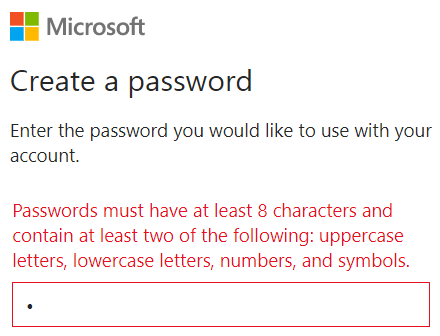
There's a lot of confusion concerning password security, especially among your average person. So I thought it would be good to open up a discussion in order to educate people, including ourselves. How important is it to create a long password? Is length even important or is compexity the most important?
Last edited: