- Jul 27, 2015
- 5,459
The US government has issued an alert about Cuba; not the state but a ransomware gang that's taking millions in purloined profits.
The Cuba gang has hit more than 100 organizations worldwide, demanding over $145 million in payments and successfully extorting at least $60 million since August, according to a joint FBI and US Cybersecurity and Infrastructure Security Agency (CISA) advisory. According to the security alert: Note: While this ransomware is known by industry as "Cuba ransomware," there is no indication Cuba ransomware actors have any connection or affiliation with the Republic of Cuba.
The FBI first warned about the cybercrime gang in December 2021, and since then, the victim count in the US alone has doubled. In that the same time, the ransom payments received also jumped. Private security researchers have identified possible links between Cuba ransomware criminals and their RomCom remote access trojan (RAT) and Industrial Spy ransomware counterparts. The crooks continue to target five critical infrastructure sectors: financial services, government, healthcare and public health, critical manufacturing, and IT, according to the FBI.
As the bureau previously noted, Cuba ransomware miscreants tend to use known bugs in commercial software, phishing emails, compromised credentials, and remote desktop protocol tools to gain initial access to their victims' networks. Once they've broken in, they distribute Cuba ransomware on compromised systems via Hancitor, a loader that can drop or execute other software nasties including RATs.
Since the spring, the criminals have modified their tools to interact with compromised networks and extort payments, according to Palo Alto Networks Unit 42 threat hunters. The security shop's research and consulting arm also discovered the Cuba ransomware crooks exploiting certain known vulnerabilities and using legitimate tools to elevate privileges and burrow deeper into their victims' environments. This includes exploiting CVE-2022-24521 in the Windows Common Log File System (CLFS) driver to steal system tokens and elevate privileges, using a PowerShell script to target service accounts for their associated Active Directory Kerberos ticket and using KerberCache to extract cached Kerberos tickets from a host's Local Security Authority Server Service (LSASS) memory. They are also known to exploit CVE-2020-1472, aka "ZeroLogon," to gain domain administrative privileges.
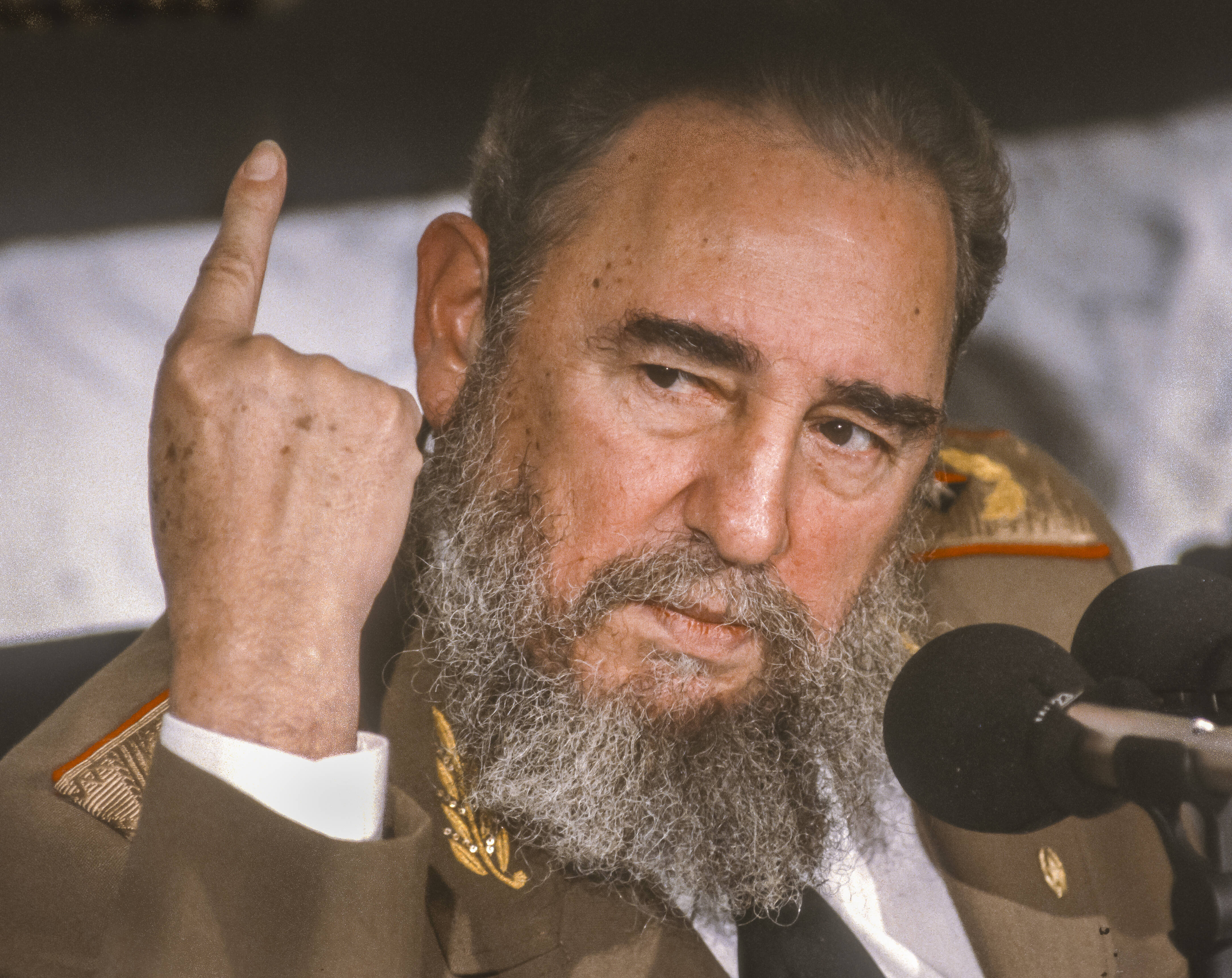
FBI warns about Cuba, no, not that one — the ransomware gang
Critical infrastructure attacks ramping up

