on the EmsisoftEmergencyKit setup file to start the installation process, then click on the “Install” button.
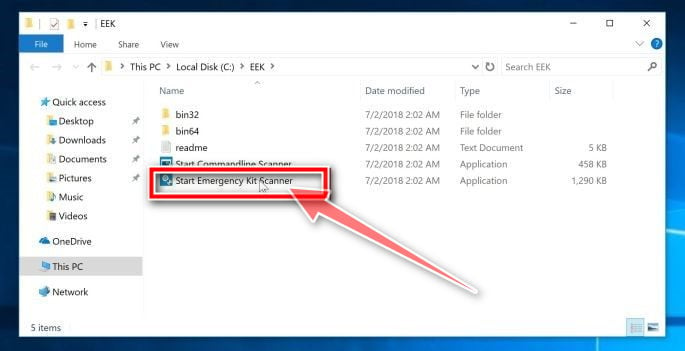
Start Emsisoft Emergency Kit.
On your desktop the “EEK” folder (C:\EEK) should now be open. To start Emsisoft, click on the “Start Emsisoft Emergency Kit” file to open this program.
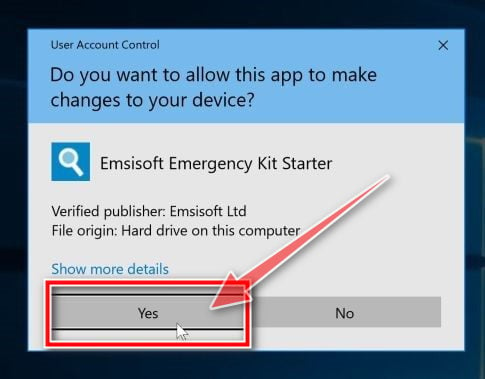
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
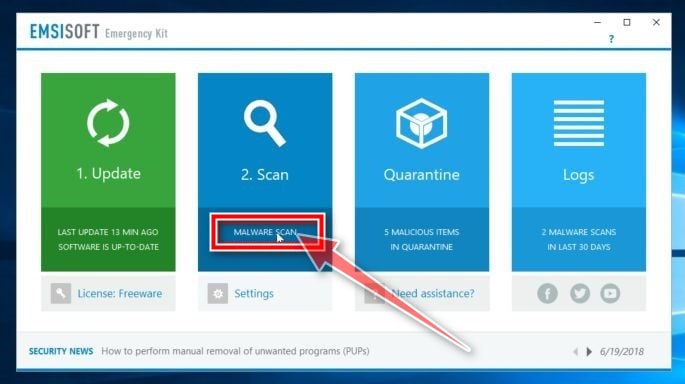
Click on “Malware Scan”.
Emsisoft Emergency Kit will start and it will ask you for permission to update itself. Once the update process is complete, click on the “Scan” tab, and perform a “Malware Scan“.
Emsisoft Emergency Kit will now scan your PC for malicious files. This process can take a few minutes.
Click on “Quarantine selected”.
When the Emsisoft scan has finished, you will be presented with a screen reporting which malicious files were detected on your computer. To remove the malicious programs, click on the “Quarantine selected“.
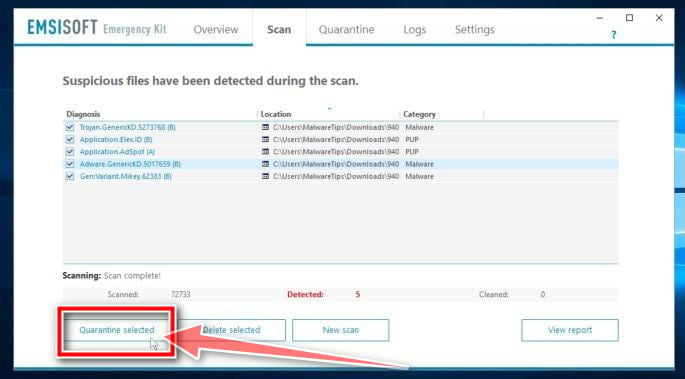
When the malware removal process is complete, Emsisoft Emergency Kit may need to restart your computer. Click on the “Restart” button to restart your computer.
When the process is complete, you can close Emsisoft and continue with the rest of the instructions.
STEP 4: Restoring the files encrypted by the TRAMP ransomware
Unfortunately, it’s not possible to recover the files encrypted by the TRAMP ransomware because the private key which is needed to unlock the encrypted files is only available through the cybercriminals. However, below we’ve listed two options you can use to try and recover your files.
Option 1: Search for a TRAMP ransomware decryption tool
At the time of writing this article, there was no decryption tool available for the TRAMP ransomware. However, the cybersecurity community is constantly working to create ransomware decryption tools, so you can try to search these sites for updates:
- https://id-ransomware.malwarehunterteam.com/
- https://decrypter.emsisoft.com/
- https://noransom.kaspersky.com/
- https://www.avast.com/ransomware-decryption-tools
Option 2: Try to restore your files with Free File Recovery Software
In very few cases, it may be possible to recover previous versions of the encrypted files using recovery software used to obtain “shadow copies” of files. We’ve listed two recovery software below, however, keep in mind that most likely these programs won’t be able to recover your files.
Here’s how to try to recover your files with ShadowExplorer:
The TRAMP ransomware will attempt to delete all shadow copies when you first start any executable on your computer after becoming infected. Thankfully, the infection is not always able to remove the shadow copies, so you should continue to try restoring your files using this method.
- You can download ShadowExplorer from the below link:SHADOW EXPLORER DOWNLOAD LINK (This link will open a new web page from where you can download “ShadowExplorer”)
- Once you have downloaded and installed ShadowExplorer, you can follow the below video guide on how to restore your files while using this program.
Another option would be to use free recovery software, like Recuva Free. Here’s how to try to recover your files with Recuva Free:
- You can download Recuva Free from the below link:
 RECUVA FREE DOWNLOAD LINK (This link will open a new web page from where you can download “Recuva Free”)
RECUVA FREE DOWNLOAD LINK (This link will open a new web page from where you can download “Recuva Free”) - Once you have downloaded and installed Recuva Free, you can follow the below video guide on how to restore your files while using this program.
Your computer should now be free of the TRAMP ransomware infection. If your current antivirus allowed this malicious program on your computer, you may want to consider purchasing the full-featured version of Malwarebytes Anti-Malware to protect against these types of threats in the future.
If you are still having problems with your computer after completing these instructions, then please follow one of the steps:
- Run a computer scan with ESET Online Scanner
- Ask for help in our Windows Malware Removal Help & Support forum.