A group of attackers has built a fake version of the Huorong Security antivirus website to trick users into downloading ValleyRAT, a Remote Access Trojan (RAT) built on the Winos4.0 framework.
Huorong Security, known in Chinese as 火绒, is a free antivirus product widely used across mainland China. The attackers registered huoronga[.]com — a near-perfect copy of the legitimate huorong.cn — with just one extra letter added at the end.
This typosquatting trick catches users who mistype the address or arrive via a phishing link. The page looks convincing enough that most visitors would suspect nothing.

Fake Huorong Download Site Used to Deploy ValleyRAT Backdoor in Targeted Malware Campaign
Fake Huorong site spreads ValleyRAT via Winos4.0 in Silver Fox typosquatting campaign targeting Chinese users.cybersecuritynews.com
Fake Huorong Download Site Used to Deploy ValleyRAT Backdoor in Targeted Malware Campaign
- Thread starter Parkinsond
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
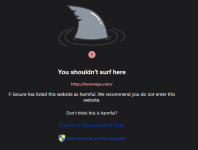
Even ControlD hagezi tif is blockingF-Secure.
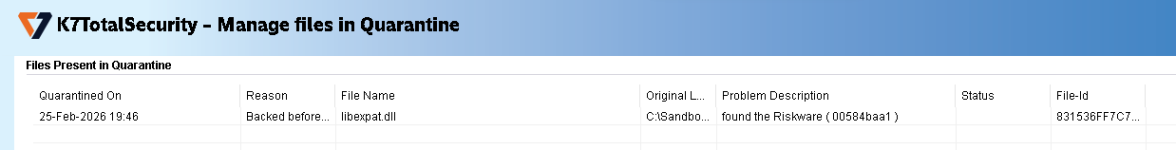
View attachment 295899
Attachments
Tested the RAT in a VM against Kaspersky Free, and it was blocked by System Watcher after executing

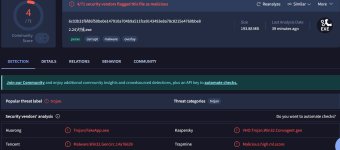
According to VT, the fake website was first reported Nov 2025; I do not know why it is still active and the delivered RAT is not detected by signature (only by behavioral analysis)!Tested the RAT in a VM against Kaspersky Free, and it was blocked by System Watcher after executing
View attachment 295901
You're seeing website submission, not the malware. The malware wasn't present in VT. I uploaded it. Kaspersky's VHO detection became live after I ran it on my VM. Kaspersky uploaded the full 198 MB sample to their server as soon as System Watcher detected it.According to VT, the fake website was first reported Nov 2025; I do not know why it is still active and the delivered RAT is not detected by signature (only by behavioral analysis)!
View attachment 295903
Detected by Huorong this time; "Fool me once, shame on you; fool me twice, shame on me"You're seeing website submission, not the malware. The malware wasn't present in VT. I uploaded it. Kaspersky's VHO detection became live after I ran it on my VM. Kaspersky uploaded the full 198 MB sample to their server as soon as System Watcher detected it.
Last edited by a moderator:
Bitdefender also detected, though the detection mechanism is different. It detected one file the malware came up with and stopped the process. Kaspersky detected the whole chain as malicious behavior and removed the source sample and a few other files created by it. Both stopped the attack but Kaspersky cleaned it up better.

