- Sep 5, 2017
- 1,168
Hi guys ,
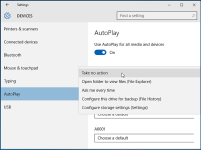
i want to know your opinion about the methods you take to harden your system against usb spreading virusus as you can see in my setup i take full control on windows firewall using Tinywall and create allow rules manually for my programs for real time protection i use Emsisoft with Vodooshield anti exe . for usb i disabled Autorun and Autoplay settings via control panel. is it enough?? is there any other windows customization for hardening or just this is enough ?? i don't want to add any other software for that purpose. it will be overkill action in my point of view. i want to know your thoughts
i want to know your opinion about the methods you take to harden your system against usb spreading virusus as you can see in my setup i take full control on windows firewall using Tinywall and create allow rules manually for my programs for real time protection i use Emsisoft with Vodooshield anti exe . for usb i disabled Autorun and Autoplay settings via control panel. is it enough?? is there any other windows customization for hardening or just this is enough ?? i don't want to add any other software for that purpose. it will be overkill action in my point of view. i want to know your thoughts