An Empirical Assessment of Endpoint Security Systems Against Advanced Persistent Threats Attack Vectors
Autors: George Karantzas and Constantinos Patsakis
https://arxiv.org/pdf/2108.10422.pdf
WARNING.
This article should not upset Home users, because the chances of such attacks (via never-seen malware) are very small in the Home environment. They can be important in Enterprises (targeted attacks).
Edit.
Post edited to include the corrected and extended article mentioned by @upnorth .
Autors: George Karantzas and Constantinos Patsakis
https://arxiv.org/pdf/2108.10422.pdf
WARNING.
This article should not upset Home users, because the chances of such attacks (via never-seen malware) are very small in the Home environment. They can be important in Enterprises (targeted attacks).
Abstract:
Advanced persistent threats pose a significant challenge for blue teams as they apply various attacks over prolonged periods, impeding event correlation and their detection. In this work, we leverage various diverse attack scenarios to assess the efficacy of EDRs and other endpoint security solutions against detecting and preventing APTs. Our results indicate that there is still a lot of room for improvement as state of the art endpoint security systems fail to prevent and log the bulk of the attacks that are reported in this work. Additionally, we discuss methods to tamper with the telemetry providers of EDRs, allowing an adversary to perform a more stealth attack.
1. Introduction
Cyber attacks are constantly evolving in both sophistication and scale, reaching such an extent that the World Economic Forum considers it the second most threatening risk for global commerce over the next decade [9]. The underground economy that has been created has become so huge to the point of being comparable to the size of national economies. Contrary to most cyberattacks which have a ‘hit-and-run’ modus operandi, we have advanced persistent threats, most widely known through the abbreviation APT. In most cyber attacks, the threat actor would try to exploit a single exploit or mechanism to compromise as many hosts as possible and try to immediately monetise the abuse of the stored information and resources as soon as possible. However, in APT attacks, the threat actor opts to keep a low profile, exploiting more complex intrusion methods through various attack vectors and prolong the control of the compromised hosts. Indeed, this control may span several years, as numerous such incidents have shown.
Due to their nature and impact, these attacks have received a lot of research focus as the heterogeneity of the attack vectors introduces many issues for traditional security mechanisms. For instance, due to their stealth character, APTs bypass antiviruses and therefore, more advanced methods are needed to timely detect them. The goal of an Endpoint Protection Platform (EPP) is prevent and mitigate endpoint security threats such as malware. Going a step further, Endpoint Detection and Response (EDR) systems provide a more holistic approach to the security of an organisation as beyond signatures, EDRs correlate information and events across multiple hosts of an organisation. Therefore, individual events from endpoints that could fall below the radar are collected, processed, and correlated, providing blue teams with a deep insight into the threats that an organisation’s perimeter is exposed to.
Despite the research efforts and the advanced security mechanisms deployed through EPPs and EDRs, recent events illustrate that we are far from being considered safe from such attacks. Since APT attacks are not that often and not all details can be publicly shared, we argue that a sanity check to assess the preparedness of such security mechanisms against such attacks is deemed necessary. Therefore, we decided to conduct an APT group simulation to test the enterprise defences’ capabilities and especially EDRs, covering also some EPPs. To this end, we opted to simulate an APT attack in a controlled environment using a set of scripted attacks which match the typical modus operandi of these attacks. Thus, we try to infiltrate an organisation using spear-phishing and malware delivery techniques and then examine the IOCs and responses produced by the EDRs. We have created four such use case scenarios which are rather indicative and diverse enough to illustrate the weak points of several perimeter security mechanisms, focusing more on EDRs.
...
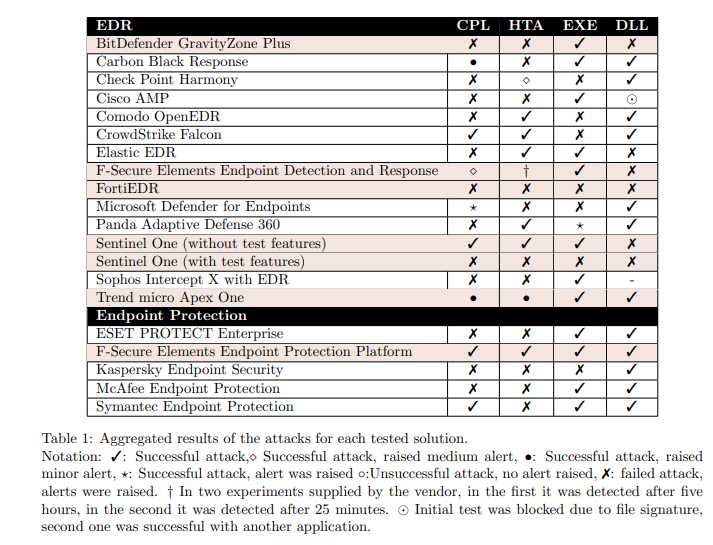
Table 1 illustrates an aggregated overview of our findings. Evidently, from the 20 attacks that were launched, more than half of them were successful. It is rather alarming that none of the EDRs managed to detect all of the attacks. More precisely, 10 attacks were completely successful, as they were completed successfully and no alert was issued; 3 attacks were successful, yet they issued a low significance alert; 1 attack was not successful, yet it did not issue an alert, and 6 attacks were detected and correctly reported by the EDRs.
Edit.
Post edited to include the corrected and extended article mentioned by @upnorth .
Attachments
Last edited: