- Jan 11, 2011
- 2,007
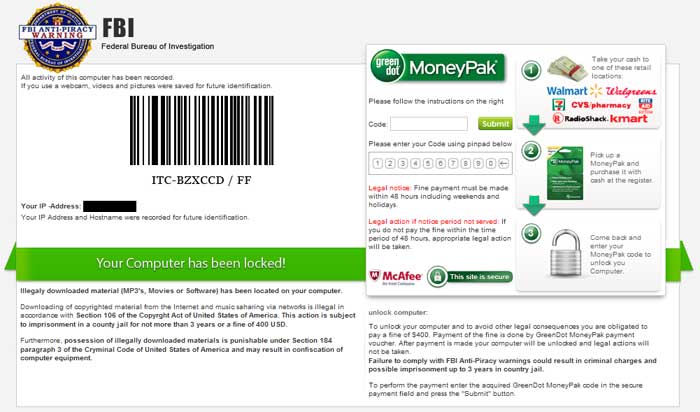
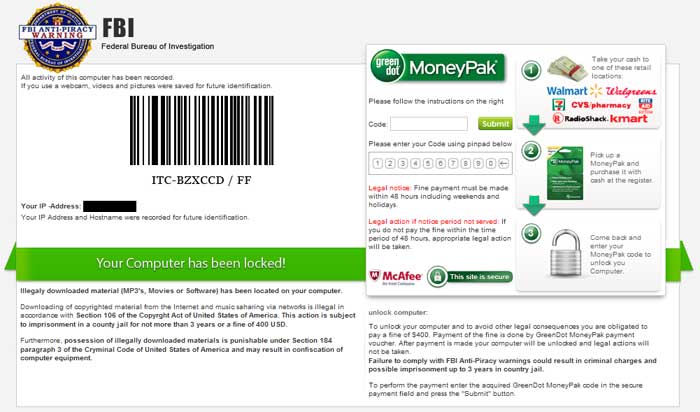
What is the FBI Anti-Piracy MoneyPak Ransomware virus?
FBI Anti-Piracy MoneyPak Ransomware (the FBI virus) is a fake warning that attempts to scare users into paying money to unlock their PC. This malware will prevent users from accessing the standard windows environment until payment is received. Do not make any payments as this infection can be removed.
Am I infected?
These are screenshots of this ransonware.

<h1>How to remove FBI Anti-Piracy MoneyPak Ransomware Virus (Removal Instructions)</h1>
Please note that this is a self-help guide, use at your own risk.
If you experience any problems completing these instructions or wish to have a staff member guide you, please start a new thread in our <a href="https://malwaretips.com/forums/malware-removal-assistance-for-windows.10/">Malware Removal Assistance</a> forum.
<h2>STEP 1 : Start your computer in Safe Mode with Networking</h2>
<br>
<img title="Safe Mode with Networking screen" src="http://malwaretips.com/images/removalguide/safemode.jpg" alt="[Image: Safemode.jpg]" width="539" height="292" border="0" /></li>
</ol>
<h2> Step 2: Download and run RKill</h2>
Download mirror 1 - Download mirror 2 - Download mirror 3
<img title="RKILL LOG" src="http://malwaretips.com/images/removalguide/rkill3.png" alt="[Image: XP Defender 2013 rkill3.jpg]" width="414" height="187" border="0" /></li>
</ol><br>
<br><>WARNING: Do not reboot your computer after running RKill as the malware process will start again , preventing you from properly performing the next step.</>
<h2>Step 3: Download TDSSkiller from here </h2>
NOTE: Reboot to safe mode with networking again and run rKill before proceeding to the next step.
<h2> Step 4: Download Malwarebytes' Anti-Malware(download link) to your desktop
 </h2>
</h2>
NOTE: Boot to safe mode with networking again
<h2>STEP 5: Double check for other malicious files with Emsisoft Emergency Kit</h2>
<ol>
<li>You can download the latest official version of Emsisoft Emergency Kit from the below link.
