silversurfer
Super Moderator
Thread author
Verified
Top Poster
Staff Member
Malware Hunter
Forum Veteran
- Aug 17, 2014
- 12,740
- 123,893
- 8,399
This week GRUB project maintainers have released hundreds of upstream patches for the severe boot loader flaws listed below.
"The BootHole vulnerability announced last year encouraged many people to take a closer look at the security of boot process in general and the GRUB bootloader in particular." "Due to that, during past few months we were getting reports of, and also discovering various security flaws in the GRUB ourselves," said Oracle software developer and GRUB maintainer Daniel Kiper.
Referring to the list of vulnerabilities and CVEs that were remedied, Kiper stated the patch bundle fixing all the bugs comprises 117 patches.
The list of GRUB2 vulnerabilities is as follows:
CVE CVSS 3.1 Severity Type Description Reported by CVE-2020-14372 High (7.5) Incomplete List of Disallowed Inputs The acpi command allows privileged user to load crafted ACPI tables when Secure Boot is enabled. Máté Kukri CVE-2020-25632 High (7.5) Use-after-free The rmmod implementation for GRUB2 is flawed, allowing an attacker to unload a module used as dependency without checking if any other dependent module is still loaded. Chris Coulson (Canonical) CVE-2020-25647 Medium (6.9) Out-of-bound write grub_usb_device_initialize() is called to handle USB device initialization. It reads out the descriptors it needs from the USB device and uses that data to fill in some USB data structures. grub_usb_device_initialize() performs very little bounds checking and simply assumes the USB device provides sane values. This behavior can trigger memory corruption or lead to arbitrary code execution. Joseph Tartaro (IOActive), Ilja van Sprundel (IOActive) CVE-2020-27749 High (7.5) Stack buffer overflow grub_parser_split_cmdline() expands variable names present in the supplied command line in to their corresponding variable contents and uses a 1kB stack buffer for temporary storage without sufficient bounds checking. An attacker can exploit the flaw to circumvent Secure Boot protections. Chris Coulson (Canonical) CVE-2020-27779 High (7.5) Improper Authorization The cutmem command allows privileged user to remove memory regions when Secure Boot is enabled Teddy Reed CVE-2021-3418 Medium (6.4) Improper Preservation of Permissions GRUB 2.05 reintroduced CVE-2020-15705. This refers to a distro a specific flaw which made upstream in the mentioned version. Dimitri John Ledkov (Canonical) CVE-2021-20225 High (7.5) Heap out-of-bounds write The option parser in GRUB2 allows an attacker to write past the end of a heap-allocated buffer by calling certain commands with a large number of specific short forms of options. Daniel Axtens (IBM) CVE-2021-20233 High (7.5) Heap out-of-bound write There's a flaw on GRUB2 menu rendering code setparam_prefix() in the menu rendering code performs a length calculation on the assumption that expressing a quoted single quote will require 3 characters, while it actually requires 4 characters. Daniel Axtens (IBM)
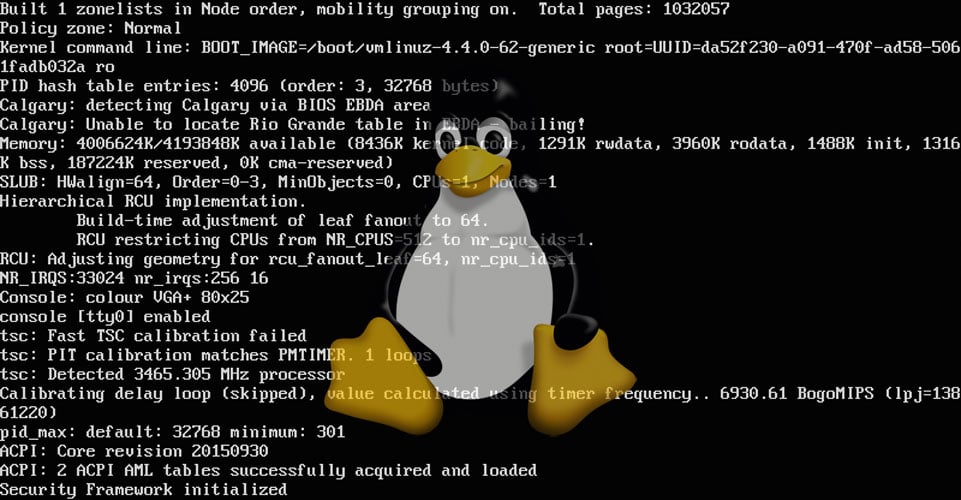
GRUB2 boot loader reveals multiple high severity vulnerabilities
GRUB, a popular Linux boot loader project has fixed multiple high severity vulnerabilities.