D
Deleted member 178
Thread author
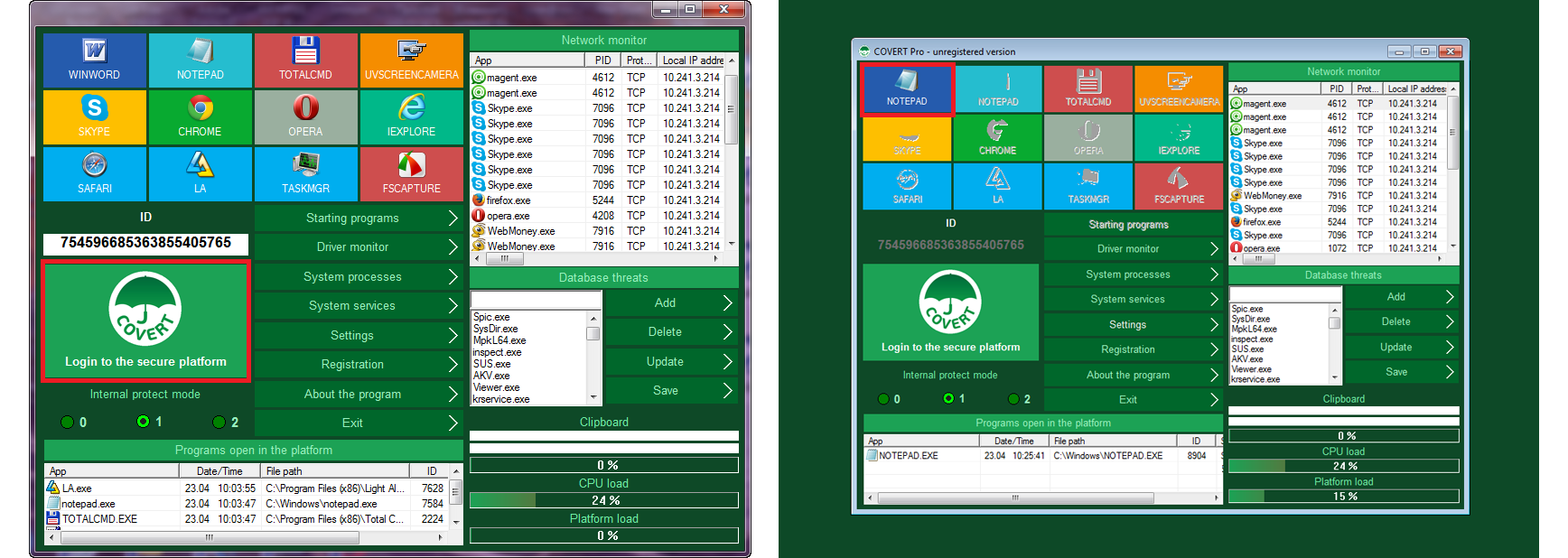
COVERT Pro – an innovative solution to ensure total privacy while working at the computer. It protects against spyware. When working in secure platform, all user’s actions in all applications (browsers, email clients, office software, messengers, etc.) are safely hidden. Using special features of COVERT Pro allows you to detect and remove all hidden applications.
Antispyware COVERT Pro for Windows
If you are convinced that the anti-virus protects you even against new spyware and programs of Riskware category, you should not read more.
Traditional antivirus and antispyware software does not protect against many of screenshoters and keyloggers, because this action is not prohibited, as it is unknown – does that make user himself or someone is spying on him.
Search for spyware on the hard drive is ineffective if it’s not in the malware databases. Analyze the code or behavior is also pointless — it is not known who and for what purpose carries specific to spyware actions.
About the uselessness of classical methods of protection you can read in our article.
Therefore, the traditional antivirus software will not protect you against spyware and riskware.
COVERT Pro – a new approach to privacy protection
To protect against spyware, COVERT Pro uses the masking method. It is the most reliable method against spyware — masking action of user. It means creation of secure platform, inside which user can run any applications, while remaining invisible to the spies.
All user activity on a computer disguised from intercepting. Capturing data from keyboard input and monitor screen is blocked.
Because antispyware COVERT Pro protects not only the physical input, but the virtual keyboard, the program can be used on tablet with OS Windows.
Another unique feature of COVERT Pro is protection against sound recording in the room where the computer is located. There are spyware programs that turns on the microphone when the sound level in the room exceeds a certain level and start to record everything on the hard drive. Then these files are sent to the e-mail address associated with spyware. COVERT Pro allows you to adjust the speakers and microphone level and completely block the microphone. You can get to this menu by pressing F2 key.
Innovative approach, low system requirements, a simple and intuitive user interface, no need to continuously update – makes the program – antispyware COVERT Pro tr
.
A short list of COVERT Pro functionality:
- 1. Secure platform. Entrance to the platform and exit in one click.
- 2. Network Monitor. Shows a list of programs that have access to the Internet at the current time.
- 3. Database threats (malicious or unwanted programs). Available for replenishing by the user.
- 4. Driver Monitor. Shows a list of active and hidden drivers in the operating system.
- 5. System processes. Provides information about the processes (running programs) that occur on your computer.
- 6. Service system. Used to display the list of running services.
- 7. Hidden services and analysis services. Allows you to analyze the svchost.exe file.
- 8. Monitor hidden processes. This is a special function that is used to detect and display the list of hidden processes (rootkits).
- 9. Internal protection mode. There are three modes of protection to control running applications within the platform.
- 10. Quick Launch Buttons application.
- 11. The login ID in the platform to create multiple platforms protection.
- 12. The scale of CPU usage.
- 13. The scale of loading the platform.
- 14. Scale of loading the clipboard.
- 15. Selection of interface languages (English, Italian, German, Czech).
- 16. Emergency exit from the program and all platforms and closing all applications.
- 17. New! Screenshot of registration window with the definition of the parameters of the hardware, where COVERT Pro is installed. Designed to protect the user from losing registration details and obtaining a new registration key free of charge.
- 18. New! Adjusting the speaker volume and microphone inside a secure platform. Allows you to lock the microphone in order to protect from the listening room where the computer is located.
Home: Protection against spyware
seems to be a kind of anti-spyware/logger Virtual Desktop.
interesting.
