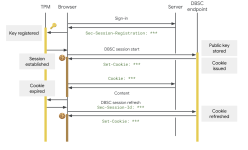
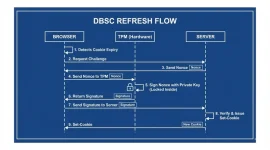
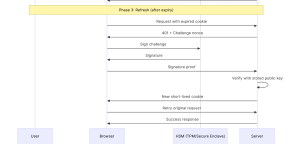
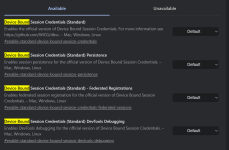
Read more here:Google has officially launched a major security upgrade to protect users from session hijacking. Starting with Chrome version 146 for Windows users, Device Bound Session Credentials (DBSC) is now publicly available.
This new feature aims to stop malware from stealing web cookies and using them to bypass passwords and multi-factor authentication. Support for macOS users will arrive in an upcoming Chrome release.
Session theft happens when a user accidentally downloads malware, such as the LummaC2 infostealer. Once on a device, this malware quietly copies existing session cookies from the browser’s local files and memory.
Attackers then send these stolen cookies to their own servers, allowing them to access user accounts without ever needing a password. Hackers frequently bundle and sell these active session tokens on dark web forums to other cybercriminals.

Google Locks Chrome Sessions to Devices to Stop Cookie Theft
Google has launched a major security upgrade to protect users from session hijacking, starting with Chrome version 146 for Windows users.
 gbhackers.com
gbhackers.com

Protecting Cookies with Device Bound Session Credentials
Posted by Ben Ackerman, Chrome team, Daniel Rubery, Chrome team and Guillaume Ehinger, Google Account Security team Following our April ...
Last edited by a moderator: