silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,210
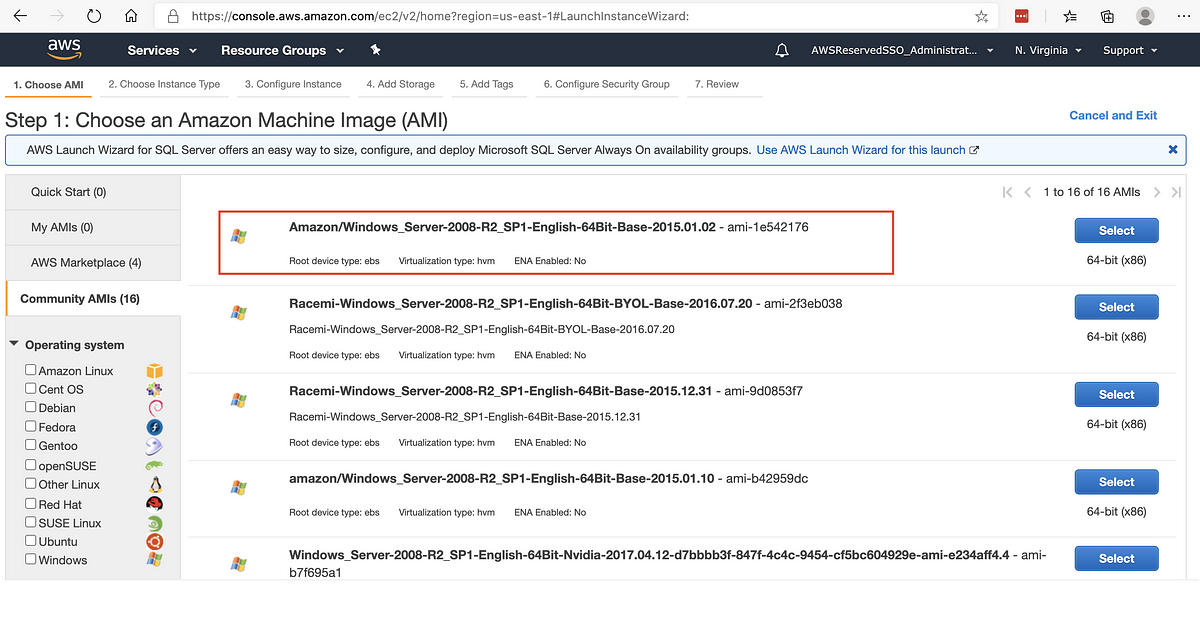
Full report by researchers below:Security researchers are sounding the alarm about Amazon Machine Images (AMIs) tainted with malicious code that could compromise an organization’s cloud environment.
While the method is not new, it could become a trend unless taking the proper precautions before deploying an Elastic Compute Cloud (EC2) instance based on community AMIs.
During a recent engagement at a financial institution, researchers at cybersecurity company Mitiga found that an EC2 server in the customer’s Amazon Web Services (AWS) environment was running unauthorized code.
They discovered an active cryptocurrency miner that had not been planted by exploiting a vulnerability or misconfigured settings. Instead, it came embedded in the community AMI used to create the EC2 instance.
Security Advisory: Mitiga Recommends All AWS Customers Running Community AMIs to Verify Them for…
Based on recent research and analysis, we are issuing a global advisory, warning AWS customers running EC2 instances based on Community…
 medium.com
medium.com