<a href="http://malwaretips.com/download-emsisoft" rel="nofollow" target="_blank"> <>EMSISOFT EMERGENCY KIT DOWNLOAD LINK</></a> <em>(This link will open a download page in a new window from where you can download Emsisoft Emergency Kit)</em></li>
<li>After the download process will finish , you'll need to <span style="font-weight: bold;">unpack EmsisoftEmergencyKit.zip</span>
<img title="Unpack EmsisoftEmergencyKit.zip" src="http://malwaretips.com/images/removalguide/ekk-zip-image.png" alt="Unpack Emsisoft Emergency Kit" width="319" height="109" /></li>
<li>Open the Emsisoft Emergency Kit folder and double click <>EmergencyKitScanner.bat</>.
<img title="Double click on EmergencyKitScanner.bat" src="http://malwaretips.com/images/removalguide/ekk-batfile.png" alt="Click on EmergencyKitScanner.bat" width="396" height="141" /></li>
<li>A pop-up will prompt you to update Emsisoft Emergency Kit,and you'll need to click the <>Yes</> button to allow this request.
<img title="Update Emsisoft Emergency Kit definitions" src="http://malwaretips.com/images/removalguide/eek-update.png" alt="Update Emsisoft Emergency Kit" width="360" height="139" /></li>
<li>After the Update process has completed,click on the <>Menu</> tab and then select <>Scan PC</>.
<img title="Go to the Scan tab to start a system scan" src="http://malwaretips.com/images/removalguide/ekk-scan.png" alt="Scan tab on Emsisoft Emergency Kit" width="479" height="346" /></li>
<li>Select <>Smart scan</> and click on the <>SCAN</> button to search for malicious files.
<img title="Start a Emsisoft Emergency Kit Smart scan" src="http://malwaretips.com/images/removalguide/ekk-smart-scan.png" alt="Emsisoft Emergency Kit smart scan" width="480" height="345" /></li>
<li>Emsisoft will now start scanning your computer for malicious files.When the scan will be completed,you will be presented with a screen showing you the infections that Emsisoft has detected.
Make sure that everything is <>Checked (ticked)</> and then click on <>Quarantine selected objects</>.
<img title="Emsisoft Scan results" src="http://malwaretips.com/images/removalguide/eek-scan-results.png" alt="Emsisoft smart scan results" width="480" height="345" /></li>
<li>Emsisoft Emergency Kit will now start removing the malicious files.If during the removal process Emsisoft will display a message stating that it needs to reboot, please allow this request.</li>
</ol>
The steps in this guide should remove any remaining traces of this program. If you are still experiencing problems on your PC or would like to have one of our staff members verify that your PC is clean, please start a new thread in our <a href="https://malwaretips.com/forums/malware-removal-assistance-for-windows.10/">Malware Removal Assistance</a> forum.
How was I infected?
How can I prevent these infections?
Keep your system updated
If you have another antivirus, it is recommended that you to switch your antivirus program to a better one. Here are some suggestions:
In addition to your antivirus, you need additional protection such as a firewall and behavioural blocker.
Here are only a few suggestions that will improve your system security. Should you wish to allow us to make full recommendations and set your PC up with maximum security, please start a thread here. Our community of PC enthusiasts and experts will give you feedback and help you secure your system from future malware infections.
Internet Explorer may be the most popular browser but it's definitely not the most secure browser. Consider using other browsers with addition add-ons to safeguard your system while browsing the internet.
Firefox is a more secure, faster browser than Internet Explorer. Firefox contains less vulnerabilities, reducing the risk of drive-by downloads. In addition, you can add the following add-ons to increase security.
Google Chrome is another good browser that is faster and more secure than Internet Explorer by having a sandbox feature. Additionally, you can add the following add-on to Chrome to heighten security.
It is important to perform system maintenance on a regular basis. Here are a few tools and on-demand scanners that you should keep & use every 1-2 weeks to keep your system healthy.
Lastly, avoid Peer-to-peer programs.
<h2> Technical Details </h2>
Registry:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run]
"random name"="C:\windows\<random>.exe"
Files:
In the C:\Documents and Settings\All Users\Application Data\(random)\ folder:
C:\Documents and Settings\All Users\Application Data\(random)\arr-next.gif
C:\Documents and Settings\All Users\Application Data\(random)\bg.wav
C:\Documents and Settings\All Users\Application Data\(random)\b-sep.gif
C:\Documents and Settings\All Users\Application Data\(random)\btn.png
C:\Documents and Settings\All Users\Application Data\(random)\btn-sq.gif
C:\Documents and Settings\All Users\Application Data\(random)\cam-place.bmp
C:\Documents and Settings\All Users\Application Data\(random)\card.jpg
C:\Documents and Settings\All Users\Application Data\(random)\green-l.png
C:\Documents and Settings\All Users\Application Data\(random)\ie7.css
C:\Documents and Settings\All Users\Application Data\(random)\larr.gif
C:\Documents and Settings\All Users\Application Data\(random)\lock.png
C:\Documents and Settings\All Users\Application Data\(random)\locked-text-en.png
C:\Documents and Settings\All Users\Application Data\(random)\logo-img.png
C:\Documents and Settings\All Users\Application Data\(random)\logo-text.gif
C:\Documents and Settings\All Users\Application Data\(random)\mainbg.gif
C:\Documents and Settings\All Users\Application Data\(random)\mcafee-lock.png
C:\Documents and Settings\All Users\Application Data\(random)\money.gif
C:\Documents and Settings\All Users\Application Data\(random)\moneypak.png
C:\Documents and Settings\All Users\Application Data\(random)\payments-en.png
C:\Documents and Settings\All Users\Application Data\(random)\side-block.png
C:\Documents and Settings\All Users\Application Data\(random)\step.gif
C:\Documents and Settings\All Users\Application Data\(random)\step.png
C:\Documents and Settings\All Users\Application Data\(random)\style.css
C:\Documents and Settings\All Users\Application Data\(random)\wait.html
C:\Documents and Settings\All Users\Application Data\(random)\(random).exe
C:\windows\(random).exe
FBI Anti-Piracy MoneyPak Ransomware (the FBI virus) is a fake warning that attempts to scare users into paying money to unlock their PC. This malware will prevent users from accessing the standard windows environment until payment is received. Do not make any payments as this infection can be removed.
Am I infected?
These are screenshots of this ransonware.

<h1>How to remove FBI Anti-Piracy MoneyPak Ransomware Virus (Removal Instructions)</h1>
Please note that this is a self-help guide, use at your own risk.
If you experience any problems completing these instructions or wish to have a staff member guide you, please start a new thread in our <a href="https://malwaretips.com/forums/malware-removal-assistance-for-windows.10/">Malware Removal Assistance</a> forum.
<h2>STEP 1 : Start your computer in Safe Mode with Networking</h2>
- Remove all floppy disks, CDs, and DVDs from your computer, and then <>restart your computer</>.</li>
[*]<>Tap the "F8 key" continuously</> until you get the Advanced Boot Options screen.</li>
[*]On the Advanced Boot Options screen, use the arrow keys to <>highlight Safe Mode with Networking</> , and then <>press ENTER</>.
<br>
<img title="Safe Mode with Networking screen" src="http://malwaretips.com/images/removalguide/safemode.jpg" alt="[Image: Safemode.jpg]" width="539" height="292" border="0" /></li>
</ol>
<h2> Step 2: Download and run RKill</h2>
Download mirror 1 - Download mirror 2 - Download mirror 3
- Save it to your Desktop.
- Double click the RKill desktop icon.
- It will quickly run. If it does not run, try another download link from above.
- When Rkill has completed its task, it will <>generate a log</>. You can then <>proceed with the rest of the guide</>.
<img title="RKILL LOG" src="http://malwaretips.com/images/removalguide/rkill3.png" alt="[Image: XP Defender 2013 rkill3.jpg]" width="414" height="187" border="0" /></li>
</ol><br>
<br><>WARNING: Do not reboot your computer after running RKill as the malware process will start again , preventing you from properly performing the next step.</>
<h2>Step 3: Download TDSSkiller from here </h2>
- Double-Click on TDSSKiller.exe to run the application
- When TDSSkiller opens, click Start scan
- If a suspicious object is detected, the default action will be Skip, click on Continue. (If it saids TDL4/TDSS file system, select delete)
- If malicious objects are found, ensure Cure (default) is selected, then click Continue and Reboot now to finish the cleaning process.
NOTE: Reboot to safe mode with networking again and run rKill before proceeding to the next step.
<h2> Step 4: Download Malwarebytes' Anti-Malware(download link) to your desktop

- Double-click mbam-setup.exe and follow the prompts to install the program.
