- Apr 24, 2013
- 1,200
Carbanak now uses a code-signing certificate from Comodo
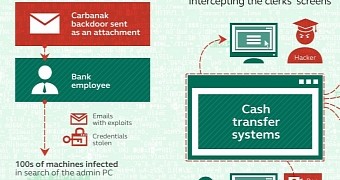
The Carbanak banking trojan was spotted once again in attacks on financial institutions and businesses across the globe, as CSIS is reporting.
Carbanak, also known as Anunak, was previously discovered and analyzed by Russian-based Kaspersky Lab security firm, in February 2015.
Back then, Kaspersky Lab was estimating that the group behind Carbanak infiltrated up to 100 financial institutions worldwide, gaining control over their computers, and stealing around $1 billion / €876.7 million.
Since then, the trojan has been making sporadic returns, always changing one small detail in its operation to keep up with firewall and antivirus updates.
New Carbanak variant uses a new proprietary communications protocol
As the CSIS team is now reporting, a new variant of the trojan has been observed in the wild, targeting the same kind of financial corporations as before.
This version of Carbanak is different from the original, using a predefined IP address instead of random generated domains to talk to the C&C server, employing random generated file names, and featuring a new proprietary protocol for managing its plugins and internal communications.
Just as before, Carbanak still hides in an infected svchost.exe process, keeps its modular structure that allows it to shape shift and adapt to victims, and continues to use a legitimate code-signing certificate to avoid detection.
According to CSIS, this new version of Carbanak uses a code-signing certificate issued by Comodo, to what appears to be a legal Russian-based business.
Carbanak continues to brazenly flaunt its Russian connection
Security researchers believe the criminals behind Carbanak have registered a real company with the sole purpose of having a legal base for some of their fraudulent transactions.
"Carbanak-related transfers are rather huge," says the CSIS team. "Possibly, they have registered a company and opened bank accounts in order to receive their stolen money while having full control of the transferring process."
Previously ESET researchers found a version of Carbanak using stolen certificates belonging to companies Moscow-based companies Stroi-Tekh-Sever, Flash, OOO "Techcom" and Torg-Group.
The Russian connection for the Carbanak trojan is very well-known, Trend Micro researchers previously linking one of its C&C servers to an IP owned by the Russian Security Service (FSB).