VB:Trojan.VBA.Agent.TY is a heuristic detection designed to generically detect a Trojan Horse. Due to the generic nature of this threat, we are unable to provide specific information on what it does.
A typical behavior for Trojans like VB:Trojan.VBA.Agent.TY is one or all of the following:
- Download and install other malware.
- Use your computer for click fraud.
- Record your keystrokes and the sites you visit.
- Send information about your PC, including usernames and browsing history, to a remote malicious hacker.
- Give a remote malicious hacker access to your PC.
- Advertising banners are injected with the web pages that you are visiting.
- Random web page text is turned into hyperlinks.
- Browser popups appear which recommend fake updates or other software.
How to remove VB:Trojan.VBA.Agent.TY adware (Virus Removal Guide)
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
- STEP 1: Use Zemana AntiMalware Free to remove the VB:Trojan.VBA.Agent.TY
- STEP 2: Use Malwarebytes to scan for Malware and Unwanted Programs
- STEP 3: Double-check for malicious programs with HitmanPro
STEP 1: Use Zemana AntiMalware Free to remove the VB:Trojan.VBA.Agent.TY
Zemana AntiMalware is a free malware scanner which can detect malicious programs that your antivirus has failed to find.
- You can download Zemana AntiMalware Free from the below link:
ZEMANA ANTIMALWARE FREE DOWNLOAD LINK (This link open a new webpage from where you can download “Zemana AntiMalware Free”) - Double-click on the file named “Zemana.AntiMalware.Setup.exe” to start the installation of Zemana AntiMalware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- Click on the “Next” button, to install Zemana AntiMalware on your computer.
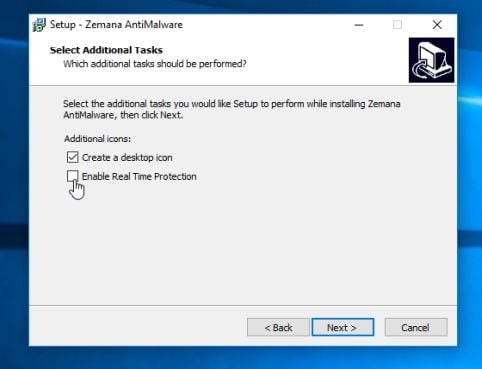
When you reach the “Select Additional Tasks” screen, you can opt-out the “Enable Real Time Protection” option, then click on the “Next” button.
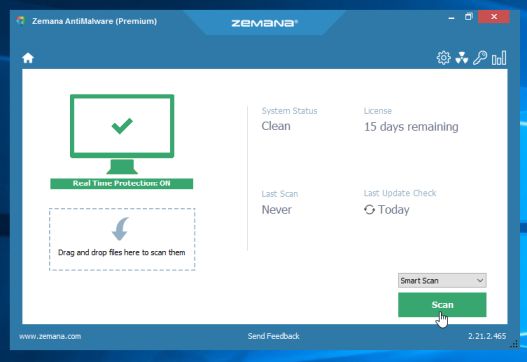
- When Zemana AntiMalware will start, click on the “Scan” button.
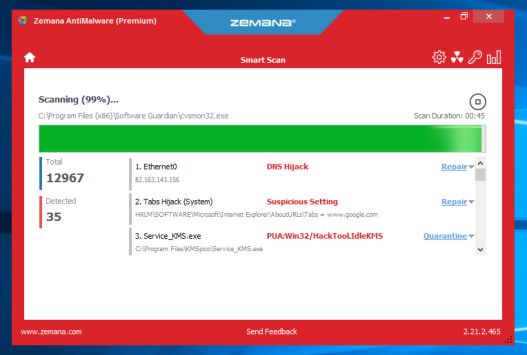
- Zemana AntiMalware will now scan computer for malicious files. This process can take up to 10 minutes.
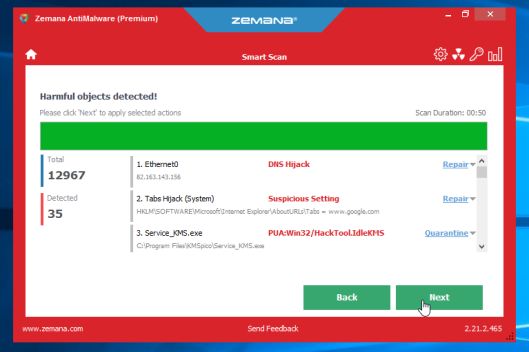
- When Zemana AntiMalware has finished it will display a list of all the malware that the program found. Click on the “Next” button, to remove the malicious files from your computer.