- At the end, be sure a checkmark is placed next to
- Update Malwarebytes' Anti-Malware
- and Launch Malwarebytes' Anti-Malware
- then click Finish.
- Malwarebytes Anti-Malware will now start and you'll be prompted to start a trial period , please select '<>Decline</>'
<img title="Decline trial period in Malwarebytes Anti-Malware" src="http://malwaretips.com/images/removalguide/mbam3.PNG" alt="[Image: Decline Malwarebytes trial]" width="432" height="165" border="0" />
[*]If an update is found, it will download and install the latest version.

[*]Once the program has loaded, select Perform quick scan, then click Scan.
[*]When the scan is complete, click OK, then Show Results to view the results.

[*]Be sure that everything is Checked (ticked) and click on Remove Selected.
[*]Reboot your computer if prompted.
NOTE: Boot to safe mode with networking again
<h2>STEP 5: Double check for other malicious files with Emsisoft Emergency Kit</h2>
<ol>
<li>You can download the latest official version of Emsisoft Emergency Kit from the below link.
<a href="http://malwaretips.com/download-emsisoft" rel="nofollow" target="_blank"> <>EMSISOFT EMERGENCY KIT DOWNLOAD LINK</></a> <em>(This link will open a download page in a new window from where you can download Emsisoft Emergency Kit)</em></li>
<li>After the download process will finish , you'll need to <span style="font-weight: bold;">unpack EmsisoftEmergencyKit.zip</span>
<img title="Unpack EmsisoftEmergencyKit.zip" src="http://malwaretips.com/images/removalguide/ekk-zip-image.png" alt="Unpack Emsisoft Emergency Kit" width="319" height="109" /></li>
<li>Open the Emsisoft Emergency Kit folder and double click <>EmergencyKitScanner.bat</>.
<img title="Double click on EmergencyKitScanner.bat" src="http://malwaretips.com/images/removalguide/ekk-batfile.png" alt="Click on EmergencyKitScanner.bat" width="396" height="141" /></li>
<li>A pop-up will prompt you to update Emsisoft Emergency Kit,and you'll need to click the <>Yes</> button to allow this request.
<img title="Update Emsisoft Emergency Kit definitions" src="http://malwaretips.com/images/removalguide/eek-update.png" alt="Update Emsisoft Emergency Kit" width="360" height="139" /></li>
<li>After the Update process has completed,click on the <>Menu</> tab and then select <>Scan PC</>.
<img title="Go to the Scan tab to start a system scan" src="http://malwaretips.com/images/removalguide/ekk-scan.png" alt="Scan tab on Emsisoft Emergency Kit" width="479" height="346" /></li>
<li>Select <>Smart scan</> and click on the <>SCAN</> button to search for malicious files.
<img title="Start a Emsisoft Emergency Kit Smart scan" src="http://malwaretips.com/images/removalguide/ekk-smart-scan.png" alt="Emsisoft Emergency Kit smart scan" width="480" height="345" /></li>
<li>Emsisoft will now start scanning your computer for malicious files.When the scan will be completed,you will be presented with a screen showing you the infections that Emsisoft has detected.
Make sure that everything is <>Checked (ticked)</> and then click on <>Quarantine selected objects</>.
<img title="Emsisoft Scan results" src="http://malwaretips.com/images/removalguide/eek-scan-results.png" alt="Emsisoft smart scan results" width="480" height="345" /></li>
<li>Emsisoft Emergency Kit will now start removing the malicious files.If during the removal process Emsisoft will display a message stating that it needs to reboot, please allow this request.</li>
</ol>
The steps in this guide should remove any remaining traces of this program. If you are still experiencing problems on your PC or would like to have one of our staff members verify that your PC is clean, please start a new thread in our <a href="https://malwaretips.com/forums/malware-removal-assistance-for-windows.10/">Malware Removal Assistance</a> forum.
How was I infected?
- Rogues can get on to computers without the user's consent through Drive-by downloads. When a user visits a compromised or infected website, the site immediately checks for any security vulnerabilities on the machine to inject the malicious code.
- Peer-to-peer (P2P) programs utorrent, Limewire, and Kazaa are frequently used by hackers to distribute malware
- Hackers can also trick the user into downloading a file, saying it is a legitimate file needed to view a video or pictures.
How can I prevent these infections?
