Canonical has published details in a security notice about a NSS vulnerability in Ubuntu 14.04 LTS, Ubuntu 12.04 LTS, and Ubuntu 10.04 LTS operating systems that has been corrected.
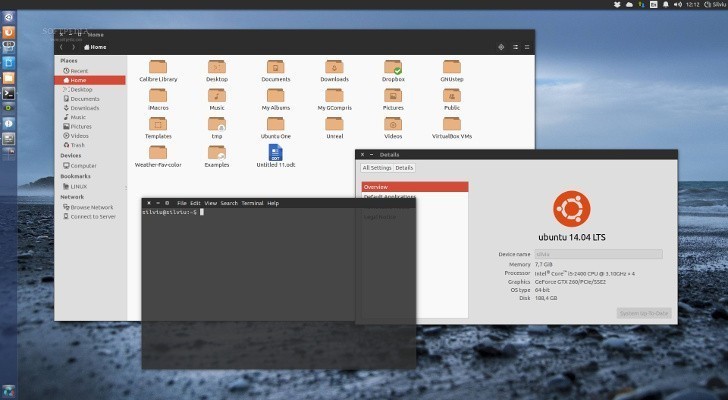
- Ubuntu 14.04 LTS
A new vulnerability has been found and fixed in the supported Ubuntu OSes and it's just a matter of updating the system in order to correct it. The developers have explained that NSS could be made to crash or run programs in certain conditions.
According to the security notice, "Tyson Smith and Jesse Schwartzentruber discovered that NSS contained a race condition when performing certificate validation. An attacker could use this issue to cause NSS to crash, resulting in a denial of service, or possibly execute arbitrary code."
For a more detailed description of the problems, you can see Canonical's security notification. Users should upgrade their Linux distribution in order to correct this issue.
The flaw can be fixed if you upgrade your system(s) to the latest libnss3 packages specific to each distribution. To apply the patch, users can simply run the Update Manager application.
If you don't want to use the Software Updater, you can open a terminal and enter the following commands (you will need to be root):
sudo apt-get update
sudo apt-get dist-upgrade
In general, a standard system update will make all the required changes. It's necessary to restart the computer in order to finish the update.
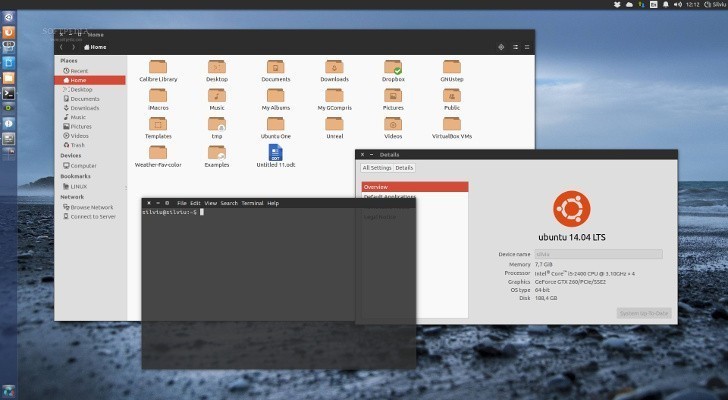
- Ubuntu 14.04 LTS
A new vulnerability has been found and fixed in the supported Ubuntu OSes and it's just a matter of updating the system in order to correct it. The developers have explained that NSS could be made to crash or run programs in certain conditions.
According to the security notice, "Tyson Smith and Jesse Schwartzentruber discovered that NSS contained a race condition when performing certificate validation. An attacker could use this issue to cause NSS to crash, resulting in a denial of service, or possibly execute arbitrary code."
For a more detailed description of the problems, you can see Canonical's security notification. Users should upgrade their Linux distribution in order to correct this issue.
The flaw can be fixed if you upgrade your system(s) to the latest libnss3 packages specific to each distribution. To apply the patch, users can simply run the Update Manager application.
If you don't want to use the Software Updater, you can open a terminal and enter the following commands (you will need to be root):
sudo apt-get update
sudo apt-get dist-upgrade
In general, a standard system update will make all the required changes. It's necessary to restart the computer in order to finish the update.