Zemana AntiMalware will now start to remove all the malicious programs from your computer. When the process is complete, you may need to restart your computer.
STEP 2: Use Malwarebytes to scan for Malware and Unwanted Programs
Malwarebytes is a powerful on-demand scanner which will scan your PC for malware and other unwanted programs that may have been installed without your knowledge. It is important to note that Malwarebytes will run alongside antivirus software without conflicts.
- You can download download Malwarebytes from the below link.
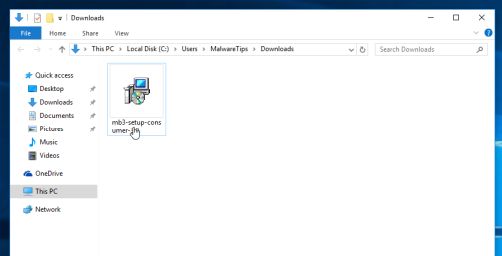
MALWAREBYTES DOWNLOAD LINK (This link open a new page from where you can download “Malwarebytes”) - When Malwarebytes has finished downloading, double-click on the “mb3-setup-consumer” file to install Malwarebytes on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
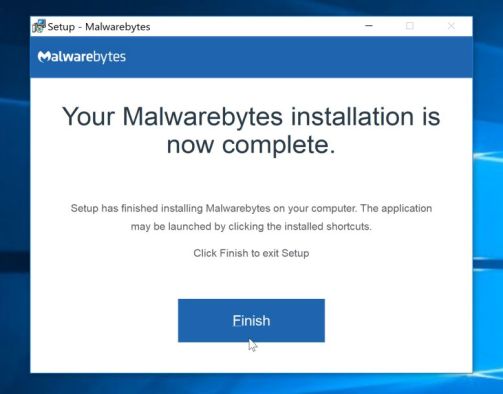
- When the Malwarebytes installation begins, you will see the Malwarebytes Setup Wizard which will guide you through the installation process.
To install Malwarebytes on your machine, keep following the prompts by clicking the “Next” button.
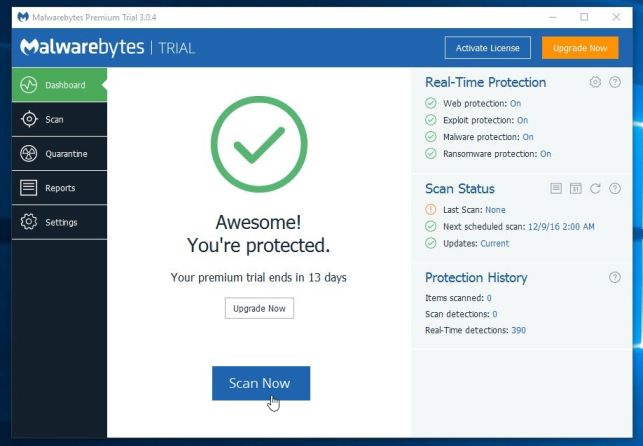
- Once installed, Malwarebytes will automatically start and update the antivirus database. To start a system scan you can click on the “Scan Now” button.
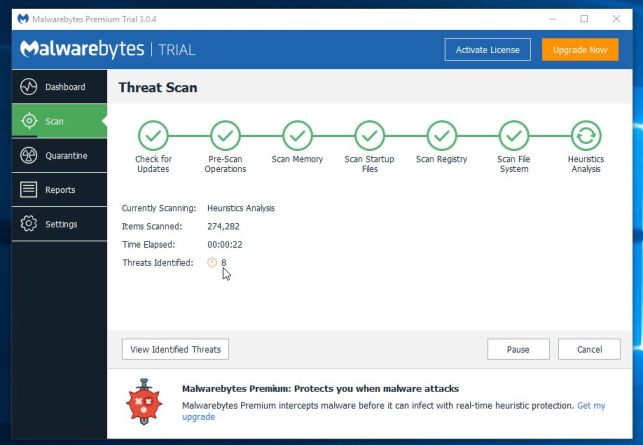
- Malwarebytes will now start scanning your computer for malicious programs.