Keep your system updated
- Keeping your programs (especially Adobe and Java products) updated is essential. Update Checker will notify you if any of your programs require an update.
- Microsoft releases patches for Windows and Office products regularly to patch up Windows and Office product bugs and vulnerabilities.
- Please ensure you update your system regularly and have automatic updates on. You can learn how to turn Automatic Updates on here
If you have another antivirus, it is recommended that you to switch your antivirus program to a better one. Here are some suggestions:
- avast! 7 Home Edition - Don't use it with Online Armor
- Avira AntiVir Personal
- Microsoft Security Essentials
In addition to your antivirus, you need additional protection such as a firewall and behavioural blocker.
- Online Armor
- Comodo Firewall - If you are an advance user
Here are only a few suggestions that will improve your system security. Should you wish to allow us to make full recommendations and set your PC up with maximum security, please start a thread here. Our community of PC enthusiasts and experts will give you feedback and help you secure your system from future malware infections.
Internet Explorer may be the most popular browser but it's definitely not the most secure browser. Consider using other browsers with addition add-ons to safeguard your system while browsing the internet.
Firefox is a more secure, faster browser than Internet Explorer. Firefox contains less vulnerabilities, reducing the risk of drive-by downloads. In addition, you can add the following add-ons to increase security.
- KeyScramber - Encrypts your keystrokes to protect you against keyloggers that steals personal & banking information
- AdBlock - Disable/blocks advertisements on websites so you won't accidentally click on a malicious ad.
- NoScript - Disables Flash & Java contents to avoid exploits or drive-by attacks
- Web of Trust - Shows the website rating by other users and blocks dangerous and poor-rated sites
Google Chrome is another good browser that is faster and more secure than Internet Explorer by having a sandbox feature. Additionally, you can add the following add-on to Chrome to heighten security.
It is important to perform system maintenance on a regular basis. Here are a few tools and on-demand scanners that you should keep & use every 1-2 weeks to keep your system healthy.
Lastly, avoid Peer-to-peer programs.
- Peer-to-peer programs are legitimate but the files shared are extremely dangerous. Hackers often use fake file names to trick users into downloading malware.
<h2> Technical Details </h2>
Registry:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run]
"random name"="C:\windows\<random>.exe"
Files:
In the C:\Documents and Settings\All Users\Application Data\(random)\ folder:
C:\Documents and Settings\All Users\Application Data\(random)\arr-next.gif
C:\Documents and Settings\All Users\Application Data\(random)\bg.wav
C:\Documents and Settings\All Users\Application Data\(random)\b-sep.gif
C:\Documents and Settings\All Users\Application Data\(random)\btn.png
C:\Documents and Settings\All Users\Application Data\(random)\btn-sq.gif
C:\Documents and Settings\All Users\Application Data\(random)\cam-place.bmp
C:\Documents and Settings\All Users\Application Data\(random)\card.jpg
C:\Documents and Settings\All Users\Application Data\(random)\green-l.png
C:\Documents and Settings\All Users\Application Data\(random)\ie7.css
C:\Documents and Settings\All Users\Application Data\(random)\larr.gif
C:\Documents and Settings\All Users\Application Data\(random)\lock.png
C:\Documents and Settings\All Users\Application Data\(random)\locked-text-en.png
C:\Documents and Settings\All Users\Application Data\(random)\logo-img.png
C:\Documents and Settings\All Users\Application Data\(random)\logo-text.gif
C:\Documents and Settings\All Users\Application Data\(random)\mainbg.gif
C:\Documents and Settings\All Users\Application Data\(random)\mcafee-lock.png
C:\Documents and Settings\All Users\Application Data\(random)\money.gif
C:\Documents and Settings\All Users\Application Data\(random)\moneypak.png
C:\Documents and Settings\All Users\Application Data\(random)\payments-en.png
C:\Documents and Settings\All Users\Application Data\(random)\side-block.png
C:\Documents and Settings\All Users\Application Data\(random)\step.gif
C:\Documents and Settings\All Users\Application Data\(random)\step.png
C:\Documents and Settings\All Users\Application Data\(random)\style.css
C:\Documents and Settings\All Users\Application Data\(random)\wait.html
C:\Documents and Settings\All Users\Application Data\(random)\(random).exe
C:\windows\(random).exe
Last edited by a moderator: