silversurfer
Super Moderator
Thread author
Verified
Top Poster
Staff Member
Malware Hunter
Forum Veteran
- Aug 17, 2014
- 12,743
- 123,910
- 8,399
A new backdoor malware called BlackWater pretending to be COVID-19 information while abusing Cloudflare Workers as an interface to the malware's command and control (C2) server.
Cloudflare Workers are JavaScript programs that run directly on Cloudflare's edge so that they can interact with connections from remote web clients. These Workers can be used to modify the output of a web site behind Cloudflare, disable Cloudflare features, or even act as independent JavaScript programs running on the edge that displays output.
For example, a Cloudflare Worker can be created to search for text in a web server's output and replace words in it or to simply output data back to a web client.
Recently MalwareHunterTeam discovered a RAR file being distributed pretending to be information about the Coronavirus (COVID-19) called "Important - COVID-19.rar".
It is not known at this time how the file is being distributed, but it is most likely being done through phishing emails.
Inside this RAR file is a file called "Important - COVID-19.docx.exe" that uses a Word icon. Unfortunately, as Microsoft hides file extensions by default, many will simply see this file as a Word document rather than an executable and be more likely to open it.
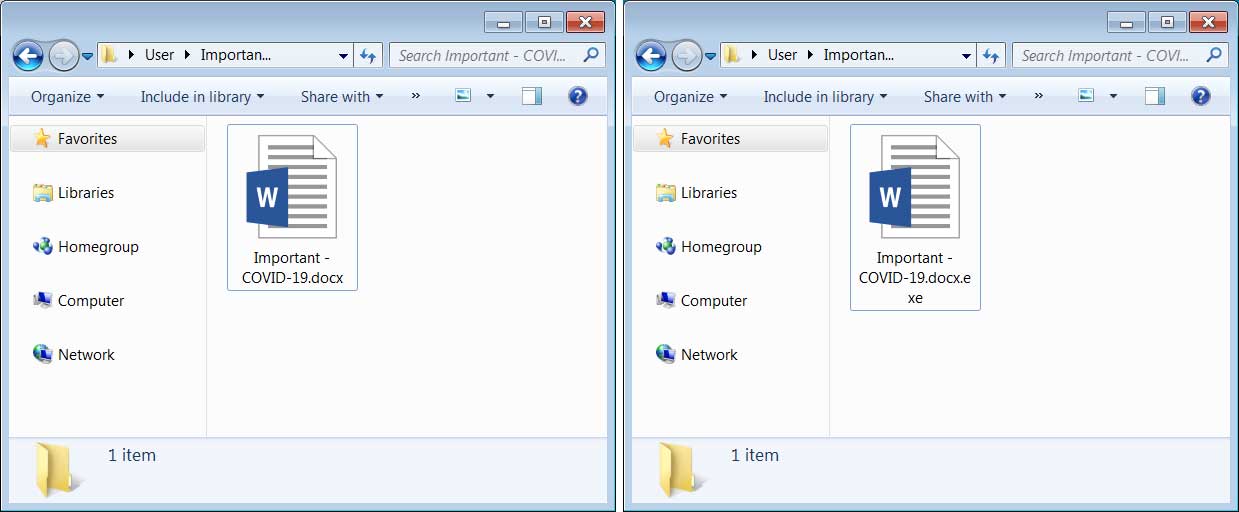
Extracted file with extensions off and on