This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
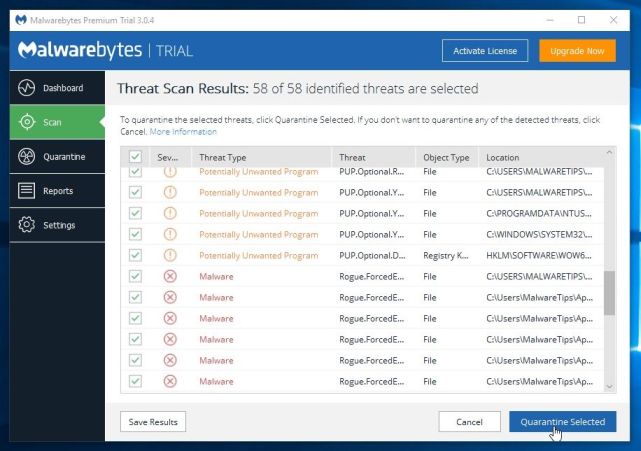
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected.
To remove the malicious programs that Malwarebytes has found, click on the “Quarantine Selected” button.
- Malwarebytes will now quarantine all the malicious files and registry keys that it has found.
To complete the malware removal process, Malwarebytes may ask you to restart your computer.
When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
STEP 3: Double-check for malicious programs for HitmanPro
HitmanPro can find and remove malware, adware, bots, and other threats that even the best antivirus suite can oftentimes miss. HitmanPro is designed to run alongside your antivirus suite, firewall, and other security tools.
- You can download HitmanPro from the below link:
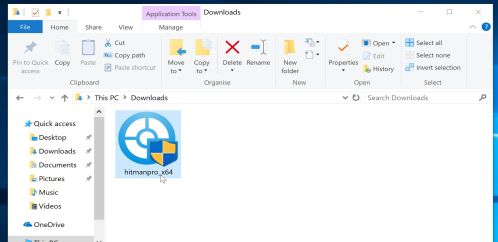
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - When HitmanPro has finished downloading, double-click on the “hitmanpro” file to install this program on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- When the program starts you will be presented with the start screen as shown below. Now click on the Next button to continue with the scan process.
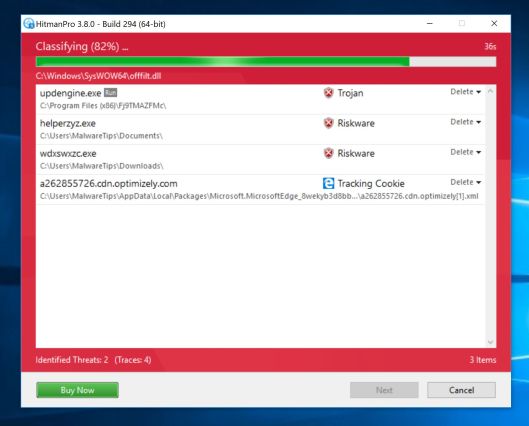
- HitmanPro will now begin to scan your computer for malware.
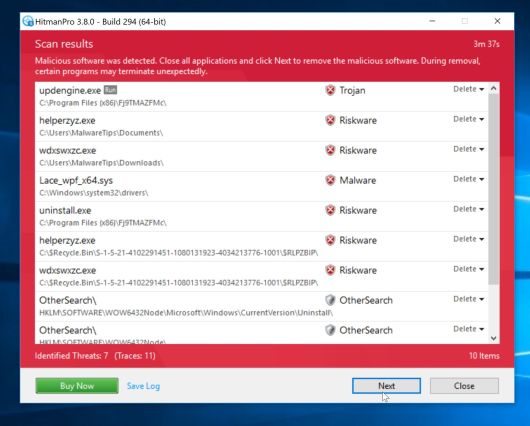
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
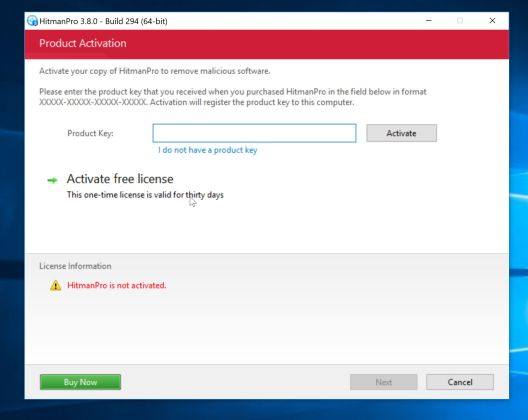
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
When the process is complete, you can close HitmanPro and continue with the rest of the instructions.
Your PC should now be free of the VB:Trojan.VBA.Agent.TY Trojan. If you are still experiencing problems while trying to remove VB:Trojan.VBA.Agent.TY malware from your PC, please do one of the following:
- Run a system scan with Emsisoft Emergency Kit
- Ask for help in our Malware Removal Assistance for Windows forum.