the hash is not showing on opentip so sure it was uploaded by K?Tested the RAT in a VM against Kaspersky Free, and it was blocked by System Watcher after executing
View attachment 295901
Also it wlll be interesting to test it against overrated ESET.
Yes, I'm sure it was uploaded. I have TrafficMonitor installed. As soon as Kaspersky's icon turned red, it started to upload it. It took a few seconds to upload as the file was 193 MB. In addition, it may have uploaded other files extracted by the malware. This is a common pattern whenever I test Kaspersky against a sample that it has never seen before. Most products don't upload the whole file but Kaspersky does quite often. That's how the NSA employees' secret hacktool file which Kaspersky deemed suspicious, ended up in Kaspersky's KSN server even though it was that employee who was being stupid while Kaspersky was just doing its job as it is designed to.he hash is not showing on opentip so sure it was uploaded by K?
Opentip is not always reliable. Sometimes it doesn't find the hash if the file wasn't uploaded manually to Opentip. But even then, it's as if Kaspersky has forgotten about this file. I have manually uploaded it now and it says it's safe
I won't say ESET is overrated but you may call it overrated only in the sense that it has some obvious weaknesses like Ransomware and MBR destroyer malware, which many users may not know about; though the case of ransomware has improved in the last couple of years.Also it wlll be interesting to test it against overrated ESET.
I would say it's underrated in the sense that it can still detect almost all threats locally pre-execution by signatures & heuristics + what they call their DNA detection with no/rare help from the cloud, which is very impressive. The more you detect pre-execution, the better, but a high detection rate by a behavior blocker looks more fancy, so this very high pre-execution detection rate of ESET is often not appreciated as much.
ESET also blocks this RAT. It detected the same file that BD detected + one more PUA.
Yes, I have noticed that Kaspersky threat intelligence portal takes a long time to upload the entire submitted file, if large in size, while VT takes only very short time (most probably uploading small parts of the submitted file).Most products don't upload the whole file but Kaspersky does quite often.
Last edited by a moderator:
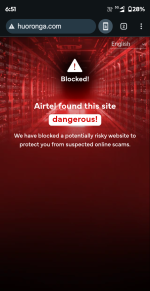
Unfortunately, SmartScreen, Google safe search, and Yandex protect do not.AIRTEL as a Telecom
Network Provider Block this phishing/Scam site as dangerous!
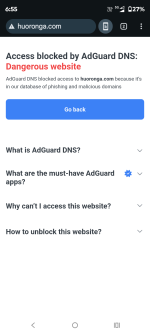
ADGUARD DNS PROTECTION also block this aswell!
View attachment 295922View attachment 295923
F
ForgottenSeer 123960
Technical Analysis & Remediation
MITRE ATT&CK Mapping
T1036 (Masquerading)
Use of fake domains (e.g., huoronga[.]com) mimicking huorong.cn.
T1562.001 (Impair Defenses: Disable or Modify Tools)
Uses PowerShell to add Windows Defender exclusions for its persistence directory (%APPDATA%\trvePath\) and main process (WavesSvc64.exe).
T1053.005 (Scheduled Task/Job)
Creates C:\Windows\Tasks\Batteries.job to establish persistence across reboots.
T1055 (Process Injection)
Injects code into other processes for stealthy execution.
T1119 / T1056.001 (Collection / Keylogging)
Captures keystrokes and reads browser cookie files.
CVE Profile
N/A [CISA KEV Status: Inactive].
The attack explicitly relies on user execution and does not leverage vulnerability exploitation.
Telemetry
Hashes (SHA-256)
NSIS Installer 72889737c11c36e3ecd77bf6023ec6f2e31aecbc441d0bdf312c5762d073b1f4
WavesSvc64.exe db8cbf938da72be4d1a774836b2b5eb107c6b54defe0ae631ddc43de0bda8a7e
Network / C2
161.248.87[.]250 (TCP 443)
Encoded C2: yandibaiji0203[.]com
Redirector
hndqiuebgibuiwqdhr[.]cyou
Registry Keys & File Paths
HKCU\SOFTWARE\IpDates_info
HKCU\Console\0\451b464b7a6c2ced348c1866b59c362e
C:\ProgramData\DisplaySessionContainers.log
Constraint
The structure resembles a modular loader, as telemetry confirms the malware dynamically deletes and rewrites its core files to evade signature detection while fetching additional payloads.
Remediation - THE ENTERPRISE TRACK (NIST SP 800-61r3 / CSF 2.0)
GOVERN (GV) – Crisis Management & Oversight
Command
Initiate internal advisory regarding software procurement policies; restrict downloading security software from unverified search engine results.
DETECT (DE) – Monitoring & Analysis
Command
Deploy SIEM queries for outbound connections to 161.248.87[.]250 over TCP 443.
Command
Hunt for Windows Defender exclusion modifications involving WavesSvc64.exe or %APPDATA%\trvePath\.
RESPOND (RS) – Mitigation & Containment
Command
Isolate endpoints exhibiting the Batteries.job scheduled task.
Command
Terminate WavesSvc64.exe processes and purge the associated %APPDATA%\trvePath\ directory.
Command
Block the provided typo domains and redirectors (huoronga[.]com, hndqiuebgibuiwqdhr[.]cyou) at the perimeter firewall/DNS sinkhole.
RECOVER (RC) – Restoration & Trust
Command
Validate clean state by ensuring HKCU\SOFTWARE\IpDates_info is removed and Defender exclusions are restored to baseline.
Command
Rotate all credentials and session cookies for users on compromised endpoints, given the malware's confirmed cookie-stealing and keylogging capabilities.
IDENTIFY & PROTECT (ID/PR) – The Feedback Loop
Command
Implement AppLocker or WDAC policies to prevent execution of unapproved NSIS installers from user-space directories.
Remediation - THE HOME USER TRACK (Safety Focus)
Priority 1: Safety
Command
"Disconnect from the internet immediately." if you recently downloaded Huorong Security from a search engine result and experience performance issues or altered Windows Defender settings.
Command
"Do not log into banking/email until verified clean."
Priority 2: Identity
Command
Reset passwords and MFA using a known clean device (e.g., phone on 5G), as ValleyRAT actively logs keystrokes and steals browser cookies.
Priority 3: Persistence
Command
Check Scheduled Tasks for a task named "Batteries" and remove it.
Command
Manually review Windows Defender exclusions under Virus & threat protection settings. Remove any unauthorized exclusions (specifically looking for trvePath or WavesSvc64.exe).
Hardening & References
Baseline
CIS Benchmarks for Windows 10/11 (Enforce Standard User privileges to block unprompted scheduled task creation).
Framework
NIST CSF 2.0 / SP 800-61r3.
TTP Summary
Typosquatting → Malicious NSIS Installer → PowerShell Defender Tampering → Registry/Task Persistence → C2 via TCP 443.
Source
Malwarebytes Threat Intelligence
CyberSecurity News
Last edited by a moderator:
They will but lateUnfortunately, SmartScreen, Google safe search, and Yandex protect do not.
SmartScreen detects it. I checked when you shared this post yesterday. Something is wrong in your system/ISP it seems. There was another site that SmartScreen was blocking for me but not for you.Unfortunately, SmartScreen, Google safe search, and Yandex protect do not.
Agree, and it seems to be a selective defect of SS, as some other websites are blocked.Something is wrong in your system/ISP it seems. There was another site that SmartScreen was blocking for me but not for you.
Anyway, I do not rely on a single protective layer; SS is always combined with ControlD hagezi tif and sometimes Norton safe web extension (inspite of throwing some FP blocks).
You may also like...
-
iClicker hack targeted students with malware via fake CAPTCHA
- Started by Gandalf_The_Grey
- Replies: 2
-
Fake Avast Antivirus Sites Are Spreading SpyNote Android Malware
- Started by enaph
- Replies: 1
-
Typosquat campaign mimics 27 brands to push Windows, Android malware
- Started by Gandalf_The_Grey
- Replies: 0
-
ExpressVPN Clone Sites Infect Visitors with Redline Malware
- Started by CyberTech
- Replies: 0