Hi Community!
We have just published our latest comparison of nine EDR and XDR solutions, and I think it's worth taking a look.
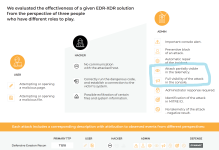
1. The document contains detailed information about the configuration used (usually default + hardened). In our test, we do not disable AV protection to reflect the use of the solution in a production environment.
2. We analyze attack response and information logging to the console.
3. This year, we have used two certification thresholds: GOLD and CERTIFIED.
 avlab.pl
avlab.pl
We have just published our latest comparison of nine EDR and XDR solutions, and I think it's worth taking a look.
- Bitdefender GravityZone XDR
- Check Point Harmony Endpoint Advanced + EDR
- Cisco AMP + XDR
- Elastic Security XDR
- Metras (part of Site)
- ThreatDown + EDR (by Malwarebytes)
- Sophos Intercept X Advanced + XDR
- WithSecure Elements EDR
- Xcitium XDR
1. The document contains detailed information about the configuration used (usually default + hardened). In our test, we do not disable AV protection to reflect the use of the solution in a production environment.
2. We analyze attack response and information logging to the console.
3. This year, we have used two certification thresholds: GOLD and CERTIFIED.
EDR-XDR Solutions Overview-2025, 3rd Edition
EDR-XDR 2025 overview: key features, detection results, and vendor comparison in one clear report.
Last edited: