Microsoft has released emergency patches to address four previously undisclosed security flaws in Exchange Server that it says are being actively exploited by a new Chinese state-sponsored threat actor with the goal of perpetrating data theft.
Describing the attacks as "limited and targeted," Microsoft Threat Intelligence Center (MSTIC) said the threat actor used these vulnerabilities to access on-premises Exchange servers, in turn granting access to email accounts and paving the way for the installation of additional malware to facilitate long-term access to victim environments.
The tech giant primarily attributed the campaign with high confidence to a threat actor it calls HAFNIUM, a state-sponsored hacker collective operating out of China, although it suspects other groups may also be involved.
Discussing the tactics, techniques, and procedures (TTPs) of the group for the first time, Microsoft paints HAFNIUM as a "highly skilled and sophisticated actor" that mainly singles out entities in the U.S. for exfiltrating sensitive information from an array of industry sectors, including infectious disease researchers, law firms, higher education institutions, defense contractors, policy think tanks and NGOs.
HAFNIUM is believed to orchestrate its attacks by leveraging leased virtual private servers in the U.S. in an attempt to cloak its malicious activity.
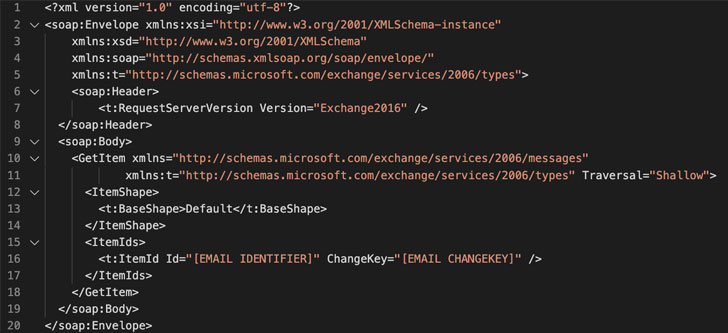
The three-stage attack involves gaining access to an Exchange Server either with stolen passwords or by using previously undiscovered vulnerabilities, followed by deploying a web shell to control the compromised server remotely. The last link in the attack chain makes use of remote access to plunder mailboxes from an organization's network and export the collected data to file sharing sites like MEGA.
To achieve this, as many as four zero-day vulnerabilities discovered by researchers from Volexity and Dubex are used as part of the attack chain —
Although the vulnerabilities impact Microsoft Exchange Server 2013, Microsoft Exchange Server 2016, and Microsoft Exchange Server 2019, Microsoft said it's updating Exchange Server 2010 for "Defense in Depth" purposes.
- CVE-2021-26855: A server-side request forgery (SSRF) vulnerability in Exchange Server
- CVE-2021-26857: An insecure deserialization vulnerability in the Unified Messaging service
- CVE-2021-26858: A post-authentication arbitrary file write vulnerability in Exchange, and
- CVE-2021-27065: A post-authentication arbitrary file write vulnerability in Exchange
Furthermore, since the initial attack requires an untrusted connection to Exchange server port 443, the company notes that organizations can mitigate the issue by restricting untrusted connections or by using a VPN to separate the Exchange server from external access.
Microsoft, besides stressing that the exploits were not connected to the SolarWinds-related breaches, said it has briefed appropriate U.S. government agencies about the new wave of attacks. But the company didn't elaborate on how many organizations were targeted and whether the attacks were successful.
Stating that the intrusion campaigns appeared to have started around January 6, 2021, Volexity cautioned its detected active in-the-wild exploitation of multiple Microsoft Exchange vulnerabilities used to steal email and compromise networks.
"While the attackers appear to have initially flown largely under the radar by simply stealing emails, they recently pivoted to launching exploits to gain a foothold," Volexity researchers Josh Grunzweig, Matthew Meltzer, Sean Koessel, Steven Adair, and Thomas Lancaster explained in a write-up.
"From Volexity's perspective, this exploitation appears to involve multiple operators using a wide variety of tools and methods for dumping credentials, moving laterally, and further backdooring systems."
Microsoft Senior Threat Intelligence Analyst Kevin Beaumont has also created a nmap plugin that can be used to scan a network for potentially vulnerable Microsoft Exchange servers.
"Even though we've worked quickly to deploy an update for the Hafnium exploits, we know that many nation-state actors and criminal groups will move quickly to take advantage of any unpatched systems," Microsoft's Corporate Vice President of Customer Security, Tom Burt, said. "Promptly applying today's patches is the best protection against this attack."
Given the severity of the flaws, it's no surprise that patches have been rolled out a week ahead of the company's Patch Tuesday schedule, which is typically reserved for the second Tuesday of each month. Customers using a vulnerable version of Exchange Server are recommended to install the updates immediately to thwart these attacks.
4 Actively Exploited 0-Day Flaws Found in Microsoft Exchange
- Thread starter enaph
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
The US is expressing growing concern over a hack on Microsoft's Exchange email software that the tech company has blamed on China.
"This is an active threat," White House press secretary Jen Psaki said on Friday. "Everyone running these servers - government, private sector, academia - needs to act now to patch them."
Microsoft said hackers had used its mail server to attack their targets.

Microsoft hack: White House warns of 'active threat' of email attack
The tech giant says a state-sponsored group operating out of China is breaching email servers.
Chris Krebs on Twitter:
This is the real deal. If your organization runs an OWA server exposed to the internet, assume compromise between 02/26-03/03. Check for 8 character aspx files in C:\\inetpub\wwwroot\aspnet_client\system_web\. If you get a hit on that search, you’re now in incident response mode.
This is the real deal. If your organization runs an OWA server exposed to the internet, assume compromise between 02/26-03/03. Check for 8 character aspx files in C:\\inetpub\wwwroot\aspnet_client\system_web\. If you get a hit on that search, you’re now in incident response mode.

Microsoft Exchange Cyber Attack — What Do We Know So Far?
Recent flaw in Microsoft Exchange servers believed to have infected tens of thousands of businesses, government entities.
 thehackernews.com
thehackernews.com

European Banking Authority hit by Microsoft Exchange hack
The EU body is one of the first major organisations to admit falling victim to the global email hack.
There’s a vexing mystery surrounding the 0-day attacks on Exchange servers
A half-dozen groups exploiting the same 0-days is unusual, if not unprecedented.
 arstechnica.com
arstechnica.com
- Aug 17, 2014
- 13,089
- 125,690
- 8,399
Threat actors are now installing a new ransomware called 'DEARCRY' after hacking into Microsoft Exchange servers using the recently disclosed ProxyLogon vulnerabilities.
Since Microsoft revealed earlier this month that threat actors were compromising Microsoft Exchange servers using new zero-day ProxyLogon vulnerabilities, a significant concern has been when threat actors would use it to deploy ransomware.
Unfortunately, tonight our fears became a reality, and threat actors are using the vulnerabilities to install the DearCry ransomware. [...]

DearCry ransomware attacks Microsoft Exchange with ProxyLogon exploits
Threat actors are now installing a new ransomware called 'DEARCRY' after hacking into Microsoft Exchange servers using the recently disclosed ProxyLogon vulnerabilities.
Discover the key facts, takeaways and vital next steps for you and your organization. F-Secure recommends all organizations patch these vulnerabilities as a priority and investigates those systems for evidence of compromise. These vulnerabilities - and exploitation of them by threat actors - have dominated the cyber security news cycle for weeks. F-Secure has observed widespread exploitation by multiple threat actors to steal data and install malware to gain further access to organizations’ networks.
In this webinar F-Secure will cover:
Patching will not remove prior compromises, but it will prevent future exploitation. It’s vital organizations find out if they have already been breached.
- The latest updates on the evolving threats
- Insights into exploitation activity observed by F-Secure
- How to identify potential breaches and exploitation on your systems
- Key takeaways for you and your organization

MICROSOFT EXCHANGE PROXYLOGON: THE PATH BEYOND THE PATCHES
Four recently-discovered vulnerabilities in Microsoft Exchange Servers - known collectively as ProxyLogon - grant attackers high privilege access to organizations' environments. Discover the key facts, takeaways and vital next steps for you and your organization. F-Secure recommends...
With court order, FBI removes hundreds of Exchange Server web shells from US organizations
 www.cyberscoop.com
www.cyberscoop.com
The FBI has used a court order to remove malicious code from hundreds of U.S. computers running the Microsoft Exchange Server email program, Justice Department officials announced Tuesday.
With court order, FBI removes hundreds of Exchange Server web shells from US organizations
It's one of the most aggressive actions taken yet by U.S. government or corporate officials to combat the Exchange Server vulnerabilities.
You may also like...
-
CISA Beware! Hackers Are Actively Exploiting Windows Server Update Services RCE Flaw in the Wild
- Started by Brownie2019
- Replies: 1
-
Attackers Exploit Windows Server Update Services Flaw to Steal Sensitive Organizational Data
- Started by Brownie2019
- Replies: 1
-
Microsoft releases emergency patches for SharePoint RCE flaws exploited in attacks
- Started by Gandalf_The_Grey
- Replies: 4
-
Security News Windows Active Directory Vulnerability Allows Attackers to Execute Malicious Code
- Started by Brownie2019
- Replies: 1
-
Security News Russian hackers exploit Zimbra flaw in Ukrainian govt attacks
- Started by Captain Awesome
- Replies: 3